Software as a Service (SaaS) has become the backbone of many businesses, offering scalable and cost-effective solutions for various industries. However, with the convenience of SaaS comes the critical responsibility of ensuring SaaS compliance with industry standards and data protection laws.
For those new to SaaS, understanding SaaS compliance can be daunting, but it is crucial for protecting sensitive data, building customer trust, and avoiding legal pitfalls. This guide will walk you through the basics of SaaS compliance, covering key standards, common challenges, and best practices to help you keep your business on the right track.
What is SaaS compliance?
SaaS compliance means that software-as-a-service providers have to follow various regulatory requirements, laws, and industry-specific standards. These standards are designed to protect sensitive data, ensure financial transparency, and maintain security protocols across cloud-based services. For SaaS providers, compliance is not just a legal obligation but is also about demonstrating their commitment to safeguarding customer data and upholding industry benchmarks.
For instance, consider a company that offers cloud-based solutions for managing healthcare records. To operate legally and securely, the company must comply with the Health Insurance Portability and Accountability Act (HIPAA), which sets strict standards for protecting sensitive patient information. Without HIPAA compliance, the company could face fines, lose customers, and suffer reputational damage.
Why is SaaS compliance important?
Understanding why SaaS compliance is important is crucial for any business operating in the SaaS space. Compliance serves two primary purposes: protecting data security and maintaining customer trust.
Data security
With data breaches becoming an everyday threat, robust SaaS compliance practices help SaaS providers safeguard their customers’ data against security risks. Compliance frameworks like the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA) impose stringent requirements on how companies collect, store, and process personal data. Failure to comply can lead to severe penalties and legal consequences.
For example, in 2023, Meta was fined $1.3 billion for GDPR violations. The company failed to ensure adequate protections for user data during transfers between the EU and the U.S. This shows how important it is to prioritize data security and compliance to avoid substantial legal penalties.
Customer trust
Compliance also plays a crucial role in building and maintaining customer trust. When customers know that a SaaS provider follows compliance frameworks like PCI DSS (Payment Card Industry Data Security Standard) or SOC 2 (Service Organization Control 2), they feel more confident that their data is secure. This trust is essential for long-term business relationships and customer retention.
Risks of non-compliance
The risks of non-compliance are significant. They include legal penalties, financial loss, reputational damage, and operational disruptions. Companies that fail to meet compliance standards may also find it challenging to attract and retain customers as trust in their services diminishes. In extreme cases, non-compliance can lead to business shutdowns, especially if the violations are severe.
Key compliance standards for SaaS providers
To effectively manage compliance, SaaS providers must understand the types of SaaS compliance relevant to their industry. These compliance standards vary depending on the nature of the service, the type of data handled, and the geographical location of the customers. Here’s an overview of some major compliance frameworks.

![]()
Financial compliance
Payment Card Industry Data Security Standard (PCI DSS)
PCI DSS is essential for any SaaS provider that handles payment card transactions. This standard outlines security measures to protect cardholder data, including data encryption, secure storage, and regular monitoring. Implementing solutions to become PCI compliant is crucial for preventing data breaches and maintaining customer trust.
Accounting Standards Codification (ASC 606)
ASC 606 provides guidelines for revenue recognition, ensuring that companies report their financial performance accurately. SaaS providers must comply with ASC 606 to demonstrate financial transparency and avoid legal issues related to revenue reporting.
Sarbanes-Oxley Act (SOX)
SOX compliance is mandatory for publicly traded companies, including SaaS providers. It focuses on corporate governance and financial reporting, requiring companies to implement internal controls and report on their effectiveness. Non-compliance with SOX can lead to severe penalties, including fines and imprisonment for executives.
Security compliance
Service Organization Control 2 (SOC 2)
SOC 2 compliance is a critical standard for SaaS providers that handle customer data. It ensures the company’s information security management systems meet industry standards. SOC 2 audits evaluate controls related to security, availability, processing integrity, confidentiality, and privacy. Achieving SOC 2 compliance is essential for demonstrating that your SaaS solutions are secure and reliable.
