INDIANAPOLIS – December 11, 2023 — Scale Computing, a market leader in edge computing, virtualization, and hyperconverged solutions, today announced that CRN®, a brand of The Channel Company, is recognizing its Scale Computing Platform (SC//Platform) as the overall winner in the 2023 Products of the Year Awards in the Converged/Hyperconverged Infrastructure category, as well as a winner in the Technology subcategory. Scale Computing Fleet Manager (SC//Fleet Manager) was also named a winner in the Customer Need subcategory of the Edge Computing/IoT category.
The CRN Products of the Year Awards honor leading IT products and services that represent the most cutting-edge technologies in the channel today. Winners in this year’s Products of the Year Awards represent innovative offerings that meet the ever-changing needs of the IT channel and their customers across 33 technology categories.
The 2023 Products of the Year finalists were selected by the CRN editorial team. Solution providers with real-world experience with the offerings then scored the products on three criteria: Technology, Revenue and Profit, and Customer Need. The product that received the highest overall score in each technology category was named the winner.
“Scale Computing’s comprehensive partner program provides MSPs and resellers with unlimited growth potential, superior technology, and world-class support. As a partner-first organization, we proudly offer innovative solutions that help customers reduce complexity and costs so they can focus on other business initiatives,” said Jeff Ready, CEO and co-founder, Scale Computing. “We are thrilled to be honored as a winner in the CRN Product of the Year Awards in both the Converged/Hyperconverged Infrastructure category and the Edge Computing/IoT category. We continue to be committed to providing reliable, highly available, simple, and scalable IT infrastructure solutions.”
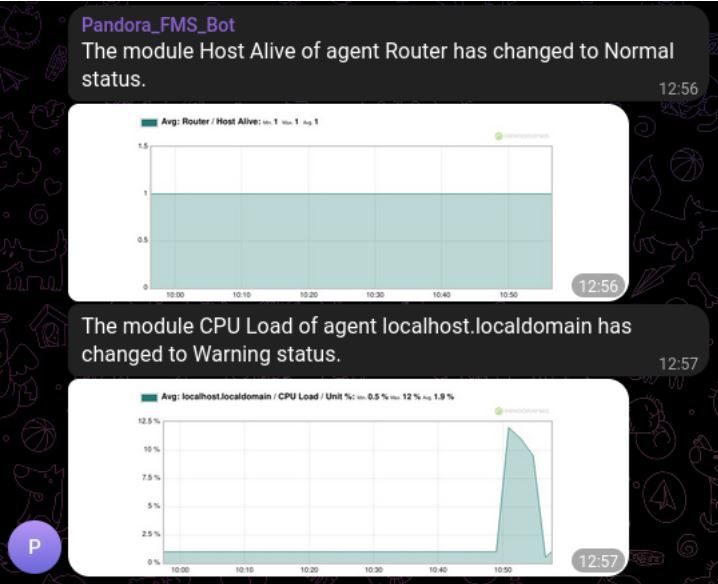
SC//Platform brings simplicity, high availability, and scalability together, replacing the existing infrastructure for running virtual machines in a single, easy-to-manage platform. SC//Fleet Manager, the industry’s first cloud-basedhosted monitoring and management tool built for hyperconverged edge computing infrastructure at scale, allows customers to quickly identify areas of concern using a single pane of glass, scaling from 1 to over 50,000 clusters. Zero-touch provisioning and Secure Link features allow administrators to centrally and securely monitor and manage hundreds or thousands of distributed edge infrastructure deployments, with few or no on-site IT personnel.
“The CRN Products of the Year Awards are among the most highly anticipated industry accolades in the IT channel, in large part because they are based on the real-world experience of solution providers that work with the technology day in and day out. This year’s winning vendors go to market with a strong focus on the channel and a demonstrated commitment to attaining product excellence that brings advantages to both partners and customers,” said Jennifer Follett, Vice President, U.S. Content and Executive Editor, CRN, at The Channel Company.
The 2023 CRN Products of the Year Awards will be featured in the December issue of CRN Magazine and published online at CRN.com/poty. For more information on SC//Platform and SC//Fleet Manager, please visit scalecomputing.com/sc-platform.
About Scale Computing
Scale Computing is a leader in edge computing, virtualization, and hyperconverged solutions. Using patented HyperCore™ technology, Scale Computing Platform automatically identifies, mitigates, and corrects infrastructure problems in real-time, enabling applications to achieve maximum uptime, even when local IT resources and staff are scarce. Edge Computing is the fastest-growing area of IT infrastructure, and industry analysts have named Scale Computing an outperformer and leader in the space, including being named the #1 edge computing vendor by CRN. Scale Computing’s products are sold by thousands of value-added resellers, integrators, and service providers worldwide. When ease-of-use, high availability, and TCO matter, Scale Computing Platform is the ideal infrastructure platform. Read what our customers have to say on Gartner Peer Insights, G2, and TrustRadius.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About Scale Computing
Scale Computing is a leader in edge computing, virtualization, and hyperconverged solutions. Scale Computing HC3 software eliminates the need for traditional virtualization software, disaster recovery software, servers, and shared storage, replacing these with a fully integrated, highly available system for running applications. Using patented HyperCore™ technology, the HC3 self-healing platform automatically identifies, mitigates, and corrects infrastructure problems in real-time, enabling applications to achieve maximum uptime. When ease-of-use, high availability, and TCO matter, Scale Computing HC3 is the ideal infrastructure platform. Read what our customers have to say on Gartner Peer Insights, Spiceworks, TechValidate and TrustRadius.