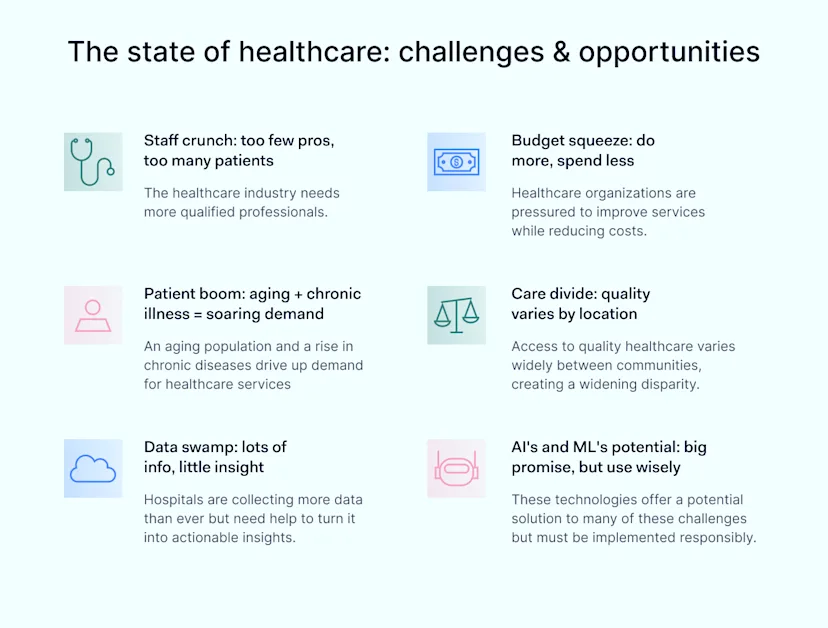
In 2022, a remarkable milestone was reached in the world of healthcare. According to the World Health Organization (WHO), global healthcare expenditures soared by a staggering $12 trillion. However, the impressive figure came with a burden. The health industry faced a dual challenge: staff shortages and the flood of patient data. Generative Artificial Intelligence (AI) emerges as a promising solution, offering revolutionary changes. Yet, alongside its potential, it also raises critical safety concerns.
This article looks at the potential of generative AI in healthcare. It also explores the risks involved in its rapid adoption. Read on to understand how AI could reshape healthcare and what precautions are necessary for its responsible implementation.
The healthcare in crisis
Under pressure: the health industry
As the pandemic spread, it stretched global healthcare systems thin. The World Economic Forum warns of growing worker shortages, widening health differences, and unsustainable spending. Moreover, by 2030, a staggering shortfall of 10 million healthcare workers globally is anticipated, highlighting the urgency of addressing the gaps.
The digitization challenges: riding the data wave
As hospitals started their journey to digitalize their customer records and operations, they faced a surge in data. Efficiency was the goal, but this integration demanded equipment investment and staff training. It’s projected that global healthcare data will surpass 10 zettabytes, that is 1,024,000,000,000,000 gigabytes, by 2025. Perhaps more concerning is the revelation that over 70% of healthcare providers across various nations are struggling with the volume of patient data.
Embracing technological adaption
To maintain the highest standards of healthcare quality, hospitals must adapt swiftly to this digital transformation. Technologies, particularly generative AI, stand ready as potential game-changers. Consider the rise of AI-powered chatbots and call centers employing generative AI methodologies. These digital assistants are pivotal in patient education and assessment, especially in low- and middle-income countries with scarce healthcare resources.
![]()
AI in healthcare: a prescription for progress
Now, let’s examine AI’s role in healthcare, focusing on its applications and innovative potential. As we explore ethical considerations and potential drawbacks, we’ll gain a comprehensive insight into AI’s impact on the healthcare sector.
The potentials and pitfalls of AI: walking the tightrope
While AI promises to transform healthcare by accelerating diagnoses, managing patient data efficiently, and assisting in complex procedures, it’s essential to acknowledge the complexities of this transformation. For example, despite analyses suggesting that an ideal share should exceed 10%, in the US and Europe, a mere 3% of healthcare spending is allocated for preventive care. This discrepancy emphasizes the need for a cautious approach to integrating AI into healthcare.
