Cybersecurity Risks in Remote Work

- Since the shift to remote work, ransomware attacks have increased by 20%
- 63% of businesses have experienced a data breach due to remote employees
- 80% of organizations have seen an increase in email phishing attacks since remote working began
These statistics serve as a clear warning about the critical significance of cybersecurity in the context of remote work. They underscore the imperative for organizations to prioritize and invest in robust cybersecurity measures to safeguard their corporate network, digital assets and sensitive information. It is essential for employers to ascertain that their corporate networks are fortified with the latest security protocols and that employees are equipped with secure devices for remote network access. Neglecting these precautions exposes organizations to the heightened cybersecurity risks of remote working, such as data security, cyberattacks and data breaches. These statistics should serve as a resounding call to action for employers to take proactive steps in fortifying their network defenses, thereby safeguarding both their critical data and the well-being of their remote workforce.
Remote work environment can be particularly vulnerable to various threats. Let’s examine these risks and explore strategies to mitigate them.
Remote Working Risks & Mitigation
- Weak Passwords and Lack of Multi-Factor Authentication:
Weak passwords and the absence of multi-factor authentication (MFA) are a significant concern in remote work scenarios. Cybercriminals often target accounts with easily guessable passwords, making it crucial to use strong, unique passwords for all online business accounts. Implementing MFA adds an extra layer of security by requiring users to provide two or more forms of authentication, such as a password and a one-time code sent to their mobile device. This additional step can significantly up their security solutions to reduce the risk of unauthorized access to sensitive data.
- Unsecured Wi-Fi Networks:
Employers should be aware that remote workers frequently connect to various Wi-Fi networks, including public hotspots. These networks are often less secure than corporate virtual private networks, making them a prime target for hackers. To mitigate this risk, employers can implement a web filtering solution within their organization’s network infrastructure. Web filtering tools can help block access to malicious websites and filter out harmful content, reducing the chances of employees encountering threats while connected to unsecured networks. Additionally, employers can encourage their remote workforce to use VPNs and ensure that employees’ home Wi-Fi networks are secured with strong passwords. This proactive approach enhances overall cybersecurity for remote teams.
- Phishing Detection and Notification:
Phishing attacks have become increasingly sophisticated, and remote workers are not immune to them. Recognizing phishing attempts is crucial. Train employees to identify suspicious emails, links, and requests for personal sensitive information. Employ advanced email filtering and security tools to detect and block phishing attempts before they reach the inbox.
- Lack of Security Updates:
One common oversight in remote work environments is neglecting to update software and operating systems promptly. Outdated software can contain known vulnerabilities that cybercriminals can exploit. Enable automatic antivirus software updates and regularly check for patches and updates to ensure your devices are protected with the latest security measures.
- Data Backup and Recovery:
Data loss can be disastrous, especially in remote work scenarios where sensitive company data from personal computers may be scattered across various devices and locations. Implement a robust data backup and recovery strategy. Regularly back up critical data to secure, remote servers or cloud or centralized storage solutions, and test the restoration process to ensure that data can be recovered in case of an incident.
- Insufficient Employee Training:
Remote workers must be adequately trained in cybersecurity best practices. Invest in cybersecurity training programs to educate employees about the various security risks that they may encounter while working remotely. Training should cover topics such as identifying phishing attempts, password security, and secure file sharing.
Cybersecurity Checklist for Employees
- Are your home devices protected by comprehensive antivirus and internet security software?
- Have you taken steps to secure your devices, ensuring encryption is enabled, and you’ve activated features like “Find my device” and remote wipe?
- Are you using a Virtual Private Network (VPN) for secure connections?
- Have you secured your home Wi-Fi network with strong encryption and a unique password?
- Are your passwords strong, unique, and regularly updated?
- Do you stay vigilant against phishing scams, refraining from clicking on unfamiliar links or opening unsolicited email attachments?
- Is your operating system up-to-date and supported by regular updates?
