Modern businesses heavily rely on internet access for communication and collaboration. This also makes it the #1 channel for cybercriminals trying to access sensitive data. This modern threat landscape is a critical cybersecurity challenge that businesses must be aware of and be prepared to defend against.
Therefore, in this blog post, we’ll discuss the importance of internet access security for businesses operating in all work models, including remote, office, and hybrid. With the number of cyberattacks ramping up, it’s crucial not to hope for the best and believe it will never happen to your company.
What internet access security challenges affect businesses?
Businesses hold and manage large amounts of sensitive data, including customer information, financial data, and trade secrets. If this information isn’t properly secured, unauthorized users can obtain access to it, causing a data breach.

Remote work challenges
During the COVID-19 pandemic, remote work has been the norm for many companies. Even after the quarantines had ended, many businesses kept working from home. While remote work brings benefits and flexibility, it also comes with challenges.
Use of personal devices
The practice of employees bringing their own device for work-related tasks, known as (BYOD), became widespread during the pandemic. Employees hired remotely usually had no personal contact with IT administration, so they worked with their home devices.
The risk lies in the fact that they’re unmanaged and may lack the same level of security as company-issued devices. These circumstances leave them vulnerable to all kinds of attacks, with limited capabilities for IT administrators to stop them.
Unsecure networks
Home networks may not have the same level of security as properly managed corporate networks. Employees using outdated or vulnerable network devices are more susceptible to exploits that hackers could use to gain entry into company systems.
Remote employees are solely responsible for securing their own devices, but they may not always have the necessary knowledge to do it effectively. This also allows hackers to initiate phishing messages or cause disruptions.
Access control
When allowing employees to work remotely, a security policy should clearly state how and who can access sensitive data. Without such a policy, organizations may fall into the trap of being unable to verify who is accessing their networks or data. This is a sure route to costly data breaches and reputational damage.
In addition, compliance regulations like GDPR and HIPAA require organizations to have robust access control policies to protect sensitive data. Failure to do so may result in legal liabilities and hurt business financially.
Office work challenges
While working in the office seems more secure than remote work in most managers’ eyes, it’s not immune to various security threats. In fact, several cybersecurity risks may be more prevalent for employees working in an office than in other models.
Social engineering
Social engineering attacks target the human aspect of security, making them harder to detect and prevent. Very little stands in a dedicated hacker’s way if they plan out a fake identity, impersonating legitimate employees, and using other psychological tactics. For example, tailgating is based on following a genuine employee through the door without authorization.
Employees in an office environment have physical access to sensitive documents and data. This can mean that once a hacker is inside the building, all the sensitive data can be compromised (or stolen).
Insider threats
While network segmentation helps to introduce boundaries that prevent users’ lateral movement in the network, all these boundaries are much more fluid in an office setting. Employees may write their passwords on sticky notes and leave them on their desks, which is something that malicious colleagues could exploit.
In-office identity thefts and malicious leaks may be harder to stop or detect. Additionally, deliberate leaks or theft of physical documents and devices by someone working on-premises are scenarios that an IT manager should prepare for.
Hybrid work challenges
Hybrid work, which combines remote and office models, adds up challenges from both approaches. Employees must be provided with secure methods to connect to hosted resources when working remotely. Meanwhile, when they’re back in the office, they need to be vigilant about risks they could be lurking in shared spaces. This makes the hybrid model the most difficult to secure.
Double the maintenance
Hybrid work puts a huge strain on IT administrators. They must simultaneously support and manage two fronts: office employees must be provided with secure network access when working on-premises and remote employees must be provided with secure routes into their network.
Both modes must be compatible, operate without interruptions, and be secure. It’s an intricate system with many moving parts, so naturally, it’s much harder to supervise.
Increased physical security risks
Hybrid employees carry work devices back and forth between the office and their homes, increasing the risk of theft or loss. A lost device may not be a serious risk if properly secured with strong passwords or encryption. However, if not, it could easily lead to a data breach.
Additionally, working in public areas or during transit increases the potential for shoulder surfing attacks, when an attacker can physically view the device screen. As the attacker needs to be physically close to their victim, this has become quite prevalent with the growing popularity of hybrid work models.
Why is internet access security important for businesses?
Modern-day enterprises heavily rely on the internet to enable all kinds of their operations. As a result, its secure access is important, regardless of the connection method an organization uses. Achieving secure internet access also enables businesses:
-
Protecting sensitive information. Unsecured communication channels may lead to the loss of sensitive information, which could be disastrous for a company’s reputation and cause legal complications.
