
Does your business rely on access control lists (ACLs) to manage user access? If not, you’re not alone. Many organizations shy away from using them due to the challenges of maintaining numerous lists across different network areas. However, an access control list can provide an extra layer of security for your network in specific scenarios and can be effectively integrated with role-based groups when needed.
This article will explore how an access control list can streamline your access management processes. We’ll also dive into the benefits of ACLs, including improved security measures and their adaptivity to various environments. Finally, we’ll offer practical insights into how access control lists are used to manage access and protect sensitive information.
Read on if you want to untangle the complexities of ACLs and enhance your network’s security.
What is an access control list (ACL)?
An access control list (ACL), sometimes called just an access list, filters network traffic based on source and destination. It’s a set of rules that determines which users can access particular network objects or devices. Users not included on the list are denied access to these resources.
Moreover, an access list can enhance role-based access control (RBAC). For example, they can be configured to allow only members of a development team to access a specific codebase while blocking access to all other users with DevOps roles who aren’t involved in the project.
Additionally, implementing network access control best practices involves using ACLs to manage user access and enhance security across the network.
What are ACLs used for?
An access control list (ACL) is a vital tool for managing permissions in computer systems and networks. It is mainly used for essential network security tasks, like controlling user access, protecting data, and preventing intrusions.
ACLs are also key for meeting cybersecurity standards and certifications, such as those related to network access control and network segmentation. Implementing ACLs is often a necessary step on the path to compliance, ensuring an organization fulfills required regulations.
ACLs help regulate the flow of data in and out of network components that users directly access, such as gateways and endpoints. For instance, a network administrator might have the permissions to read, write, and edit sensitive files, while a guest user may only view these files. An access control list ensures such selective control access based on specific criteria like IP addresses, protocols, or ports. This enhances network security by allowing precise control of who can access what.
Additionally, ACLs can be set up on various network devices, including routers, switches, VPNs, or databases. This provides a clear and effective way to manage access, improving traffic flow for better efficiency and security. By blocking malicious traffic and giving IT admins granular control, ACLs play a key role in keeping network systems safe and running smoothly.
How ACLs work
Access control lists manage access and monitor traffic within networks and systems, ensuring that only authorized interactions are permitted. Primarily installed in routers and switches, ACLs play a critical role in traffic control by guiding the flow of data throughout the network.
Each ACL contains access control entries (ACEs), which list user or group names along with their granted access rights. These rights are organized in a string of bits known as an access mask. Whether used for packet filtering or file access, ACLs provide a structured, rule-based security approach that helps administrators maintain control over network and system resources.
Rule creation and ordering
ACLs function by using predefined rules to allow or deny packets, with the order of these rules being critical in determining how traffic is managed. The process starts with rule creation and ordering, where admins set up ACL rules in a specific sequence that prioritizes certain traffic over others based on security policies.
Packet evaluation
This is another key function of ACLs, where the data within each packet is checked against the ACL rules to decide if it should be allowed through or blocked. This evaluation is based on criteria like IP addresses, port numbers, and packet content, aligning with established security measures.
Default actions
For file systems, ACLs detail specific user access privileges to system objects such as files and directories, dictating actions like reading, writing, or executing based on the user’s role (e.g., administrator or guest).
This granularity extends to default actions, where ACLs enforce predetermined responses when a packet or access request does not meet any of the specified rules. Typically, this results in a denial of access to protect the network’s integrity.
An access control list: various types
Access control lists come in various types, each serving a unique purpose based on functionality and scope.. There are two basic ones:
-
File system ACLs manage access to files and directories within an operating system. They dictate user access permissions and privileges once the system is accessed.
-
Networking ACLs regulate network access by providing instructions to network switches and routers. They specify the types of traffic allowed to interface with the network and define user permissions within the network. Networking ACLs function similarly to firewalls in controlling network traffic.
Additionally, ACLs can be categorized according to their traffic filtering capabilities:
-
A standard ACL does not differentiate between IP traffic. Instead, it allows or blocks traffic based on the source IP address.
-
An extended ACL offers a more granular level of control. It uses both the source and the destination IP addresses, such as a source IP address, destination IP addresses, port numbers, and protocol types (ICMP, TCP, IP, UDP). It can differentiate IP traffic to dictate what is allowed or denied access.
