At the end of the last century I had the opportunity to help in a very ambitious computer project: the search for radio messages emitted by extraterrestrial civilizations… And what the hell does it have to do with Distributed Systems?
Recently my colleagues wrote an interesting article on distributed network visibility, which I really liked and I came up with the idea of taking it to the next level. If this post tries to offer full knowledge of the different components in operation within our network, Distributed Systems go “further”; they reach where we lack control over the devices that comprise it.
I am going to exemplify both at the social science level, comparing a union versus a confederation (as a central of workers and unioI am going to exemplify both at the social science level, comparing a union versus a confederation (as a central of workers and unions and not from a political point of view).
*Confederacy
According to Merriam-Webster
1. A group of people, countries, organizations, etc. joined together for a common purpose or by a common interest: LEAGUE, ALLIANCE
Distributed computing, distributed systems, are they the same?
Distributed Systems
If you look for the concept of Distributed Systems on Wikipedia (that magical place), you will be redirected to the article called Distributed Computing and, I quote:
“Distributed computing also refers to the use of distributed systems to solve computational problems. In distributed computing, a problem is divided into many tasks, each of which is solved by one or more computers, which communicate with each other via message passing.”
Without going any further: Wikipedia, if we consider ourselves as computers, it is a very high-level Distributed System, since we comply with its intrinsic characteristics… And what are they?
Features of Distributed Systems
A Distributed System (or Distributed Computing) has:
• Concurrence: Which in the case of computers is a distributed program and in Wikipedia they are people… who use specialized software distributed by web browsers.
• Asynchronous: Each computer (or Wikipedian) works independently without waiting for a result from the other, when it finishes its batch of work, it delivers it and it is taken in and saved.
• Resilience: A computer device that breaks down or loses connection, or a person who dies, withdraws or is expelled from Wikipedia, in both environments does not mean stopping the work or global task. There will always be new resources, machines or humans, ready to join the Distributed System.
The aliens
Right, I started this article talking about them. In today’s -unfortunately- destroyed radio telescope in Arecibo, Puerto Rico, astronomers Carl Sagan and Frank Drake sent a message to the Hercules cluster, a group of galaxies 25,000 light years away from our planet.

“Hercules Globular Cluster (https://commons.wikimedia.org/wiki/File:Hercules_Globular_Cluster,_EVscope-20211008.jpg) ”
That means that it will take 50 thousand years to get an answer, if there is life out there, but what if it is us who were already sent messages thousands or millions of years ago?
Well, this was the program Seti@home about: it collected radio signals and chopped them into two-minute pieces that were sent to each person who wanted to collaborate in the analysis with their own computer. At the end of the calculation according to a special algorithm, the result was sent and a new piece of code was requested. If a computer after a reasonable time did not return an answer, then the same piece was sent to another computer that wanted to collaborate: the “prize” consisted in publicly recognizing the collaborator as a discoverer of life and intelligence outside this world.
I installed the program and put it as a screensaver, so I calculated while I was working on something else or resting.
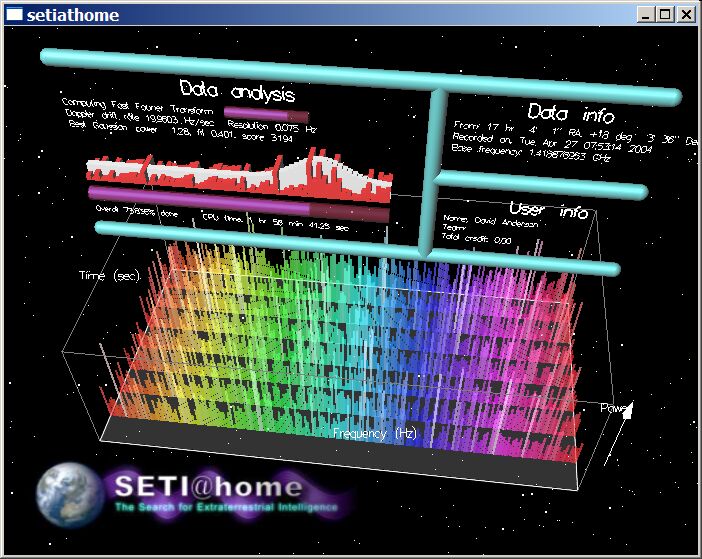
“Seti@home (imagen de setiathome.berkeley.edu) ”
There you have it! A distributed system for analyzing the radio signals of the universe!
Distributed monitoring
Distributed monitoring depends on the network topology used, and I bring it up as an introduction or approach to monitoring a distributed system. If you are new to Pandora FMS, I recommend you take some time to read this post.
Essentially it is about distributed environments that give service to a company or organization but do not execute a common software and have very different areas or purposes between departments, supported in communication with a distributed network topology accompanied by a well planned security architecture in monitoring.
Pandora FMS offers in this field service monitoring, very well described in the official documentation.
Observability
It would be an attribute of a system, and the topic is worth a full blog post, but, in summary, I expose observability as a global concept that includes more alert monitoring and alert management activities, visualization and trace analysis for distributed systems, and log analysis.
Companies like Twitter have taken observability very seriously and, as you may have guessed, that addictive social network is a distributed system but with a diffuse end product (increase our knowledge and facts about the real world).
Transaction monitoring
How can we monitor a distributed system if it consists of very heterogeneous components and, as we saw, can reach any part of our known universe?
Pandora FMS has Business Transactional Monitoring, a tool that I consider the most appropriate for distributed systems since we can configure transactions, as many as we need, and then use the necessary transactional agents to do so.
It is a difficult topic to take in but our documentation starts with a simple and practical example, with which, as you experiment, you may add “blocks” of more complex transactions until you reach a point where you can have a panorama of the distributed system.
All this is possible with Pandora FMS since it has standard monitoring, remote checks, transaction synthetic monitoring and the Satellite server for distributed environments that can be used with transactional monitoring for distributed systems.
Present and future
The question is no longer whether we need distributed systems. That is a fact. Today people use distributed systems in computing services in the cloud or in data centers and the Internet.
Distributed systems can offer impossible functions in monolithic systems or take advantage of computer processes, such as performing restorations from backups by asking other systems for chunks that are missing or have deteriorated in the local system.
For all these cases, and in any case, the flexibility of Pandora FMS will always be useful and adaptable for current or future challenges.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About PandoraFMS
Pandora FMS is a flexible monitoring system, capable of monitoring devices, infrastructures, applications, services and business processes.
Of course, one of the things that Pandora FMS can control is the hard disks of your computers.