In today’s business environment, cloud computing is the most flexible and cost-efficient method to set up operations. Yet, as businesses increasingly rely on cloud-based services to store, manage, and exchange data, this attracts unwanted guests.
Consequently, there has been a significant increase in data breaches, disrupting business operations and jeopardizing companies’ security and compliance worldwide. These breaches often stem from attackers exploiting vulnerabilities and misconfigurations in cloud systems.
This blog will cover the most recent cloud security trends that are shaping the industry. By keeping up with these developments, businesses can enhance the protection of their digital assets and reinforce the security of their cloud computing infrastructure to mitigate potential breaches.
Key takeaways
Cloud computing offers businesses cost-efficiency, flexibility, and scalability, but it also introduces security vulnerabilities and risks
The shared responsibility model requires cloud providers to secure the infrastructure while customers secure their data and applications
The cloud security landscape is constantly evolving and businesses need to keep up with new trends
Cloud security has progressed significantly with improvements in data protection, network security, and connectivity
The future of cloud security will see more integration of AI and machine learning
To keep up with the trends, organizations can regularly update security policies, implement advanced threat detection, embrace automation, and foster a culture of security awareness
Understanding the concept of cloud security and why it matters today
Cloud computing solves many business problems like scalability, cost-efficiency, and flexibility. At the same time, for most businesses, it also means stepping into unfamiliar territory where it’s easy to leave gaps that hackers could exploit.
The shared responsibility model is also something that needs to be established. In it, the cloud provider is responsible for securing the underlying cloud infrastructure, while the customer is responsible for securing their data and applications. Though it sounds simple, it’s not always easy to crystallize a comprehensive cloud security approach.
As more organizations embrace cloud adoption and rely on cloud services, the need for effective cloud security measures has never been greater.
Evolutions in cloud security
Cloud security has come a long way since its inception. Initially, concerns regarding data protection and network security limited cloud adoption (as well as a requirement for stable online connectivity). Fortunately, as cloud technology has matured, so has its security.
The concept of cloud computing emerged in 1950 with the development of mainframe computers, which could be accessed through thin or static clients. Since then, cloud computing has undergone several iterations, progressing from static clients to dynamic ones, from software-based systems to service-oriented solutions.
Security problems started cropping up when businesses began entrusting their data to major companies like Amazon. Despite the numerous benefits and efficiency improvements, storing critical data on servers that customers couldn’t physically access challenged the conventional notion of security. As data storage expanded in type and volume, hosting companies implemented more extensive precautions to safeguard the data.
The current state of cloud security
Today’s cloud service providers go to great lengths to protect the data stored on their servers. This includes thorough employee background checks to minimize the risk of insider attacks and isolation procedures that prevent one company from accessing another’s data. Yet, it’s still the user’s responsibility to ensure secure passwords and connections like they would have if the data were stored locally.
Encryption of data at rest and in transit, network segmentation, and adopting cybersecurity mesh architectures have all enhanced cloud security. As cloud environments become increasingly complex and multi-cloud adoption rises, ensuring consistent security across different platforms and providers becomes challenging. This emphasizes the need for ongoing security training and proactive new technologies adoption.
An in-depth look into key cloud security trends for 2023
Security teams must be aware of the latest cloud security trends to stay ahead of the ever-changing threat landscape. Here are the main ones you should be aware of:
1. Cybersecurity mesh
Companies are adopting the concept of cybersecurity mesh to ensure the security of data and assets in the cloud. This approach involves creating a distributed network and infrastructure that forms a security perimeter around the individuals and devices connected to the network. By implementing cybersecurity mesh, companies can centrally manage data access and enforce security policies, aligning with Zero Trust architecture principles.
2. Hybrid and multi-cloud environments
The trend in cloud security involves adopting a hybrid approach or leveraging multiple cloud services. Organizations can migrate their data entirely to the cloud or keep some data and services hosted privately. The hybrid approach combines local and cloud-hosted services, allowing for more secure deployments. Additionally, using multiple clouds has gained popularity, with companies adopting a multi-cloud strategy. This approach allows for better utilization of security tools across different environments, such as SIEM and threat intelligence.
3. Zero Trust
The principle of Zero Trust emphasizes verifying rather than blindly trusting anything within or outside an organization’s perimeters. With the increasing reliance on cloud services, Zero Trust should be a priority for all organizations. Traditional perimeter security measures and firewalls are insufficient to protect valuable resources such as user data and intellectual property. Zero Trust enhances security around every device, user, and connection, enabling proactive threat management and comprehensive defense strategies.
4. SASE framework
Gartner has stated that the future of network security lies in the cloud. The Secure Access Service Edge (SASE) framework offers a cloud-based cybersecurity solution that supports digital enterprises’ dynamic and secure access needs. It combines wide area networking (WAN) capabilities with multiple security features such as anti-malware and security brokers to establish a comprehensive security environment within a cloud infrastructure. SASE is an essential framework for securely connecting users, systems, and endpoint devices to a unified cloud environment.
