“Some ransomware wants you to pay. Anubis wants you to suffer.” That’s not a tagline. It’s the growing sentiment among cybersecurity experts who’ve analyzed this latest digital weapon. Anubis doesn’t just encrypt your files and hold them hostage for ransom. It goes one step further: wiping everything clean, even after demanding payment. No recovery. No negotiation. Just devastation.

Unlike traditional ransomware strains, which typically give you a chance to recover your data post-payment, Anubis offers no real path to redemption. Victims are left not only locked out but burned down. This post explains what Anubis ransomware does, how it gets into systems, and why it’s causing serious concern in 2025. You’ll also find practical tips to stay safe and what to do if you’ve already been hit.
What Is Anubis Ransomware and Why Is It So Dangerous?
2025 marks the emergence of a new trend in cybercrime: Anubis ransomware. This destructive variant, named after the Egyptian god of death and the afterlife, is living up to its namesake by offering no redemption.
Unlike earlier variants designed primarily for financial extortion, Anubis behaves like a hybrid between ransomware and wiper malware. Its goal is not only to demand payment but to eliminate any hope of recovery, even if the ransom is paid. Victims report total data loss, corrupted boot sectors, and irrecoverable systems. Anubis doesn’t care whether you comply with its demands. Once it strikes, your data is either encrypted, deleted, or both.
How Anubis Ransomware Infects Systems
Anubis doesn’t use novel tricks to gain access. It thrives because it exploits what still works. Several studies have pointed out that its infection methods include:
- Phishing Emails
Emails with hazardous links or attachments often appear to be job offers, invoices, or delivery alerts.
- Cracked Software and Torrents
Users who install pirated or unverified programs without knowing it make their computers vulnerable to Anubis.
- Infected Loaders
Malware loaders like Phobos spread Anubis as a secondary payload, which enables rapid execution.
- Exploiting Weaknesses
Old operating systems or third-party apps that haven’t been fixed are the best targets.
Anubis cunningly remains inactive when it infiltrates a system. This allows it to bypass antivirus programs by masquerading as legitimate processes or by checking if it’s running in a virtual environment. After it determines the timing is appropriate, it releases its payload.
Step-by-Step: What Happens When You’re Infected With Anubis Ransomware
Here’s how a typical Anubis infection unfolds:
- Step 1: File Scanning and Targeting
Anubis swiftly searches for important files, including papers, pictures, videos, backups, and more. It also scans for shadow copies and network-attached storage (NAS) to ensure that no recovery point is missed in its detection.
- Step 2. Encryption Begins
Using strong AES or RSA encryption algorithms, Anubis locks your data and renames files with unique extensions. A ransom note is usually dropped in every affected folder.
- Step 3. Data Wiping Initiated
Anubis differs from typical ransomware in that it can remove or modify files even after they have been encrypted. It wipes off boot sectors, stops recovery tools from functioning, and occasionally even wipes drives completely, ensuring your data is permanently deleted.
- Step 4. Corruption and System Failure
Some victims report that their machines become unbootable. Others face complete file system collapse. Anubis may overwrite data multiple times to prevent forensic recovery tools from accessing it.
- Step 5. Deception and Silence
Even if a victim pays the ransom, they often receive no decryptor—or a fake one. It’s a setup for heartbreak, not hope. Anubis operates with no intention of restoring your files.
Why Paying the Ransom Won’t Recover Your Files
Many ransomware attacks, while destructive, at least offer a sliver of hope in the form of decryption. Anubis does not.
- Wiping Is Part of the Design
The malware is coded to wipe data regardless of whether payment is made. It’s not about extortion—it’s about eliminating recovery.
- Fake Ransom Notes
Anubis mimics known ransomware interfaces, but there’s no evidence that the attackers provide functional decryptors. Some keys are corrupted; others never arrive.
- Backup Destruction
Anubis actively deletes backups, disables Windows recovery, and wipes external drives—leaving victims completely vulnerable.
- Payment Funds Further Attacks
Paying not only fails to solve the problem—it encourages more devastating campaigns. Anubis isn’t just malware; it’s a statement of cybercrime.
How to Protect Your System From Anubis Ransomware Attacks
Protecting yourself from Anubis takes more than just antivirus software. Here’s how to stay ahead:
- Harden Your Email Security
Filter out phishing emails using AI-powered spam filters and sandbox attachments—train users to recognize and respond to threats.
- Patch Regularly
Outdated systems are easy prey. Enable automatic updates across your OS and applications. Monitor for zero-day exploits.
