Last Saturday (18), the digital world was shocked by another episode of data leaks, and the protagonist this time was Twitter. That’s right, hackers were able to steal data from users of the microblogging platform. And it was not ordinary users, but celebrities, public people and even organizations with millions of followers who had their data exposed, including the use of bitcoin wallets in the scheme. Although it is still under investigation, it is already clear that this episode exposed a major vulnerability of Twitter.
But what were the dynamics of this attack? Also, in times of elections, can we trust the process of choosing future leaders?
By targeting the accounts of world leaders and celebrities on Twitter, hackers managed to orchestrate an attack based on social engineering, and thus promote a scheme involving cryptocurrencies through administration tools of the social network itself. According to the Verizon Data Breach Investigations Report 2020, 22% of the nearly 4,000 incidents and security attacks surveyed involved social engineering. Bill Gates, Elon Musk, Barack Obama, Warren Buffet, and even US presidential candidate Jon Biden were some of the hacked profiles. Not to mention the Apple and Uber accounts.
But how did these hackers manage to perform this well-orchestrated attack?
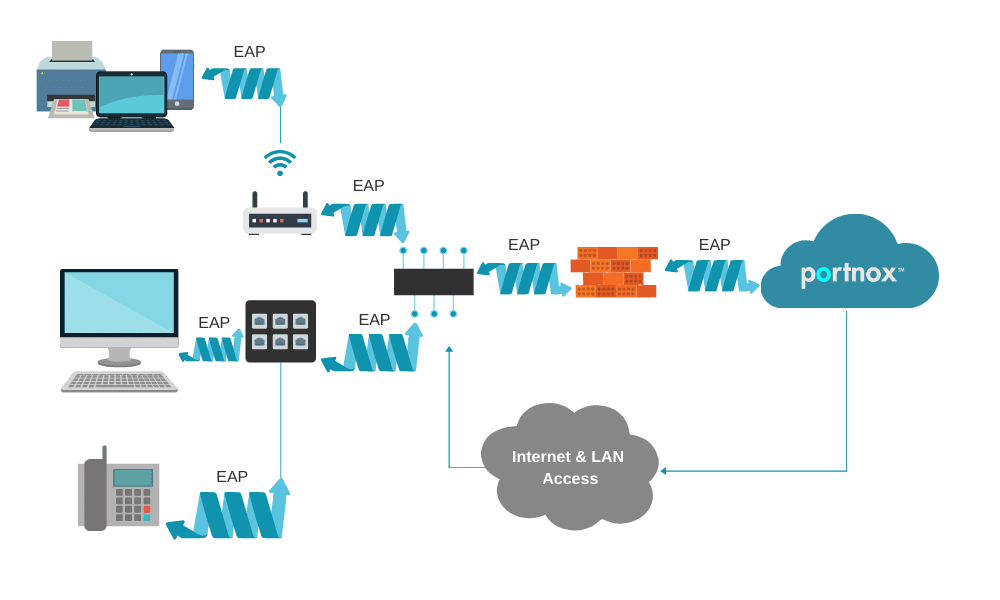
The answer comes in the form of two words: SIM Swapping. SIM Swapping is a technique used by malicious agents that aim to transfer the number and data of the victim’s SIM chip to another one in their possession. In this case, through social engineering attacks, the hacker convinces a telephone line’s user that a problem has occurred with their chip and needs to transfer the number to another. This type of attack requires that some information, such as the number, name, and other data, is already in the attacker’s hands. Depending on the situation, it is not that difficult to obtain this information if it has already been leaked, for example. Similarly, agents can also persuade operators to perform this transfer, since they have access to all data required for the swap.
Through Social Engineering techniques, malicious attackers deceive their victims to gain improper access to credentials and administrative tools. By obtaining this access, hackers changed their victims’ email addresses on the microblogging network. Then, the attackers disabled the two-factor authentication. This makes it possible to prevent any account modification alerts from being received by its legitimate user. With absolute control of the accounts, hackers start promoting the cryptocurrency-based scam scheme.
