Granting administrator access to a user who does not even have time to explain why they need this permission is not an efficient way to solve a company’s problems but rather to harm its security.
This is because sensitive data can fall into the wrong hands through a cyber invasion, in addition to the organization’s own collaborator posing a threat due to the possibility of human, accidental, or purposeful errors.
In this context, it is recommended to apply the Principle of Least Privilege, which grants these users only the necessary permissions to perform their tasks.
In this article, we explain in detail this concept and its importance, among other information on the subject. To facilitate your reading, we divided our text into topics, which are:
- What is the Principle of Least Privilege?
- Why is the Principle of Least Privilege Important?
- 10 Benefits of the Least Access Principle
- How to Implement the Principle of Least Privilege
- Principle of Least Privilege: Example
- Challenges of the Principle of Least Privilege
- Need-to-Know Principle and Principle of Least Privilege: What Is the Relationship?
- Zero Trust and the Principle of Least Privilege: What Is the Relationship?
- How to Keep Your Data Protected Using Passwords
- About senhasegura
- Conclusion
Enjoy the read!
What is the Principle of Least Privilege?
Also known as Least Access Principle, the Principle of Least Privilege (POLP) refers to a concept of cybersecurity according to which users should receive only the necessary permissions to read, write, and execute files indispensable to their operations.
In practice, the Principle of Least Privilege integrates the security policy of companies and restricts access to applications, systems, and processes only to privileged users.
Depending on the system, it is possible to base these privileges on the roles of professionals within organizations.
Why is the Principle of Least Privilege Important?
First, the Principle of Least Privilege is critical to reducing the attack surface, preventing the action of malicious users. This is extremely important, since privileged credentials are among the main targets of attackers.
That is, by limiting superuser and administrator access through the Least Access Principle, one can protect a company from intrusions. Moreover, it helps prevent the spread of malicious software, such as malware.
However, it is essential to be aware of the need to apply the Principle of Least Privilege to endpoints. This helps prevent hackers from using elevated privileges to increase their access and move laterally across the IT framework.
The need to keep companies in compliance with strict auditing standards also explains why the Principle of Least Privilege is important.
10 Benefits of the Least Access Principle
The main benefits of the Least Privilege are:
- Elevation of privileges when necessary
- Restriction of access to applications
- Restriction of access to system settings
- Control of the data used
- Smallest attack surface
- Reduction of human failures
- Malware containment
- Enhanced data security
- Protection against common attacks
- Compliance with audit criteria
Here are more details on these benefits:
Elevation of Privileges When Necessary
It is necessary to apply the Least Access Principle (POLP) whenever one needs to elevate the privileges of an employee to a particular application for a specific time to operate.
Restriction of Access to Applications
Another purpose of the Principle of Least Privilege is to prevent an administrator from changing the settings of equipment by installing applications and exposing the organization’s network to cyber threats.
Restriction of Access to System Settings
The Principle of Least Privilege also has the function of reducing administrative privileges by restricting access to system settings.
Thus, a user may have administrative privileges without being able, for example, to change firewall settings, since the control of the environment is intended for the administrator.
Control of the Data Used
Through the Principle of Least Privilege, one can record and store detailed information about each access granted and obtain greater control of the company’s data.
Smallest Attack Surface
If a malicious agent breaks into a user account with limited permissions, their attack will compromise only the resources accessed by that user. In contrast, if the hacked account is an administrator, the hack will impact the entire network.
This means that, in order to reduce the attack surface used by hackers to harm a business, it is recommended to keep the minimum number of administrator accounts.
Reduction of Human Failures
In addition to hacking, applying the Principle of Least Privilege in your organization helps prevent problems caused by human errors. After all, users with access to resources that go beyond what is necessary to perform their tasks can, unintentionally or even purposely, delete or reconfigure something.
Malware Containment
The Principle of Least Privilege helps prevent your network from getting infected by malware. This is because an administrator with many accesses can spread malware to multiple systems, while it is possible to count its dissemination on networks where Least Privilege applies.
However, it is not enough to restrict users’ access, as the same must be done in relation to applications in order to prevent this type of attack on your network.
Enhanced Data Security
You may remember when Edward Snowden leaked millions of classified NSA (National Security Agency) files to the media due to his privileged access. The incident has caused many problems, which could be avoided if his permissions were limited to the scope of his work.
