Can any employee access company resources from anywhere and at any time? It depends on the company’s infrastructure. Recently established businesses have more chances to provide access wherever their teams are. However, companies with legacy architectures need to readapt to have the same time and place flexibility.
Every company infrastructure setup is unique. Therefore, it may require a different approach to solving the same challenges — like how users can access office-based data, applications, or devices while not being present on that particular site.
The most common solution is to choose VPN for security purposes and enablement of distributed teams. However, the VPN selection depends on its type and existing company network arrangement.
If your target is to enable employees to securely connect to different offices and branches of the organization despite being elsewhere, Site-to-Site VPN is the option to explore.
Site-to-Site solution using NordLayer
Site-to-Site allows users to reach office-bind resources on HQ, your assigned office, or another company branch while not actually being on-site. It is a type of VPN that establishes an encrypted connection to a requested resource on the company network.
NordLayer’s cloud-based feature elevates typical industry Site-to-Site capabilities by connecting not just different corporate sites and resources but by enabling both on-site present and remote users to connect to any company resource on the network.
Therefore, connection to a single physical location via a virtual private gateway using VPN translates into user connection to all devices and resources assigned to a company router or firewall.
How does NordLayer’s Site-to-Site feature work?
The cloud-based feature can be enabled by connecting NordLayer’s virtual private gateway to the company’s router or firewall.
Moreover, cloud-based Site-to-Site makes it possible to configure a dedicated VPN server to connect to cloud service providers like Amazon AWS, Google Cloud, or Azure.
Users with VPN access – whether present in the branch office, HQ, or remote – can connect to the company network and access the added internal resources and the on-site devices connected to the router/firewall, even though they don’t support a VPN connection.
Remote user connection:

Connection from a company branch:

Connection from HQ:

NordLayer’s Site-to-Site feature requires virtual private gateways and physical location configuration. Once it’s ready, a VPN connects users to the local company network and allows them to access company resources like applications, data, computers, or printers.
The same logic applies to users accessing the company’s cloud service provider resources. VPN established connection and router/firewall configuration to support IKEv2 Site-to-Site functionality with a static public IP address can provide access to resources for employees despite their location.
Shortly, suppose an employee for a job needs to access your organization’s customer information stored in a database located in HQ, the email server that stands in an office branch on another continent and needs to print it out while working from home. In that case, it’s all available via NordLayer’s Site-to-Site VPN functionality.
How NordLayer’s Site-to-Site is different?
Traditional WAN companies have an architecture based on an all-to-one setup when business units – remote locations and resources of the corporate – are connected to one main point.
Such organizations exploit extensive legacy Site-to-Site architectures that employees use to connect to the network’s main point, allowing them to access company-enclosed resources from different locations. This type of network architecture delivers interconnectivity yet lacks remote flexibility and has downsides affecting network performance, efficiency, and scalability.
As a solution to legacy Site-to-Site, NordLayer is developed to provide flexible and simple problem-solving to the general downsides of using legacy networking. When focusing on the feature functionality, the distinction between legacy setup and cloud-based remote network access solution comes from overcoming the limitations of traditional Site-to-Site solutions.
Cloud-based NordLayer solution handles legacy infrastructure challenges of increasing remote connections with quick integration to the existing architecture. It reverts performance–efficiency–scalability limitations to company advantage:
Decreased deployment time and expenses. NordLayer solution is fully hardware-free and compatible with hardware-based or hybrid existing infrastructures. Functionalities can be deployed within minutes and don’t require complex costs and long delivery times, focusing on time-to-value for the organization.
Maintained security and productivity levels. NordLayer Site-to-Site distributes encrypted user traffic to company resources based on the request nature without affecting connection quality instead of bulk processing all users to a primary point of connection and allocating to requested resources afterward.
User traffic distribution. The feature decreases the heavy traffic load directing users to the internet resources, internal data centers, servers, or applications in a more streamlined manner. Therefore, the increased remote user traffic peaks don’t impact performance quality as with a traditional Site-to-Site setup.