- Backup Smarter
Use offline and immutable backups. Store copies in multiple geographic locations. Finally, test recovery frequently.
- Use Advanced Endpoint Protection
Implement EDR solutions that monitor behavior, detect anomalies, and block encryption in real-time.
- Limit Application Access
Restrict what can run by using application whitelisting. Separate networks to prevent infections from spreading laterally.
- Stay Informed
To stay up-to-date on emerging strategies, follow cybersecurity alerts, threat information streams, and community sites like MISP.
What to Do If Anubis Ransomware hits you
If you suspect that you’ve fallen victim of an Anubis attack, act fast:
- 1. Disconnect Affected Devices Immediately
Keep infected systems separate from other systems to prevent the spread of infection. Cut off the infected computer from the internet and other networks. Turn off Bluetooth and Wi-Fi. The idea is to isolate Anubis from moving to other systems or getting to cloud backups.
⛔ Do not reboot the device unless directed to do so by an incident response professional, as it may trigger additional payloads or wiping routines.
- 2. Notify Your Cybersecurity Team
If you work for a corporation, it’s essential to establish your incident response strategy. Inform your legal and cybersecurity departments. If you’re the lone user, contact specialists or NoMoreRansom.org for ransomware support.
- 3. Identify the Malware Variant
Use an appropriate program to upload the ransom note or an encrypted file. If you know it’s Anubis, you can determine what recovery solutions are available and which ones are not.
- 4. Preserve Evidence
Don’t delete encrypted or damaged files yet. Save ransom notes, email headers, system logs, and any suspicious files. These can help investigators trace the source or understand the attack vector.
- 5. Avoid Paying the Ransom
As covered earlier, paying Anubis is extremely unlikely to result in file recovery. Moreover, it finances further attacks and may even invite future targeting. Focus instead on containment, forensics, and safe restoration
- 6. Rebuild from Clean Backups
Wipe and reformat the system, then restore from a checked, offline backup. Recovery may be impossible without backups.
- 7. Report the Incident
If your firm or area has established rules for reporting cybercrime (such as the NCA in the UK, CISA in the US, or CERT in Nigeria), follow them. This helps keep an eye on global trends and informs others.
