In a unique report put out by Analysys Mason in 2021, ESET scored among the leaders for small- and medium-sized business (SMB) endpoint security vendors. The reason for this placement is clear: backed by a strong managed service provider (MSP) program tailored to the needs of SMBs, ESET has shown consistent financial growth in serving the SMB market around the world.)
Similarly, in 2022, Canalys published a unique report called the MSP Tech Stack, which layers five core MSP technologies positioning cybersecurity at the bottom. Although ESET did not feature among the cybersecurity vendors in this report, ESET is poised to reach a milestone in product development where it will meet the two entry criteria:
1. Over 10% of revenue sourced via MSPs.
2. A strong detection and response capability ready for MSPs.
The first criterion on revenue source is a mark already hit by ESET. The second criterion is on track to be met with the release of ESET Inspect Cloud – ESET’s XDR-enabling technology, which was already released for businesses in March 2022 – into ESET’s MSP program later this year.
The Canalys MSP Tech Stack serves as an insightful lens into the MSP world because it reveals the delicate balance between trust and freedom sought by MSPs: the trust to select any one vendor as a long-term, stable partner committed to its MSP program, and the freedom to mix and match several trusted vendors from the tech stack to access the best technologies available.
Finding a trusted security partner
Many events cause MSPs concern, like unwanted changes to partner programs, acquisitions between vendors serving the MSP community, or the widespread blocking of sales in the wake of the Ukraine invasion followed by the breaking and forging of many partnerships. In addition to this tumultuous time for service chains around the world, the concerns about cyberthreats remain ever present with governments simultaneously advising the solicitation of help from security experts and caution about the security posture of third-party vendors.
For many MSPs trudging through this complexity, turning to ESET as an EU-headquartered security provider may be a perfect fit, to put it boldly. Since its origins 35 years ago, ESET has been proud to be a privately owned company not beholden to stockholders and thus free to engage with partners to design an MSP program built on their feedback and the actual needs of SMBs. This means that ESET can offer partners a stable relationship set to last for many years.
But to be stable is not to be stagnant. ESET continually strives to enhance its MSP portfolio and improve the quality of its security products along with their integrations and features for MSPs. The key examples demonstrating this commitment are ESET PROTECT and ESET Inspect.
Prevent, detect, and respond from the cloud
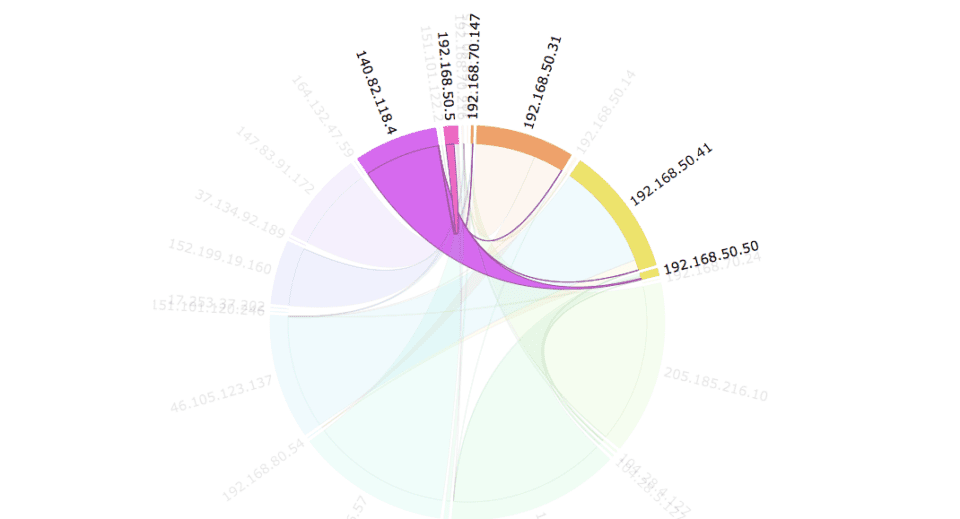
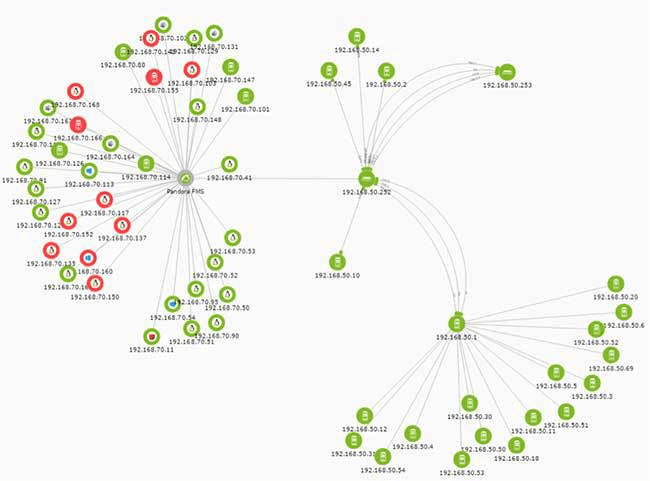
ESET PROTECT represents ESET’s tiered approach to providing businesses with subscriptions for scalable protection centered around a management console. When this move was made in 2021, a key feature was the release of a cloud-based version of ESET PROTECT. This new foray to the cloud was not an isolated event but a paradigm shift of becoming cloud first in the way ESET plans to serve businesses and MSPs in the future.
Of course, ESET was already leveraging the power of the cloud to provide increased protection for many years. But the birth of ESET PROTECT was a new way for MSPs to scale their efforts and focus their time now unencumbered by on-premises concerns. This was followed in 2021 by the genesis of yet another cloud product – ESET Cloud Office Security – which directly protects cloud-based tools, chiefly Microsoft 365.
Yet, after having traversed all this ground to the cloud, the appetite of MSPs for cloud-provisioned protection has only been sharpened. And the succulent steak for this meal, ESET Inspect Cloud, is the detection and response module laying the foundation of ESET’s pursuit of XDR.
Interested in partnering via ESET’s MSP program? Read more here.
Apart from ESET Inspect, other plans are in store for MSPs. To give only a few hints now, ESET has long-term plans to offer multifactor authentication from the cloud, to build a vulnerability and patch management solution, and to launch a unified license management solution capable of serving the needs of all partners’ distribution model types.
Further reading:
- MSPs must master cybersecurity II
- Criminal hacking hits managed service providers: Reasons and responses
- No-cost ESET plugins for MSPs streamline security via low-effort dashboard
- With more businesses moving to the cloud and adopting SaaS, ESET Cloud Office Security provides easily managed security to MSPs and their Microsoft 365 clients
- A new business offering for a new business world
- Bringing cloud-based management to the managed service providers’ tool kit with ESET PROTECT Cloud
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About ESET
For 30 years, ESET® has been developing industry-leading IT security software and services for businesses and consumers worldwide. With solutions ranging from endpoint security to encryption and two-factor authentication, ESET’s high-performing, easy-to-use products give individuals and businesses the peace of mind to enjoy the full potential of their technology. ESET unobtrusively protects and monitors 24/7, updating defenses in real time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company. Backed by R&D facilities worldwide, ESET became the first IT security company to earn 100 Virus Bulletin VB100 awards, identifying every single “in-the-wild” malware without interruption since 2003.