Efficiency and scalability. Naturally, user traffic distribution significantly reduces on-site equipment use managing the ad-hoc demand to upgrade. On the contrary, cloud-based Site-to-Site functionality enables the company to scale on demand without resource-intensive planning.
The feature brings another level to team performance in business operations using Site-to-Site. NordLayer’s cloud-based feature ‘helps cut hardware-ing and distance corners’, bringing efficiency to secure data sharing and authorized access of on-site devices within the organizations, even if physically impossible.
Benefits of Site-to-Site VPN
Primarily, Site-to-Site VPN allows for establishing non-office-only based connections. The VPN enables secure data transfers and trusted user activity between the on-premise network and the public network established over the internet.
Implementing NordLayer on top of your existing infrastructure, Site-to-Site unlocks effective and robust cybersecurity measures for various organizational aspects.
Increased network security
Sensitive data and confidential information is the target of most cyber attacks. Thus, encrypted data transfers between organization members utilizing Site-to-Site, whether in the office or remote, help safeguard against data breaches.
Streamlined business operations
Team performance is heavily related to the availability and capacity of the company network. Therefore, Site-to-Site feature maintains a good speed and stable data traffic flow to provide users with quality connectivity and constant access to resources that influence business continuity.
Flexible and scalable protection
Hardware-free Site-to-Site configuration is a beneficial add-on to the existing company network, even the largely hardware-based ones. Thus, the reaction-to-action time to solve ad-hoc challenges is multiple times shorter and easier. It requires minimal resources and provides a solution based on business needs within minutes.
Entering NordLayer’s Site-to-Site
NordLayer solution provides a modern approach-based Site-to-Site VPN. The feature allows present and remote employees to access data and devices in multiple corporate environments.
Using our remote network access solution to enable Site-to-Site VPN for the organization, IT admins have to follow simple actions to configure the feature. First, they need to create VPN gateways via the Control Panel as entry points into the network and assign teams or role-based employees to access the gateway so they can enter the company network. Site-to-Site has to be configured for every company unit for the seamless cooperation of teams.
With fewer systems to manage, unlimited scalability, flexibility, and easy setup, companies can ensure smooth and productive connections for their users and maintain high-security levels of the business.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
These days, cybercrime is rampant. It’s no longer a matter of “if” you’re going to suffer an attack but “when” it will happen. All companies want to be ready for any crisis. And this is where a business continuity plan comes into play.
But what is a business continuity plan exactly? Why is it important? What should one include? Today, we’re exploring all these questions in-depth.
What is a business continuity plan?
A business continuity plan (BCP) is a document that sets guidelines for how an organization will continue its operations in the event of a disruption, whether it’s a fire, flood, other natural disaster or a cybersecurity incident. A BCP aims to help organizations resume operations without significant downtime.
Unfortunately, according to a 2020 Mercer survey, 51% of businesses across the globe don’t have a business continuity plan in place.
What’s the difference between business continuity and disaster recovery plans?
We often confuse the terms business continuity plan and disaster recovery plan. The two overlap and often work together, but the disaster recovery plan focuses on containing, examining, and restoring operations after a cyber incident. On the other hand, BCP is a broader concept that considers the whole organization. A business continuity plan helps organizations stay prepared for dealing with a potential crisis and usually encompasses a disaster recovery plan.
Importance of business continuity planning
The number of news headlines announcing data breaches has numbed us to the fact that cybercrime is very real and frequent and poses an existential risk to companies of all sizes and industries.