- Do you keep all software on your devices, including applications and programs, updated to the latest versions?
- Have you enabled two-factor authentication where applicable?
Cybersecurity Checklist for Employers
- Do you have a documented work from home security policy?
- Do you have a BYOD (Bring Your Own Device) policy?
- Do you provide cybersecurity awareness training to employees?
- Are you ensuring that staff use a VPN, and is it up to date with security patches?
- Do you encourage centralized data storage and regular data backups?
- Do you equip company devices with approved antivirus and internet security software?
- Do you promote strong passwords and consider password manager usage?
- Do you encourage two-factor authentication?
- Do you use encryption software to protect company data?
In conclusion, we haven’t reached a final destination in remote work, and the future brings new challenges, security threats, and opportunities. Organizations have to make choices. They might consider going back to traditional offices with better security control, but that might not be practical in our remote-friendly world. So, it’s essential to keep updating and strengthening security controls and measures.
There’s also the idea of giving remote workers the tools to secure their personal devices and home networks as well as office environments. This might become necessary in the future to protect sensitive data.
Staying alert, informed, and ready can help both individuals and organizations navigate remote work challenges while keeping their digital environments safe.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About SafeDNS
SafeDNS breathes to make the internet safer for people all over the world with solutions ranging from AI & ML-powered web filtering, cybersecurity to threat intelligence. Moreover, we strive to create the next generation of safer and more affordable web filtering products. Endlessly working to improve our users’ online protection, SafeDNS has also launched an innovative system powered by continuous machine learning and user behavior analytics to detect botnets and malicious websites.


Cyberview #2: Casino hacks, modern car data privacy, and ChatGPT
Welcome back to another episode of Cyberview! Explore latest developments in the world of tech and cybersecurity with Gerald Kasulis, Frida Kreitzer, and Carlos Salas.
In this episode, the Cyberview squad covers the hot topics that have been making waves recently – from X’s changing privacy policy, alarming revelations about data collection in the auto industry, OpenAI’s Enterprise offering, and the all-too-familiar tale of big business (in this case two of Vegas’ biggest casinos) falling foul to social engineering attacks.
In recent months, two of Las Vegas’ biggest hotel-casinos, MGM Resorts and Caesars Entertainment, were battered by cyberattacks.
MGM Resorts faced broad system outages and service disruptions, affecting properties in Las Vegas and elsewhere. According to Vox, “a group known as Scattered Spider is believed to be responsible, and it reportedly used ransomware made by ALPHV, or BlackCat, a ransomware-as-a-service operation. The hackers are said to be especially good at “vishing,” or gaining access to systems through a convincing phone call.”
Caesars Entertainment stated that it experienced a similar social engineering attack, albeit on an outsourced IT support vendor. The resulting data breach caused many of its loyalty program members’ Social Security numbers and driver’s license numbers to be stolen, along with other personal data. Caesars paid roughly $15m of the $30m ransom, according to the Wall Street Journal. These attacks remind us again of the vulnerability of human error, the persistent “weak link of cybersecurity”.
Car Companies & Data: A Privacy Nightmare
A recent report from Mozilla has shed light on some alarming data collection practices among car manufacturers. The study of 25 car companies found each to collect more personal data than necessary for operating vehicles and maintaining customer relationships. In Mozilla’s words, “Cars are the worst product category we have ever reviewed for privacy.”
This data covers not only driving habits and locations visited, but also sensitive details such as immigration status, weight, genetic information, and even facial expressions.
Cars are jam-packed full of sensors, microphones, cameras, connected devices, apps, and more – in short, a rich harvesting ground for data. This data is vulnerable to sale or share to third parties. Albert Fox Cahn’s remark, “Cars are wiretaps on wheels,” is ringing true.
X’s Latest Privacy Policy: Biometrics, Verification, and More
Elon Musk’s X recently rolled out some controversial changes. The app formerly known as Twitter stated that it “may collect and use your personal information” – employment, educational history, skills, job search activity, etc – “to recommend potential jobs for you, to share with potential employers when you apply for a job, to enable employers to find potential candidates, and to show you more relevant advertising.”
