Remote work is now a key part of how many businesses operate. It offers new ways of working, like flexible hours and the chance to save money on office space. Because of this, it’s important to have a clear plan for remote employees and those who work both in the office and at home.
In this article, we’ll take a look at how to put together a remote work agreement for your company. We’ll cover why you need one, what should be included, and some helpful tips for making it work. By planning ahead, businesses can make the move to remote work smoothly, leading to a successful and energetic work environment.
What is the remote work policy?
A remote work policy is like a set of rules that bosses and workers follow when working from home or outside the office. It explains everything you need to know about working remotely, like your job duties, when you should be working, the technical help you can get, and other important information.
This policy helps to protect both the company and the workers so nobody gets into legal trouble. It sets fair rules for everyone and ensures all employees understand what they need to do when working remotely.
A remote work policy might talk about things like:
What equipment you’ll need
Making sure you have a good internet connection
How you’ll talk to your co-workers
Ways to keep computer information safe
Having a remote work policy helps businesses be more flexible, letting people work where they want while ensuring everyone does their job right and keeps information secure.
The details of a remote work policy can change depending on things like what kind of business you’re in, how big your company is, and what laws you have to follow. But no matter what, certain things are always important regarding remote work policies.
Why does your company need a remote work policy?
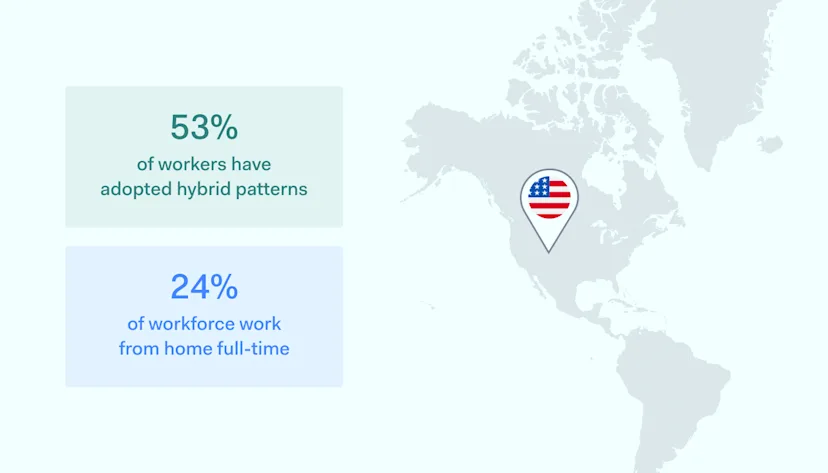
After the COVID-19 pandemic, there was a shift in employees’ view of remote work. A well-defined remote work agreement becomes crucial with the increasing prevalence of remote workers. Here are the main arguments for it:
Work flexibility is not a bonus but an expectation
Work flexibility is in greater demand than ever before. According to the American Opportunity Survey, when people have an opportunity to work flexibly, 87% of them take it. This is noticeable across occupations, demographics, and geographies. The data shows that the remote work trend continues to shape the future of work relationships.
According to the same research, the third most popular reason for workplace changes was a search for more flexible work arrangements. This means businesses that have already adopted remote work policies have the advantage of attracting top talent. Yet, it’s first necessary to form a remote work policy to move forward with remote work as a practice.
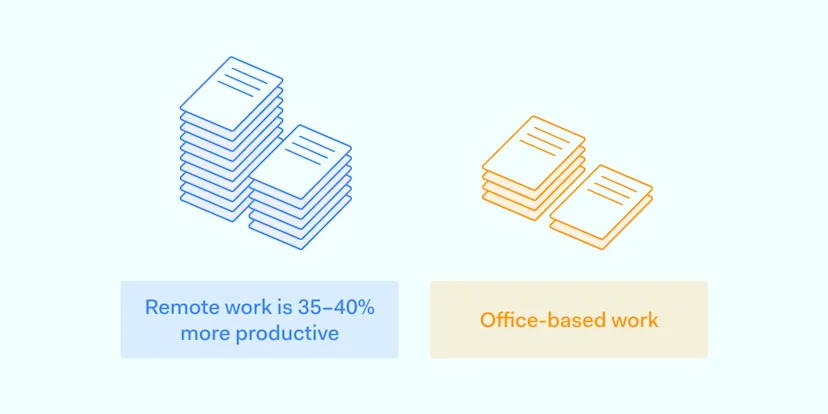
Remote work brings value to the company
There are tangible business benefits directly attributed to flexible working conditions. Working from home did increase productivity by 5%. This shows that giving employees the freedom to choose how they work enables them to be more efficient regarding their work scope. In this case, the business wins, as it reaps the productivity benefits.