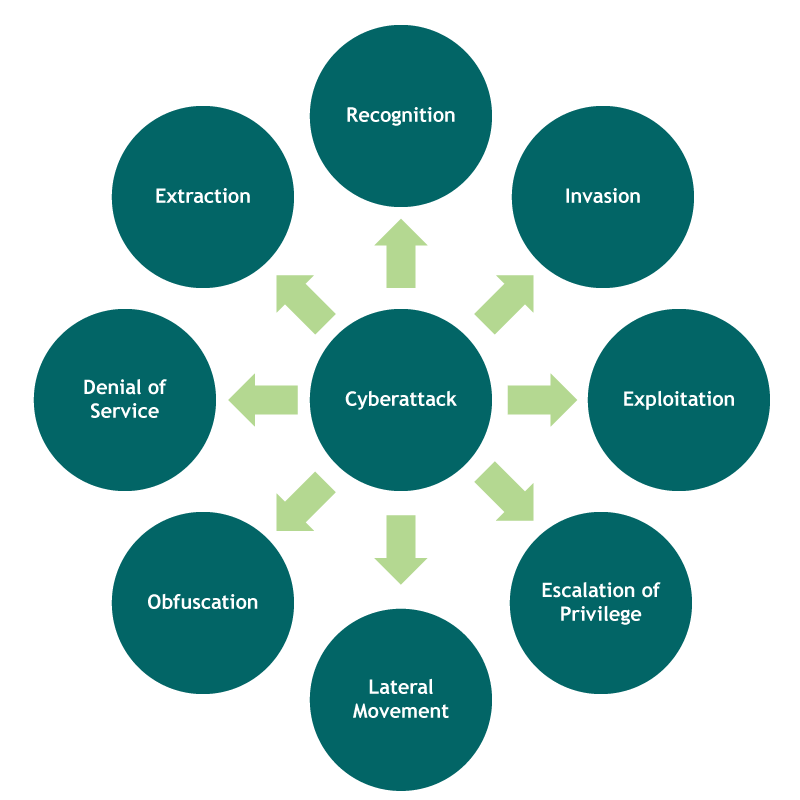
Typically, the logic of a cyberattack like this involves several phases:
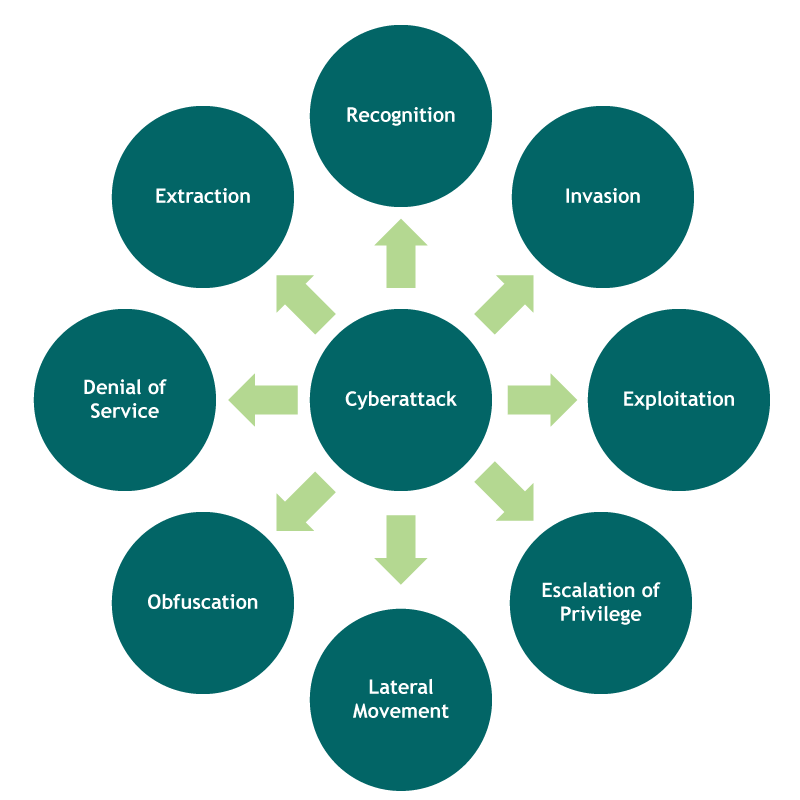
- Recognition: In this first phase, malicious attackers try to identify IT routines, as well as security measures and data traffic flow. Also, hackers scan the entire environment to get a clear view of network resources, as well as privileged credentials and services. Domain controllers, Active Directory, and servers are the attackers’ first targets to find other privileged credentials and complete the cyberattack. In many cases, this prior knowledge may exist due to some previous link between the attacker and the victim organization.
- Invasion: based on what was discovered in the Recognition phase, hackers are able to enter the environment normally through malware or exploitation of vulnerabilities.
- Exploitation: This phase involves the act of exploiting vulnerabilities to compromise the environment.
- Escalation of Privilege: attackers usually need more privileges on systems to gain more access and privileges. This is usually done by escalating administrator privileges.
- Lateral Movement: Once in the infected environment, attackers can move laterally to other devices and credentials, in order to obtain more data and more access.
- Obfuscation: For a cyberattack to be successful, attackers need to erase all tracks left in the environment. At this point, it is even possible to change log data and confuse the incident investigation team.
- Denial of Service: disruption of the normal access by users and systems to prevent the actions of the attack from being monitored or blocked.
- Extraction: when the malicious user is able to improperly extract the data.
A unanimity among cybersecurity professionals is that this attack on Twitter involved privileged or administrative credentials. According to the Data Breach Investigations Report, the use of privileged credentials occurs in 20% of the attacks. This type of credential, also called “keys to the kingdom”, allows access to add, remove, and modify settings in accounts, applications, and systems. In this specific case, the hacker was able to compromise a credential from the Twitter administration tools. By gaining access, the attacker was able to move around the environment, compromising other privileged accounts.
According to confirmation by Twitter itself, the nature of the attack was an insider threat. When it comes to data breaches, employees themselves can be one of the biggest risks to the organization. According to Verizon, these threats can be: accidental, when personnel is only poorly trained; negligent, when employees try to bypass the implemented policies; or malicious – the most dangerous – when an employee is motivated by financial gains, espionage, or revenge. An important fact, according to Verizon, is that 30% of cyberattacks performed in 2019 involved insider threats.
But how to prevent this type of attack?
It is complicated to deal with an attack coming from someone inside the organization. This is mainly because this insider threat knows (very) well the organizational environment, the mechanisms, and tools installed. So, it is easy for these attackers to deceive these control mechanisms. In this case, using Zero Trust-based controls can be a good way to mitigate the risks associated with a cyberattack. In terms of credential protection, the implementation of this strategy must not only be focused on identity only, such as access and permissions, but also on the aspect of user behavior. So much so that, in this specific case, the compromised credentials had protection mechanisms, as two-factor authentication. Finally, Zero Trust-based policies recommend the implementation of policies to allow people to take only the necessary actions, based on the concept of Least Privilege.