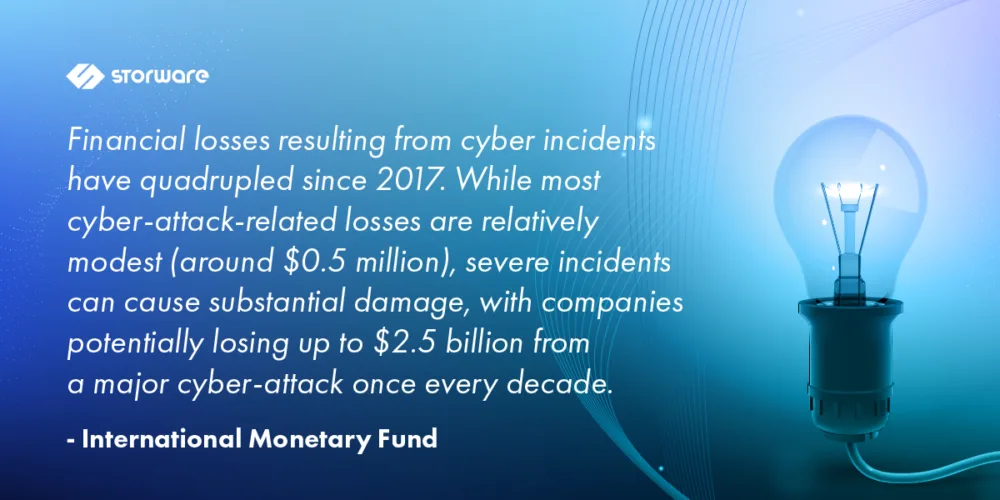
The efficiency and reliability of backups are becoming increasingly important. Statistics on incidents are staggering, and there are also internal infrastructure problems. The growing cryptocurrency market allows for the unpunished collection of ransoms. And companies themselves do not want to inform the public about problems, because they additionally expose themselves to image losses.

Decision-makers are becoming aware that a cyberattack or failure can paralyze the work of a company or institution at any time. Nowadays, you have to be prepared for the worst-case scenario and have a proven plan on how to quickly return to normal work mode when something bad happens.
The definition of IT infrastructure downtime is not unambiguous. However, it most often refers to time not spent on productive work as a result of a cyberattack.
Of course, sometimes such downtime is the result of internal errors, natural disasters, or incorrect configuration of IT systems.
The activity of companies can be stopped for several hours, but sometimes the downtime lasts longer. This was the case, for example, with the well-known American brewery Moison Coors in 2021. The cyberattack halted the operation of the plant for several weeks, which made it impossible to produce almost 2 million hectoliters of beer. As you can easily guess, the financial losses were huge. Similar, though no less dramatic, examples can be multiplied endlessly.