Additionally, remote work expands the pool of potential employees. This means that the workplace can attract global talents while fostering innovation, ultimately leading to improved profitability. Far from just being something that exists to please employees, remote work has direct and quantifiable effects on business performance. Yet, it also needs a remote work policy to be viable.
Compliance must remain a priority
Remote work, just like any other job, has to follow specific laws and rules. Employers need to know where their employees are working to avoid legal and tax problems. Since these rules can be very different in various places, it can be tricky for companies with remote workers in different regions or countries.
They also have to think about things like health insurance, which plays a big part in shaping remote work policies.
It’s crucial to regularly check and update remote work rules with the help of legal, HR, IT, and other important departments. This helps to keep everything running smoothly and legally. There may be limits on where or for how long employees can work remotely, and these rules should be part of your remote work policy. By putting these rules in place, you can protect your organization against future misunderstandings and communication breakdowns.
Data security and confidentiality
Employees working from home or elsewhere can create security risks for the company’s information and digital assets. To keep everything safe, the company needs a clear policy for remote work. This policy should spell out the rules everyone must follow to protect sensitive data and other important information.
The remote work policy should also include other safety measures, like:
Making sure that remote workers are using safe, up-to-date software.
Requiring them to use virtual private networks (VPNs) to keep their connections private.
Making them use multi-factor authentication to access company systems, which means they have to provide more than one piece of information to prove who they are.
Requiring encrypted communication tools for sensitive conversations.
Regularly updating and patching remote devices to guard against possible weaknesses.
By following these steps, the company can keep its valuable assets safe and maintain the trust of its clients, partners, and stakeholders in a world where more and more work is being done remotely.
Remote work policy components and examples
To help you create your remote work policy, we drafted a potential structure that could be used as an example.
Objective
This guide outlines the conditions and regulations for staff members working from places other than designated work locations such as [office, building, floor, etc.]. It aims to ensure that both employees and supervisors know the remote work conditions and guidelines.
The relevant authorities must first approve all remote work requests [supervisor, manager, Human Resources, etc.]. This remote work regulation stays effective until [an end date is set or the policy is reviewed].
Applicability
This policy is relevant only to [full-time employees, suitable part-time employees, staff not in training, etc.].
Guidelines
Eligible staff members are required by [Company name] to work remotely on a [temporary or permanent] basis. Work can be carried out [anywhere, specific city or state, etc.].
The following criteria must be outlined for positions that qualify for remote work:
Work timing and presence
Specified times when remote employees must be working
Example: “Remote employees should be actively working according to the schedule outlined in their contract. If an alternative work schedule is desired, written consent from a supervisor must be obtained, and the new schedule must be communicated to the team.”
Remote work setting
Standards related to the remote working space
Example: “To ensure optimal productivity, remote workers must select an environment without distractions, with stable internet access, and conducive to focused work during working hours.”
On-location work
Steps remote employees need to follow when working on-site
Example: “If planning to work at the office, remote employees should use [Company Name] ‘s reservation system to check and reserve available workspaces to prevent overcapacity.”
Communication expectations
Preferred methods of communication and expected response times
Example: “Remote employees should be accessible through Slack or phone during working hours and should reply to emails within a day unless specified differently in the client’s statement of work. Regular check-ins with teammates and attendance at mandatory meetings are also required.”