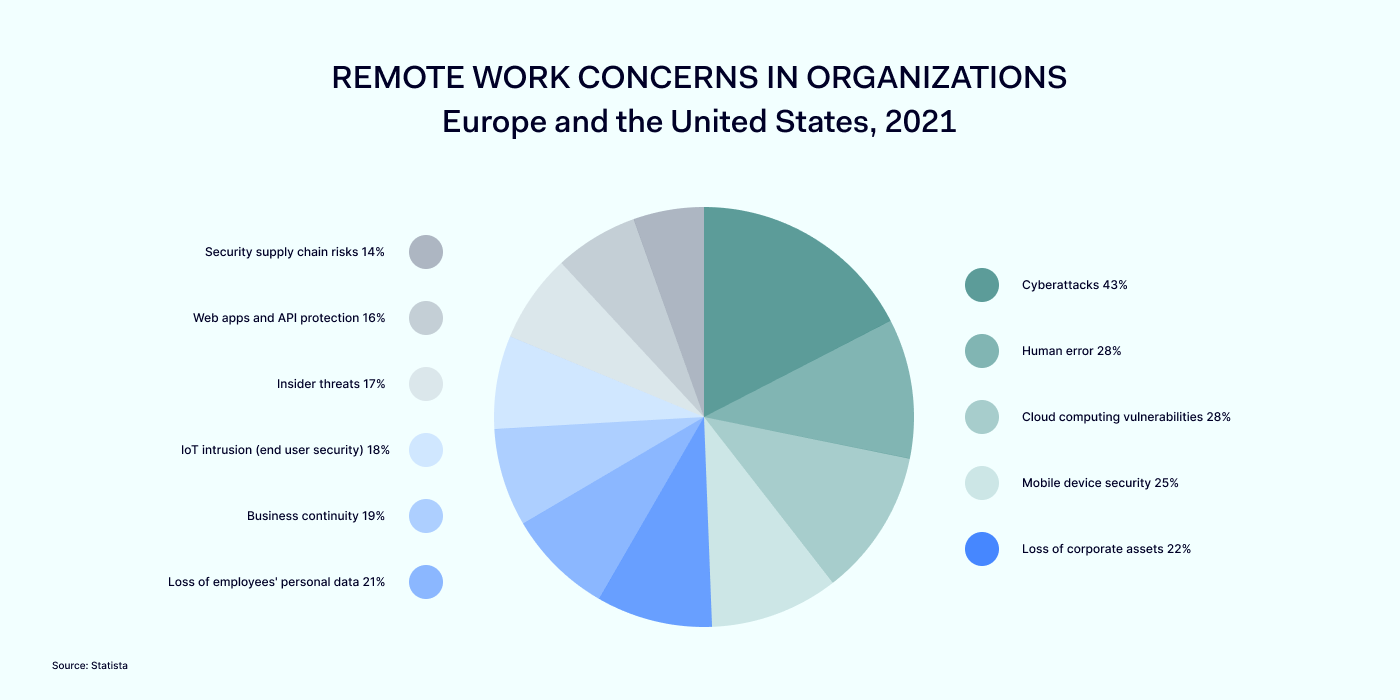
Consider that in 2021, approximately 37% of global organizations fell victim to a ransomware attack. Then consider that business interruption and restoration costs account for 50% of cyberattack-related losses. Finally, take into account that most cyberattacks are financially motivated and the global cost of cybercrime topped $6 trillion last year. The picture is quite clear — cybercrime is a lucrative venture for bad actors and potentially disastrous for those on the receiving end.
To thrive in these unpredictable times, organizations go beyond conventional security measures. Many companies develop a business continuity plan parallel to secure infrastructure and consider the plan a critical part of the security ecosystem. The Purpose of a business continuity plan is to significantly reduce the downtime in an emergency and, in turn, reduce the potential reputational damage and — of course — revenue losses.
Business continuity plan template
Password security for your business
Store, manage and share passwords.
30-day money-back guarantee
Business Continuity Plan Example
[Company Name]
[Date]
I. Introduction
Purpose of the Plan
Scope of the Plan
Budget
Timeline
The initial stage of developing a business continuity plan starts with a statement of the plan’s purpose, which explains the main objective of the plan, such as ensuring the organization’s ability to continue its operations during and after a disruptive event.
The Scope of the Plan outlines the areas or functions that the plan will cover, including business processes, personnel, equipment, and technology.
