When you think of a password manager, you probably think about its ability to generate unique and secure passwords for every account. While that’s true, password managers also protect against a range of technical threats you might not expect—threats that can devastate businesses, from phishing attacks using Punycode domains that trick employees into revealing corporate credentials to keyloggers and brute-force attacks on admin panels that expose sensitive systems.
In 2025, with 74% of all data breaches involving some kind of human element or error and costing companies millions in downtime and fines, password managers like NordPass are far more powerful than just a password generator—they’re a business’s shield against financial and reputational ruin. In this article, we’ll break down 5 cyber threats and explain exactly how password managers defend against them.
1. Phishing
Phishing is a cyberattack in which attackers trick users into revealing sensitive information, like usernames and passwords, by creating fraudulent websites that mimic legitimate ones. This type of attack is a huge problem, especially for businesses losing data to fake login pages. In 2025 so far, phishing has accounted for over 36% of all data breaches, and about 3.4 billion phishing emails are sent every day. These numbers show how widespread and persistent phishing has become.
These attacks often rely on techniques like Punycode domains, hijacked subdomains, and typosquatting to deceive users. Phishing links are commonly distributed via email, SMS, or malicious ads, directing victims to fake login pages where their credentials are captured.
For example, an attacker might create a domain like http://www.goоgle.com (using the Cyrillic “о” instead of the Latin “o”), which looks nearly identical to http://www.google.com but directs users to a malicious site. Alternatively, attackers might exploit a misconfigured DNS setting to hijack a subdomain, like secure.login.example.com, making the phishing site appear as if it belongs to the legitimate example.com. In typosquatting, domains like http://www.faceboook.com or http://www.pay-pal.com are registered to exploit common user typing errors.
:format(avif))
Image: An example of an open-source phishing kit
Password managers protect against phishing by using exact domain matching when autofilling credentials. When a user visits a phishing site, even if the domain visually resembles the legitimate one, the password manager recognizes the mismatch and refuses to autofill credentials.
For instance, if credentials are saved for http://www.paypal.com, they will not be provided on a phishing domain like http://www.paypa1.com. This prevents users from unknowingly submitting their passwords to fraudulent sites.
Another layer of protection comes from eliminating the need for manual password entry. Password managers use secure browser APIs or system-level frameworks like Android’s Autofill API or iOS’s AutoFill to inject credentials directly into login fields. This bypasses keyboard input entirely, preventing phishing websites from capturing credentials through keylogging or fake form fields.
2. Credential stuffing
Credential stuffing is a type of cyberattack in which attackers use large sets of stolen username and password combinations, often obtained from previous data breaches, to gain unauthorized access to user accounts on different platforms.
For businesses, this is a huge threat—employees reusing personal passwords for work accounts can open the door to attackers who might use a breach of a random website to access corporate emails, CRM systems, or financial tools, costing companies millions in stolen data or ransomware payouts. The attack relies on the assumption that many people will reuse the same credentials across multiple websites and services.
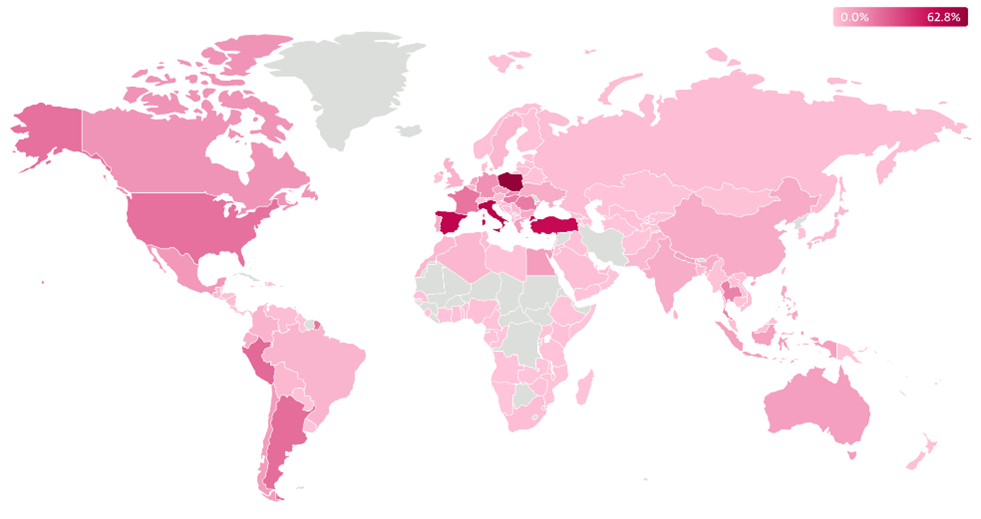
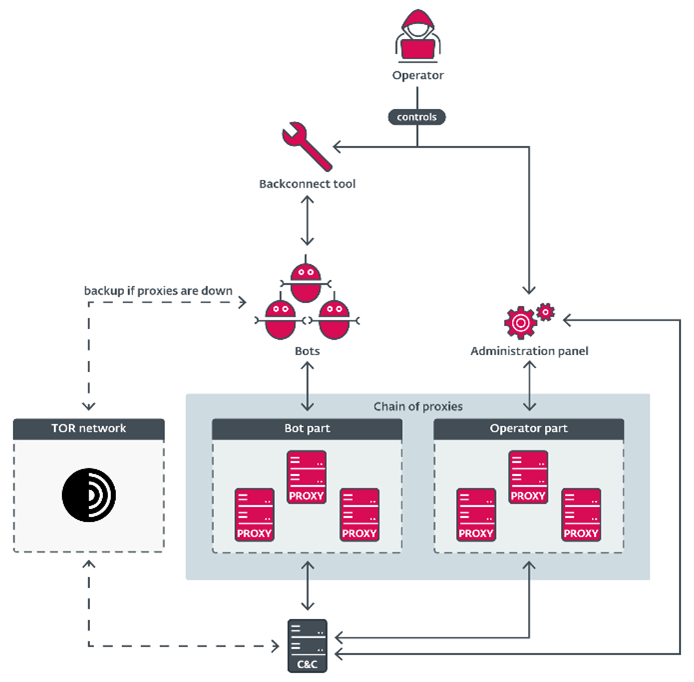
Automated tools are used to test these credential pairs across numerous sites at scale, often with the help of bots, enabling attackers to exploit any reused credentials efficiently.
