Summary: Discover 2024’s major ransomware attacks in healthcare, logistics, and manufacturing. Learn how advanced solutions like NordLayer help prevent and mitigate these threats
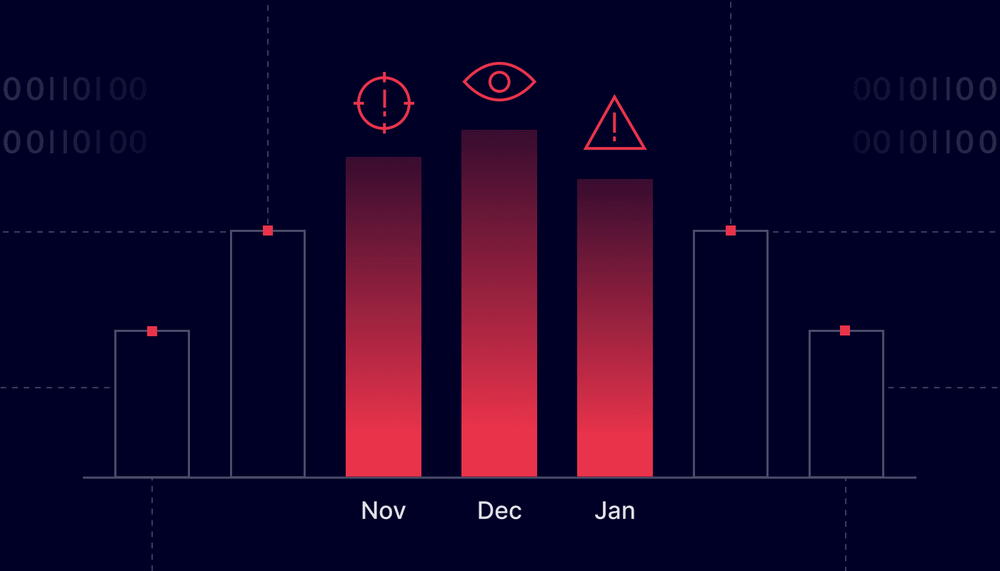
Ransomware attacks in 2024 have escalated to new heights, surpassing the scale and sophistication of threats seen in 2023. Attackers have become more aggressive than the previous year, using advanced tactics such as double and triple extortion. Organizations are not only facing encrypted files but also the threat of a data breach, with stolen data being leaked or even sold on the dark web. This increases the risks of reputational damage and regulatory penalties.
No organization is immune, and attackers now use more accessible tools like Ransomware as a Service (RaaS). Industries once considered less vulnerable, such as logistics and energy, have increasingly been in the crosshairs alongside traditionally targeted sectors like healthcare and education. This year alone, ransom payments have skyrocketed—rising from under $200,000 in early 2023 to $1.5 million in June 2024—with some organizations shelling out tens of millions of ransomware payments to regain access to their systems or prevent private data from being exposed.
In this blog post, we’ll examine the most significant ransomware incidents of 2024, their impacts, and practical measures your organization can take to strengthen cybersecurity.
Major ransomware attacks of 2024
Ransomware attacks in 2024 have become increasingly sophisticated and common, affecting industries worldwide and causing lasting financial and operational damage. Here are some of the most notable incidents of the year:
7. Healthcare: Change Healthcare
Date: February 2024
Impact: A phishing campaign exploited vulnerabilities in Change Healthcare’s email systems, deploying ransomware that encrypted critical operations. Services like claims processing and prescription drug management were disrupted across numerous U.S. hospitals, affecting thousands of providers and millions of patients.
The attackers demanded $22 million, which the company paid to restore essential services swiftly and limit disruptions to patient care. Strengthening cybersecurity has become key for healthcare providers, and tailored tools like NordLayer help safeguard personal data and ensure continuity.
6. Finance: Latitude Financial Services
Date: February 2024
Impact: Attackers stole 14 million customer records, including sensitive information like driver’s licenses, passports, and financial data. Latitude Financial decided not to pay the ransom, aligning with Australian government policies that discourage ransom payments. They stated that paying the ransom would not guarantee the secure return of data and could encourage further attacks. Instead, the company focused on restoring systems, contacting affected customers, and strengthening its cybersecurity measures.
Financial institutions can mitigate risks with NordLayer’s robust network security solutions, which safeguard critical systems and help meet regulatory compliance.
5. Non-profit: A global organization supporting orphans
Date: March 2024
Impact: A global non-profit supporting orphans (the organization’s name hasn’t been disclosed) was targeted by a ransomware group that encrypted sensitive files, including children’s photographs and medical records. The attackers initially demanded a ransom large enough to bankrupt the organization. After learning it was a non-profit, they lowered their demand.
However, this incident shows how non-profits, with limited defenses but valuable data, are becoming prime targets. Organizations can protect themselves with NordLayer’s security tools, which are tailored to address unique vulnerabilities in the sector.