The Budget specifies the estimated financial resources required to implement and maintain the BCP. It includes costs related to technology, personnel, equipment, training, and other necessary expenses.
The Timeline provides a detailed schedule for developing, implementing, testing, and updating the BCP.
II. Risk Assessment
Identification of Risks
Prioritization of Risks
Mitigation Strategies
The Risk Assessment section of a Business Continuity Plan (BCP) is an essential part of the plan that identifies potential risks that could disrupt an organization’s critical functions.
The Identification of Risks involves identifying potential threats to the organization, such cybersecurity breaches, supply chain disruptions, power outages, and other potential risks. This step is critical to understand the risks and their potential impact on the organization.
Once the risks have been identified, the Prioritization of Risks follows, which helps determine which risks require the most attention and resources.
The final step in the Risk Assessment section is developing Mitigation Strategies to minimize the impact of identified risks. Mitigation strategies may include preventative measures, such as system redundancies, data backups, cybersecurity measures, as well as response and recovery measures, such as emergency protocols and employee training.
III. Emergency Response
Emergency Response Team
Communication Plan
Emergency Procedures
This section of the plan focuses on immediate actions that should be taken to ensure the safety and well-being of employees and minimize the impact of the event on the organization’s operations.
The Emergency Response Team is responsible for managing the response to an emergency or disaster situation. This team should be composed of individuals who are trained in emergency response procedures and can act quickly and decisively during an emergency. The team should also include a designated leader who is responsible for coordinating the emergency response efforts.
The Communication Plan outlines how information will be disseminated during an emergency situation. It includes contact information for employees, stakeholders, and emergency response personnel, as well as protocols for communicating with these individuals.
The Emergency Procedures detail the steps that should be taken during an emergency or disaster situation. The emergency procedures should be developed based on the potential risks identified in the Risk Assessment section and should be tested regularly to ensure that they are effective.
IV. Business Impact Analysis
The Business Impact Analysis (BIA) section of a Business Continuity Plan (BCP) is a critical step in identifying the potential impact of a disruption to an organization’s critical operations.
The Business Impact Analysis is typically conducted by a team of individuals who understand the organization’s critical functions and can assess the potential impact of a disruption to those functions. The team may include representatives from various departments, including finance, operations, IT, and human resources.
V. Recovery and Restoration
Procedures for recovery and restoration of critical processes
Prioritization of recovery efforts
Establishment of recovery time objectives
The Recovery and Restoration section of a Business Continuity Plan (BCP) outlines the procedures for recovering and restoring critical processes and functions following a disruption.
The Procedures for recovery and restoration of critical processes describe the steps required to restore critical processes and functions following a disruption. This may include steps such as relocating to alternate facilities, restoring data and systems, and re-establishing key business relationships.
The Prioritization section of the plan identifies the order in which critical processes will be restored, based on their importance to the organization’s operations and overall mission.
Recovery time objectives (RTOs) define the maximum amount of time that critical processes and functions can be unavailable following a disruption. Establishing RTOs ensures that recovery efforts are focused on restoring critical functions within a specific timeframe.
VI. Plan Activation
Plan Activation Procedures
The Plan Activation section is critical in ensuring that an organization can quickly and effectively activate the plan and respond to a potential emergency.
The Plan Activation Procedures describe the steps required to activate the BCP in response to a disruption. The procedures should be clear and concise, with specific instructions for each step to ensure a prompt and effective response.
VII. Testing and Maintenance
Testing Procedures
Maintenance Procedures
Review and Update Procedures
This section of the plan is critical to ensure that an organization can effectively respond to disruptions and quickly resume its essential functions.
Testing procedures may include scenarios such as natural disasters, cyber-attacks, and other potential risks. The testing procedures should include clear objectives, testing scenarios, roles and responsibilities, and evaluation criteria to assess the effectiveness of the plan.
The Maintenance Procedures detail the steps necessary to keep the BCP up-to-date and relevant.