:format(avif))
Image: Cybercrime forum discussions focusing on credential-stuffing tools
For example, if an attacker acquires a leaked database from a breached e-commerce platform, they might use the stolen email-password pairs to attempt logins to banking, social media, or other sensitive services. Automated credential stuffing tools, like Sentry MBA or OpenBullet (as seen above), can test thousands of combinations per minute, often evading basic security measures like rate limiting or CAPTCHA using proxies.
Password managers provide a strong defense against credential stuffing by generating and storing unique, complex passwords for every account. Since credential stuffing depends on the reuse of credentials across multiple platforms, having a distinct password for each account renders the attack ineffective. Password managers make this feasible by securely storing and autofilling these unique passwords, so users don’t need to remember them.
NordPass offers a valuable feature called Password Health. This feature scans all passwords stored in your vault and checks how vulnerable they are, giving you a clear view of your password security. It alerts you about weak, reused, or compromised passwords, helping you take necessary actions to strengthen your online security. This is an effective way to ensure your passwords aren’t putting your accounts at risk.
3. Brute-force attacks
Brute-force attacks involve systematically guessing passwords by trying all possible combinations, often with the help of automated tools. While most modern consumer platforms include protection mechanisms like two-factor authentication (2FA), CAPTCHA, or account lockouts to prevent these attacks, there are edge cases where brute-force attacks remain viable. This is particularly true for public-facing admin portals or legacy systems that lack built-in protections by default.
For instance, if your business runs a WordPress site without security plugins, it may be leaving its admin panel (/wp-admin) exposed to brute-force attacks. Attackers might use tools like Hydra or WPScan to test thousands of password combinations, starting with weak or default credentials like admin with password123. Without additional configurations, some versions of these platforms remain vulnerable, as they typically don’t include features like rate limiting or CAPTCHA out of the box. Users must proactively install plugins to secure these areas.
:format(avif))
Image: An example of WPScan brute-force functionality
Password managers provide an important layer of protection against brute-force attacks by encouraging the use of strong, complex passwords that are resistant to guessing. A password manager can generate a password like Tx8&@K1p!Rv2#, which is more difficult to crack, even with the most advanced brute-force tools. Furthermore, password managers ensure that users don’t rely on weak or default credentials and prevent the reuse of passwords across different systems, which attackers could exploit.
NordPass, in particular, not only generates strong, complex passwords but also stores them securely. Users have the flexibility to determine the complexity of their passwords, allowing them to create passwords that are both highly secure and tailored to their needs. Importantly, NordPass encourages the use of unique passwords for each account, ensuring that even if one set of credentials is exposed, it cannot be used to access other systems.
In addition to generating and securely storing strong passwords, NordPass also includes its built-in Authenticator feature, which can be used as an authenticator app. This adds an extra layer of security by enabling 2FA for your accounts, making it a lot harder for attackers to gain access, even if they manage to crack a password. The NordPass Authenticator is a convenient and secure option to further bolster your defenses against brute-force and other types of attacks.
With a password manager, the only password users need to remember is their master password—the key to unlocking their vault of securely stored credentials. Once this master password is entered, the manager handles the rest, automatically filling in passwords for all other accounts. This removes the burden of remembering each password individually, while still keeping your accounts protected with strong, unique passwords.
Although brute-force attacks are not a genuine risk for most consumers due to modern protections, they still pose a threat in specific scenarios, like unsecured admin portals or systems without rate limiting. By using a password manager to create and store strong, unique passwords, users add an extra layer of defense against this type of attack. In these edge cases, password managers provide protection, ensuring that even if other security layers are missing, accounts are protected with passwords that are resilient to brute-force attempts.