5. Security integration into DevSecOps
DevSecOps is a methodology that integrates security protocols throughout the software development lifecycle (SDLC). Organizations can address threats proactively rather than reactively by incorporating security measures early in the development process. DevSecOps is particularly effective in fast-paced, fully automated software development lifecycles, enabling secure innovation. Collaboration between DevOps and security teams is essential to implement strong security measures throughout the entire supply chain and make security a continuous process within the continuous integration/continuous delivery pipeline.
6. Cloud-native tools and platforms
Cloud-native applications designed specifically for the cloud environment are becoming increasingly prevalent. These applications take advantage of the speed and efficiency offered by cloud platforms. Traditional security tools designed for on-premises applications may not be adequate to protect cloud-based resources. Companies recognize the need to invest in cloud-based security tools and platforms to safeguard their cloud resources against potential attacks.
The dark side of trends
While cloud security progresses along with cloud computing, it’s crucial to acknowledge the dark side of trends that security teams must address. Attackers are finding new ways to exploit vulnerabilities, and organizations must be cautious. Here are the emerging threats directed at cloud computing security:
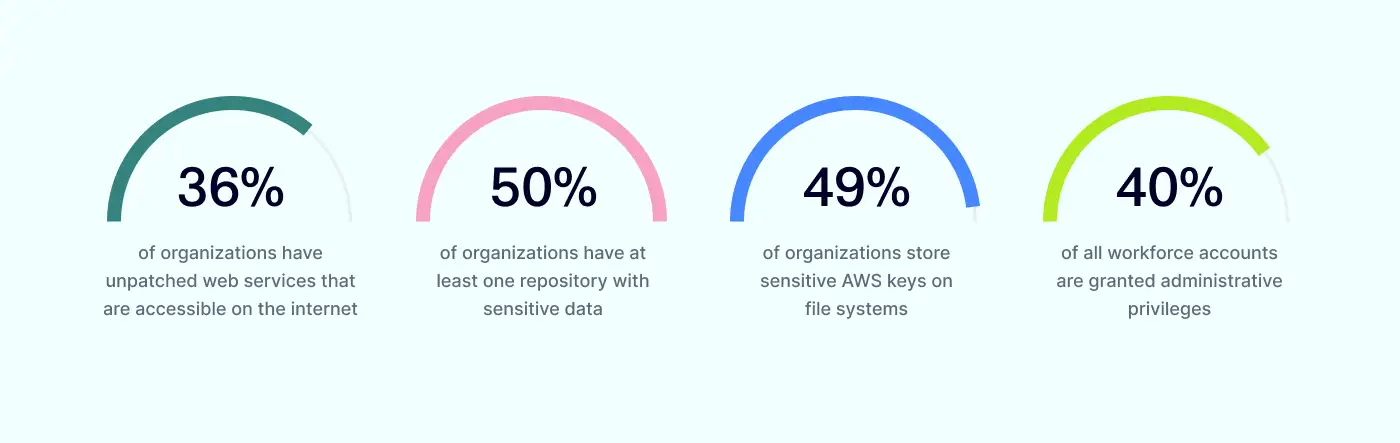
Slow patching leaves web services vulnerable
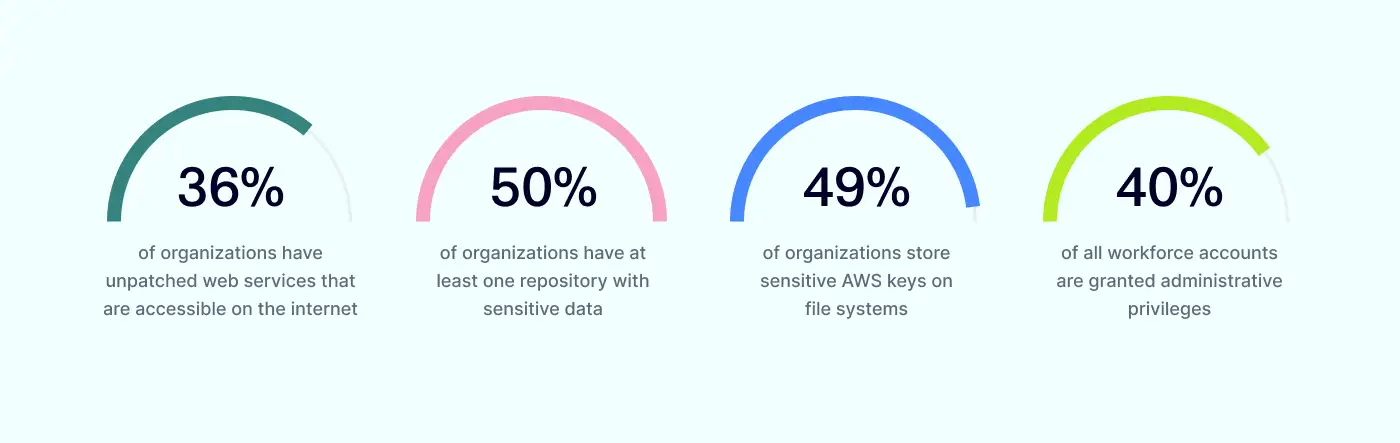
Based on the Orca Security report, 36% of organizations have web services in their cloud environment that are accessible to the Internet but remain unpatched. Such services pose a significant risk as they contain known vulnerabilities and bugs, which can serve as primary entry points for attacks on cloud environments. The absolute majority of cyber-attacks on cloud infrastructure begin with the exploitation of these known vulnerabilities.