4. Manufacturing: Allied Telesis
Date: May 2024
Impact: A LockBit ransomware attack encrypted corporate files and stole sensitive data dating back to 2005, disrupting operations for the telecommunications equipment manufacturer. The attackers threatened to release the stolen information if their ransom demands were unmet. The incident underlined the manufacturing sector’s vulnerability to such sophisticated threats.
This security breach is a stark reminder of the need forproactive cybersecurity measures. To mitigate risks like this, NordLayer offers tailored network security solutions for manufacturing industries to help protect critical systems and data.
3. Government: Indonesia’s National Data Center
Date: June 2024
Impact: The Brain Cipher ransomware group targeted Indonesia’s National Data Center, disrupting critical government services, including immigration processing at Jakarta’s airport. The attack encrypted sensitive data and temporarily paralyzed various government operations, highlighting the vulnerability of national infrastructure to sophisticated cyber threats.
Agencies can strengthen their defenses with NordLayer’s solutions for government institutions, designed to safeguard critical operations.
2. Software & IT: CDK Global
Date: June 2024
Impact: CDK Global, a key software provider for North American car dealerships, fell victim to a BlackSuit ransomware attack. Dealerships had to revert to manual processes for sales and paperwork, causing delays in registrations and transactions. The attack compromised sensitive customer data, such as social security numbers and bank account details, exposing millions to potential fraud.
CDK Global temporarily shut down its systems, creating substantial operational and financial challenges for dealerships dependent on its digital solutions. To speed up recovery, CDK Global reportedly paid a $25 million ransom in cryptocurrency. Despite the payment, the impact lasted about two weeks, with most systems restored by early July.
Software and IT companies can enhance security with NordLayer’s solutions, which help mitigate vulnerabilities and maintain operational efficiency.
1. Transportation: Port of Nagoya, Japan
Date: July 2024
Impact: The ransomware attack on Japan’s busiest port targeted the port’s computer systems, encrypting critical data and disrupting operations. As a result, cargo handling and customs clearance processes were severely impacted, causing shipment delays and creating a ripple effect throughout international trade networks.
The incident underscored the vulnerabilities in critical infrastructure and the need for robust cybersecurity measures in transportation. NordLayer offers tailored solutions for retail companies to protect dynamic networks and global supply chains, ensuring continuity even in the face of sophisticated threats.
These incidents highlight the urgent need for organizations to adopt comprehensive cybersecurity strategies. Ransomware attacks continue to grow in both sophistication and impact, making it crucial to counter these evolving threats.
Online threats keep evolving
Ransomware attacks are growing in sophistication, using tactics like double extortion, where stolen data is threatened with public release unless a ransom is paid. The increasing accessibility of Ransomware as a Service (RaaS) has lowered the entry barrier, enabling less-skilled cybercriminals to execute high-impact attacks with more frequently.
Key trends in 2024 include:
- Higher ransom demands: The financial stakes are higher than ever. Ransom payments in 2024 are now exceeding $10 million in many cases, with some organizations facing demands well beyond that. Attackers are increasingly targeting organizations with high-value data or critical infrastructure, knowing the urgency to recover will push companies to pay.
- Target expansion: While healthcare, finance, and education have long been prime targets for ransomware groups, other critical sectors like logistics and energy are now in the crosshairs. As supply chains and energy grids become more interconnected and reliant on digital systems, these industries face greater risks of disruptions with global consequences.
- Advanced tactics: Ransomware groups are not only focusing on traditional on-premise networks but also exploiting vulnerabilities in cloud environments, which is becoming a bigger concern. This highlights the need for more advanced, tailored security solutions.
These trends show how ransomware incidents are becoming more sophisticated and multifaceted. This increases the potential for significant damage and calls for organizations to adopt more comprehensive, layered defense strategies.
Protecting against ransomware threats

A comprehensive strategy involves protecting not just your systems but also your data and network infrastructure. Each layer of defense plays a crucial role in minimizing the impact of a ransomware attack and preventing it from escalating. Below are essential strategies organizations should adopt:
1. Identify vulnerabilities and patch systems
Many ransomware attacks exploit vulnerabilities in outdated systems. To address known vulnerabilities and maintain a secure network, regularly update software. Ensure that all systems—operating systems, applications, and firmware—are consistently patched. This process should include automated updates where feasible, and IT teams should conduct routine vulnerability scans to identify and fix any weak points before they can be exploited.
2. Use endpoint detection
Use endpoint security solutions to identify and neutralize threats early. These tools not only detect ransomware but also offer insights into the nature of the attack, helping teams understand how it infiltrated the network. Ensure these solutions are configured to alert IT staff of suspicious activity and automatically block unauthorized file encryption attempts.
3. Implement multi-factor authentication (MFA)
MFA adds an extra layer of security, ensuring only authorized users can access sensitive systems, especially those handling sensitive or critical data. By requiring additional verification steps, such as a mobile authentication app, biometric verification, or a hardware token, MFA helps prevent unauthorized access even if login credentials are compromised.
4. Segment the network
Network segmentation isolates critical systems, much like fire doors prevent the spread of fire in a building. This limits the spread of ransomware within the network and minimizes potential damage. You can achieve it by segmenting critical applications, databases, and other high-value assets into subnets with strict access controls.