And there’s more. X has introduced a biometric verification system for paid users, based on government-issued IDs. Seemingly, this system will prevent impersonation and offers “prioritized support” to premium users. These users can opt to submit their government IDs and an image for verification, earning a badge (replacing the old “blue tick”) on their profile.
These changes are likely related to X’s recent moves into the job market space (look out, LinkedIn), and part of X’s broader plan to transform into an “everything app”. Also, training AIs.
OpenAI’s ChatGPT Enterprise: Protecting Business Data
Growing concerns about business data security (how much of our ChatGPT prompts are being used to train the next large language model?) have pushed OpenAI in a more B2B-friendly direction with the launch of ChatGPT Enterprise: “You own and control your business data in ChatGPT Enterprise. We do not train on your business data or conversations, and our models don’t learn from your usage.”
This move puts OpenAI in direct competition with its major backer, Microsoft, as both aim to attract business clients. What’s the connection? The Cyberview team delves into the details.
Stay tuned for the next episode of Cyberview.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.


ESET named Strategic Leader in AV-Comparatives 2023 Endpoint Prevention and Response (EPR) Test
Our strong performance in the AV-Comparatives EPR Test further confirms the ROI of ESET XDR-enabling products and services. Can the test also contextualize ESET’s performance in round five of the MITRE Engenuity ATT&CK® Evaluations: Enterprise?
Introduction
In the recently published Endpoint Prevention and Response (EPR) Comparative Report 2023 by AV-Comparatives, ESET PROTECT Enterprise version 10.1 scored highly in the EPR CyberRisk Quadrant™. Deemed a Strategic Leader along with only three other vendors, ESET sits at the top of the prevention and response capability ranking with the highest detection rate.
For some ESET partners, and even our sales leads, this result in the AV-Comparatives EPR Test stands in apparent contrast to the substep visibility coverage we provided in the 2023 round of the MITRE Engenuity ATT&CK® Evaluations: Enterprise. Some might argue that the statistical results for the detection and protection scenarios of the evaluation look quite different. Do testers, vendors, and end users all live in separate universes where math isn’t a universal language?
In our view, the APT-minded testers at MITRE Engenuity haven’t created a performance ranking (nor a competitive test) in their examination of protection and detection across the cyberattack chain, at least not one that can be easily compared to other tests. Readers transitioning their consideration from the ATT&CK Evaluations to the AV-Comparatives EPR Test will require a shift in attention. This shift must include a focus on the effectiveness of simulating real-world conditions and, importantly, consideration of the different audiences of the tests — in the case of the EPR Test, both end users and participating vendors.
Comparing audiences
The two tests discussed here have unique audiences in mind. AV-Comparatives has built its EPR Test to evaluate vendors’ product expectations and, critically, to give buyers transparent access to standard and agreed-on outcomes via a methodology that best mimics real-world performance. As part of the service to buyers, third-party testers typically provide their own analysis of the raw data, which is what AV-Comparatives offers in its EPR Report.
In contrast, MITRE Engenuity does not provide comparative analyses of vendor performance in the ATT&CK Evaluations. Indeed, MITRE Engenuity states:
These evaluations are not a competitive analysis. We show the detections we observed without providing a “winner.” Because there is no singular way for analyzing, ranking, or rating the solutions, we instead show how each vendor approaches threat defense within the context of ATT&CK.
This statement makes it abundantly clear that the ATT&CK Evaluations are not a ranking but a resource, first, for vendors, and second, for the security staff at organizations, who can engage thoroughly with the raw data provided.
We can put this another way: third-party tests are both a product and a service that provides its users – both vendors and end-user businesses – with input to make educated decisions concerning product R&D or business cost and real-world performance, respectively.
