Currently, most companies rely on their Information Technology department and IT service management (ITSM) to meet the demands of users and become increasingly competitive.
But what is this strategy about after all? In practice, the term IT Service Management (ITSM) refers to the processes and resources used by IT teams to deliver IT services in an agile and effective manner, positively impacting a company’s performance.
Beyond the delivery of services and support, this set of practices prioritizes the needs of users and the services provided, seeking continuous improvement rather than taking only IT systems into account.
In this post, we bring you a complete guide, with everything you need to know about IT Service Management (ITSM) through the following information:
- What Is IT Service Management (ITSM)?
- Benefits and Importance of IT Service Management (ITSM)
- Key IT Service Management (ITSM) Processes
- ITSM, ITIL, DevOps: Understand These Abbreviations
- What Is the Difference Between ITSM And ITIL?
- Services Related to ITSM
- Workforce Training: Understand this Approach
- ITSM Resources
Read it until the end!
- What Is IT Service Management (ITSM)?
IT Service Management (ITSM) needs a strategic approach focused on the end-user. ITSM strategies contribute to creating an IT organization that matches the needs of users and their businesses.
In practice, IT service management (ITMS) consists of the strategies used by companies that offer IT services to their users. Therefore, technologies, processes, and people are essential in ITSM.
This mechanism seeks to understand the needs of the end-user in order to meet them. This involves the design of IT systems with efficient demand management, implementation of processes, hardware, and software that improve services.
That is, ITSM functions provide the development of IT systems capable of meeting expectations and accommodating evolving technologies.
An institution that uses IT Service Management (ITSM) can effectively offer responsive services with more availability, at an affordable price. This solution also contributes to improving employee productivity and consumer experience, as well as optimizing the assessment and improvement of services.
- Benefits and Importance of IT Service Management (ITSM)
All companies depend on IT service management (ISTM) to some extent. This is what enables simplified management of problems, service requests, incidents, changes, and IT assets, among other actions.
ITSM helps IT professionals, and the principles of service management favor a company as a whole, ensuring more efficiency and better performance.
Moreover, structured approaches in IT service management (ISTM) have the purpose of aligning information technology with business goals and standardizing services, considering resources, budgets, and results. It also allows you to reduce risks and expenses and improve the consumer experience. Its benefits include:
- The possibility of aligning IT teams with the company’s priorities, using metrics that calculate their success;
- It enables different departments to collaborate;
- It unites information technology professionals to development teams through facilitated project management approaches;
- It also makes it possible to qualify IT professionals to share information that guarantees constant improvements;
- It optimizes the coordination of requests, ensuring a more efficient service;
- It directs the focus of customer services through self-service and optimized processes;
- It allows one to respond to incidents quickly and prevent future inconvenience.
- Key IT Service Management (ITSM) Processes
Recently, ITIL’s version 4 has stopped recommending ITSM “processes”, replacing them with ITSM “practices”. This term change explains that certain elements must be considered to achieve a holistic view of the work. Culture, technology, and information and data management are among them.
However, for us, what matters is not the change of terminology, but the use of the best resources by information technology teams to ensure the efficiency of services. The following recommended actions stand out:
- Service Request Management
Service request management must be repeated, after all, this is what makes it possible to deal with different requests, such as access to an application, hardware update, and software improvement. This workflow is capable of automating tasks and qualifying customers to accomplish them.
Knowledge management is the possibility of generating, using, sharing, and managing the knowledge and data of a given institution. It consists of a multidisciplinary approach that allows achieving the company’s goals through good use of knowledge.
This process aims to allow the assets of a company to be deployed, maintained, accounted for, updated, and discarded at the right time. In short, its function is to ensure the tracking and use of valuable items by a company, whether they are tangible or intangible.
Here, we refer to a process that has the function of responding to incidents, such as service interruption. Taking all software services used by companies today into account, there are many chances of failure. For this reason, this process is used in order to solve problems quickly.
When an incident occurs, IT teams need a solution that enables them to respond effectively so that recovery is agile. In this sense, it is necessary to communicate with all stakeholders, remove obstacles to solve the incident and improve the service to avoid further downtime in the future.
Nevertheless, incident management aims to resume services quickly, without harming the core business. Therefore, it may depend on a temporary solution, trying to identify the source of the problem later on.
In this case, the issue is to detect and manage the reasons for incidents in an IT service. That is, problem management is not limited to identifying and correcting incidents, but to understanding their reasons and eliminating them.
