In the previous article – part one of this topic, I covered the basics of HTTPs requests you should know how to create/modify using OWASP’s ZAP. Also, I have covered how to set up a test environment with two virtual machines run by VMware Workstation. If you somehow ended up here and didn’t read the first part – How to test application with ZAP – Part One, please read it first and set up the environment!
I will start by explaining what ZAP is and what you can do by using it.
What is ZAP?
ZAP stands for Zed Attack Proxy. This tool was developed by the OWASP community and is actively maintained by them. It is a free, open-source, so-called web app scanner. In general, it is a well-known application security testing (DAST) tool. The official site where you can download this tool can be found at this link. You can also find some tutorials on their site that will help you learn more about using this tool.
ZAP can be installed and used in Windows, Linux, or Mac OS. It can be also run in a Docker container.
This tool is used mainly for finding vulnerabilities in web applications, pentesting, etc. In this article, we will mainly use this tool for creating/modifying requests and sending them to the basic web application we will set up in Ubuntu.
ZAP can scan and find vulnerabilities related to:
- SQL injection
- Broken Authentication
- Sensitive data exposure
- Broken Access control
- Security misconfiguration
- Cross-Site Scripting (XSS)
- Insecure Deserialization
- Components with known vulnerabilities
- Headers with low-level security
Key features ZAP contains:
- Active Scan
- Passive Scan
- OWASP ZAP Fuzzer
- OWASP ZAP API
- WebSocket Testing
- JAX Spidering
- Scan Policy Management
- ZAP Marketplace
*Before installing ZAP, check if your system already has Java 8+ installed because that is the only requirement. I have already provided ZAP official site where you can download it, but you can also do it via terminal with the following command: sudo apt install -y zaproxy. Please run this command to install ZAP in your new Kali machine so we have it prepared for the third part of the series.
How are we going to test the application using ZAP in a real test environment?
As I mentioned, you first need to set up the test environment described in the previous part of this series. Then we will deploy the web application we create via Docker inside an Ubuntu machine. We will create the test application in Angular 13. And after that, we will make the connection between Kali and Ubuntu. From Kali, we will use ZAP to make requests and try to hit the running web application in Ubuntu.
How to create an Angular web application
I created an Angular application in Windows. First, you will need to download a code editor. For this guide, I used Visual Studio Code. You can find download it from its official site. Then you would need to install Node.js from their official site. Download the LTS version and install it.
From now on, we will use the Visual Studio Code terminal to issue the commands.

Using the terminal, we will first install Angular CLI with the following command:
npm install -g @angular/cli
Then you can check the version of the installed CLI:
ng version
You can also check if node js is installed properly by using this command:
npm -v
Now we will use Angular CLI to create a new app with this command:
ng new <application name>
Good, now we have the app, and we want to test if the installation was successful by running the application with this command – ng serve; You should see the application running on your localhost – port 4200 (http://localhost:4200). If that port is not used.
We want to prepare our application for deployment, so we need to configure a few additional things. First, we want to create a Dockerfile so we can deploy the app with Docker.
To do so, we are going to the application’s main folder and adding a new file, which we are naming “Dockerfile.”
Paste this code in the Dockerfile:
FROM node:16.14.0 as node
WORKDIR /app
COPY package.json /app/
RUN npm install
COPY ./ /app/
RUN npm run build --prod
FROM nginx:latest
COPY ./nginx.conf /etc/nginx/conf.d/default.conf
RUN rm -rf /usr/share/nginx/html/*
# NOTE: Change this path according to your project's output folder, check in angular.json outputPath
COPY --from=node /app/dist/ /usr/share/nginx/html
EXPOSE 80
We will use Nginx to host the angular build inside the container. We will need to create another file in the main folder and name it “nginx.conf”. Copy this code to the file:
server {
listen 80;
sendfile on;
default_type application/octet-stream;
gzip on;
gzip_http_version 1.1;
gzip_disable "MSIE [1-6]\.";
gzip_min_length 256;
gzip_vary on;
gzip_proxied expired no-cache no-store private auth;
gzip_types text/plain text/css application/json application/javascript application/x-javascript text/xml application/xml application/xml+rss text/javascript;
gzip_comp_level 9;
root /usr/share/nginx/html;
location / {
try_files $uri $uri/ /index.html =404;
}
}
Now you need to build the application, so the dist folder gets created. You can do that with the command – ng build.
When you have created the application, you can copy it to your Ubuntu VM. I used GitHub and just cloned the repo to my Ubuntu Server.
How to deploy the Angular application
First, run both VMs in VMware – Ubuntu and Kali, so you can be ready for the next steps.
