What is and how to install WSL2 and why is it great news for IT?
Background
Before diving into what WSL2 is, how to install it, and how to use it – which we will – I would like to add some background information you might relate to if you were born in the 80s like me.
From a very young age I have felt attracted to computers, and in my childhood they were not as common as they are today, when almost everyone has one within reach.
I think my first encounter with a computer was when I was 11 or 12 years old, with an old computer that my father had in his office. I remember spending hours in front of the screen, although I’m not quite sure what I was doing, because at that time there was no internet.
That old computer had Windows 3.1; my first computer also meant my first Operating System was Windows, which I used in all its versions (and I will also spoil that I still use it). From then on I kept on using it, in fact, I didn’t know about anything else until I got to college and some friends told me about Linux (Mac was not an alternative for me).
Since I met Linux I fell in love with the penguin operating system, its philosophy and its fantastic terminal, so I started testing it on my home computer, with all the compatibility issues it involved at the time, when you spent half a day installing and two more looking for drivers. However it was a new experience and, although frustrating, totally rewarding when you achieved this sense of accomplishment. Of course, for me it was no more than an experiment for many years.
Half of my professional life revolved around Windows, from my first jobs as a microcomputer technician to managing servers and services based on Microsoft OS. I even studied at a Microsoft partner academy and got certified in Microsoft Windows Server 2012. It wasn’t until early 2013 that I had my first professional experience with Linux on an old web server that someone had to maintain. Indeed, that someone was me and I devoted many more hours than necessary to that lonely server.
Like many of you, I find myself in the following position: I love Linux and its ecosystem but it seems to me that Microsoft does a very good job on its OS and, for some reason, I always end up coming back to it. The ideal thing would be to have the best of both worlds. I’ve tried dual boot, virtualization, and cwin, but none felt like a full experience. I thought it was the best I could get even if it wasn’t ideal and just moved on, until Microsoft announced WSL.
What is WSL?
WSL stands for Windows Subsystem for Linux, which was nothing more than a compatibility layer for native Linux environments within Windows. Its first version was announced in 2016 and it was big news. I remember having the Ubuntu 16.04 terminal running natively on Windows and thinking “this is what I’ve been waiting for, everything I need without losing compatibility”.
Unfortunately WSL, although very useful, had several shortcomings: all the executions were interpreted, there was no access to all the hardware of the machine, the overall performance was quite poor, etc. I didn’t stop using it, but it wasn’t suitable for everyone. Still, it was the first step. In 2019 they announced WSL2, which would no longer be interpreted, it would have the entire native Linux kernel and would be running on Windows at full performance. WSL2 was recently released for all Windows 10 2004 version users. It seems that having everything I needed is now becoming a reality. It’s not perfect, that’s for sure, but it’s impressive how well it works.
Why WSL2 and not a Linux distro?
“It depends”, that’s the answer. Many of you, due to company policies, will not be able to change the OS of your computer or will be stuck with Windows for using the Office suite or Adobe tools, or even because you feel more comfortable on Windows rather than Linux.
In my case, I have the freedom to choose the operating system I use, my company does not enforce any restrictions as long as it stays updated and has an antivirus active. I have tried using Linux straight away and in the end I always have to go back to Windows or virtualize it and I prefer to virtualize Linux on Windows rather than the other way around.
In my day to day I have many different tasks, although I have a WSL2 terminal always open on one of my virtual desktops, I spend half of the day in meetings with different providers (webex on Linux is a nightmare). I use different VPNs and virtual client desktops, I edit videos for Pandora FMS YouTube channel, etc. And I do many of these things with tools that do not work quite well in Linux, so WSL2 has given me the almost perfect solution for my daily tasks.
(If you think you would be interested in reading an article about my workflow and all the tools I use, leave a message in the comment box).
Deploy WSL2
If you are here, it is because you relate to one of the cases here exposed. Installing WSL2 is very simple, but let’s go step by step.
