The Opportunities and Obstacles of Zero Trust
The rapid evolution of digital threats demands a robust response, for enterprise zero trust efforts to fortify cybersecurity defenses. At its core, Zero Trust challenges traditional notions by assuming that threats can emerge both outside and inside an organization. This paradigm shift empowers businesses to enhance security by verifying every access request, thereby mitigating the risk of unauthorized access. However, this promising approach is not without its challenges. As of 2024, the majority of organizations have begun their journey towards a Zero Trust strategy, often collaborating with multiple security providers to lay the groundwork for implementation. This trend underscores the complexity and ambition involved in adopting Zero Trust.
Major Challenges in Implementing Zero Trust
Implementing Zero Trust at an enterprise level demands a meticulous approach due to the intricate nature of large-scale deployments. This endeavor can span several years, requiring significant resources and planning. Among the primary challenges is the constant need to update Zero Trust policies to keep pace with evolving business needs. This continuous adaptation can become a formidable task, necessitating sustained commitment and expertise.
Another critical issue is the impact on user experience. Strict security measures often introduce latency and perceived inconvenience, which can disrupt workflows and lead to resistance from employees. This resistance can undermine the overall effectiveness of the security strategy, making it crucial to strike a balance between robust protection and a seamless user experience.
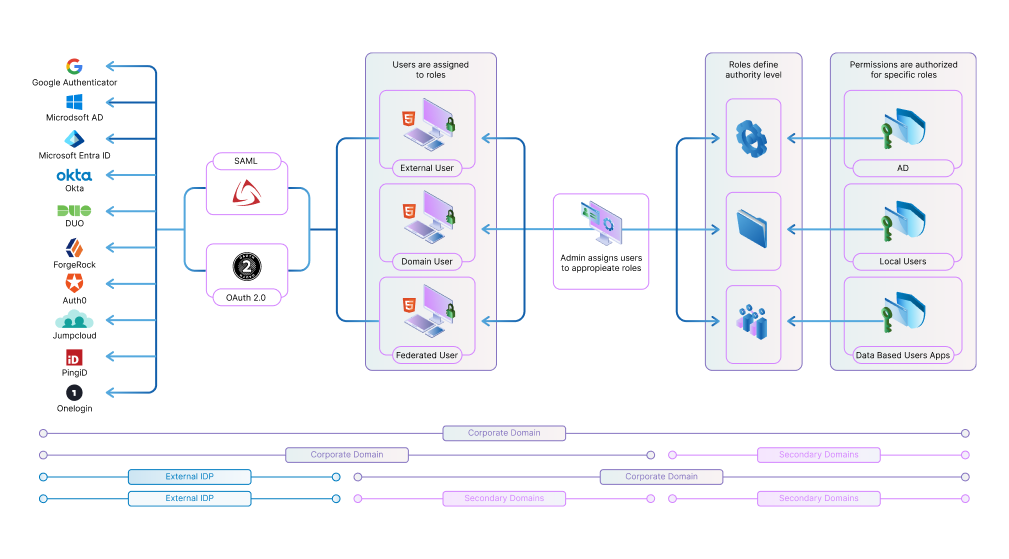
Integration with existing infrastructure is another significant hurdle. Many organizations have complex, legacy systems that may not easily align with Zero Trust principles. Ensuring seamless interoperability between new Zero Trust solutions and established systems requires careful planning and execution. The necessity to maintain comprehensive visibility and control over network activity adds another layer of complexity, demanding advanced monitoring and management capabilities.
Moreover, the financial investment associated with Zero Trust implementation can be substantial. This includes not only the cost of new technologies but also the expenses related to training, change management, and ongoing maintenance. Organizations must be prepared to allocate sufficient budget and resources to support this transformative initiative.
Lastly, the rapidly changing threat landscape presents an ongoing challenge. As cyber threats become increasingly sophisticated, Zero Trust architectures must continually evolve to counter new tactics and vulnerabilities. This dynamic environment requires organizations to stay ahead of the curve, leveraging innovative solutions and strategies to maintain a robust security posture.
Navigating these challenges requires a strategic, well-coordinated effort. By addressing these complexities head-on, organizations can lay the groundwork for a resilient and effective Zero Trust architecture that meets both current and future security demands.
Selecting Products for Enterprise Zero Trust
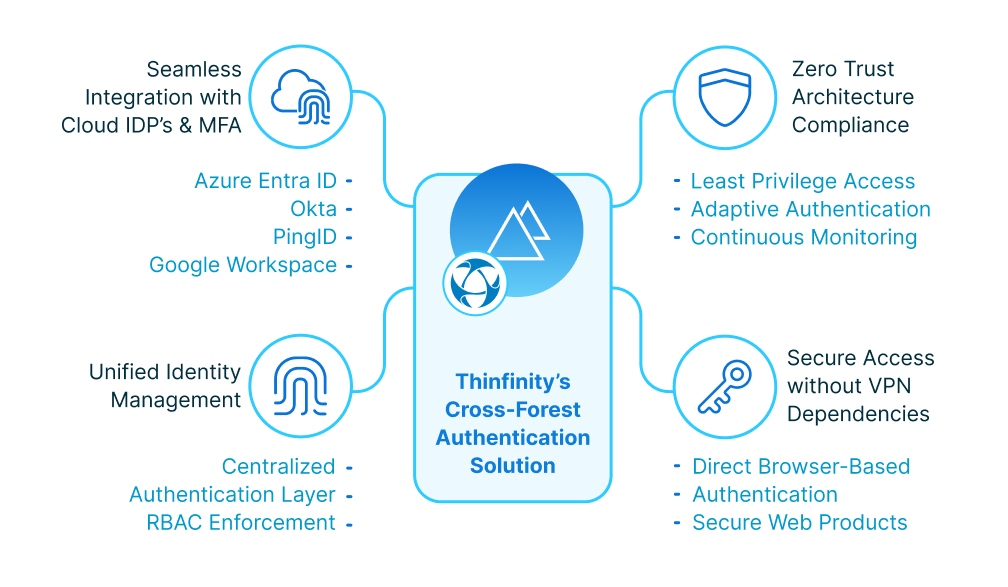
Selecting products for an Enterprise Zero Trust strategy demands a discerning approach rooted in both technical requirements and strategic foresight. The first step is to evaluate the interoperability of potential solutions with existing infrastructure. Seamless integration is paramount, ensuring that new Zero Trust tools enhance rather than disrupt current operations. Solutions must offer robust capabilities for continuous authentication and micro-segmentation, providing granular control over user access.
