Introduction
IoT (Internet of Things) is a revolutionary technology with tremendously promising potential impact. It has grown exponentially, from industry to home, and the number of IoT devices will likely keep rising. However, this new technology also raises security concerns. As these devices become prevalent in the public sector and the home, IT specialists must be able to use them appropriately
A recent forecast shows that 27 billion internet-connected devices will be in place by 2025. As IoT technology becomes more widespread, it is beginning to influence how individuals interact worldwide. To ensure safety for IoT devices, organizations must ensure that these devices are correctly configured and monitored.
Network Access Control (NAC) can address these IoT management and security issues by providing foundational protection against the rise of IoT threats.
IoT Device Management, Onboarding & NAC
IoT device management and onboarding involves securely linking IoT devices to internal networks. Organizations can then monitor and control IoT devices while securing their networks by enrolling them.
NAC is a foundational security tool that helps with this by significantly reducing unauthorized access to critical business assets while also remedying flaws in the device enrollment process. NAC is central in securing IT infrastructure against rogue IoT devices and other malicious threats.
How NAC Facilitates IoT Device Management & Onboarding
Below are some roles in which implementing NAC can help IoT devices management and onboarding:
Authentication
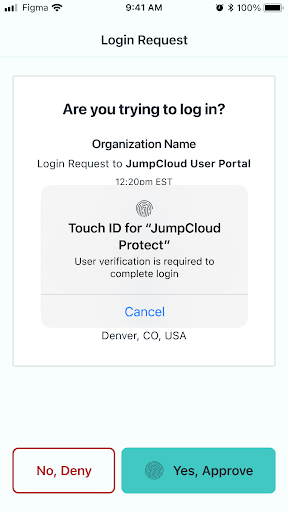
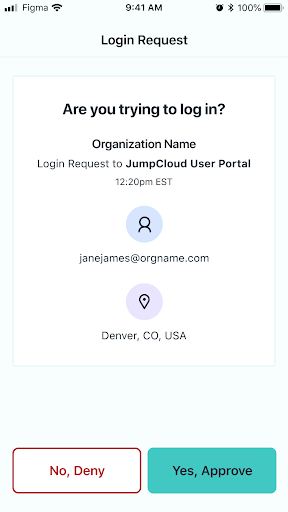
IoT devices need to be authenticated before they can connect to a network to mitigate the threats such as man-in-the-middle and replay attacks. NAC helps mitigate this risk by blocking access between the user and the network until they are fully authenticated.
Network Configuration
NAC can also adjust the network configuration of IoT devices during onboarding. For example, if it is required for a device to connect to a specific subnet or VLAN, the NAC can automatically configure it to do so.
Monitoring
The security posture of IoT devices can significantly affect both the security of devices and their respective networks. It is critical to monitor the health of current devices and ensure that they are properly secured. NAC performs real-time monitoring and establishes monitoring policies.
Event & Log Management
NAC is responsible for gathering log and anomaly data from IoT devices. It can log various events, such as device-related information, user activity, firewall and gateway logs, reports on application and security configuration changes, etc. Users can use this data to troubleshoot problems in case of any issues arising from connected devices
Data Management
The collected data NAC gathers form connected IoT endpoints helps to improve the security configurations of specific devices. Moreover, NAC controls how information is exchanged between connected devices and an organization’s cloud services (i.e., IoT applications).
Security Configuration
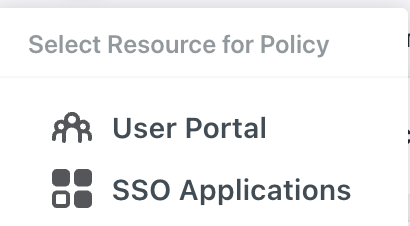
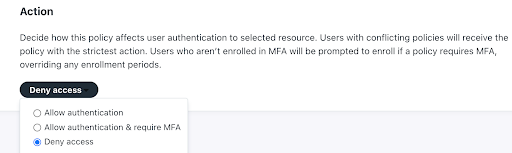
NAC can be used to perform deep security configurations of IoT devices, such as determining if IoT device users are permitted to connect to the network.
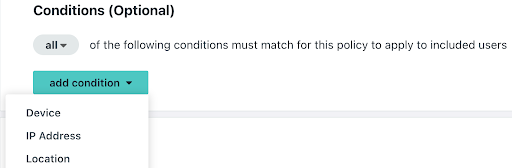
If a user is authorized, NAC can also configure IoT devices’ security settings and configurations accordingly. It can be further configured to check specific attributes, such as whether an IoT device has antivirus software installed or whether it uses particular firewall rules.
Compliance
Upon completion of the onboarding process, the IoT device will be validated for compliance with the organization’s security policies. NAC can help oversee corporate security compliance by requiring updates and software patches, ensuring business services adhere to regulatory standards, and configurations adhere to the licensing policy.
Implementing a NAC-Based IoT Device Management Solution
In executing a NAC-based IoT device onboarding solution, NAC solutions must be available for an organization’s devices and cloud services. Users must also have access to the security control plane to configure policies for connected devices and make decisions based on them. The following steps help to implement the NAC-based IoT device onboarding solution:
Identify IoT Devices that Require Onboarding
NAC solutions can help organizations identify what IoT devices are connected to the network, how and when they were connected, and how their configuration changes over time. This information can be used to develop policies that optimize the secure operation of IoT devices.
Enable IoT Devices for Onboarding
Once the devices have been identified, it is crucial to ensure that they are onboarded securely. NAC solutions can help support this process by enforcing security policies for IoT devices and using identification services and rules to ensure that there are no exceptions.
Enable Cloud Services for Onboarding
The network’s security dramatically relies on the cloud applications’ security. This means that it is vital for organizations to ensure that the cloud applications are appropriately configured for security and adhere to policies.
Apply IoT Device Management & Control Policies
Once the onboarding process has been completed and each device performs as expected, it is vital to ensure that the appropriate adjustments are made. NAC solutions can provide a way to quickly deploy security policies for IoT devices or schedule recurring tests to ensure they work as expected.
Monitor IoT Device Health
The network’s security depends on the health of all the connected devices – and IoT is no exception. To ensure that the security of each device is maintained, it is essential to ensure that they are operating as expected. NAC solutions can monitor IoT device performance over time and provide specific alerts when a problem is identified in a device.
Final Thoughts on NAC & IoT Device Management
NAC is a vital component of IoT device onboarding and is essential for an organization’s devices and cloud services. NAC can help ensure that devices are securely configured and performing as expected, while also ensuring that cloud applications are installed and configured securely.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About Portnox
Portnox provides simple-to-deploy, operate and maintain network access control, security and visibility solutions. Portnox software can be deployed on-premises, as a cloud-delivered service, or in hybrid mode. It is agentless and vendor-agnostic, allowing organizations to maximize their existing network and cybersecurity investments. Hundreds of enterprises around the world rely on Portnox for network visibility, cybersecurity policy enforcement and regulatory compliance. The company has been recognized for its innovations by Info Security Products Guide, Cyber Security Excellence Awards, IoT Innovator Awards, Computing Security Awards, Best of Interop ITX and Cyber Defense Magazine. Portnox has offices in the U.S., Europe and Asia. For information visit http://www.portnox.com, and follow us on Twitter and LinkedIn.。