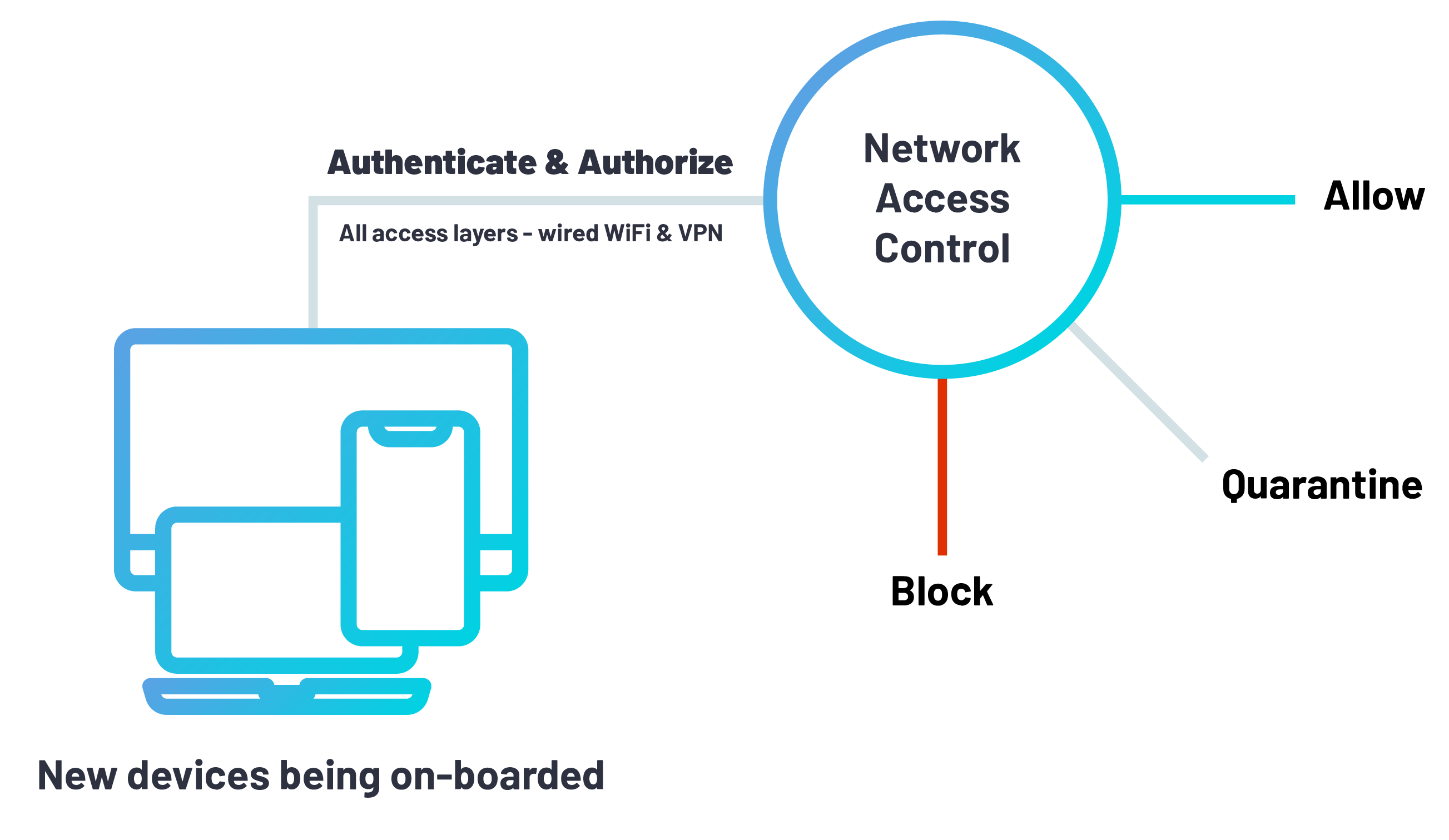
Change management aims to review the IT system before the requested change takes place in the network of an institution, reducing downtime in the operation. In other words, this process has the function of ensuring these changes do not affect its performance. Additionally, network changes are intended to eliminate vulnerabilities, upgrade a component to optimize performance or replace an obsolete or defective component.
There are three types of changes in the IT system or service:
- Standard changes, which consist of routine changes and obey a predefined process of risk assessment and pre-approval;
- Normal changes, which do not have predefined processes and must involve a risk assessment and an approved implementation plan before making the changes to the network and;
- Emergency changes, which are necessary when unforeseen interruptions occur, which threaten the network.
Configuration management aims to ensure consistency of performance, functional and physical attributes of a product with its requirements, aesthetics, and operational information.
Also known as IT automation, it allows the configuration of computer system resources, servers, and other assets to be efficient and reliable, most of the time, through a high level of automation.
This is because automation makes it possible to rely on redundancies that contribute to avoiding problems caused by human failures and keeping assets in good condition.