-
Mitigating cyber threats. Mostly, the internet is a publicly used platform, and it exposes businesses to various risks like malware, phishing, and hacking attempts.
-
Complying with regulations. Many industries are subject to regulations requiring them to maintain strict security measures. Failure to comply can result in heavy fines or legal repercussions.
-
Ensuring business operations continuity. Cyberattacks have the potential to disrupt day-to-day business operations, leading to downtime and lost revenue.
By tackling internet access security challenges, businesses can avoid risks and establish a proper foundation for uninterrupted growth and operational continuity.
How do businesses secure their internet access against various threats?
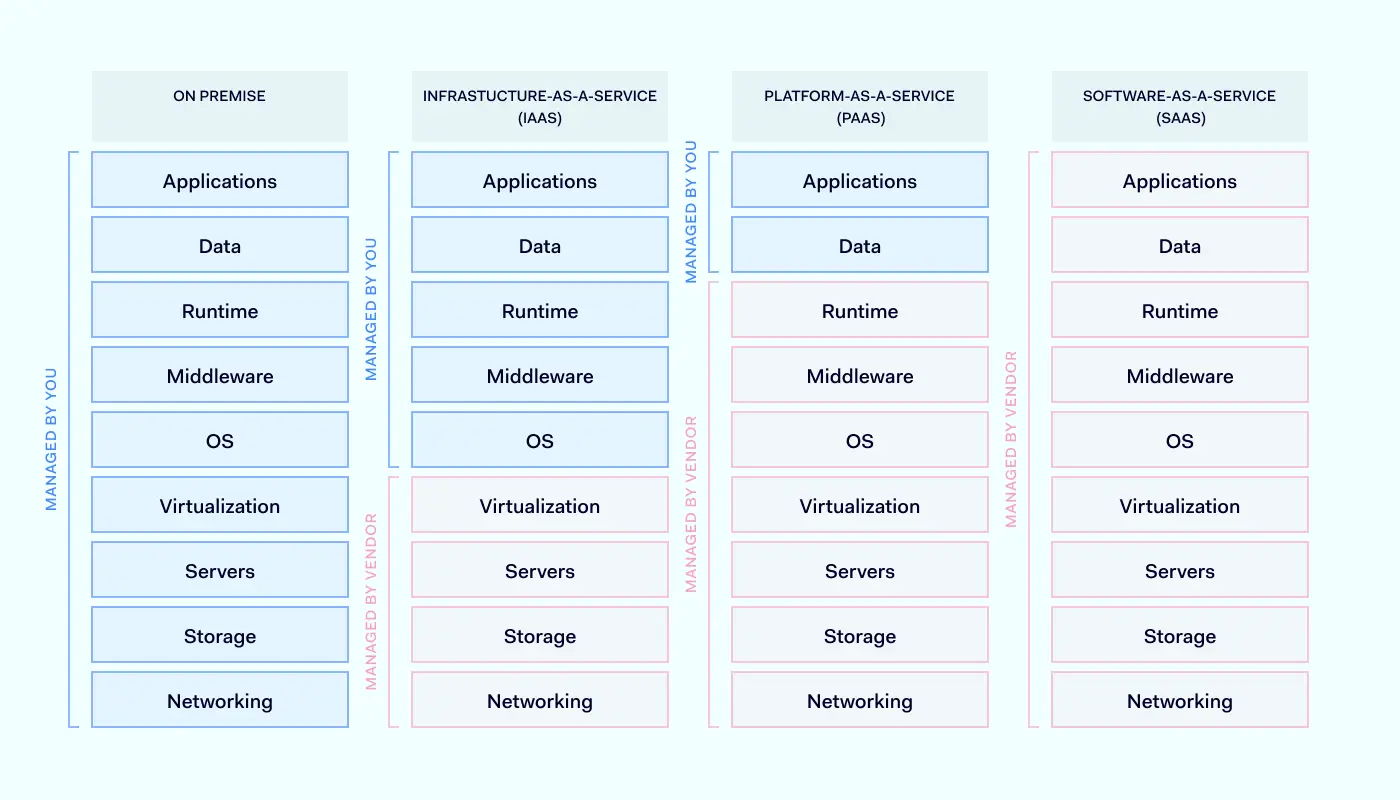
Securing work environments against threats can vary depending on the business size and risks faced by businesses. Some companies have the manpower and resources to build their own in-house solutions. Others take the simplest approach and turn to a third-party provider adopting their already established tools. Here are two real-life examples.