Applying the Least Access Principle is an efficient way to limit the number of users with access to sensitive data, reducing the possibility of internal leaks and strengthening digital security.
Moreover, in the event of a violation, the restrictions imposed by the Principle of Least Privilege allow for easier tracking of the cause.
Protection Against Common Attacks
Applications with high privileges are often targeted by hackers, who insert malicious instructions into SQL statements to control critical systems. However, this type of attack can be avoided through the Principle of Least Privilege (POLP), which impacts the possibility of elevating permissions.
Compliance with Audit Criteria
Applying the Least Access Principle allows organizations to operate in accordance with the most stringent audit requirements, making it possible to avoid threats and reduce the downtime and losses generated by a potential attack.
How to Implement the Principle of Least Privilege
Some practices are recommended when the goal is to apply the Principle of Least Privilege. Some of them are:
- Conduct an audit of the accounts;
- Establish the Least Privilege into new accounts;
- Elevate privileges for a limited time;
- Ensure that elevations of privileges are appropriate;
- Track all user actions on the network; and
- Conduct periodic audits.
Check out these items in more detail below:
Conduct an Audit of the Accounts;
The first step in implementing the Least Access Principle is to audit all existing privileges in accounts, programs, and processes, ensuring that users are only granted the necessary permissions to perform their activities.
Establish the Least Privilege Into New Accounts
Next, it is important to keep in mind that new accounts must be created in compliance with the Principle of Least Privilege, regardless of whether they are used by company managers or IT staff.
After all, if any of these users require a higher level of access afterward, it may be granted temporarily.
Elevate Privileges for a Limited Time
The privileges granted must be temporary whenever a user needs to raise the level of access for a specific project. In such cases, to ensure even greater security, it is possible to use single-use credentials.
Ensure that Elevations of Privileges Are Appropriate
Before applying the Principle of Least Privilege to accounts that already exist, you should assess which roles require elevated access and whether users actually rely on this elevation of privileges to perform their operations.
This assessment should be carried out periodically, including new tasks that may require privileged access.
Track All User Actions On the Network
To apply the Principle of Least Privilege, it is also important to monitor and track all user actions on your network.
This monitoring will allow you to detect over-privileged users, track suspicious activity, and identify evidence of an intrusion before it causes incalculable damage.
Conduct Periodic Audits
To ensure that permissions are always at the appropriate level, periodic audits are required.
Keep in mind that performing this type of maintenance is much easier than starting to implement the Principle of Least Privilege policy from the beginning, saving you time and ensuring more security for your company.
Principle of Least Privilege: Example
Here are some cases where the use of POLP is indispensable:
We advise the conscious and responsible use of social media through the application of the Principle of Least Privilege. In other words: to offer only the information necessary to make use of these media and not to share sensitive data with other user profiles.