The advantages of using an access control list
An access control list isn’t a one-size-fits-all solution for network security. However, using roles for access management offers several benefits:
-
Enhanced security. Users access only resources aligned with their roles, minimizing the risk of credential theft or phishing attacks. ACL implements separation of duties, reducing the threat posed by privileged users.
-
Improved efficiency. ACLs streamline access control maintenance. Admins can assign new hires to role groups, granting them associated permissions without creating individual profiles.
-
Optimized network performance. With ACLs, admins can define criteria such as source and destination IP addresses, ports, and protocols to regulate traffic flow. By restricting access to certain resources based on these criteria, ACLs help prevent unnecessary network congestion and improve overall network performance.
-
Scalability & flexibility. ACLs allow for flexible role adjustments as organizations evolve. Changes can be applied globally, reducing the chance of security vulnerabilities.
-
Compliance & auditing. ACLs help meet regulatory requirements like HIPAA. Healthcare entities, for example, can limit access to patient records through role-based restrictions. Additionally, ACLs simplify auditing access, making it easier to track access requests and user activity.
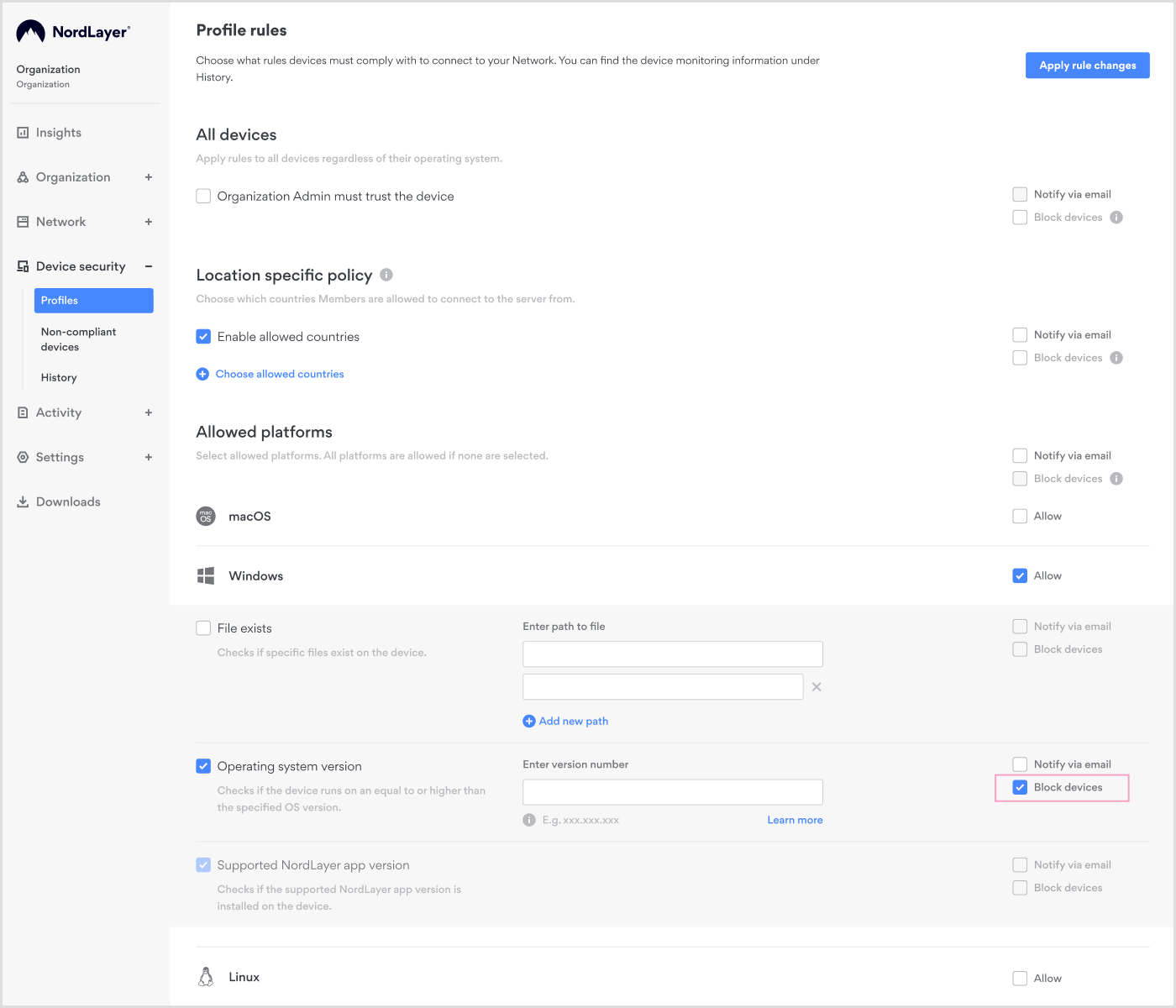
Enhancing device security with ACLs
While ACLs offer significant advantages in network security, it’s essential to extend this protection to device-level security. By adopting Device Posture Security (DPS), your organization can evaluate the security of devices connecting to the network.
