- ESET researchers discovered a new NGate malware variant abusing the legitimate Android HandyPay application.
- To trojanize HandyPay, threat actors most likely used GenAI.
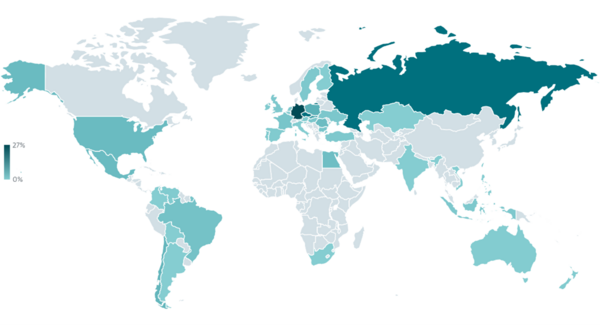
- The campaign has been ongoing since November 2025 and targets Android users in Brazil.
- ESET investigated two NGate samples being distributed in the attacks: one via a fake lottery website, the other through a fake Google Play website.
BRATISLAVA — April 21, 2026 — ESET Research has discovered a new variant of the NGate malware family that abuses a legitimate Android application called HandyPay, instead of the previously leveraged NFCGate tool. The threat actors took the app, which is used to relay NFC data, and patched it with malicious code that appears to have been AI generated. As with previous iterations of NGate, the malicious code allows the attackers to transfer NFC data from the victim’s payment card to their own device and use them for contactless ATM cash-outs and unauthorized payments. Additionally, the code can capture the victims’ payment card PINs and exfiltrate them to the operators’ C&C server. The primary targets of this are users in Brazil; however, NFC-based attacks are expanding into new regions.
The malicious code used to trojanize HandyPay shows signs of having been produced with the help of GenAI tools. Specifically, the malware logs contain an emoji typical of AI-generated text, suggesting that LLMs were involved in generating or modifying the code, although definitive proof remains elusive. This fits a broader trend in which GenAI lowers the barrier to entry for cybercriminals, enabling threat actors with limited technical skill to produce workable malware.
ESET Research believes that the campaign distributing the trojanized HandyPay began around November 2025 and remains active. It should also be noted that the maliciously patched version of HandyPay has never been available on the official Google Play store. As an App Defense Alliance partner, we shared our findings with Google. ESET also reached out to the HandyPay developers to alert them about the malicious use of their application.
As the number of NFC threats keeps rising, so too has the ecosystem supporting them become more robust. The first NGate attacks employed the open-source NFCGate tool to facilitate the transfer of NFC data. Since then, several malware-as-a-service (MaaS) offerings with similar functionality have become available for purchase. However, in this campaign the threat actors decided to go with their own solution and maliciously patched an existing app – HandyPay.
“Why did the operators of this campaign decide to trojanize the HandyPay app instead of going with an established solution for relaying NFC data? The answer is simple: money. The subscription fees for existing MaaS kits run in the hundreds of dollars: NFU Pay advertises its product for almost US$400 per month, while TX-NFC goes for around US$500 per month. On the other hand, the legitimate HandyPay app is significantly cheaper, only asking for a €9.99 per month donation, if even that. In addition to the price, HandyPay natively does not require any permissions, only to be made the default payment app, helping the threat actors avoid raising suspicion,” says ESET researcher Lukáš Štefanko, who discovered the new NGate variant in the trojanized NFC payment app.
The first new NGate sample is distributed through a website that impersonates Rio de Prêmios, a lottery run by the Rio de Janeiro state lottery organization (Loterj). The second NGate sample is distributed via a fake Google Play web page as an app named Proteção Cartão (machine translation: Card Protection). Both sites were hosted on the same domain, strongly implying a single threat actor. The malware abuses the HandyPay service to forward NFC card data to an attacker-controlled device. Apart from relaying NFC data, the malicious code also steals payment card PINs, enabling the threat actor to use the victim’s payment card data to withdraw cash from ATMs.
For a more detailed analysis of the new NGate variant, check out the latest ESET Research blog post, “New NGate variant hides in a trojanized NFC payment app,” on WeLiveSecurity.com. Make sure to follow ESET Research on Twitter (today known as X), BlueSky, and Mastodon for the latest news from ESET Research.
Geographical distribution of NGate attacks from January 2025 to February 2026
About ESET
For 30 years, ESET® has been developing industry-leading IT security software and services for businesses and consumers worldwide. With solutions ranging from endpoint security to encryption and two-factor authentication, ESET’s high-performing, easy-to-use products give individuals and businesses the peace of mind to enjoy the full potential of their technology. ESET unobtrusively protects and monitors 24/7, updating defenses in real time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company. Backed by R&D facilities worldwide, ESET became the first IT security company to earn 100 Virus Bulletin VB100 awards, identifying every single “in-the-wild” malware without interruption since 2003.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.