Transparency, speed, and high levels of trust make blockchains an increasingly popular option. Those benefits are well-recognized among forward-thinking businesses. However, blockchain security issues are much less prominent, and that’s a problem. Read on to discover common blockchain risks and use our best practices to secure every link in the chain.
Key takeaways
Blockchains are decentralized ledgers consisting of blocks with unique cryptographic hashes. The blocks form an immutable chain that every user can inspect. This transparency enhances trust and integrity in information transmission.
Blockchain security is coming into focus as the technology becomes mainstream. Threats include man-in-the-middle, Sybil, and 51 attack types that exploit insecure nodes. Blockchains are vulnerable to traditional phishing and endpoint vulnerabilities. Smart contracts and poorly designed routing systems also put blockchains at risk.
Mitigate threats by following blockchain security best practices. Users should implement robust encryption and Identity and Access Management (IAM) solutions. Secure development practices, multi-signature wallets, fail-safes, regular audits, and Zero Trust Security solutions mitigate blockchain security risks.
Blockchains are decentralized digital ledgers that record transactions between different devices or individuals. Chains consist of “blocks”. Each block has a unique cryptographic hash. Subsequent blocks create hashes based on previous blocks, generating a chain where each entry is connected but unique.
Blockchains are tough to change after creating blocks. This immutability makes them a good fit for verifying information transmission. Participants can see information about block generation, making the process extremely transparent.
Analysts project the global blockchain market will grow to $40 billion by 2025, and use cases will multiply. Secure information exchange, digital identification, and tracing financial transactions are just a few areas emerging blockchain technologies are disrupting.
However, as with all new digital technologies, decentralized ledgers potentially pose critical security risks. Hackers routinely use untraceable crypto wallets to mount ransomware attacks. Consensus protocols that establish ledger entries are vulnerable to attack. Poorly designed smart contracts can also put businesses at risk.
This article will take a closer look at blockchain security issues. We will explore how blockchains work and discuss how you can safely capitalize on blockchain technology.
Introducing the main types of blockchain
Blockchains are defined by whether they use public or private keys to verify transactions.
Public blockchain networks are accessible to everyone. Cryptocurrencies like Ethereum or BitCoin fall into this category. Public systems create public and private keys for blockchain participants. The public key enables users to engage transparently with other currency holders, while the private key protects their digital wallets.
Public blockchain technology is decentralized, with no single controlling entity. Decentralization promotes trust among participants and makes the blockchain more resilient. Distributed ledgers are hard to tamper with, as changes need approval from the user community. They also enable access for customers or larger user groups.
Private keys are limited to a defined community of users. Each authorized user receives a private key. Digital signatures based on this key verify interactions with the blockchain ledger.
Private blockchain security ensures control and confidentiality for the blockchain owner, making it suitable for many enterprise uses. However, private blockchains can be vulnerable to insider attacks. Attackers can also exploit centralized chains, using the blockchain controller as an attack vector.
Exploring blockchain security issues
Users often think blockchains guarded by encryption are safer than traditional information transfer systems. Ledgers supposedly make tampering difficult. In theory, changing data blocks without authorization is unlikely without a user’s private keys.
However, there are questions about this reputation for security. Blockchains can put sensitive data at risk, resulting in significant financial losses or data exposure. Companies adopting private or public blockchain solutions should thoroughly assess their security vulnerabilities.
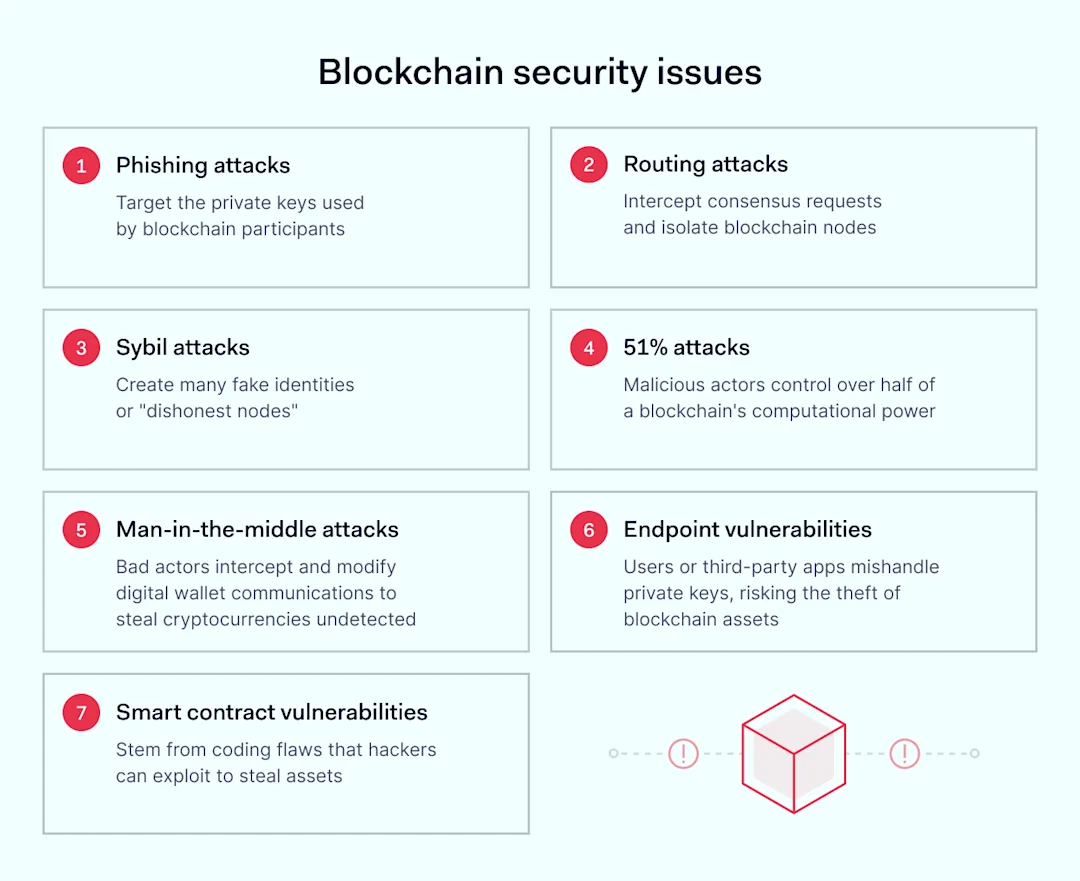