In order to minimize the risk of a cyberattack, enterprises use various methods: they implement advanced security systems and introduce cybersecurity training. Prevention is important, but you must always be prepared for the worst-case scenario. Therefore, business continuity plans are implemented, which establish procedures for creating backups and recovering data after a failure.
More Data, Longer Backup Window
The constant increase in data means that the backup window is extended. Meanwhile, the business needs of companies and the allocation of resources are completely different. Backup, in an ideal world, should happen in the background and not interfere with the main tasks of the IT infrastructure. Is it possible to reconcile one with the other?
It seems that everything is a matter of scale. This depends on the company’s profile, its size, as well as the type and amount of data processed. In the case of small production plants, the efficiency of the backup is not so important. However, there are many sectors of the economy where even a short failure means a serious drop in revenue. In addition to operational delays, there are issues related to compliance, for which severe financial penalties are threatened.
At first glance, planning a backup process seems to be relatively simple – just enough storage media for storing data and some software. However, the larger the organization, the greater the scale of difficulties, because the efficiency of creating backups is influenced by a whole lot of factors.
The basic issue during planning is the identification of computers covered by the backup. And it is not just about their number, but also operating systems, network technologies, any connected disks or tape drives, as well as applications whose backups need to be performed, e.g. Microsoft Exchange.
You also need to consider the types of data, such as text, graphics, or databases. How compressible is the data? How many files are involved? Will the data be encrypted? It is known that encrypted backups may run slower.
What Type of Backup to Choose?
When planning a backup, one of the three available methods is selected: full, incremental, differential. Making the right decision has an impact not only on the amount of disk space needed, but also the time of restoring and saving data. However, the first backup will always be full (and usually its execution takes the longest).
Choosing the right variant is not an easy matter and there is no golden mean here. Each of the methods mentioned earlier has weaknesses and strengths.
Performing a full backup is time-consuming and requires a lot of disk space, but in return it provides full protection and the ability to quickly restore all data.
The alternative is an incremental backup: after creating a full backup, the process of creating incremental backups follows, in which information about data changes since the last backup is saved. The user does not consume too much space in the data store. The process of creating copies is fast. The downside is the slow data recovery time.
The third option is a differential backup, where only data that has changed since the full backup is considered. The process is repeated until the next full backup is performed. In this case, the full backup is the point of reference for creating subsequent copies. Thanks to this created backup, it is possible to quickly restore the complete set of data. This option is recommended for frequently used and changed files. However, the more time passes from the last full backup, the differential files grow, which can extend the time of creating the backup. Although a differential backup is more economical than a full one, it may take up more space than an incremental one if the data is frequently changed.
Choosing the right backup strategy is crucial, and the complexity increases with organizational size. Factors like data types, compression, encryption, and the choice between full, incremental, and differential backups all play a role. Solutions like Storware can help simplify this process by automating backup schedules, flexible backup types, and providing centralized management. This allows organizations to tailor their backup strategy to their specific needs and optimize for both efficiency and recovery time.
RTO (Recovery Time Objective)
The maximum allowable time for which a system, application, or business process can be down after a failure or disaster, before the consequences become unacceptable, is determined by the RTO (Recovery Time Objective) factor.
For example, a company provides project management software in a cloud model, and the RTO is 8 hours. If the servers in the cloud fail due to a technical problem or a cyberattack, the IT team has eight hours to restore the service before it negatively affects customers. If you do not meet the 8-hour RTO, customers may be cut off from access to critical project data for too long, leading to delays in their work.
RPO (Recovery Point Objective)
It is important not only the type of copies made and the time of their recovery, but also the frequency of their creation, which has a direct impact on the requirements for the carrier, the speed of data transfer and the ability to restore. In a large, modern factory, the loss of critical data can lead to the downtime of the entire production line. Consequently, the company is exposed to losses of many millions.
Financial institutions, which carry out a huge number of transactions online, or cloud service providers are in a similar situation. In such situations, the RPO (Recovery Point Objective) indicator, which determines when to make a backup so that the occurrence of a failure does not significantly affect the continuity of the company’s operational work, should be close to zero. As you can easily guess, this is not a cheap solution, requiring redundant creation of backups and data replication in real time.
Examples of RTO and RPO in Different Industries
Healthcare
- RTO: A hospital’s electronic health record (EHR) system might have an RTO of 4 hours, meaning it must be restored within 4 hours to avoid significant disruption to patient care.
- RPO: The same hospital might have an RPO of 1 hour for the EHR system, meaning that no more than 1 hour of patient data can be lost in the event of a system failure.
Financial Services
- RTO: A bank’s online banking platform might have an RTO of 1 hour, meaning it must be restored within 1 hour to avoid significant customer inconvenience and potential financial losses.
- RPO: The same bank might have an RPO of 30 minutes for its core banking system, meaning that no more than 30 minutes of transaction data can be lost in the event of a system failure.
E-commerce
- RTO: An e-commerce website might have an RTO of 30 minutes, meaning it must be restored within 30 minutes to avoid significant revenue loss and customer dissatisfaction.
- RPO: The same e-commerce website might have an RPO of 15 minutes for its product catalog database, meaning that no more than 15 minutes of product data can be lost in the event of a system failure.
Manufacturing
- RTO: A manufacturing plant’s production line control system might have an RTO of 2 hours, meaning it must be restored within 2 hours to avoid significant production delays and potential financial losses.
- RPO: The same manufacturing plant might have an RPO of 1 hour for its inventory management system, meaning that no more than 1 hour of inventory data can be lost in the event of a system failure.
Important Considerations
- The specific RTO and RPO values for a given system or application will depend on the organization’s business requirements and risk tolerance.
- Organizations should conduct a business impact analysis (BIA) to determine the potential impact of downtime and data loss on their operations.
- RTO and RPO values should be regularly reviewed and updated to ensure they remain aligned with the organization’s business needs.
Meeting stringent RTO and RPO targets requires a robust and reliable backup and recovery solution. Storware offers [mention specific Storware features related to RTO/RPO, e.g., fast recovery capabilities, near-zero RPO with replication, automated failover, etc.] enabling businesses to minimize downtime and data loss in the event of a disaster. By leveraging such solutions, companies can confidently meet their recovery objectives and ensure business continuity.
Data and Backup Storage
Some organizations do not distinguish between data storage and backup. The first process is usually dictated by legal requirements, which specify how long digital information should be stored. In addition, we have rules when and how to delete them when they are no longer needed.

Legal requirements for data storage include:
- Sarbanes-Oxley Act (SOX),
- European General Data Protection Regulation (GDPR),
- Payment Card Industry Data Security Standard (PCI-DSS)
- and the Health Insurance Portability and Accountability Act (HIPAA).
On the other hand, storing backups determines how long an additional copy of the data must be maintained in the event of loss, damage, or disaster.
While data storage and backup are distinct processes, they are closely intertwined. A comprehensive backup solution like Storware can integrate with existing storage infrastructure and help organizations manage their backup retention policies effectively. This ensures compliance with legal requirements while optimizing storage costs and simplifying backup management
Most companies make the mistake of keeping backups for too long. Statistically, data recovery most often takes place on the basis of the latest versions, and not those from six months ago or older.
Therefore, it is worth realizing that the more data contained in the backup infrastructure, the more difficult it is to manage and the more it costs.
Summary
The issues mentioned in this article do not exhaust the issues related to backup performance. In the next material, we will take a closer look at carriers, network connections, deduplication and compression, as well as the most common errors leading to a decrease in backup performance.