Whatagraph
A digital marketing reporting platform, Whatagraph transitioned to a hybrid work model when faced with the challenge of local talent shortage. This also meant that they needed to figure out how to allow their remote hires to connect securely to their infrastructure. A comprehensive cybersecurity solution establishing a private gateway to the company’s data and applications was an obvious choice. As Whatagraph is a rapidly scaling company, the solution must also integrate admin features and provide uncomplicated scaling.
To address their needs, Whatagraph turned to NordLayer, using it mainly as a business VPN back when it was still called NordVPN Teams. They leveraged NordLayer’s Virtual Private Gateways with dedicated IP addresses to securely connect to their company network, sealing the sensitive data in an encrypted tunnel.
What also helped was that NordLayer seamlessly integrated with their existing solutions, eliminating the need for additional technical integration. This provided Whatagraph with optimal internet access security within minutes.
Atlantis Games
A mobile game development company, Atlantis Games, found themselves trapped in a corner when manual user handling ways weren’t keeping up with their growth. Initially, their setup was manually allowlisting individual users’ IP addresses, which worked for a small team. However, once a business expanded and developers and customer support specialists needed multiple IP addresses, the manual approach proved to be too much of a task.
NordLayer came to the rescue by providing a smoothly running client with uninterrupted connections. By using Virtual Private Gateways with IP allowlisting for organization members, Atlantis Gamest eliminated the need for manual maintenance or in-house hardware purchases. Plus, they were able to segment teams by projects and allowlist their IP addresses accordingly. The setup mitigated the data breach risk and introduced more granular data access controls.
As the tool seamlessly integrated with their existing company cloud systems, the transition was smooth and freed them from tedious manual management. This resulted in a more efficient and secure connectivity model with additional NordLayer features.
Actionable tips and best practices
Businesses must handle the data that they hold responsibly, not only to fulfill their promise to their clients, but also to meet requirements from the government bodies. By following best industry tips and practices, organizations can help prevent cybersecurity incidents and mitigate the risk of lawsuits and financial penalties.

-
Using strong and unique passwords. Online account protection largely rests on the strength of your users’ passwords. Reusing passwords makes it easier for hackers to gain entry into multiple accounts with the same set of credentials. Therefore, requiring a strong and unique password is a simple yet effective way to secure against the simplest threats.
-
Regularly updating software. Periodically updating software is crucial to maintaining a secure system and protecting against cyber threats. As vulnerabilities are discovered daily, using outdated software makes it easier for hackers to exploit known flaws. The only way to avoid those exploits is to patch vulnerabilities to reduce your system’s susceptibility to attacks.
-
Using a VPN. When a user connects to a VPN, its internet traffic is encrypted, protecting all exchanged information under a seal. VPNs also mask your real IP address, making it more difficult for websites and services to track your online activity or location. This alone can make remote working risks less severe.
-
Limiting user access to sensitive information. Enforcing a need-to-know basis for accessing all data. By restricting access to only those who require it, you can reduce the risk of unauthorized access or exposure to confidential information. This can minimize the likelihood of insider threats and ensure accountability for information access.
-
Training employees to recognize cyber threats. Cybercriminals often target employees through phishing emails to gain access to sensitive information. This makes employees a key component of the organization’s defense system. For this reason, they should be equipped to recognize and stop hacking attempts, alongside our technical systems.
How can NordLayer help?
Internet access security is a priority for most companies, no matter what industry they work in. Nowadays, it poses unique security challenges businesses need to address due to various work models like remote, office, and hybrid.
NordLayer can assist enterprises in protecting their connections over the public internet. This is achieved by encrypting the connection between the user’s device and the middleman server using advanced ciphers. It ensures that all data exchanged is kept secure and cannot be read by outsiders.
With cutting-edge security technologies, NordLayer can block access to malicious websites and control entry to specific content categories. Using Public Shared Gateways, NordLayer expands browsing capabilities, allowing global business exploration and guaranteeing the confidentiality of users’ and resources’ true location.
Businesses can enhance their internet access security by implementing best industry practices and regularly training employees on security threats. This is a sure way to protect sensitive information from data breaches, no matter what work model your organization is.
Contact our sales team and discover how to achieve greater internet access security.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.







 Exploit mitigation improvements in Windows 8
Exploit mitigation improvements in Windows 8