Participating in the ATT&CK Evaluations and the EPR Test
Another key point is who participates in these tests. The 2023 round of the MITRE Engenuity ATT&CK® Evaluations: Enterprise tested 29 vendors1 against two attack scenarios built from techniques used by the Turla threat group. Ultimately, this test assists vendors in working on validating their approach to optimized detection and protection – this includes the reasoning behind detecting or not detecting specific substeps in the evaluation.
Conversely, the 2023 AV-Comparatives EPR Test evaluated 12 vendors with a highly comprehensive approach that deployed 50 targeted attack scenarios using a diversity of techniques mapped to the ATT&CK knowledge base. These scenarios were not communicated ahead of the test, a fact that further contrasts the AV-Comparatives approach with that of MITRE Engenuity. The resultant EPR CyberRisk Quadrant factors in product efficacy in breach prevention, the calculated savings, and the product’s purchase, operational accuracy, and workflow delay costs.
Despite the high value of AV-Comparatives’ approach, historically, several participating vendors have opted not to reveal their names. Furthermore, a slew of other vendors who participated in the ATT&CK Evaluations have decided not to participate in the EPR Test. Potential end users of XDR products can rightly question the costs of these untested products and whether those costs potentially degrade the apparent detection capability shown in the ATT&CK Evaluations.
In developing our own capabilities and reviewing our performance in past Engenuity Evaluations, we opine that the usual “price” for a claim of 100% detection or protection in an evaluation is likely paid in false positives. However, our product, ESET PROTECT Enterprise, completed the AV-Comparatives test without producing any false positives – a bit of an ESET obsession, actually. The fact is, false positives drive real-world costs – costs that could even exceed those of a real compromise – due to IT staff potentially having to spend many hours to handle them.
Our participation in the AV-Comparatives EPR Test is important to help ESET communicate our value to IT security decision-makers. These decision-makers love quadrants such as the EPR CyberRisk Quadrant because they simplify understanding the capability of different products. We can imagine a CISO thinking: “Give me the product with the best detection and protection capability. Oh wait, the CFO reminded me to factor in cost!”
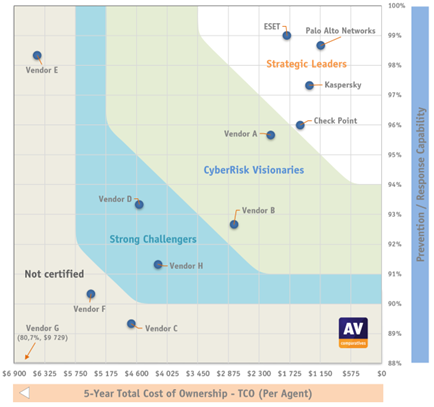
AV-Comparatives’ EPR CyberRisk Quadrant is a great resource for organizations to start evaluating and shortlisting XDR solutions on prevention and TCO metrics, before necessarily diving into the depths of technology and implementation.
1The MITRE Engenuity ATT&CK Evaluations: Enterprise began with 30 vendors. MITRE Engenuity communicates 29 having completed the evaluation.
Comparing methodologies
While AV-Comparatives uses a real-world methodology and provides analysis, MITRE Engenuity provides the emulation plan and results as raw data. If, as an organization, you have the resources and skilled IT staff, you could even rerun an ATT&CK Evaluation in your network, or substeps of it, to obtain highly relevant, real-world feedback on the actual effectiveness and cost of various solutions.
However, without such a personalized rerun, our assessment is that the ATT&CK Evaluations are unsuitable as the primary basis for a purchase decision. Instead, the goal of the evaluations is to provide trained eyes a resource to understand the specific levels of substep visibility that a product offers. Whether the provided level of visibility is suitable for an end user is hotly debated, but our main response is that you don’t need 100% visibility, nor do you need technique detections for every substep. What is necessary, however, is seeing enough relevant substeps – as not every substep is equally important to determine whether an attack is happening – then mitigate and/or stop it.