Phishing attacks
Blockchains are as vulnerable to phishers as traditional networks. In this case, phishing attacks target the private keys used by blockchain participants. Cunning attackers persuade key holders to hand over the passwords used as ciphers for private key hashes. When they get the key, hackers can make transactions, extract information, and ruin the integrity of blockchain ledgers.
Solution: The best remedy for phishing attacks is improving employee security training. Include blockchain security issues in cybersecurity training. Every ledger user should know the risks of sharing their private keys.
Routing attacks
Blockchains rely on consensus mechanisms to establish the legitimacy of transactions. However, attackers can use routing attacks to intercept consensus requests and isolate blockchain nodes. Isolated nodes can’t make transactions or ledger changes. Attackers can slow down business processes and launch damaging 51% of attacks (please see below).
Solution: Organizations can cut the risk of routing attacks by protecting blockchain communications with strong encryption and using network monitoring tools to identify suspicious traffic patterns.
Sybil attacks
Sybil attacks create many fake identities or “dishonest nodes.” Dishonest nodes seem authentic to blockchain users (“honest nodes”). However, dishonest nodes enable attackers to control network traffic. They can then force honest nodes to act against their interests.
Sybil attacks enable attackers to leech sensitive information about blockchain users (IP data, for example). Malicious actors can also block new transactions, effectively holding users to ransom.
Solution: Fortunately, Sybil attacks are usually easy to detect. They tend to affect blockchain operators with weak validation and monitoring systems. Ensure you have robust measures in place to authenticate every node.
51% attacks
In 51% of attacks, malicious actors control over half of a blockchain’s computational power. Control matters because attackers can then dominate how the ledger functions.
The most common method involves creating fake “pools” and enticing legitimate users to join. The attacker separates this pool from the original ledger, creating a second parallel blockchain. Attackers then leverage their pool to add blocks faster than users on the original chain.
Problems arise when hackers reintegrate the fake blockchain with the original. If standard rules apply, the largest blockchain becomes the default version. Rules may reverse transactions on the legitimate ledger, eroding user trust.
During a 51% attack, the blockchain is no longer fully decentralized or transparent. A single user can change ledger entries and block additions and potentially force double transactions, leeching money from currency users. For example, in 2020, Ethereum Classic suffered three 51% attacks. Each attack cost currency holders $9 million through double transactions.
Solution: Organizations can cut the risk of 51% attacks by switching from proof-of-work (PoW) consensus algorithms to proof-of-stake (PoS) algorithms. Slowing down transaction confirmations can also make attacks prohibitively expensive.
Man-in-the-middle attacks
Hackers use man-in-the-middle attacks to place themselves between users and digital wallets. Attackers posing as legitimate nodes can intercept transmissions and change their destination or contents. After that, thieves can divert cryptocurrency to their wallets. Because hackers recycle transmission data to the legitimate sender, the diversion may be very hard to detect.
Man-in-the-middle techniques can also steal private keys, giving attackers unlimited access to a user’s blockchain assets. Both attack methods compromise information stored on the blockchain and undermine trust.
Solution: Robust encryption and consensus mechanisms usually mitigate MITM attacks. Blockchain users should adopt secure protocols and verify all transaction details independently.
Endpoint vulnerabilities
Some blockchain security issues start close to home. Users may store their private keys locally and fail to apply protective measures. Stolen smartphones and compromised apps can divulge authentication information. Third-party vendors can expose blockchain keys, putting client assets at risk.
Solution: Do everything possible to prevent encryption key theft. Encrypt devices that store keys and implement rigorous physical security.