Tools and technology
What will the company supply in terms of hardware and software
Example: “[Company Name] will furnish remote employees with the necessary tools and technology tailored to their roles and responsibilities. This equipment must be used exclusively for business and kept secure.”
Information security
Instructions for safeguarding confidential information
Example: “Remote employees are expected to follow the company’s acceptable use policy (AUP) and bring your device (BYOD) policy, taking necessary measures to reduce cybersecurity risks and safeguard sensitive and proprietary information.”
Best practices for implementing a remote work policy

![]() Implementing a remote work policy benefits employees and employers, allowing flexibility and the ability to tap into a broader talent pool. However, to ensure success, it’s a good idea to consider the following best practices.
Implementing a remote work policy benefits employees and employers, allowing flexibility and the ability to tap into a broader talent pool. However, to ensure success, it’s a good idea to consider the following best practices.
1. Identify which roles are suitable for remote work
Not every position in an organization can seamlessly transition to remote work arrangement. While a software developer may easily work from home, an office administrator may not fulfill all job obligations remotely. Therefore it’s necessary to outline which roles can function in a home environment without decreasing employee performance.
Secondly, it’s also important to look at the tasks themselves and determine whether they can be done remotely, even when factoring that some job roles are more suited to remote work. In those cases, setting a fixed amount of time for in-person and remote work is a good compromise.
2. Reinforce the guidelines
It’s important to know which company rules and guidelines need to be followed, even if employees are working from home. All the usual company rules still apply, but we need to make sure everyone understands that these rules aren’t put on hold just because they’re working remotely.
By providing clear and easy-to-understand guidelines, we can set clear expectations for everyone. This will help prevent confusion and make managing remote work much easier. It creates a level of openness and trust that will make remote working a smooth and efficient process for all involved.
3. Create remote work plans
Company goals need to be broken down into clear and achievable targets. Department heads can help turn these big objectives into practical tasks and responsibilities. This gives employees a clear path to follow, making their jobs easier during changes or transitions.
Managers should make it a habit to lay out these plans and talk them over with their teams. They should also keep an eye on progress to make sure everyone is on track to meet the goals. This helps prevent confusion, especially when shifting to a remote work model that may require more effort from employees outside the office. It keeps everyone on the same page and ensures a smooth transition.
4. Specify the necessary tools for remote work
Remote workers need the right technology and help to do their jobs and work together with their team. This means making sure they have what they need to do their tasks from home or elsewhere. Sometimes, you might even need to buy extra software or tools to help remote workers handle the special demands of working away from the office.
Remote work often causes communication problems and mix-ups. But by supporting remote employees with different tools, you can help them stay in touch in real-time. This makes it easier to sort out any problems that might come up.
5. Detail insurance and liability considerations
If you’re working from home, it’s essential to know your rights and how things like injuries or losses will be dealt with. A good remote work policy will cover all these details, including benefits, insurance, and liability considerations. It’s not just important for employees; employers need this too, to make sure that everyone’s working in a safe and secure way.
What does all this mean in practice? Well, it helps create a positive work environment and makes sure that the company is following the law, reducing legal risks. Plus, it shows that the company really cares about its employees’ well-being and safety. By being clear and open about the rules and policies, it can help build trust and make remote workers feel like a part of the team, boosting productivity and inclusion within the company culture.
Easier cybersecurity with NordLayer
Remote working is quickly transforming traditional employment models. Yet, in this arrangement, the company and its employees share the responsibility of maintaining security and the well-being of company data. Achieving this may only be feasible with the right tools and solutions for network management.
NordLayer offers a package for hybrid work security that enhances the safety of working remotely. We enhance collaboration between remote employees and modern businesses allowing them to control access to company resources and safeguard critical assets.
Without needing any special hardware, NordLayer provides an accessible solution suitable for businesses of all sizes and easily enables secure remote work from anywhere. Solve your remote work challenges with effective solutions to make your setup safer.
Contact our sales department to learn more about our solutions and uplift your remote work capabilities today.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.