The financial magnitude and growth of AI in healthcare underscore its transformative potential. The AI healthcare market, valued at $11 billion in 2021, is projected to skyrocket to $187 billion by 2030. This exponential growth indicates the increasing reliance and investment in AI technologies to innovate and enhance healthcare delivery and management.
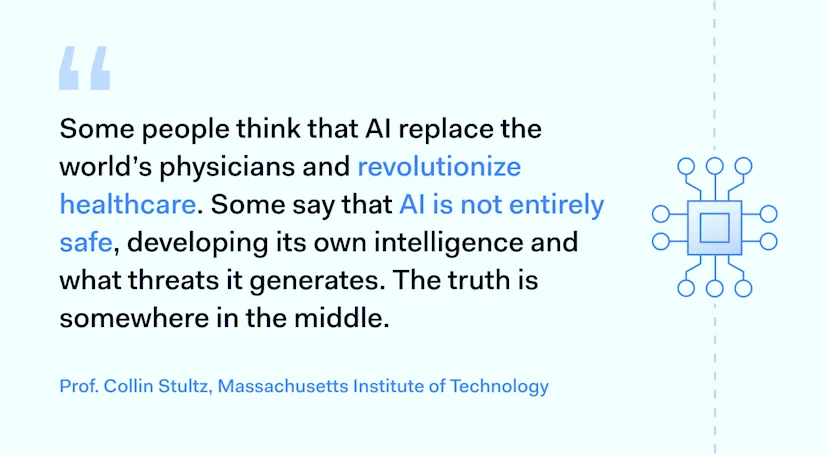
Yet, it’s crucial to navigate this path with caution. Professor Collin Stultz, a cardiologist from the Massachusetts Institute of Technology and an expert in machine learning for cardiovascular care, says that perspectives on AI in healthcare oscillate between viewing it as a panacea for numerous challenges and perceiving it as a potential threat. As is often the case, the truth likely resides somewhere between these extremes.
![]()
Caution and security: protecting healthcare data
The World Economic Forum’s Breaking Barriers to Health Data program suggests creating a consortium where different organizations can share their health-related data, especially about genes. This way, they hope to fill the gap in available genetic information and also improve research and diagnostic capabilities.
For instance, the Mayo Clinic and Pramana’s collaboration to digitize pathology slides. This showcases the practical data usage in healthcare. With the rise of AI in the industry, it’s crucial to understand its capabilities and limitations, especially in the face of increasing data breaches.
Providing robust security measures for sensitive data is vital to maintaining patient trust and safeguarding information. Implementing AI must be approached cautiously, ensuring patient data and healthcare service integrity are uncompromised.
Addressing staff shortages: AI as a helping hand
The WHO estimates a global shortfall of 10 million healthcare workers by 2030, highlighting a critical need to address workforce gaps. AI can step in to alleviate pressure by handling routine tasks, enabling healthcare professionals to focus on complex patient needs. It’s important to note that AI isn’t here to replace human expertise but rather to enhance the efficiency of the human workforce.
AI’s ability to generate insights is also key in designing and executing efficient and inclusive clinical trials. This application enhances the efficiency of clinical trials and ensures they are robust and representative of many populations. For example, H1, a technology company, has used AI to streamline decision-making and accelerate patient recruitment in clinical trials, ultimately lightening the workload on existing staff.
AI in action: transformative cases in healthcare
Artificial Intelligence notably influences drug discovery and clinical trials in the pharmaceutical industry. Let’s now explore real-world examples that demonstrate its profound impact.
AI in drug discovery: unknown avenues
AI is ushering in a new era in drug discovery, offering new pathways to understand disease mechanisms and formulate targeted treatments. Consider Benevolent AI, a prime example, which applies AI to identify patient subgroups that respond most favorably to specific treatments. This approach enhances treatment precision and reveals new therapeutic possibilities by providing deeper insights into disease processes.
Also, tools based on deep learning uncover novel insights into the underlying disease mechanisms and identify new therapeutic assets. Companies like DeepMind and Benevolent AI are pioneering this innovative approach.
Streamlining clinical trials: faster, smarter, and more inclusive
The journey from drug discovery to patient benefit is usually lengthy, often stretching over 15 years. However, it can be shortened with AI stepping in and optimizing critical processes, such as site selection and participant recruitment, ensuring that life-changing treatments reach patients faster.