The Future of Ransomware: Why Anubis Is a Warning Sign
Anubis is not an isolated case. It’s a sign of where ransomware is headed.
- Sabotage Over Profit
We’re seeing a shift toward psychological, destructive attacks that aim to damage reputations, morale, and infrastructure.
- Rise of Wiper Hybrids
Like NotPetya before it, Anubis masquerades as ransomware while actually functioning as wiperware. Expect more of these hybrids.
- Broader Target Range
While small businesses and individuals are current victims, larger institutions may soon fall prey—especially those lacking resilience.
- Security Must Evolve into Resilience
Prevention alone isn’t enough. You need layered defense, tested backups, and response plans. In this age of chaos malware, recovery readiness is everything.
How to Protect Company from Anubis?
To sum up, Anubis is a particularly nasty strain of ransomware that not only encrypts data but also includes a “wiper” module capable of permanently destroying files, making recovery impossible even if a ransom is paid. It operates as a Ransomware-as-a-Service (RaaS) model, meaning it’s readily available to various cybercriminals, and targets Windows, Linux, NAS, and ESXi environments. However, Storware Backup and Recovery can significantly protect companies against Anubis ransomware by focusing on core principles of robust data protection:
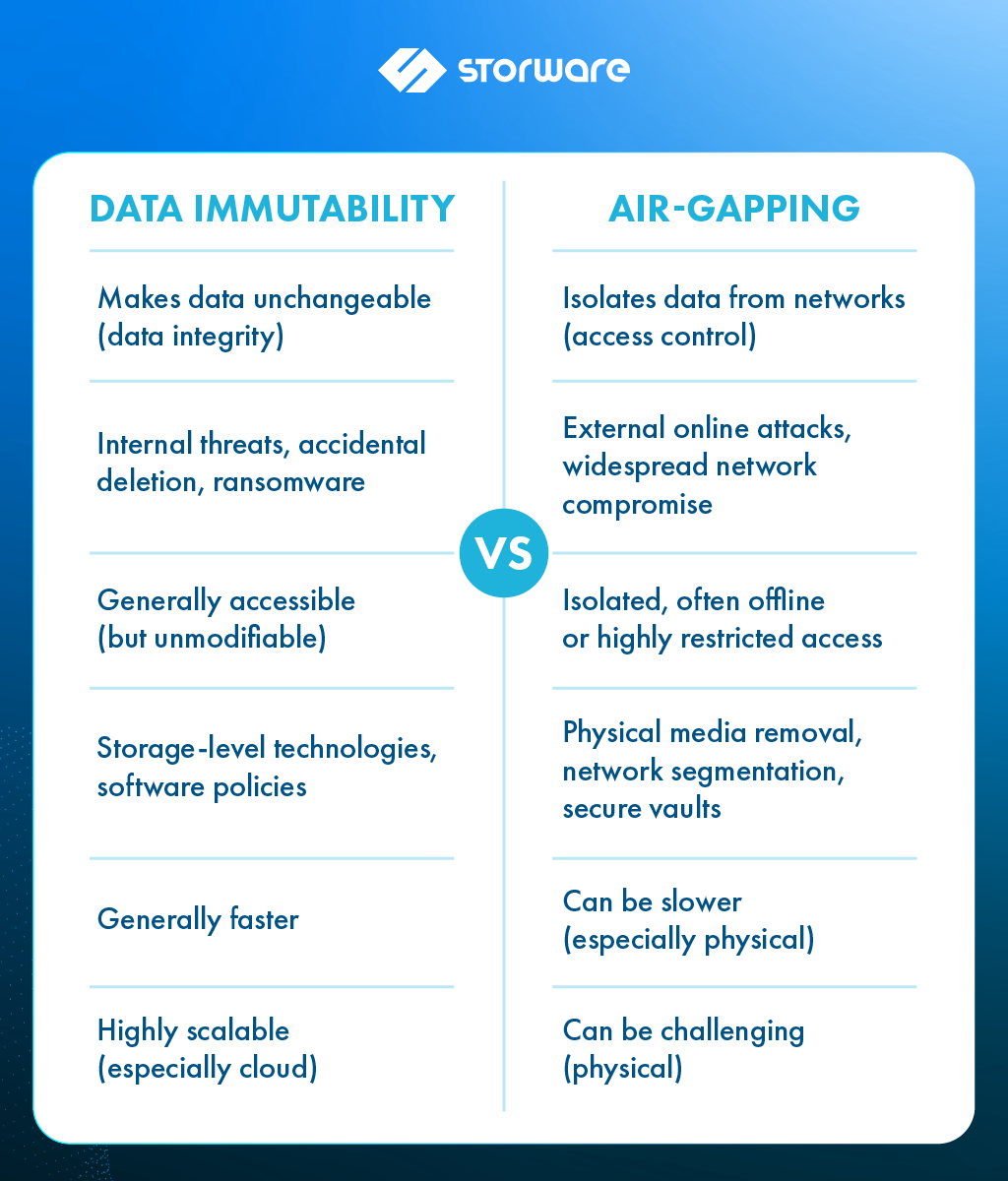
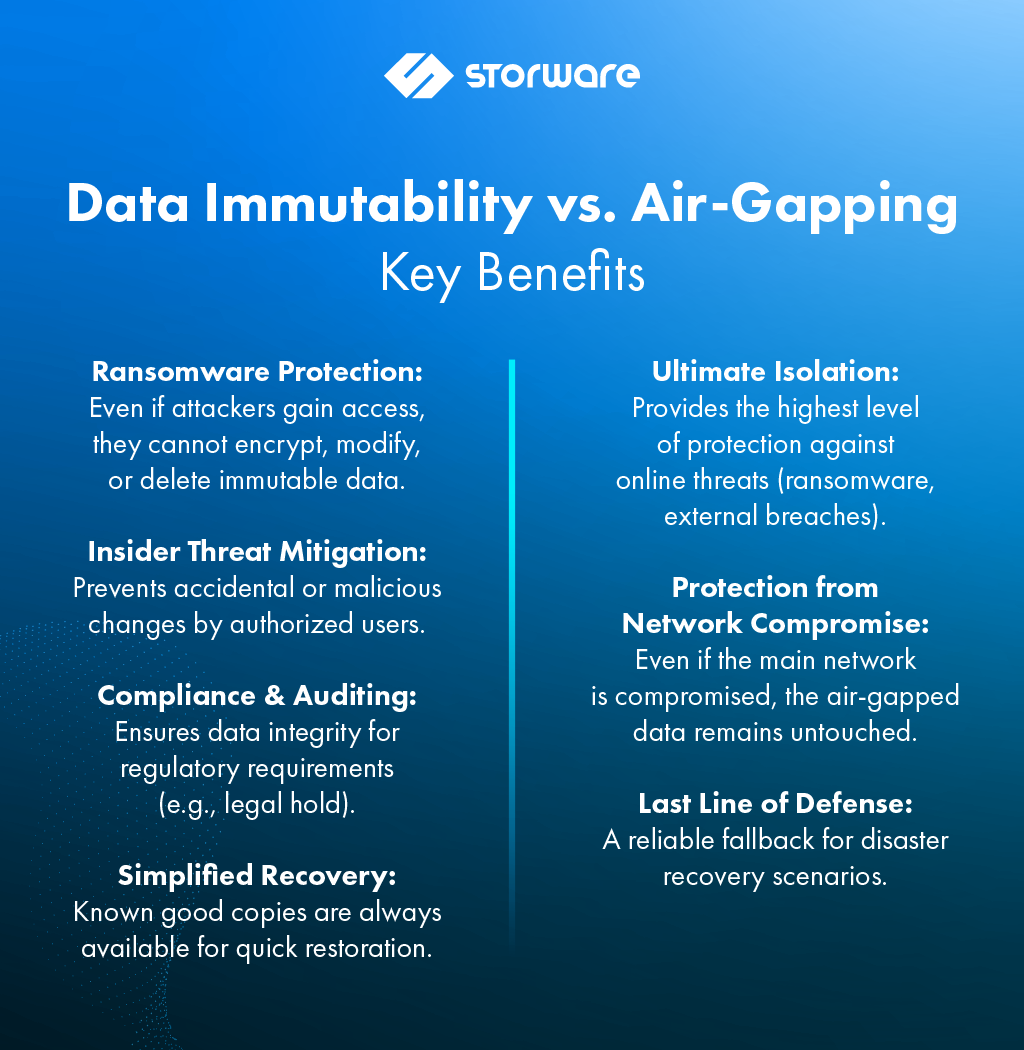
- Immutable Backups: Storware supports immutable storage destinations, which means once data is written, it cannot be altered, deleted, or encrypted by ransomware. This is a critical defense against Anubis’s wiper functionality, as even if the active data is destroyed, a clean, unmodifiable copy remains.
- Air-Gapped Backups: Storware facilitates air-gapped backup strategies. This involves creating a physical or logical separation between primary data and backup systems. By having backups offline or segmented from the network, they become inaccessible to ransomware, even if the primary network is compromised. This is highly effective against Anubis’s ability to spread across domains and target backup systems.
- Multiple Backup Destinations (3-2-1 Rule): Storware encourages adhering to the 3-2-1 backup rule
