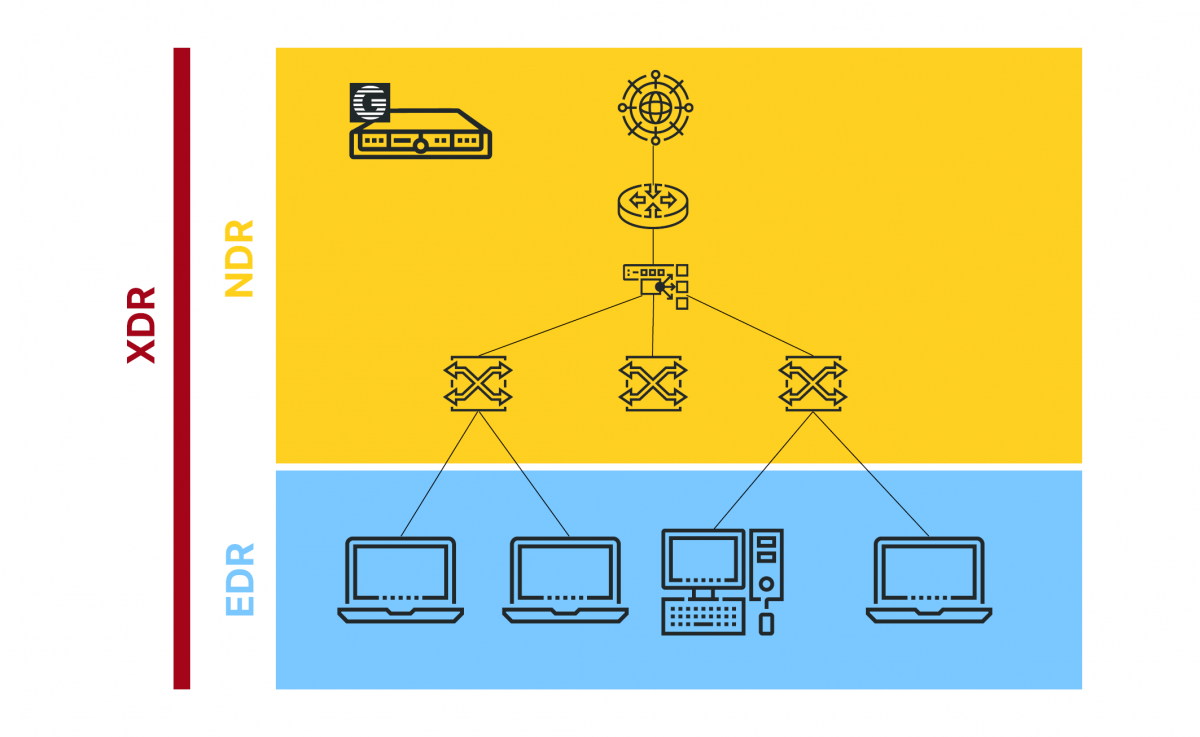
While the convergence of IT and OT has been around for several years, there still exists a disparity between the technology, tools, and resources deployed in each network type. IT teams often turn to traditional security vendors for NGFW, XDR, and NDR tools, which don’t always work effectively in OT environments due to the different needs of SCADA and ICS systems.
GREYCORTEX has made it its mission to provide customers who have both IT AND OT networks with technologically advanced and reliable security tools. By fostering collaboration between IT and OT teams, they enable you to strengthen your security strategies and better protect yourself against cyber threats.
In addition to its robust detection and response capabilities, GREYCORTEX Mendel offers powerful real-time network analytics. This technology provides you with visibility into your network activities, whether you’re managing a small network of 100 devices or a vast, geographically dispersed network with hundreds of thousands of devices.
How It Works
GREYCORTEX Mendel sees and visualizes traffic in the context of time and events, including L2 and L3 OT protocols and application data. To identify all devices in a network and gain a comprehensive understanding of their interactions, the protocols they use, and where data flows, Mendel requires complete packet visibility. This is where Garland Technology comes in. Network TAPs are a tested and proven industry best practice for ensuring complete network visibility for security and monitoring tools.