The DIY analysis required to really extract value from the ATT&CK Evaluations means all readers must be prepared to dive independently into the emulation plan and carefully consider each substep and what that means for your organization. Critically, the more you understand adversarial techniques, the challenges of reconstructing attack chains, and the commonality of events in your environment, the better your analysis and takeaways will be. Thus, the expertise required to interpret and assess the evaluations immediately puts decision-makers, who typically prefer digestible executive summaries, at arm’s length.
The measures taken by AV-Comparatives to offer a best approximate real-world environment, complete with commercially available and open-source attack tools, as well as tactics, techniques, and procedures (TTPs) assembled from MITRE’s ATT&CK knowledge base, underline testing for the service of businesses and institutions that rely on endpoint protection, detection, and response capabilities against real-world attacks.

(source)
The thoughtful approach taken by AV-Comparatives to quantify product performance beyond protection and detection across the attack chain pays big dividends in avoiding problems due to false positives.
A standout example taken from the results of the Turla ATT&CK Evaluation is the number of alerts allowed to be generated without penalty. One vendor had over one million alerts per attack chain. Another vendor’s dashboard showed almost 6.7 million suspicious events. In contrast, ESET Inspect displayed around 6,000 detections (including both endpoint and rule-based detections) on Day One of the evaluation and around 2,000 on Day Two. Keep in mind that the test environments had four or five machines, and MITRE Engenuity did not test products “with a battery of clean scenarios” as AV-Comparatives did!
Betting on both horses
As a vendor, we have clear motivations to maintain our participation in both the MITRE Engenuity ATT&CK Evaluations and the AV-Comparatives EPR Test, which were executed very professionally. Both the EPR Test, with its dual technical and business audience, and the ATT&CK Evaluations, with its (ideally) technical audience, promote advanced security practice.
Betting on multiple horses is nothing new. The high level of engagement by ESET malware researchers and security analysts with the ATT&CK knowledge base has helped drive product R&D around improvements to our EPP, EDR, and threat intelligence products for many years. ESET began contributing to MITRE ATT&CK very early on and now stands among the top 10 out of more than 350 contributors to the ATT&CK knowledge base. Thus, participating in the ATT&CK Evaluations continues the critical dialogue between several teams to balance visibility into and usability of ATT&CK techniques and procedures.
With the internal dialogue established and sustained via our engagement with MITRE Engenuity, our parallel participation in AV-Comparatives’ EPR Test provides the necessary balance to factor in user-centric real-world needs. The result is composite use of both tests because both tests have significant merit and are (different) horses for courses.
Conclusion
With an aim to not only lead in prevention and response, but also to deliver a competitive total cost of ownership score, ESET sees decision-makers as the key readers of the AV-Comparatives EPR Report.
The stimulating dialogue instigated by the MITRE Engenuity ATT&CK Evaluations is a whole other animal. For enterprises, institutions, and other select businesses with SOC teams or skilled security staff in-house, we encourage you to continue leveraging the ATT&CK knowledge base and looking more deeply at the ATT&CK Evaluations. However, we see the true value there as a trigger for innovation, experimentation, and constant improvement.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About ESET
For 30 years, ESET® has been developing industry-leading IT security software and services for businesses and consumers worldwide. With solutions ranging from endpoint security to encryption and two-factor authentication, ESET’s high-performing, easy-to-use products give individuals and businesses the peace of mind to enjoy the full potential of their technology. ESET unobtrusively protects and monitors 24/7, updating defenses in real time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company. Backed by R&D facilities worldwide, ESET became the first IT security company to earn 100 Virus Bulletin VB100 awards, identifying every single “in-the-wild” malware without interruption since 2003.