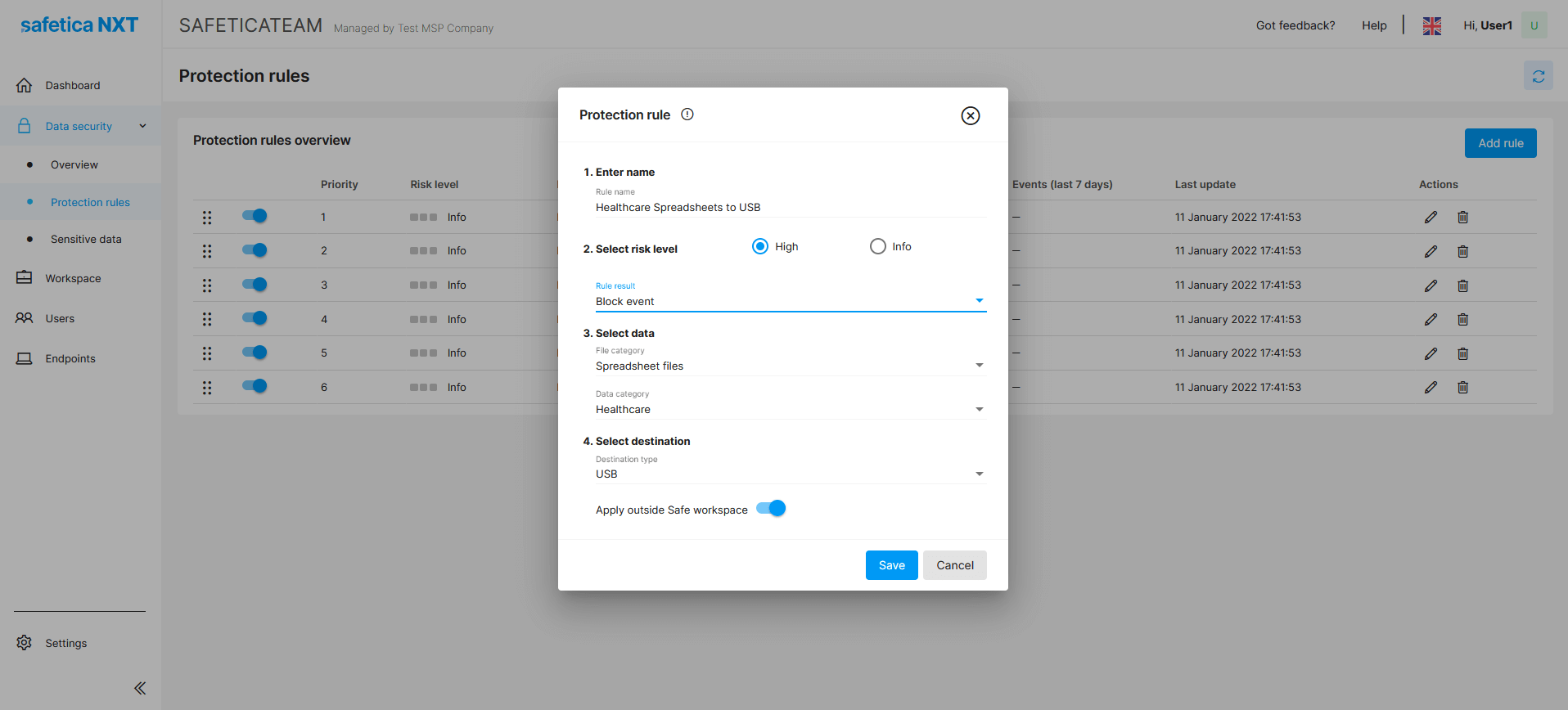
Remember that you must have Windows 10 version 2004 or higher to be able to use WSL2.
Checking it is as simple as pressing the start key, typing winver and pressing enter.
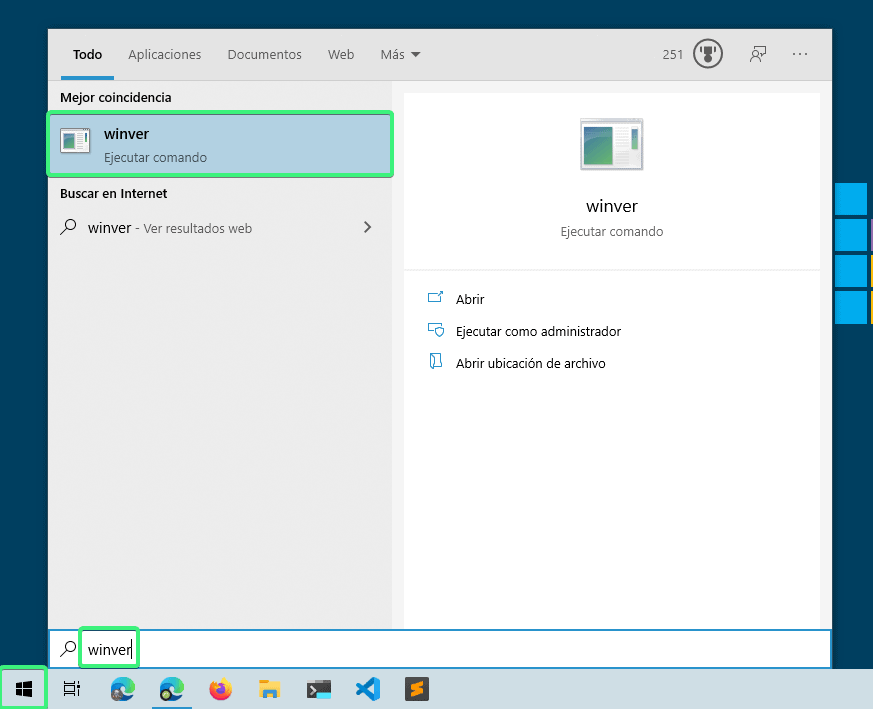
It will show you a screen like this, where you will see Windows 10 version.