H1, a pioneering AI platform, is making waves in the pharmaceutical industry by facilitating quicker decision-making processes. It has successfully reduced site failures and accelerated patient recruitment in clinical trials, shaving off weeks, if not months, from the typical timeline.
Enhancing clinical trial design: a revolution in progress
AI is not only helping streamline clinical trials. It also revolutionizes their very design, ensuring that they both are efficient and representative of diverse populations.
One critical aspect of enhancing clinical trials is tailoring messages and recruitment strategies to attract the right patients. AI is bridging the gap by connecting doctors with clinics capable of recruiting suitable participants. This approach improves the efficiency of clinical trials.
For instance, Johnson & Johnson, the industry giant, uses AI-based data analysis to innovate how medicines are discovered and developed. By improving patient data, AI generates insights that empower clinical research teams to design and execute more targeted and inclusive clinical trials.
The potential of AI in pharmaceuticals
Integrating AI in drug discovery and clinical trials will revolutionize the pharmaceutical industry. This acceleration, combined with optimizing clinical trials, highlights AI’s transformative and innovative power in healthcare. It opens up a new horizon of possibilities and advancements that bring treatments to patients more swiftly than before.
The financial stakes of AI in healthcare are staggering. This market’s growth indicates a substantial investment and reliance on AI technologies to innovate healthcare delivery and management.
AI: optimism versus skepticism
The dialogue surrounding AI in healthcare is multifaceted, with both enthusiasts and skeptics presenting compelling arguments. Advocates highlight AI’s potential to revolutionize healthcare, emphasizing its capacity to enhance efficiency, improve diagnostic accuracy, and pave the way for personalized medicine.
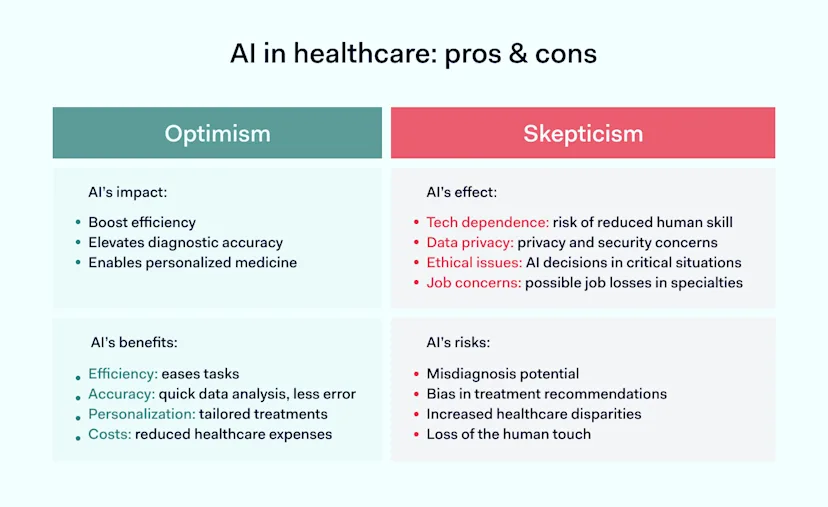
As Prof. Collin Stultz from MIT points out, the reality of AI’s role in healthcare likely lies somewhere between these extremes of optimism and skepticism. Striking a balance becomes essential, harnessing the potential benefits of AI and mitigating associated risks.
AI brings notable advancements in healthcare but also introduces ethical dilemmas, especially concerning data usage and algorithmic biases. The conversation often revolves around maximizing AI’s capabilities while ensuring ethical, transparent, and equitable use.
AI promises to revolutionize healthcare but also presents practical challenges, such as regulatory compliance, system interoperability, and algorithm efficacy validation.
The ongoing debate is between AI’s theoretical potential and the practical challenges of its implementation, calling for a pragmatic approach that acknowledges both its promises and pitfalls.
Also, the discussion about the human element in AI-driven healthcare focuses on augmenting professionals’ capabilities versus the risk of care dehumanization and technology over-reliance.