- Agentless Architecture (for certain workloads): For some environments like virtual machines, Storware offers an agentless approach, reducing the attack surface. This means fewer agents on individual machines that could potentially be exploited by ransomware.
- Granular Recovery: Storware enables granular recovery, allowing companies to restore specific files, folders, or even entire virtual machines from a clean backup point. This minimizes downtime and data loss in the event of an Anubis attack.
- Snapshot Management: Storware provides stable, agentless snapshot management for virtual machines and other environments. Snapshots can be taken frequently, offering granular recovery points and allowing organizations to revert to a state before an infection occurred.
- Support for Diverse Environments: Anubis targets various environments (Windows, Linux, NAS, ESXi). Storware’s broad support for virtual machines, containers, cloud instances, applications, and endpoints ensures that a wide range of company data can be protected.
In essence, Storware Backup and Recovery empowers companies to protect against Anubis ransomware by providing a reliable and resilient backup infrastructure that emphasizes immutability, isolation, and multiple recovery points. This significantly reduces the impact of an attack and enables a swift recovery, even in the face of Anubis’s destructive wiper capabilities.
Final Thoughts
In 2025, ransomware attacks underwent significant changes. It is no longer just a financial burden; it is now a weapon. Anubis indicates that future cyberattacks will combine stealth, accuracy, and damage, targeting not only your data but also your confidence in recovery.
For individuals and organizations, the message is clear: don’t wait for the encryption screen to act. Start treating ransomware defense like disaster planning, because with threats like Anubis on the loose, that’s precisely what it is.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About Storware
Storware is a backup software producer with over 10 years of experience in the backup world. Storware Backup and Recovery is an enterprise-grade, agent-less solution that caters to various data environments. It supports virtual machines, containers, storage providers, Microsoft 365, and applications running on-premises or in the cloud. Thanks to its small footprint, seamless integration into your existing IT infrastructure, storage, or enterprise backup providers is effortless.