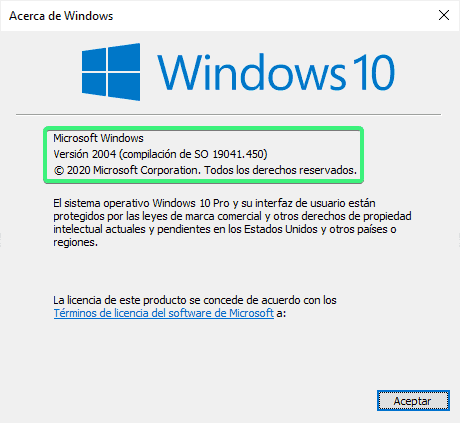
If you comply with the correct Windows version, let’s get to work. If not, it is time to go update Windows.
Step 1: Enable WSL on your system.
The easiest way is to open a PowerShell terminal as administrator and run:
dism.exe /online /enable-feature /featurename:Microsoft-Windows-Subsystem-Linux /all /norestart
Don’t close the terminal or restart yet.
Step 2: Enable virtualization.
Execute the following command in the PowerShell terminal open as Admin.
dism.exe /online /enable-feature /featurename:VirtualMachinePlatform /all /norestart
Now restart the machine.
Step 3: Activate WSL version 2 as default.
Open a PowerShell terminal again as administrator and execute:
wsl --set-default-version 2
You will see a message similar to: “WSL 2 requires an update to its kernel component. For information, please visit https://aka.ms/wsl2kernel”. Go to the URL and download the package following the wizard steps.

Step 4: Download the distro, preferably from Windows store. Type in wsl in the search engine so that the options come out (personally I use Arch, but it is not in the store so it is a bit more complicated to install). I recommend installing Ubuntu, the first to be released and in my opinion the one with the most covering support.

Once downloaded, open it and the distro installation will start. It will ask for the username and password. For the Linux system you can set the one you prefer, it has nothing to do with the Windows user.

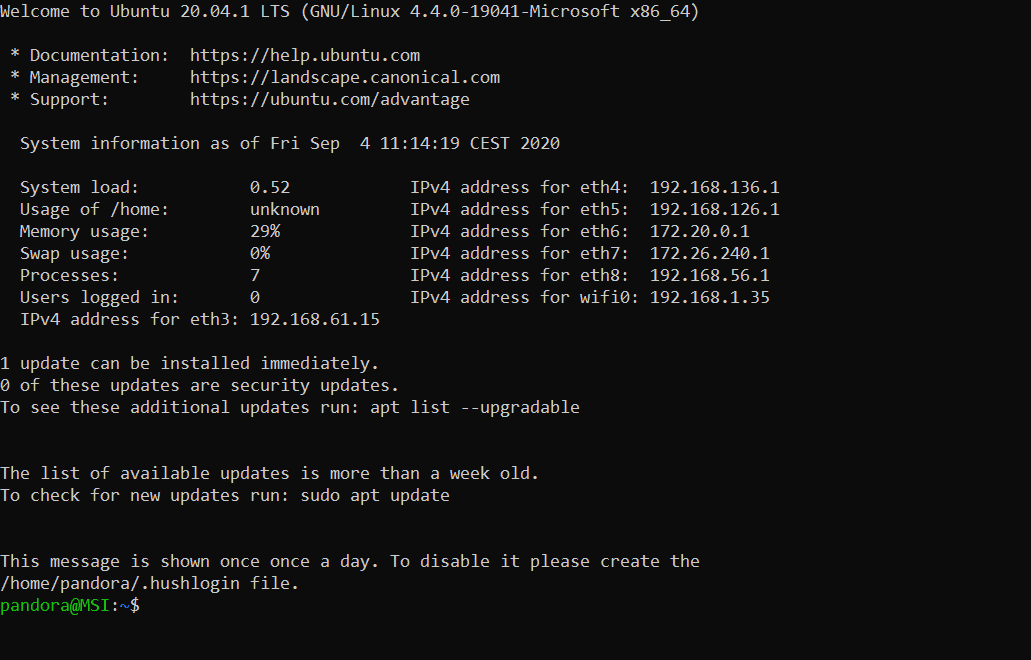
Once the installation is finished, you will see a screen similar to the following and the prompt ready to use Ubuntu bash.
Step 5: Check the installation from a PowerShell terminal, executing:
wsl --list --verbose
Where it will list the distros installed and their versions. I already said that it used arch and yes I also have Windows running in WSL2 for Docker. In your case, it will show just the one that you have installed, in this case Ubuntu, and it would have to be version 2.

Conclusions
With these simple steps you will have Ubuntu installed within Windows with its kernel at 100% and you can run all the tools you need, such as Docker natively directly in the Linux kernel (something that before with HyperV was not working for me and that WSL1 did not support).
Implementation is not perfect, it has many advantages but it also has some problems to figure out. Even so, I think it is the best current implementation to have a hybrid system where to enjoy the best of both worlds, so I recommend it 100%.
If you are interested in the subject, we can write an article listing the advantages, disadvantages and alternative solutions to certain problems that this technology currently poses. Let me know if you are interested in the comments.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About PandoraFMS
Pandora FMS is a flexible monitoring system, capable of monitoring devices, infrastructures, applications, services and business processes.
Of course, one of the things that Pandora FMS can control is the hard disks of your computers.