To deploy the application, we will use Docker. For me, it is one of the easiest ways for deployment.
First, we will need to download and install Docker. We will download Docker, where we want to deploy the Angular application, which would be on our Ubuntu machine.
The easiest way to install Docker in Ubuntu would be to do it through Kali machine, which you used to SSH inside the Ubuntu Server; I did this because Ubuntu Server is quite frugal, and Kali lets me paste the commands easily, has coloring for the commands, etc.
In Kali terminal type command:
ssh user_name@ubuntu_ip_adress , in my case it would be:
ssh jenny@192.168.221.129
Now you will be asked for the password of the Ubuntu VM. Type it in – or use key authentication if that’s easier for you – you should now be inside your Ubuntu machine. We are now going to install Docker and create our container on the Ubuntu Server.
We will download Docker to Ubuntu with the following commands:
curl -fsSL https://download.docker.com/linux/ubuntu/gpg | sudo gpg --dearmor -o /etc/apt/keyrings/docker.gpg
echo \
"deb [arch=$(dpkg --print-architecture) signed-by=/etc/apt/keyrings/docker.gpg] https://download.docker.com/linux/ubuntu \
$(lsb_release -cs) stable" | sudo tee /etc/apt/sources.list.d/docker.list > /dev/null
sudo apt update
sudo apt-get install docker-ce docker-ce-cli containerd.io docker-compose-plugin
Now we have installed Docker. We can check that by running a basic command to list all containers. In our case, because we didn’t create and run any container yet, we will have an empty list. Command is:
sudo docker ps
Now we are finally at the step of deploying our web application via Docker.
We want to change the directory (cd <folder_name>) to the web application project folder and run the following commands while inside that directory:
sudo docker build -t testzap:v1.0.0 -f ./Dockerfile .
sudo docker run -p 80:80 -d testzap:v1.0.0
Then test using
sudo docker ps
We can check the list of running containers with this command:
sudo docker container ls
Great, our application now runs on port 80.
Setup ZAP to use in the browser
We will use Kali as an attacker machine, so we will send requests from it to our victim/target machine – Ubuntu.
You probably already installed ZAP, but if you didn’t, check out the What is ZAP section.
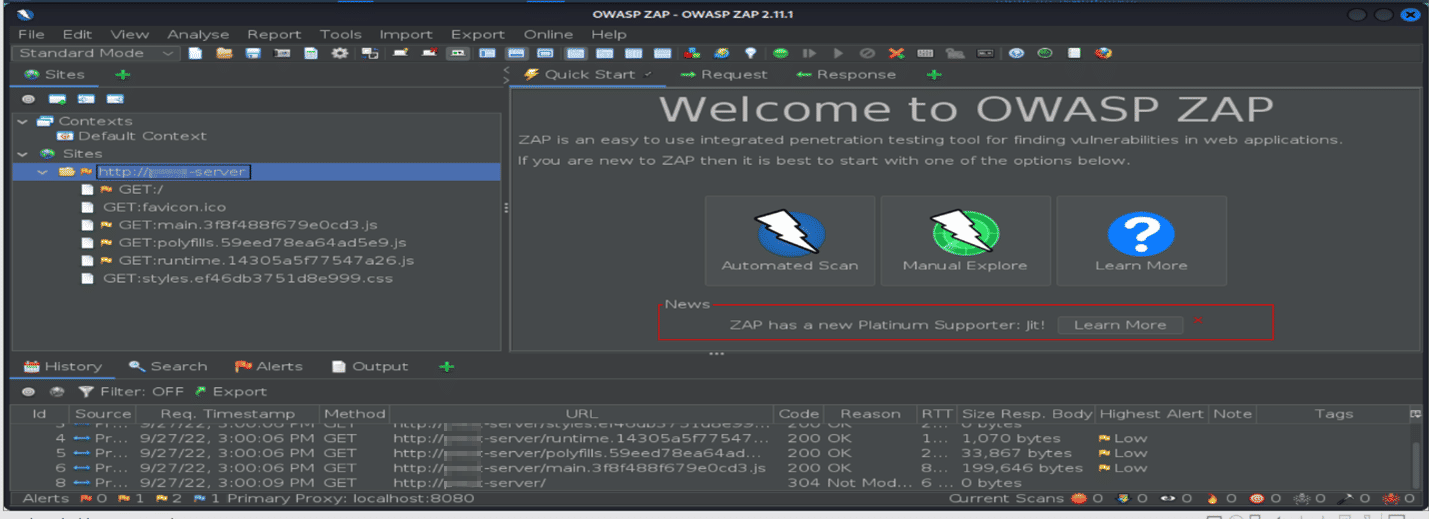
Run ZAP. This window will pop up:

We can select no, and if we want to save the session, we can do it at a later time.
