
Introduction
Jsonpickle is a python library which is widely used to serialize and deserialize python objects. Serialization is very useful to save state for an object and reconstruct the object from that state.
In this post, we will exploit the latest jsonpickle library to get remote command execution.
Installation
Jsonpickle is available on the Python Package Index (PyPI), a repository hosting over 10TB of packages that programmers use to build their applications. We install the library with the command, pip3 install jsonpickle.
Setting Up Jsonpickle
For the scope of this article, we will focus on only two functions from the jsonpickle library: encode and decode.
First, we define a class named “zoo” and create an object for it.

Figure 1: Creating a class and an object for it
Now if we want to save the state of the object, we can encode the object with jsonpickle and print the byte stream, which can be used later to reconstruct the object with its state included.

Figure 2: Encoding the object with jsonpickle
Conversely, we can reconstruct the object with a decode function.

Figure 3: Decoding the object with jsonpickle
Attack Scenario
Now that we’ve demonstrated the two functions and how they work, we are ready to move forward with the attack.
Since we are attacking the jsonpickle library, we create a sample web application with jsonpickle to attack.
Our simple web application takes the base64 encoded serialized data and then decodes the base64 to jsonpickle object. And finally convert the jsonpickle object to actual object

Figure 4: Demonstrating encoding and decoding jsonpickle object
So, when we run the application with flask run, we can pass our data to http://127.0.0.1:5000/data?serialized= to interact with jsonpickle library


Creating the Exploit
So, we create a class RCE with member function reduce which will execute our payload.
After creating the object, we need to serialize the object and encode it with base64 so it can be passed to our web application.

Figure 5: Creating RCE and a serialized object
Now we copy the base64 payload and pass it to our web application, and we see that the command execution is successful and we have compromised the application.

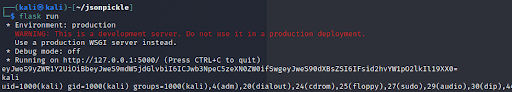
Figure 6: Compromised application from base64 payload
Key Takeaway
The vulnerability is in the latest version of the jsonpickle library. As there are no fixes available, use of this library should be avoided. If the need to use jsonpickle still arises, ensure that jsonpickle does not handle unprocessed user data.
#jsonpickle #python #exploit
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About VRX
VRX is a consolidated vulnerability management platform that protects assets in real time. Its rich, integrated features efficiently pinpoint and remediate the largest risks to your cyber infrastructure. Resolve the most pressing threats with efficient automation features and precise contextual analysis.