Through DPS, you can evaluate and monitor devices according to your predefined rules. But that’s not all. You can also automatically restrict network access for accounts using non-compliant devices. This integrated approach enhances overall network security by addressing vulnerabilities at both the network and device levels.
IT administrators can easily implement ACLs for Device Posture Security using our web-based Control Panel. To enable DPS checks, create various rules such as existing file check, OS version, jailbreaking or rooting status, and device location. Setting up ACLs in the panel is simple. Just create a profile and specify the desired rules. Once configured, it’s important to test the ACL to ensure that it is functioning as expected. Finally, activate the ACL to start enforcing the specified access control rules on your network.
ACLs for internal network segmentation
Protecting your data from leaks and insider threats is more crucial now than ever. It’s not just about safeguarding information; it’s about maintaining the credibility of your business. That’s where access control lists (ACLs) come in. They act as gatekeepers, deciding who gets access to what within your network. By setting up ACLs, you can stop unauthorized users from moving laterally through your network, helping to prevent data breaches.
Additionally, when you combine ACLs with role-based access control (RBAC), you gain even more control over who can access different parts of your network. With our Cloud Firewall feature, you can optimize your network by implementing granular segmentation using ACLs. These lists act as virtual bouncers, controlling who can access which parts of your network.
Our intuitive Control Panel facilitates the creation and management of ACLs, providing a streamlined and centralized approach to network security management.
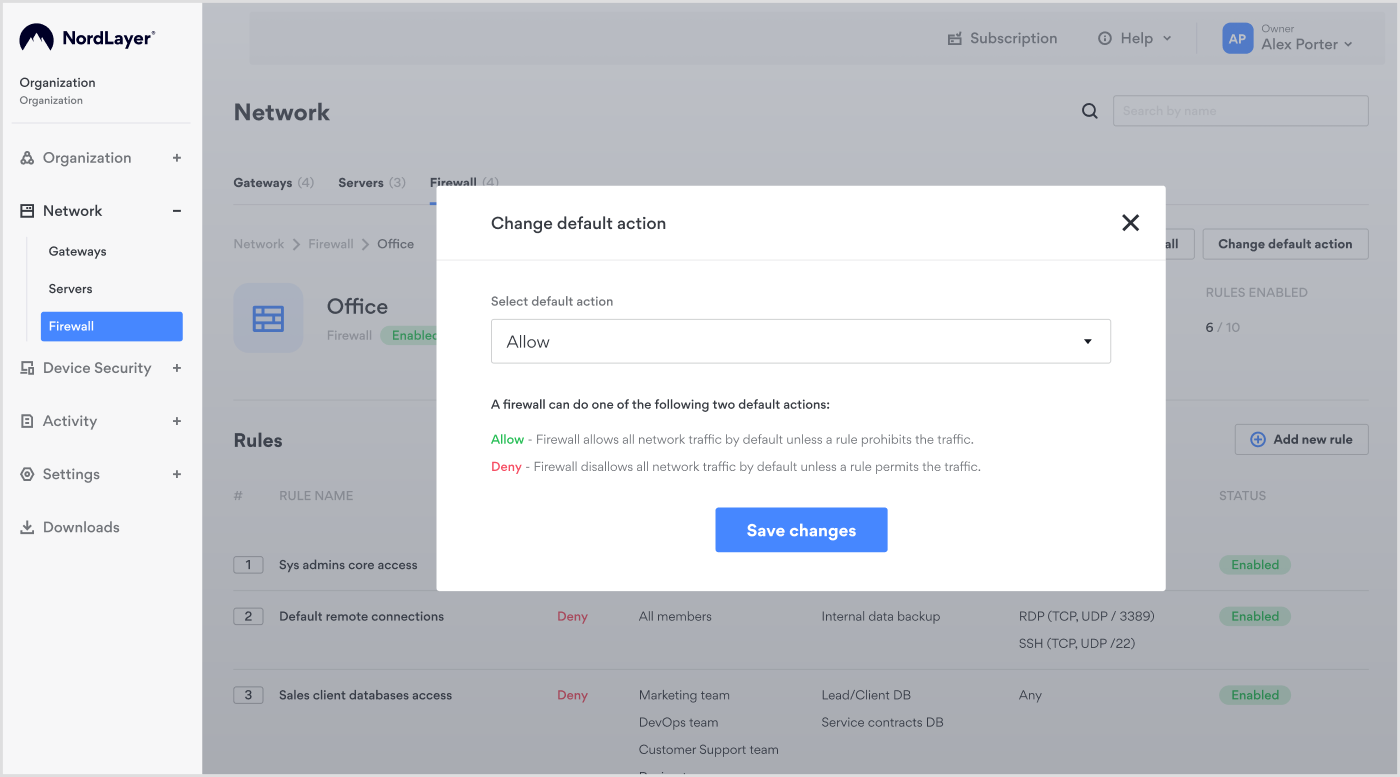
ACLs in external access control
Managing network access isn’t just about your team. You also have to consider third-party vendors, contractors, and other external partners who might need access to your systems. With access control lists, you can ensure that these third parties only have access to the specific resources they need, minimizing the risk of unauthorized access and potential security breaches.

By setting up granular segmentation and ACL rules, you can protect your network against potential threats while enabling collaboration with external partners. Our Cloud Firewall feature makes managing external access easy, ensuring your network is protected from all angles.
Boost your network security with NordLayer’s ACLs
Access control lists (ACLs) make role-based access control more precise, ensuring only the right people have access to your data and resources, and improving network performance. They’re the frontline defense against unauthorized access and potential breaches.
But the benefits of ACLs don’t stop there. By combining ACLs with our Cloud Firewall feature, you’re not just building walls—you’re creating an impenetrable fortress around your devices and network. With NordLayer, setting up and managing ACLs is a breeze, giving you peace of mind knowing your network is fortified against any threats that come its way.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
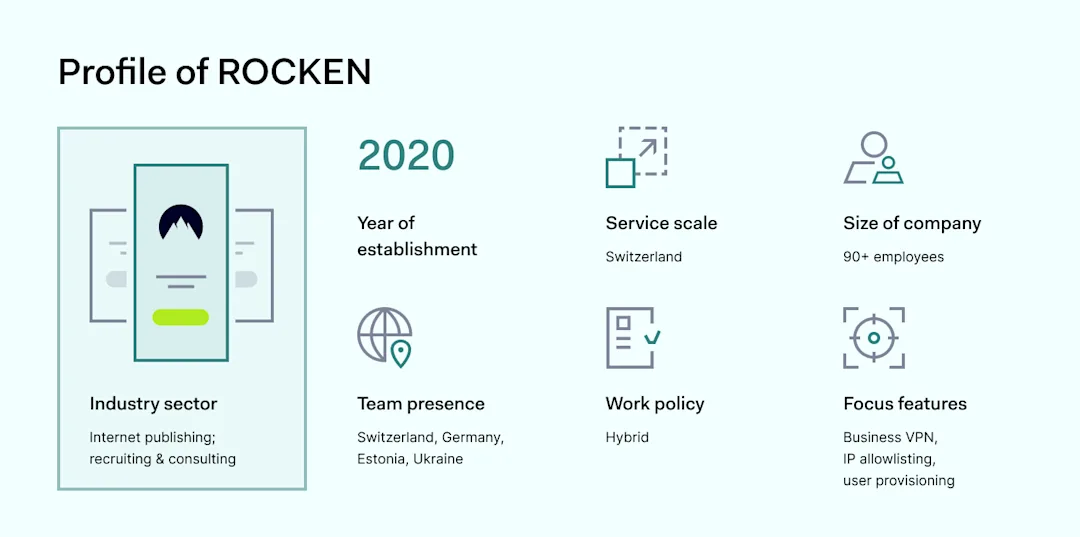
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.







)
)