ISO/IEC 27001
ISO/IEC 27001 is an international standard for information security management systems. It provides a framework for managing and protecting sensitive information through a systematic approach. Implementing an ISO 27001 compliance solution can help SaaS providers safeguard their data, meet customer expectations, and improve overall security.
Center for Internet Security (CIS) Controls
The CIS Controls are a set of best practices for cybersecurity. They provide a prioritized set of actions to protect organizations from cyber threats. SaaS providers can use these controls to strengthen their security posture and reduce security risks, including breaches.
National Institute of Standards and Technology Cybersecurity Framework (NIST CSF)
The NIST CSF is a voluntary framework that provides guidelines for managing and reducing cybersecurity risks. SaaS providers can adopt it to enhance their security practices and ensure they are aligned with industry standards.
Data privacy compliance
General Data Protection Regulation (GDPR)
GDPR is a European Union regulation that governs how companies handle personal data. It applies to any SaaS provider that processes data belonging to EU citizens, no matter where the company is based. Compliance with GDPR is essential for avoiding hefty fines and protecting customer privacy. Companies can explore GDPR compliance services for tailored support.
HIPAA (Health Insurance Portability and Accountability Act)
HIPAA sets the standard for protecting sensitive patient information in the healthcare industry. SaaS providers that handle health-related data must comply with HIPAA to avoid penalties and ensure that patient information is kept confidential. Implementing HIPAA compliance solutions is vital for any SaaS provider operating in the healthcare sector.
CCPA (California Consumer Privacy Act)
The CCPA is a state law that grants California residents rights over their personal data. It requires businesses to disclose what information they collect, allow consumers to opt out of data sharing, and delete personal data upon request. SaaS providers must comply with CCPA to avoid legal penalties and maintain customer trust.
Data security and privacy regulations
Data security and privacy are at the heart of SaaS compliance. Data protection laws like GDPR, HIPAA, and CCPA are designed to protect individuals’ data from misuse and unauthorized access. These regulations require SaaS providers to implement strict security measures, such as data encryption, access controls, and regular monitoring, to ensure that data is protected at all times.
For example, a SaaS provider offering cloud storage services must ensure that data is encrypted at rest and in transit. This means that even if a malicious actor gains access to the data, they would not be able to read it without the decryption key.
Complying with data security and privacy regulations can help SaaS providers protect their customers’ information and avoid legal consequences.
Challenges in achieving SaaS compliance
Achieving SaaS compliance can be challenging for SaaS providers, especially those just starting. Here are some common challenges and potential solutions:
Complexity of regulations
SaaS compliance requirements can be complex and vary by industry and region. For example, a global SaaS provider may need to comply with multiple regulations, such as GDPR, CCPA, and HIPAA, each with unique requirements. To manage this complexity, SaaS providers can use SaaS compliance management tools that automate tracking and implementing regulatory requirements.
Resource constraints
Small and medium-sized SaaS companies often lack the resources for compliance efforts. Hiring compliance experts or outsourcing SaaS compliance can be expensive. However, non-compliance can be even more costly in the long run. To handle this, SaaS providers can focus on implementing the most critical compliance measures first and gradually expand their compliance efforts as their business grows.
Keeping up with changes
Compliance standards and data protection laws are constantly evolving, and SaaS providers must stay up-to-date with the latest changes to remain compliant. This requires continuous monitoring of regulatory updates and adjusting compliance practices as needed. An effective compliance strategy includes subscribing to industry newsletters, attending webinars, and participating in compliance forums to stay informed.
Benefits of SaaS compliance
While achieving SaaS compliance can be challenging, the benefits far outweigh the effort. Here are some key benefits:
Improved security
SaaS compliance ensures that providers implement robust security controls to protect customer data. This reduces the risk of data breaches and cyber-attacks, safeguarding both the company and its customers.
Enhanced customer trust
SaaS security compliance demonstrates to customers that their data is in safe hands, building trust and loyalty and leading to long-term customer relationships.
Competitive advantage
Compliant SaaS companies can differentiate themselves from competitors who may not offer the same level of security and privacy protection. This can be a significant selling point in a crowded market.