4. Keyloggers
Keyloggers are malicious tools designed to record every keystroke a user types, allowing attackers to steal sensitive information like usernames, passwords, and other private data. Companies can leak important information if keyloggers hit employee devices. They are often deployed as malware through phishing emails, malicious websites, or software downloads, but they can also exist as physical hardware devices installed between a keyboard and a computer.
Software-based keyloggers function by intercepting keyboard inputs at different stages within the operating system. They often utilize API hooks to monitor and record keystrokes as they are being processed.
For example, a keylogger on a Windows system might use the SetWindowsHookEx function to intercept keystrokes in real time. This allows it to capture credentials and other private information as they are typed. Clipboard loggers, another variation, monitor copy-paste actions to steal sensitive data like passwords copied for use.
:format(avif))
Image: Guides being shared on a cybercrime forum on how to write keyloggers
Password managers effectively counter these risks by eliminating the need for manual password entry. Instead of requiring users to type their passwords, password managers use secure autofill mechanisms to directly input credentials into login fields. On web browsers, they inject credentials through direct interaction with the DOM, while on mobile devices, they use system-level frameworks like Android’s Autofill API or iOS’s AutoFill. These methods bypass the keyboard entirely, rendering keyloggers unable to capture any useful data during the login process.
Although a keylogger could potentially capture the master password during the initial login to the password manager, modern password managers mitigate part of this risk by minimizing the need for repeated master password entry. Many password managers support biometric authentication, like fingerprint or facial recognition, allowing users to unlock the manager without typing anything after the initial login. Biometric data is securely stored on the device and cannot be intercepted by keyloggers, making it a highly secure and convenient method of authentication.
5. Database leaks
Database leaks occur when attackers gain unauthorized access to databases storing sensitive user information, such as usernames, passwords, and personal details. Businesses face huge losses when customer data spills out. These leaks often happen due to issues like web-application vulnerabilities, misconfigured servers, or outdated software.
Once a database is leaked, attackers can use the stolen credentials in further attacks, like credential stuffing (as mentioned above) or direct account takeovers, particularly if the passwords are weak or reused across multiple accounts.
For example, in a typical breach, a compromised database may store passwords in plain text or use weak hashing algorithms like MD5 or SHA-1, which are vulnerable to tools like Hashcat.
Hashcat, a high-performance password-cracking tool, allows attackers or researchers to brute-force or perform dictionary attacks on leaked password hashes to recover plaintext passwords. Even strong passwords can become vulnerable if the hashing algorithm is outdated or poorly implemented (e.g., missing salting).
:format(avif))
Image: A researcher or cybercriminal trying to use Hashcat to crack passwords
Password managers protect users from the consequences of database leaks in several key ways. First, they encourage the use of unique, strong passwords for every account. This ensures that even if one set of credentials is exposed in a breach, it cannot be used to access other accounts. For example, a leaked password from an e-commerce site would not provide access to a user’s banking or email accounts if unique credentials were used.
In addition to promoting password uniqueness, password managers generate and store randomized passwords that are resistant to brute-force attacks. A password like T&$9jf@3#1Px2! is much harder to crack using tools like Hashcat compared to common or weak passwords. Password managers also make it easy to update compromised passwords quickly by identifying affected accounts and help in generating secure replacements.
Many password managers further enhance protection by integrating breach monitoring tools. For example, NordPass offers an integrated Data Breach Scanner that provides real-time alerts when your email or credit card details appear in a data breach or leak. This feature allows you to respond proactively by updating your credentials before attackers can exploit the compromised data.
NordPass follows a zero-knowledge architecture, meaning it never has access to user passwords. Additionally, NordPass provides businesses with a free tool to check for potential leaks through its dark web monitoring service. This service helps companies detect any exposed employee or customer data across the dark web, adding an essential layer of defense for businesses concerned about database breaches.
Get protection with NordPass
Credential theft can cause serious problems for businesses of all sizes. When someone’s login details are stolen, it can lead to unauthorized access to accounts, financial scams, identity theft, or even corporate spying. Hackers often sell stolen login details on dark web marketplaces, making them available to criminals around the world.
If a hacker gets into someone’s email, they can reset passwords for other accounts, giving them access to even more services. To protect against credential theft and its harmful effects, it’s important to use strong passwords and a password manager.
Start taking control of your security today. As a business owner, you have the power to strengthen your company’s defenses by mandating the use of a password manager. NordPass Business makes it easy to implement best practices across your team, protecting against the very threats we’ve discussed.
:format(avif))
NordPass also constantly passes security audits, ensuring it meets the highest levels of protection. This helps your business achieve information security standard compliance (like ISO and NIS2), which protects against high penalties for non-compliance and potential data leaks.
Get started with a complimentary 3-month trial by clicking here and using the code “danielk”—no credit card required. Don’t wait until it’s too late; secure your business now.
Disclaimer: Examples are provided for informational and educational purposes only. NordPass does not endorse, promote, or support their use and has no affiliation with them. Readers are strongly advised to comply with all applicable laws and regulations. All trademarks mentioned are the property of their respective owners.











:format(avif))
:format(avif))
:format(avif))
:format(avif))
:format(avif))
:format(avif))
:format(avif))