If you choose to save the session, it will be saved to the disk in an HSQLDB database. The database gets a default location and name. You can access the db later. If you don’t persist a session, the files are deleted once you exit ZAP.
Then you will see the list of Add-ons. Click on Update all.
I like to use the Brave browser, so you can also check it out and download it on this site.
How to use ZAP in Brave?
We will need to install a proxy extension called proxyswitchyomega. Search it in Brave and install it.
It is a good practice to create separate profiles in the browser, which we are going to use only for our security testing.
We would also like to configure proxyswitchyomega. We are going to click on it in the browser and go to the Settings section Profiles –> Proxy and change localhost in field proxyserver/servers. And here, we can also rename the server (ZAP) and click on Apply.
Great, ZAP in Browser is set up.
Go to the browser, click on the ProxySwitchyOmega button, and click on ZAP (or how you named your proxy). Then navigate to the http://<Ubuntu_IP>:80, and our new application will appear. In my case, its 192.168.221.129:80.

Also, within the ZAP interface, inside the tree on the left-hand side under sites, you will see that the URL of the application will appear. In my case, under sites, ZAP is showing the domain name (http://**-server); this is because I have previously set that up on Kali. The IP address resolved to that name is the one from above – 192.168.221.129 – which is my Angular app.
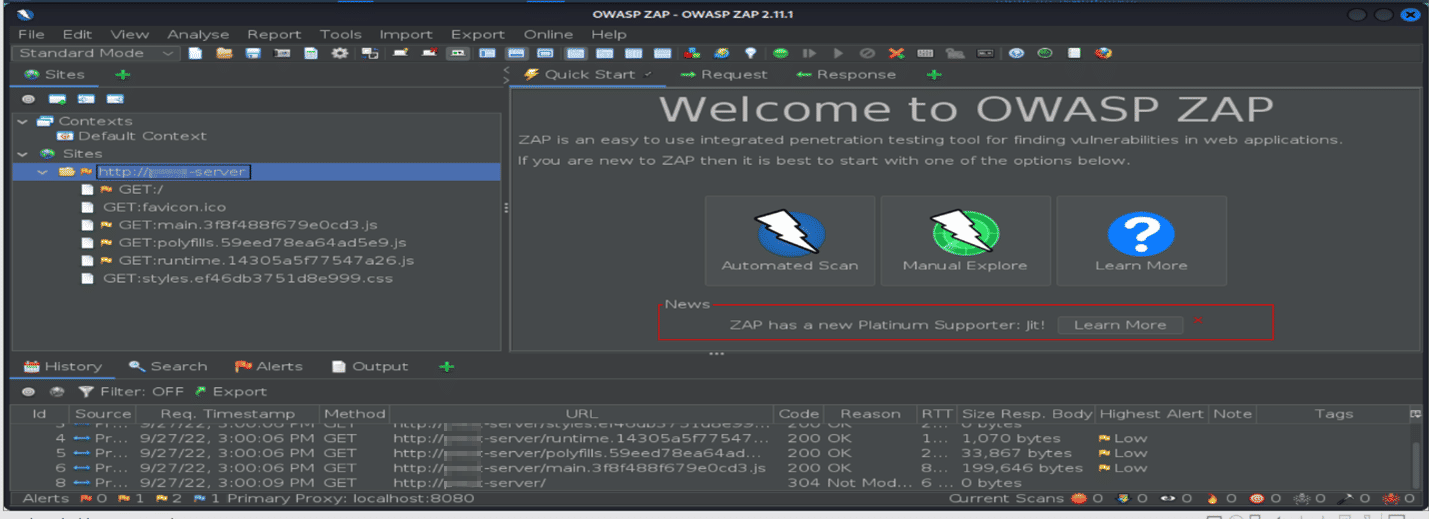
Finally, we can now start investigating our application via ZAP!
In the next chapter, I will show you how to investigate the application!
Conclusion
In this second part of the testing with ZAP series, I tried to explain what the ZAP tool is used for, how to create an Angular web app, deploy it using Docker and send the request with ZAP.
You are now fully equipped to start with security testing. You can also use other security tools with this test environment setup if you wish (for example, Burp Suite).
Interesting links related to the ZAP topic:
#ZAP #Angular14 #Brave #Docker #Kali #Ubuntu
Cover photo by Markus Winkler