Best practices for maintaining SaaS compliance
Maintaining SaaS compliance is an ongoing process that requires constant attention. Here are some best practices to help:
Regular audits
Conduct internal and external audits regularly as part of your compliance strategy. Audits help assess your compliance status and identify any gaps in your security practices. They can also help you stay on top of compliance requirements and ensure that your SaaS solutions remain secure.
Employee training
Regularly train employees on SaaS compliance requirements and their role in maintaining it. An informed team is better equipped to follow measures and avoid potential compliance risks.
Usage of compliance management tools
Leverage compliance management tools to automate tracking and implementing regulatory requirements. These tools help reduce human error and ensure all compliance obligations are met. Additionally, use only SaaS-compliant tools for daily operations to create a secure environment and minimize risks. The more secure your operational tools, the stronger your overall compliance posture.
Document compliance efforts
Keep detailed records of your compliance activities, including policies, procedures, and audit results. This documentation is crucial during an audit or regulatory inquiry.
SaaS compliance checklist
To help you get started, here’s the SaaS compliance checklist of key steps.

![]()
Identify applicable regulations: Determine which compliance standards (like GDPR, HIPAA, or PCI DSS) apply to your SaaS business
Implement security measures: Ensure your platform meets all security requirements, such as encryption and access controls
Conduct regular audits: Schedule regular audits to assess your compliance and identify areas for improvement
Train employees: Provide ongoing training to ensure employees understand their compliance responsibilities
Use compliance tools: Implement tools to automate and streamline your compliance tasks
Document compliance efforts: Keep detailed records of your compliance activities, including financial compliance measures and the implementation of security controls.
How can NordLayer help companies stay compliant?
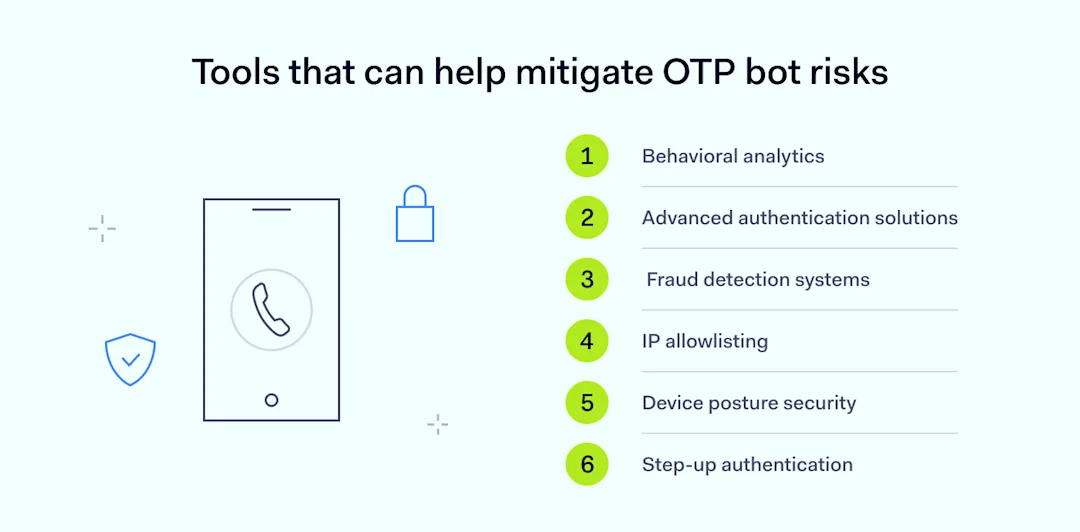
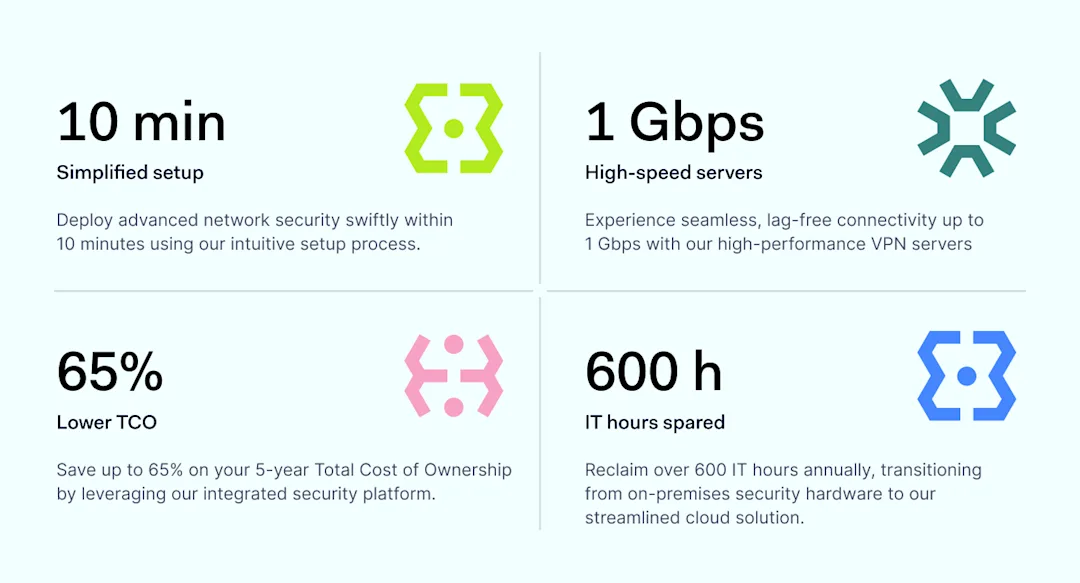
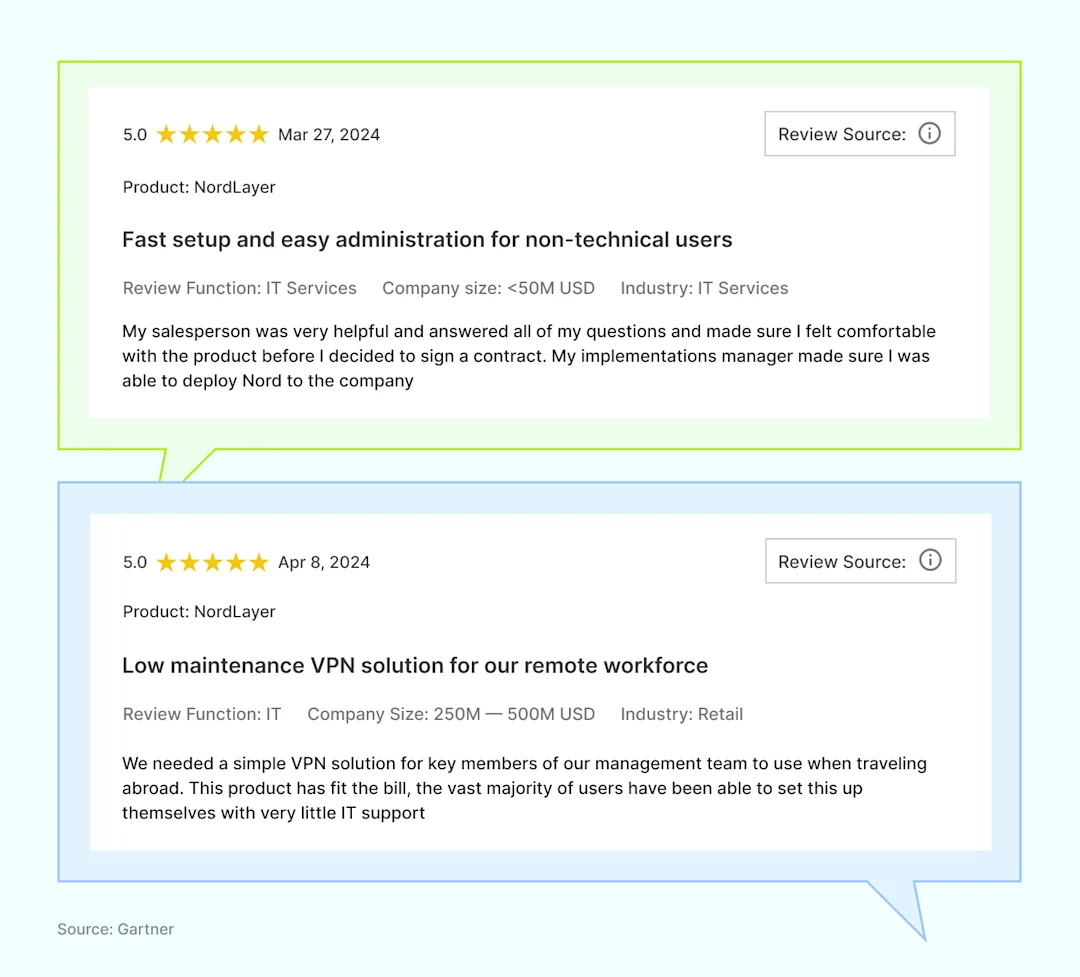
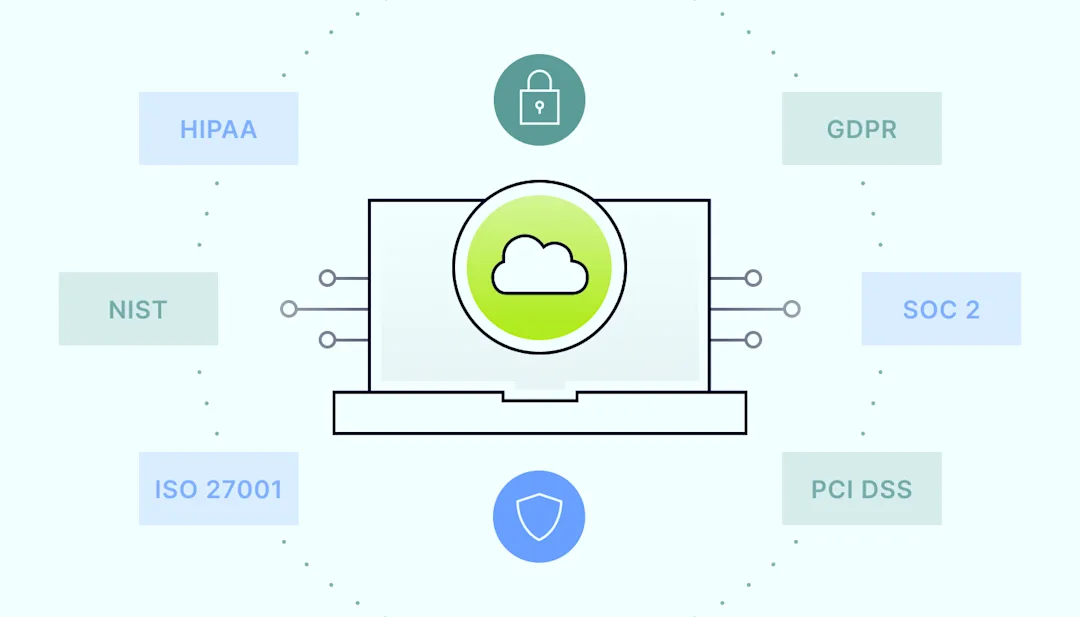
NordLayer itself meets multiple compliance standards for securing applications and services, including GDPR, HIPAA, ISO 27001, and PCI DSS. Compliance often requires specific network security measures, such as traffic encryption, advanced network access control, and multi-factor authentication.
NordLayer addresses these needs by providing robust security features designed to meet these requirements. By integrating NordLayer, you can enhance the security of your SaaS solutions, ensuring they align with compliance standards and protect sensitive data effectively.
Conclusion
SaaS compliance is a critical aspect of running a successful software-as-a-service business. By understanding and adhering to key compliance standards, SaaS providers can protect their customers’ data, build trust, and avoid legal pitfalls. While achieving compliance can be challenging, the benefits—including improved security, customer loyalty, and competitive advantage—make it well worth the effort.
By following best practices and leveraging tools like NordLayer, you can navigate the complex world of SaaS compliance with confidence and ensure your business’s long-term success.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.