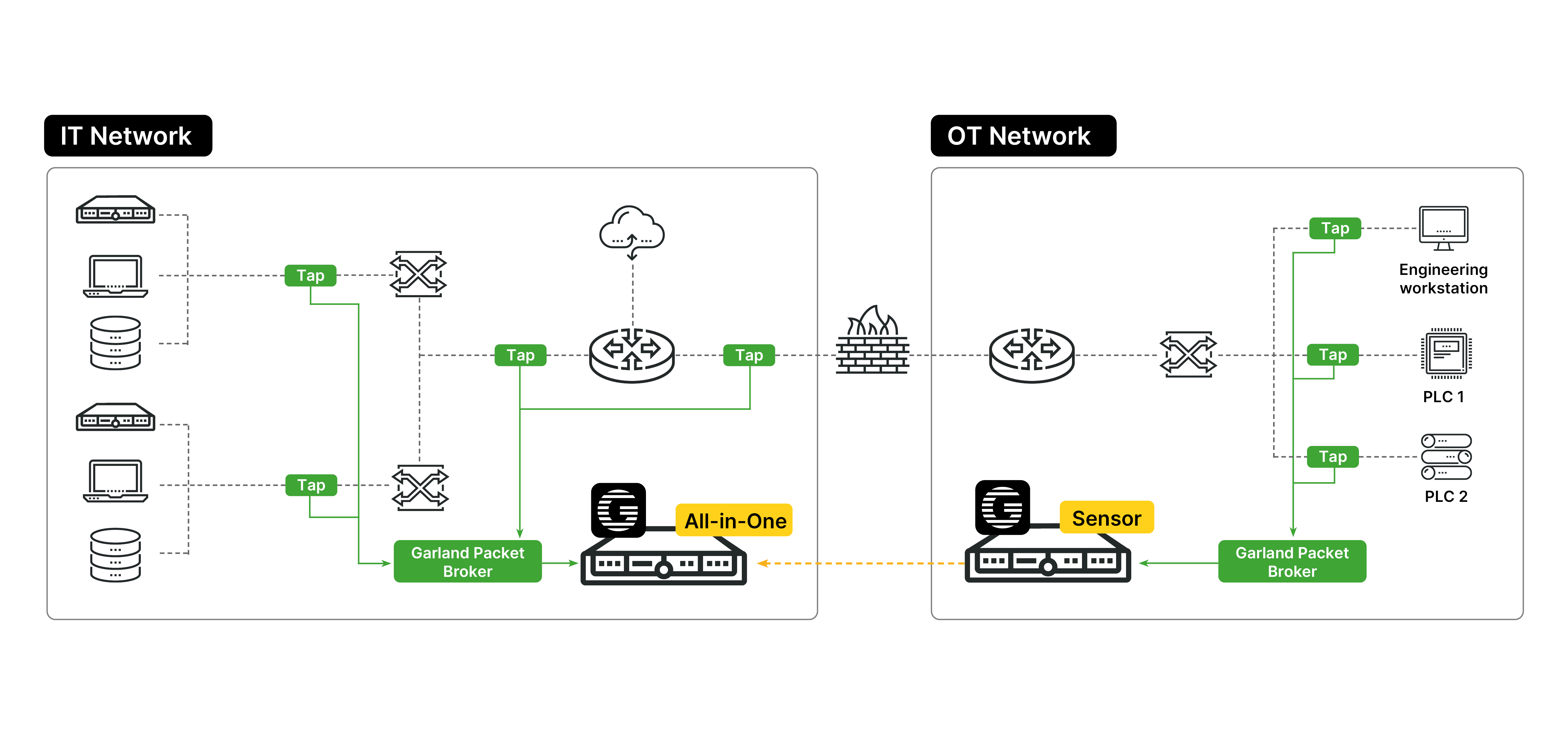
Scenario #1: Security Monitoring for IT and OT Infrastructure
- Within both IT and OT environments, data from the network segments are fed through Garland Technology Network TAPs. These TAPs mirror the network traffic to provide 100% visibility across the environments.
- In OT scenarios, Garland commonly uses its specialized Industrial Network TAPs that are purpose-built for industrial, manufacturing, utility, and military environments.
- Data from multiple Network TAPs is delivered to Garland’s PacketMAX™ Advanced Features to aggregate, filter, and load balance the mirrored traffic.
- The aggregated traffic from each location is then delivered to GREYCORTEX Mendel. Mendel serves as both a Network Detection and Response solution for the IT infrastructure and as an advanced industrial Intrusion Detection System (IDS) for industrial environments, utilizing deep packet inspection for ICS and SCADA traffic.
- Mendel offers a complete view of your network and business applications through active and passive asset discovery. It provides detailed asset information, including vendor details, hardware and software versions, and network configurations.
Scenario #2: Security Monitoring of Medical IoT Devices and Critical Healthcare Systems
- Garland Technology’s compact, high-performance network TAPs provide a 100% full duplex copy of the wire data.
- Network traffic is sent to the PacketMAX™: Advanced Features packet broker for aggregation, filtering, load balancing, and deduplication to remove duplicate packets. The refined traffic is then sent to GREYCORTEX Mendel for detailed analysis and detection of malicious activities and advanced threats.
- Mendel enables system analysts to investigate security and operational events effectively. It helps them find root causes and respond to threats quickly. This is possible because Mendel provides a comprehensive view of network activities, whether it’s for specialized medical devices like CT scanners, X‑Ray machines, and DICOM workstations, or for Medical Information Systems and Building Automation Systems.
Key Benefits of the Garland-GREYCORTEX Solution
- Easy to manage and cost-effective, providing comprehensive monitoring of IT, OT, and IoT environments.
- Gain 100% network visibility into your active IT and OT assets without added latency.
- Ensure security with TAPs that lack IP or MAC addresses, making them immune to hacking.
- Improve collaboration and break down silos across teams with deep visibility across all network and application layers.
- Leverage real-time network analytics and advanced detection of threats and operational issues, with the capability to respond swiftly.
- Quick to implement within strict maintenance windows.
About Garland Technology
Garland Technology is an industry leader in IT and OT network solutions for enterprise, critical infrastructures, and government agencies worldwide. Since 2011, Garland Technology has been engineering and manufacturing simple, reliable, and affordable Network TAPs and Network Packet Brokers in Richardson, TX. For help identifying the right IT/OT network visibility solutions for projects large and small, or to learn more about the inventor of the first bypass technology, visit garlandtechnology.com.
About GREYCORTEX
GREYCORTEX uses advanced artificial intelligence, machine learning, and data mining methods to help organizations make their IT operations secure and reliable.
MENDEL, GREYCORTEX’s network traffic analysis solution, helps corporations, governments, and the critical infrastructure sector protect their futures by detecting cyber threats to sensitive data, networks, trade secrets, and reputations, which other network security products miss.
MENDEL is based on 10 years of extensive academic research and is designed using the same technology which was successful in four US-based NIST Challenges.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.