5. Backup data regularly
Frequent backups of important data should be a cornerstone of your ransomware defense strategy. Regularly schedule backups and ensure they are stored in secure, immutable formats that prevent tampering. The 3-2-1 rule—three copies of data, two different storage types, and one off-site—can provide extra security. Verify the integrity of backups periodically and run simulated recovery drills to confirm that data can be restored efficiently in case of an attack.
6. Train employees
Educate staff on recognizing phishing and other tactics used by ransomware groups. Awareness is a vital defense against social engineering attacks. Beyond that, offer comprehensive training on recognizing signs of suspicious activity, safe browsing practices, and the importance of reporting incidents promptly. Consider including scenario-based training that immerses employees in real-world attack simulations, reinforcing proper responses in a controlled environment.
7. Get cyber insurance
Cyber insurance can help organizations recover financial losses from a ransomware attack, including ransom payments, recovery costs, and legal fees. Cyber insurance can be an important financial safety net, but it’s not a substitute for solid security practices. Make sure the policy clearly defines what qualifies an insurable event and what documentation or proof is required for claims.
How NordLayer enhances security
NordLayer aligns closely with the recommended strategies to protect against ransomware:
1. Identity vulnerabilities and patch systems. With the Device Posture Security (DPS) feature, NordLayer identifies device types and their operating system versions accessing sensitive data. DPS provides timely notifications when a device with an outdated OS version connects to the network, enabling proactive measures such as restricting access to private gateways for devices that don’t meet security rules.
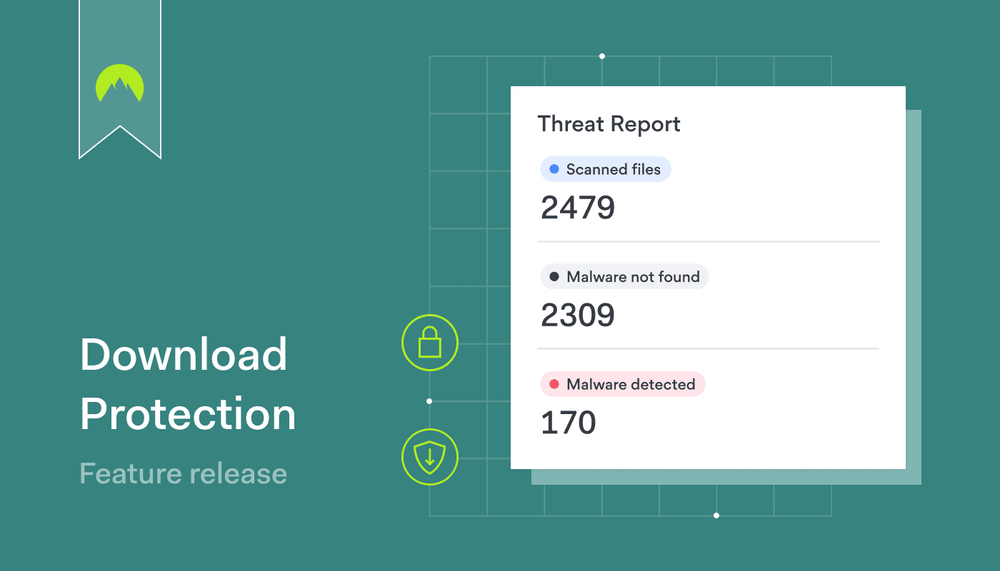
2. Endpoint protection. NordLayer offers Download Protection to block malicious files before they can infect devices and spread malware, which could lead to ransomware attacks.
3. Implement multi-factor authentication (MFA). NordLayer facilitates advanced authentication layers to bolster Zero Trust Network Access (ZTNA). Beyond basic MFA, NordLayer supports additional methods like Single Sign-On (SSO), IP allowlisting, and encrypted connections, ensuring that access to sensitive systems remains secure.
4. Segment the network. Customers can implement granular network segmentation Using Access Control Lists (ACL) within NordLayer’s Cloud Firewall tool. This isolates critical applications and high-value assets, minimizing lateral movement and potential damage in case of a breach.
5. Backup data. While NordLayer does not directly handle backups, its security measures protect access to systems where backups are stored.
6. Cyber insurance. Although NordLayer does not directly offer cyber insurance, pairing NordLayer with NordProtect provides a comprehensive solution for securing critical infrastructure.
By integrating these features, NordLayer supports organizations in addressing ransomware threats while reinforcing their overall security framework.
Lessons from 2024
The top ransomware attacks of 2024 are a stark reminder that no organization is immune to ransomware threats. Whether it’s healthcare organizations, financial firms, or critical infrastructure, the potential for a data breach remains high.
By adopting proactive measures and advanced cybersecurity solutions like NordLayer, businesses can strengthen their defenses and minimize the impact of ransomware attacks. As the threat landscape evolves, staying ahead of cybercriminals is not just a necessity—it’s a responsibility.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.