Smart contract vulnerabilities
Smart contracts are becoming increasingly popular but can also be risky. Developers build these self-executing contracts into blockchain operations. When two users meet pre-defined conditions, the contract processes their transaction. There is no need for an intermediary to verify credentials. Transactions should be faster and more secure.
However, that’s not always the case. The code base of smart contracts could contain flaws, creating room for malicious exploits. For instance, in 2021, hackers leveraged code flaws in smart contracts to extract over $600 million from Poly Network.
Solution: The problem with smart contracts often lies in the code. Apply code audits and verify every contract before use. Follow secure development practices to ensure high-quality outputs and use trusted code libraries when building contracts.
Blockchain security best practices
The list above may be concerning, and it should be. Blockchain usage is generally safe, but users must be aware of common blockchain security issues to mitigate critical risks. If not, one of the attacks we’ve discussed will eventually materialize.
Help is at hand. Follow the best practices below to benefit from blockchain technology and ensure secure transactions.
Apply robust encryption to blockchain networks
The first blockchain security fundamental is obvious. Always encrypt private keys used to access and change blockchain network nodes.
Use AES-256 (or even more secure standards) to generate blockchain hashes. Remember: every link in the chain should be unique and verifiable. Meeting these conditions is only possible with virtually undecipherable encryption.
Additionally, use encrypted digital signatures to verify blockchain network transactions. Signatures based on the Elliptic Curve Digital Signature Algorithm (ECDSA) should deliver sufficient security.
Implement Identity and Access Management (IAM) solutions
Controlling access to your blockchain network is all-important. IAM solutions define who can use private keys and change the blockchain ledger. Unauthorized users are blocked at the source, making it harder to launch insider attacks.
IAM also makes phishing more complex. Hackers may obtain user credentials. However, IAM systems can detect suspicious logins via contextual verification. Just having a password is not enough to manipulate blockchains.
Combining IAM with robust multi-factor authentication is also advisable. MFA dramatically cuts risks linked to endpoint vulnerabilities.
Adopt secure development practices
Secure development practices ensure the security of apps, contracts, and algorithms. Code reviews check for vulnerabilities before blockchains go live. Measures like bug bounties and penetration testing assess existing blockchain systems. Security teams can detect problems before they enable malicious access.
Use multi-signature wallets for blockchain transactions
One of the biggest blockchain security problems is verifying user requests. Inadequate verification can lead to crippling Sybil or 51 attack methods, ruining the integrity of blockchain systems. Multi-signature (or multi-sig) wallets solve this problem.
These digital wallets require more than one user to approve blockchain network operations, essentially a form of separation of duties. Single users cannot make critical changes or divert funds. Every change requires third-party sign-off.
Multi-sig wallets also have benefits for eCommerce users of blockchain networks. The third party can arbitrate disputes, smoothing problematic transactions.
Put fail-safes in place to deal with security incidents
Fail-safes ensure blockchain security vulnerabilities won’t cause catastrophic failures. Or at least they make disasters less likely.
For example, circuit breakers and emergency stops can kick in when unexpected conditions arise in smart contract transactions. Companies can use secure backups to hold encryption keys and implement secure key recovery systems.
At a more general level, incident recovery policies are crucial. Employees should understand how to restore blockchain networks when emergencies arise. Response plans may include upgradeability measures to fix vulnerabilities without compromising blockchain availability.
Regularly audit blockchain networks
Networks based on blockchain technology are like any other systems. Users must constantly revisit their security measures to detect emerging vulnerabilities. Security teams should also collect user data to monitor transactions.
Audits should include code reviews. Reviews cover apps, consensus mechanisms, encryption, and transfer protocols. Code audits within the software development lifecycle enable timely changes and continuous vulnerability management.
You can use penetration testing to simulate real-world attacks and assess functional weaknesses. Cover the attack types listed above and note any possible weak points.
Finally, audit network security issues that govern access to blockchain networks. For instance, consider device security, password hygiene, and access management. Training is also important, as one careless employee can open the way to 51 attack methods.
Solve blockchain security issues with NordLayer
Blockchain networks now occupy niches throughout the business world. Distributed ledgers are making transactions easier to trace and more trustworthy. They enable secure global payments, manage logistics flows, and record processes like real estate title management.
However, it’s easy to oversell the security benefits of blockchains. As we have seen, blockchain security is an urgent concern for companies adopting the new technology. Hackers can dominate networks, force transactions, steal keys, and destroy the integrity of ledgers. Users need to respond quickly.
NordLayer offers user-friendly solutions that enhance blockchain security by ensuring that only authorized people have access to your blockchain environments.
Our Zero Trust Security solutions, such as IP allowlisting, Cloud Firewall, and MFA, block access for all unauthorized network users and allow the distribution of access rights to blockchain networks. Only users with appropriate credentials can access blockchains, and everyone else remains locked out.
Encrypted VPN tunnels protect private keys, reducing the risk of man-in-the-middle attacks. Device posture checks if connected devices comply with device security rules, promoting endpoint security. ThreatBlock also restricts access to malicious blockchain websites.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.