It’s essential to prioritize products that deliver comprehensive visibility across the network. This visibility is crucial for monitoring and managing user activities, detecting anomalies, and responding swiftly to potential threats. Look for solutions that offer advanced analytics and real-time insights, enabling proactive security measures and informed decision-making.
Equally important is the consideration of scalability. As organizations grow and their needs evolve, the chosen Zero Trust products should be capable of adapting without requiring a complete overhaul. Scalable solutions allow enterprises to expand their security measures incrementally, aligning with both budgetary constraints and long-term objectives.
Adaptability is another critical factor. The cybersecurity landscape is ever-changing, and Zero Trust solutions must evolve to address new vulnerabilities and attack vectors. Products that offer regular updates, backed by a strong support ecosystem, will ensure the organization remains protected against emerging threats.
Another key aspect is ease of management. Solutions that simplify policy enforcement and reduce administrative overhead can significantly enhance operational efficiency. Automated features that facilitate continuous compliance and streamline incident response processes are highly beneficial, allowing security teams to focus on strategic initiatives rather than routine tasks.
Vendor reputation and support services should not be overlooked. Collaborating with reputable vendors who have a proven track record in Zero Trust can provide additional assurance of product reliability and effectiveness. Furthermore, strong vendor support can aid in overcoming implementation challenges, ensuring a smoother transition to a Zero Trust architecture.
By carefully considering these factors, organizations can select Zero Trust products that align with their security goals, operational needs, and future growth trajectories.
Mapping a Realistic Path Forward
Mapping a realistic path forward with Zero Trust begins with strategic planning and measured execution. A phased rollout strategy is essential, allowing organizations to gradually introduce Zero Trust principles without overwhelming existing systems and workflows. Initial efforts should concentrate on critical areas that provide significant security benefits and minimal disruption. This targeted approach helps in building momentum and demonstrating early successes.
Engaging all relevant stakeholders early in the process is crucial. Clear communication about the objectives, benefits, and operational changes can foster buy-in and mitigate resistance. Tailored training sessions and educational programs will empower employees, turning them into active participants in the security transformation.
A flexible technology stack is fundamental. Choose solutions that can adapt to evolving business needs and integrate seamlessly with current infrastructure. This adaptability ensures the Zero Trust model can scale and evolve as the organization grows and as new threats emerge.
Continuous monitoring and real-time analytics are key components. Implement tools that provide comprehensive visibility and facilitate proactive threat detection. By maintaining rigorous oversight, organizations can swiftly address vulnerabilities and adjust policies as necessary.
Another critical element is fostering a culture of continuous improvement. Regularly review and refine Zero Trust policies to align with the latest cybersecurity developments and organizational changes. This iterative process helps in maintaining a robust security posture while accommodating the dynamic nature of cyber threats.
Invest in strong vendor partnerships to leverage expert insights and support throughout the implementation journey. Reputable vendors with proven expertise in Zero Trust can provide invaluable guidance, ensuring smoother transitions and more effective solutions.
By embracing a structured, adaptable, and collaborative approach, organizations can successfully implement Zero Trust, achieving enhanced security and resilience against an increasingly sophisticated threat landscape.
Building a Resilient Cybersecurity Future with Zero Trust
Successfully optimizing your cybersecurity budget with an enterprise Zero Trust strategy requires more than just adopting new technologies—it demands a paradigm shift in how organizations approach security. By addressing challenges such as integration, user experience, and continuous adaptation, businesses can unlock the full potential of Zero Trust to protect critical assets and reduce vulnerabilities.
Through careful planning, strategic product selection, and fostering a culture of continuous improvement, organizations can establish a robust and scalable Zero Trust architecture. The result? A resilient cybersecurity framework that not only withstands current threats but also evolves to meet the demands of an ever-changing digital landscape.
About Portnox
Portnox provides simple-to-deploy, operate and maintain network access control, security and visibility solutions. Portnox software can be deployed on-premises, as a cloud-delivered service, or in hybrid mode. It is agentless and vendor-agnostic, allowing organizations to maximize their existing network and cybersecurity investments. Hundreds of enterprises around the world rely on Portnox for network visibility, cybersecurity policy enforcement and regulatory compliance. The company has been recognized for its innovations by Info Security Products Guide, Cyber Security Excellence Awards, IoT Innovator Awards, Computing Security Awards, Best of Interop ITX and Cyber Defense Magazine. Portnox has offices in the U.S., Europe and Asia. For information visit http://www.portnox.com, and follow us on Twitter and LinkedIn.。
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.