In addition, it is important to configure privacy and security options in order to restrict users’ access to your publications.
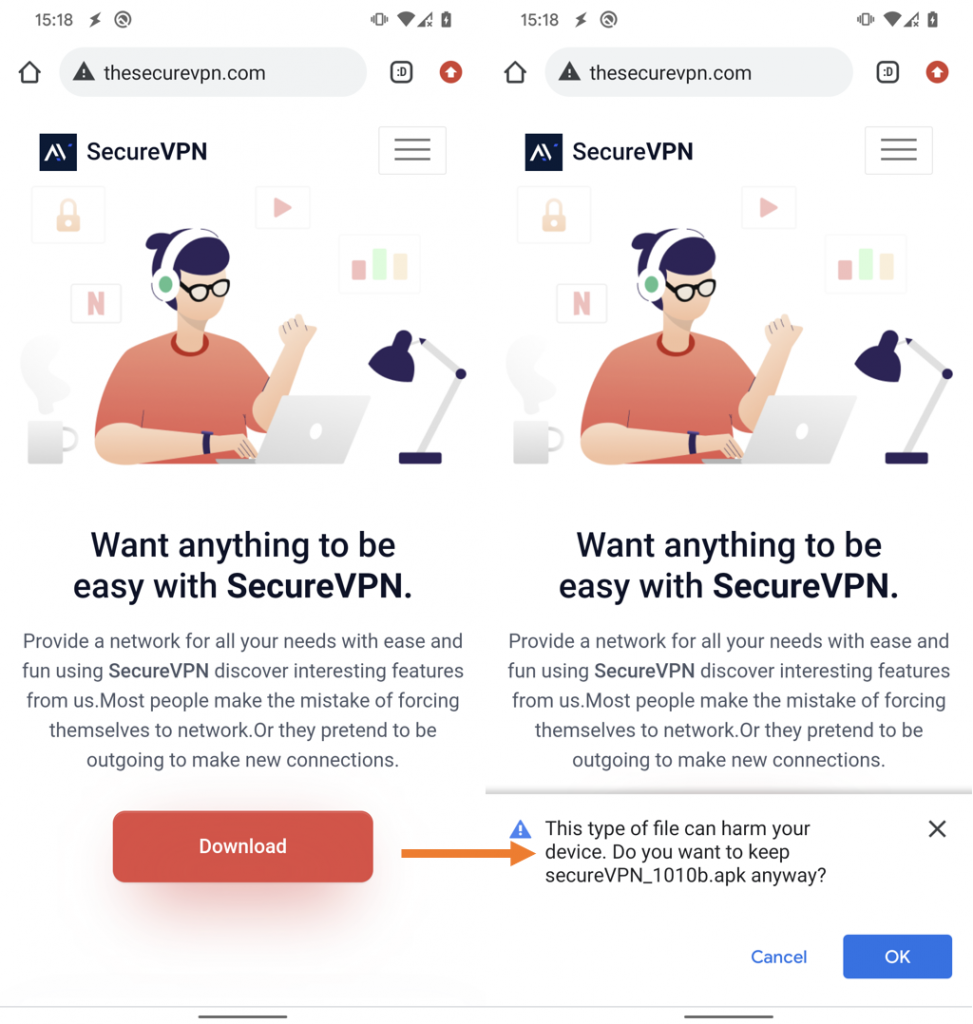
Many applications request unnecessary permissions to perform their functions, such as telephone, location, and contacts, and can even be used to steal the banking details of the victims.
Therefore, it is also essential to apply the Principle of Least Privilege in this case in order to avoid damage caused by malicious apps.
A receptionist of a health insurance plan should not have access to the clinical and confidential data of patients. This is because, without the Principle of Least Privilege, if a malicious user invades your computer, they will have access to these files.
A manufacturing company should also grant its employees only the level of access needed to perform their tasks, rather than giving access to your entire ICS. This is because remote access to industrial resources and interconnectivity generate security vulnerabilities for the organization.
The retail sector usually has a high turnover of employees, which can be a problem if there is no control over the levels of access granted. For this reason, companies in the segment must apply the Principle of Least Privilege to ensure that only the right people have access to their data and resources.
Professionals working in financial services deal with millions of customer files daily. To reduce risks, it is appropriate to apply the least access principle (POLP) in that context.
Many corporations outsource services such as CRM systems, HR, and databases. When they need technical support, it is advisable to apply the Principle of Least Privilege, ensuring that outsourced professionals have access only to the system they need to repair, which reduces risks to the company.
Challenges of the Principle of Least Privilege
The main feature of the Least Access Principle is the possibility of granting users only the necessary permissions to perform their tasks, and the major challenges related are the minimum access and the access expiration. Check it out:
Often, the administrator is not sure if the user really needs a high level of access before providing it and grants this permission anyway to reduce inconvenience to the user and not needing to contact technical support.
Nevertheless, it is advisable not to provide privileged access without being 100% sure it is necessary. If the access provided is not required, this is unlikely to be reported to technical support, increasing the attack surface. In contrast, if the user does not receive the access they need, they may request this permission.
Another challenge related to privileged access is that often a user’s roles are changed over time, without removing previous privileges. As a result, many employees accumulate unnecessary privileges to perform their activities.
To avoid this problem, it is recommended to set a deadline for the access expiration, which ensures that it expires if it is not renewed.
Need-to-Know Principle and Principle of Least Privilege: What Is the Relationship?
Used by governments and large organizations to protect state and industrial secrets, the Need-to-Know Principle is a concept that advocates restricting information access only to people who need it to perform their tasks, regardless of the corporation’s level of security or the authorization of superiors.