ESET 研究建議 儘快將 Roundcube Webmail 升級至最新版本

ESET 研究團隊已經密切追蹤 Winter Vivern 的網絡間諜行動超過一年。在我們的例行監測中,我們發現該組織從 2023 年 10 月 11 日開始利用 Roundcube Webmail 伺服器中的一個零日 XSS 漏洞進行攻擊。根據 ESET 的遙測數據,這是一個與 CVE-2020-35730 不同的漏洞,該攻擊活動針對歐洲政府實體和一個智庫的 Roundcube Webmail 伺服器。
Winter Vivern 是一個由 DomainTools 於 2021 年首次揭示的網絡間諜組織。根據推測,該組織至少從 2020 年開始活動,其目標是歐洲和中亞的政府機構。為了達成入侵目標,他們使用了惡意文件、釣魚網站和自定義的 PowerShell 後門,並自 2022 年開始,一直在針對屬於政府機構的 Zimbra 和 Roundcube 電子郵件伺服器進行攻擊。我們觀察到該組織在 2023 年 8 月和 9 月利用了 Roundcube 中的另一個 XSS 漏洞 CVE-2020-35730。請注意,Sednit(也稱為 APT28)也在利用這個舊的 Roundcube XSS 漏洞對同一目標進行攻擊。
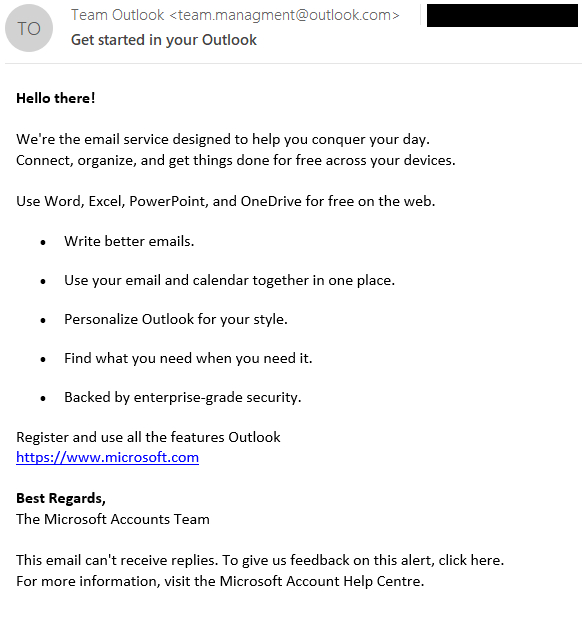
利用分配給 CVE-2023-5631 的 XSS 漏洞,攻擊者可以通過發送特殊製作的電子郵件消息進行遙距攻擊。在這次 Winter Vivern 的攻擊活動中,電子郵件是從 team.managment@outlook[.]com 發送的,主題為 “Get started in your Outlook”,如圖 1 所示。
Winter Vivern 通過利用 Roundcube 的零日漏洞加強了其行動。此前,他們已經利用了 Roundcube 和 Zimbra 中已知的漏洞,而這些漏洞的概念證明已在網上公開。儘管該組織的工具集的複雜性較低,但由於他們持續存在並非常頻繁地進行釣魚活動,以及大量與互聯網相關的應用程式未定期更新,即使已知漏洞的存在,Winter Vivern 也對歐洲政府構成一定的威脅。
About Version 2
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products. Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
關於ESET
ESET成立於1992年,是一家面向企業與個人用戶的全球性的電腦安全軟件提供商,其獲獎產品 — NOD32防病毒軟件系統,能夠針對各種已知或未知病毒、間諜軟件 (spyware)、rootkits和其他惡意軟件為電腦系統提供實時保護。ESET NOD32佔用 系統資源最少,偵測速度最快,可以提供最有效的保護,並且比其他任何防病毒產品獲得了更多的Virus Bulletin 100獎項。ESET連續五年被評為“德勤高科技快速成長500 強”(Deloitte’s Technology Fast 500)公司,擁有廣泛的合作夥伴網絡,包括佳能、戴爾、微軟等國際知名公司,在布拉迪斯拉發(斯洛伐克)、布裏斯托爾(英國 )、布宜諾斯艾利斯(阿根廷)、布拉格(捷克)、聖地亞哥(美國)等地均設有辦事處,代理機構覆蓋全球超過100個國家。