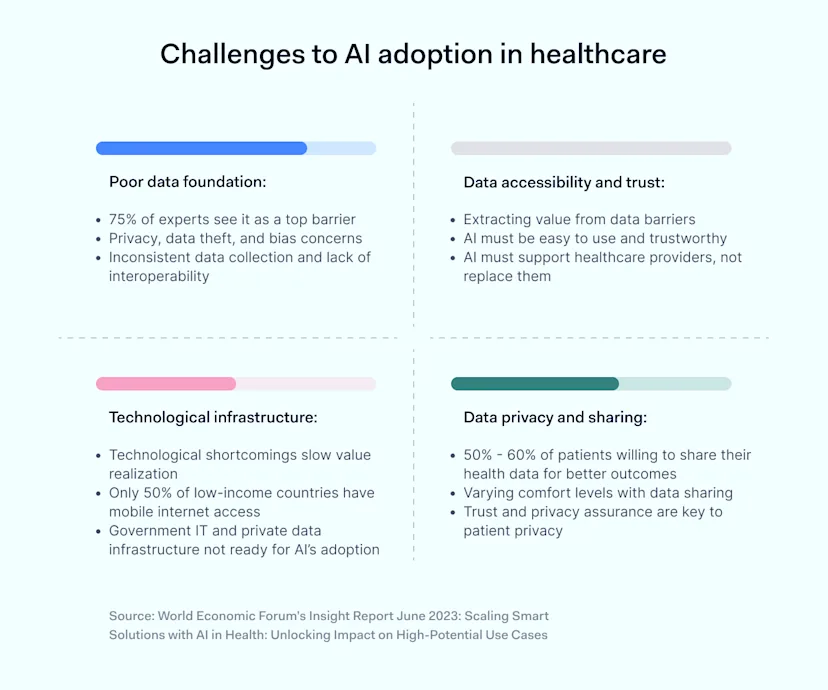
Potential risks of AI
As the integration of AI into healthcare continues to advance, it brings with it a set of challenges and concerns. From data privacy issues to ethical dilemmas, the healthcare sector must tread carefully to ensure that the adoption of AI enhances patient care without compromising safety or trust.
![]()
Data security and breaches
One of the biggest concerns with AI in healthcare is data security. Hospitals and clinics store highly sensitive information, like medical history and personal details.
Data breaches in healthcare are becoming more common, and that’s a big red flag when we’re talking about using AI to manage patient data. So, how can we make sure AI is safe to use?
First, any AI system has to meet strict security standards before it even gets near patient data. This means heavy-duty encryption and multiple layers of security checks. Also, regular audits and monitoring can help catch any unusual activity before it becomes problematic.
While AI has much potential to improve healthcare, it also comes with risks that must be managed carefully. Data security is at the top of that list, which healthcare providers and tech companies must take seriously.
Steps to ensure data safety
Best Practices for Secure AI Integration
Safety is a top priority for integrating AI into healthcare, especially concerning data security. There are still ways to ensure patient data remains secure when using AI systems.
Strict access control: limit who can access the AI system and the patient data it uses. Only authorized personnel should have access, and even then, only to the extent necessary for their role.
Data encryption: all data in transit should be encrypted; this can be achieved with a solution like NordLayer. This makes it much harder for unauthorized users to make sense of the data even if they manage to access it.
Regular security audits: conduct regular security audits to identify any vulnerabilities. This should include both the AI system itself and the broader data infrastructure.
Multi-factor authentication (MFA): MFA requires multiple verification forms before granting sensitive systems or data access. This adds an extra layer of security that can deter unauthorized access.
In-house AI tools: while third-party solutions may not always meet your needs, developing in-house AI tools allows for customized security measures tailored to your organization’s unique requirements.
User training: educate healthcare staff on the importance of data security and the best practices for using AI systems. A well-informed team is a crucial line of defense against potential breaches.
Incident response plan: plan how to respond if a data breach occurs. Quick action can minimize damage and help restore system integrity.
By following these best practices, healthcare providers can take significant steps toward ensuring that the integration of AI into their systems is as secure as possible. While AI presents new challenges in data security, careful planning and stringent measures can mitigate these risks.
Conclusion
Reflecting on the need for AI in healthcare, it’s evident that AI presents promising solutions while the sector grapples with challenges such as staff shortages and intricate data management. Yet, with these advancements come inherent security risks. As we delve deeper into the digital transformation of healthcare, responsible AI implementation paired with stringent security measures becomes paramount. Consider NordLayer to protect your sensitive data for a secure digital future.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.