When we talk about digital security, its application involves the use of mandatory access control (MAC) and discretionary access control (DAC) solutions.
The Principle of Least Privilege, in turn, refers to the need to direct just the accesses each user of a network or system needs to perform their functions.
Zero Trust and the Principle of Least Privilege: What Is the Relationship?
Under the Zero Trust-based security concept, organizations should not rely on anything that is within or outside their boundaries. Therefore, any access requests must be checked and evaluated before being granted.
To limit which systems a user can access, this security model uses features such as auditing, credential protection, and multifactor authentication (MFA).
Moreover, it is recommended to apply the Principle of Least Privilege as a strategy to limit the level of access of users only to the necessary permissions.
How to Keep Your Data Protected Using Passwords
The cyber universe requires many security measures to mitigate risks, and POLP is one of the most effective. However, there are other ways to protect an organization’s resources and data, and one of them is to choose secure passwords.
Here’s what you should take into account to set a password:
- Use long and complex passwords. This prevents hackers from using techniques to guess them. However, just using complex passwords may not be enough to avoid the action of malicious attackers.
- Many devices are configured with default passwords. Change them immediately.
- Avoid reusing your passwords on different accounts. In addition, constantly check if you have ever been a victim of data leaks through senhasegura Hunter. In that case, change your passwords immediately.
- Set up your passwords to be changed frequently. The ideal is at least every three months.
- Do not write down, store in an easily accessible place, or share your passwords with others, thus avoiding unauthorized access.
- Consider password management solutions, or even privileged access management (PAM), to manage the use of systems and devices.
- Use multifactor authentication (MFA) mechanisms to add a layer of security to your accounts.
- Set up means of retrieving access, such as including phone numbers or emails.
- Passwords are one of the oldest security mechanisms in the computing world and are also one of the main attack vectors by hackers. And in the “new normal” era, with increasing threats resulting from the covid-19 pandemic, it is vital that users be alert and properly protect their digital identities. In this way, we can avoid cyberattacks that can cause considerable damage not only to people, but also to businesses. Remember: security starts with you!
About senhasegura
We, from senhasegura, are part of the MT4 Tecnologia group, created in 2001, to promote cybersecurity.
We are present in 54 countries, providing our clients with control over privileged actions and data. In this way, we avoid the action of malicious users and data leaks.
We understand that digital sovereignty is a right of all and this goal can only be achieved with applied technology.
Therefore, we follow the life cycle of privileged access management, before, during, and after access, by using machine automation. Among our commitments, the following stand out:
- To ensure more efficiency and productivity for businesses, as we avoid interruptions due to expiration;
- To perform automatic audits on the use of privileges;
- To automatically audit privileged changes to detect abuses;
- To ensure customer satisfaction;
- To perform successful deployments;
- To provide advanced PAM capabilities;
- To reduce risks;
- To also bring companies into compliance with audit criteria and standards such as PCI DSS, Sarbanes-Oxley, ISO 27001, and HIPAA.
Conclusion
By reading this article, you saw that:
- The Principle of Least Privilege is a security policy, where each user of a system must receive only the necessary permissions to complete their activities;
- This allows to reduce the attack surface and avoid the action of malicious attackers;
- It also brings other benefits, such as avoiding the proliferation of malware and human failures, that may generate risks;
- To implement the Least Access Principle in an organization, it is necessary to audit existing accounts, ensure that elevation of privileges is granted for a limited period, and track all actions of users on the network, among other good practices;
- As examples of situations in which the Principle of Least Privilege should be applied, we highlight social networks and health systems, among others;
- The main challenges related to the adoption of the Principle of Least Privilege refer to minimum access and access expiration;
- The Principle of Least Privilege can be associated with the Need-to-Know Principle and the Zero Trust-based security model.
- In addition to using the Principle of Least Privilege, keeping an organization’s data secure involves other measures, such as the adoption of strong and unique passwords.
Did you like our article on the Principle of Least Privilege? Then share it with someone who may be interested in the topic.
ALSO READ IN SENHASEGURA’S BLOG
Why Identity and Access Management is Important for LGPD Compliance
Windows Print Spooler Failure: Why Should I Upgrade Immediately?
What is An Incident Response Plan (irp) and Why is It Important to Have One?