Unpatched vulnerabilities provide malicious actors with easy access to cause service downtime, enable remote code execution, or facilitate unauthorized remote access in certain cases. Users must promptly apply fixes through updates or patches to contain potential risks.
Git repositories containing sensitive data
Storing sensitive data in Git repositories should be avoided at all costs. It may include information like database passwords, API keys, encryption keys, hash salts, and secrets, which can be mistakenly pushed into a Git repository. While it deviates from security practices, the inclusion of this data into the source code of an application might inadvertently leak it to hackers. Therefore, repositories must be checked for sensitive information, which should be removed from the repository and its history.
AWS keys storage on file systems
At least 49% of organizations store sensitive AWS keys on file systems within virtual machines. AWS keys can function as backdoors to your system. They can grant access to all your resources and the ability to perform any operation, like launching EC2 instances or deleting S3 objects. Therefore, it’s crucial always to store your AWS keys separately and avoid sharing them with external parties.
Instead of AWS, it’s a good practice to use temporary credentials. They include an access key ID and secret access key that would also include a security token specifying the expiration date of the credentials.
Too many administrators for a single organization
Single sign-on providers suggest putting limits on the administrative privileges. For instance, only 50% of admins should have super admins privileges, if you have more, you’re risking your organization’s security. This is much more than it would be advisable, as administrators have many permissions that directly relate to your information security.
As a rule of thumb, it’s generally inadvisable, except in exceptional circumstances, not to define an IAM role with full administrative privileges. Such a role grants anyone who assumes it the ability to perform any action on any resource within the account. This violates the Principle of Least Privilege (PoLP), significantly expands the attack surface, and increases the risk of a full account takeover.
The road ahead: future of cloud security
Looking ahead, the future of cloud security is full of challenges and opportunities. One of the most obvious courses for development is the continued integration of artificial intelligence and machine learning into cloud security operations. These technologies will enable autonomous threat detection, automated incident response, and adaptive security measures.
The speed at which these developments will reach the end-users depend on the service providers’ initiatives to invest in advanced technologies. Yet, it’s likely that the shared responsibility model will continue to be relevant, and while the user will be provided with more tools, it will still be needed to make sense of the provided data and act on it.
Conclusion
Cloud security is an ever-evolving landscape with new trends and challenges emerging regularly. For this reason, organizations must stay alert and recognize the importance of cloud security and its recent developments.
By adopting advanced technologies, adopting proactive security measures, and fostering collaboration with cloud providers, organizations can navigate the complex cloud environment while safeguarding their data, applications, and infrastructure against evolving security threats.
FAQs
What is the role of AI in cloud security?
AI can be used to enhance threat detection and response capabilities by analyzing vast amounts of data and identifying patterns that may indicate security threats or anomalies. In addition, AI can assist in automating security tasks, such as security patching, vulnerability management, and incident response. This can help prevent various types of attacks like malware, phishing attempts, and data breaches, reduce the workload on security teams, and improve overall efficiency.
What is a cloud access security broker (CASB), and how does it contribute to cloud security?
CASB is an intermediary between an organization’s premises infrastructure or network and cloud service providers. It helps organizations extend their security policies and controls to the cloud environment. Offering a range of security functionalities, it also helps to expand visibility into cloud storage, data loss prevention (DLP), access control, threat detection, encryption, and compliance monitoring.
How does the Zero Trust model enhance cloud security?
The Zero Trust model enhances cloud security by shifting the traditional perimeter-based security approach to a more dynamic and granular model. Instead of blindly trusting users or devices within a network, Zero Trust assumes that all network traffic, whether from inside or outside the network, is potentially malicious and must be verified before granting access. That way, organizations can reduce the risk of lateral movement within their cloud environment, mitigate the impact of compromised credentials, and improve overall security posture.
What strategies can organizations adopt to stay ahead of future cloud security trends?
To stay ahead of future cloud security trends, organizations can:
Regularly assess and update security policies
Implement advanced threat detection and response capabilities
Embrace automation and orchestration
Foster a culture of security awareness
All of these actions improve overall business security posture and help stay one step ahead of unauthorized access attempts.
How can NordLayer help?
As cloud computing is at the center of modern business operations building, its security is at the forefront of business priorities. A robust cloud security strategy must include access controls, encryption, firewalls, and auditing. However, finding a reliable partner isn’t always easy.
NordLayer can be a helpful ally when securing public and private cloud infrastructure setups. Using our Virtual Private Gateways, SaaS applications, and other resources can be reached efficiently but securely. With features like IP allowlisting, overall business network security posture is improved, allowing only authorized personnel to access your cloud environments.
Identity checks can be enforced using 2FA and SSO to ensure secure authentication. A tandem of all of these features makes cloud security management safer and easier to manage.
Contact the NordLayer team to learn more about how your cloud infrastructure could be secured.