The Review and Update Procedures describe how the BCP will be reviewed and updated regularly to ensure its continued effectiveness. This may involve conducting a review of the plan on a regular basis or after significant changes to the organization’s operations or threats.
What should a business continuity plan checklist include?
Organizations looking to develop a BCP have more than a few things to think through and consider. Variables such as the size of the organization, its IT infrastructure, personnel, and resources all play a significant role in developing a continuity plan. Remember, each crisis is different, and each organization will have a view on handling it according to all the variables in play. However, all business continuity plans will include a few elements in one way or another.
Clearly defined areas of responsibility
A BCP should define specific roles and responsibilities for cases of emergency. Detail who is responsible for what tasks and clarify what course of action a person in a specific position should take. Clearly defined roles and responsibilities in an emergency event allow you to act quickly and decisively and minimize potential damage.
Crisis communication plan
In an emergency, communication is vital. It is the determining factor when it comes to crisis handling. For communication to be effective, it is critical to establish clear communication pipelines. Furthermore, it is crucial to understand that alternative communication channels should not be overlooked and outlined in a business continuity plan.
Recovery teams
A recovery team is a collective of different professionals who ensure that business operations are restored as soon as possible after the organization confronts a crisis.
Alternative site of operations
Today, when we think of an incident in a business environment, we usually think of something related to cybersecurity. However, as discussed earlier, a BCP covers many possible disasters. In a natural disaster, determine potential alternate sites where the company could continue to operate.
Backup power and data backups
Whether a cyber event or a real-life physical event, ensuring that you have access to power is crucial if you wish to continue operations. In a BCP, you can often come across lists of alternative power sources such as generators, where such tools are located, and who should oversee them. The same applies to data. Regularly scheduled data backups can significantly reduce potential losses incurred by a crisis event.
Recovery guidelines
If a crisis is significant, a comprehensive business continuity plan usually includes detailed guidelines on how the recovery process will be carried out.
Business continuity planning steps
Here are some general guidelines that an organization looking to develop a BCP should consider:
Analysis
A business continuity plan should include an in-depth analysis of everything that could negatively affect the overall organizational infrastructure and operations. Assessing different levels of risk should also be a part of the analysis phase.
Design and development
Once you have a clear overview of potential risks your company could face, start developing a plan. Create a draft and reassess it to see if it takes into account even the smallest of details.
Implementation
Implement BCP within the organization by providing training sessions for the staff to get familiar with the plan. Getting everyone on the same page regarding crisis management is critical.
Testing
Rigorously test the plan. Play out a variety of scenarios in training sessions to learn the overall effectiveness of the continuity plan. By doing so, everyone on the team will be closely familiar with the business continuity plan’s guidelines.
Maintenance and updating
Because the threat landscape constantly changes and evolves, you should regularly reassess your BCP and take steps to update it. By making your continuity plan in tune with the times, you will be able to stay a step ahead of a crisis.
Level up your company’s security with NordPass Business
A comprehensive business continuity plan is vital for the entire organization’s security posture. However, in a perfect world, you wouldn’t have to use it. This is where NordPass Business can help.
Remember, weak, reused, or compromised passwords are often cited as one of the top contributing factors in data breaches. It’s not surprising, considering that an average user has around 100 passwords. Password fatigue is real and significantly affects how people treat their credentials. NordPass Business counters these issues.
With NordPass Business, your team will have a single secure place to store all work-related passwords, credit cards, and other sensitive information. Accessing all the data stored in NordPass is quick and easy, which allows your employees not to be distracted by the task of finding the correct passwords for the correct account.
In cyber incidents, NordPass Business ensures that company credentials remain secure at all times. Everything stored in the NordPass vault is secured with advanced encryption algorithms, which would take hundreds of years to brute force.
If you are interested in learning more about NordPass Business and how it can fortify corporate security, do not hesitate to book a demo with our representative.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordPass
NordPass is developed by Nord Security, a company leading the global market of cybersecurity products.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.