Configuration management applies to systems such as:
- Servers;
- Databases and other storage systems;
- Operating system;
- Network;
- Forms;
- Programs.
The configuration of these systems is extremely important for the good performance of your company, since it is the configuration that guarantees its operation. Other advantages of management include:
- Decreased number of security interruptions and breaches through the visibility and tracking of changes in your systems;
- Cost reduction, as duplication of technology equipment is avoided;
- Improved experience for IT teams and users, immediately identifying and correcting inappropriate configurations that may impair the performance of the equipment;
- Control of processes through the enforcement of policies and procedures related to asset identification, auditing, and status monitoring;
- Faster troubleshooting, better service quality, and lower software engineering costs;
- Effective change management, which allows avoiding problems;
- Agile recovery of service when there is downtime; and
- Better release management and transparent status accounting.
- ITSM, ITIL, DevOps: Understand These Abbreviations
There are several structures used to guide the work of IT teams. For this reason, there are several abbreviations you need to know about the structures that most influence the work of these professionals. Here they are:
IT Service Management (ITSM) refers to the delivery of IT services to consumers. This approach can be influenced by DevOps concepts and planned in order to align with ITIL practices.
This is the most frequently accepted approach to ITSM. It focuses on practices adopted to align IT services with the demands of a business. It can contribute to companies adapting to changes and continuous scales.
ITIL 4, its latest update, guides IT professionals to a holistic, commercial, and audience-valued benchmark, stimulating a more flexible approach based on teamwork. Its guiding principles recommend simplicity, collaboration, and feedback.
Often, this approach is misunderstood as a set of “rules” rather than guidelines that can be interpreted.
DevOps ensures IT services are delivered in a practical and agile manner, as well as improving collaboration between development professionals and IT operations so that software is created and tested securely. Its benefits include: trust, the ability to solve critical problems quickly, faster software releases, and better management of unplanned work.
The DevOps concept is based on collaboration between teams that previously worked in isolation from each other. It is about working collaboratively.
Generally, ITSM and DevOps are launched as opposing options. That is, it is not usually very clear what these tools offer and how they can work together.
However, if your team intends to work smarter and faster, without giving up the process and control, they need to use ITSM and DevOps resources.
This is because ITSM can be used to promote agility and meet the different demands of companies. DevOps benefits the execution of tasks, promoting collaboration.
- What Is the Difference Between ITSM And ITIL?
Information Technology Infrastructure Library (ITIL) refers to best practices for IT service management (ITSM). Its latest version is ITIL 4, launched in 2019, which promotes collaboration as a way to provide agility and flexibility for organizations. ITIL 4 is based on six processes, namely:
- Plan: strategic planning should consider three aspects: user demands, organization limitations, and future directions;
- Engage: All stakeholders should have their demands understood. For this, user experience needs must be interpreted in order to meet their expectations with IT services;
- Design and Transition: the design must also be prepared and take into account the needs of the user, in addition to the company’s strategies;
- Obtain and Build: it is possible to create a new service internally or obtain it, this will depend on the technologies available to meet the user needs;
- Delivery and Support: after creating the service and making it available to users, IT support must be offered to enable the effective use of the solution;
- Improve: an efficient IT service management (ITSM) enables the continuous monitoring and improvement of the services offered.
- Services Related to ITSM
An example of an IT Service Management (ITSM) related service is when you access an online help center and have your questions answered by a chatbot. These virtual agents are programmed to respond to frequent user inquiries, such as:
- How do I reset my password?
- Why is my Internet signal fluctuating?
In addition to answering questions like these, IT Service Management (ITSM) allows one to:
- Respond to requests based on machine learning;
- Visualize data in order to prioritize resources and optimize performance;
- Manage incidents and any problems;
- Restore services in an agile manner, if necessary;
- Manage assets.
- Agile Service Management
Agile Service Management is a set of values that contribute to making organizations more flexible. Therefore, Agile acts as a solution for the time-consuming development processes, which can delay the release of new features.
The Agile Manifesto for Software Development, launched in 2001, presents the following values:
- Individuals and interactions about processes and tools;
- Software that works on complete documentation;
- Customer collaboration on contract negotiation; and
- Response to change rather than following a plan.
The concept of Agile has gained relevance in other areas, such as sales. This is because people started to apply its main values in all types of businesses, resulting in numerous versions of the Agile manifesto, such as Modern Agile.
In addition to the four values, an Agile Service Management has 12 principles. These are:
- Meet the expectations of the public through the early and continuous delivery of valuable work;
- Split complex operations into simpler tasks that can be completed quickly;
- Understand that the best services are performed by self-organized teams;
- Provide employees with the environment and resources they need and trust in their ability to execute the project;
- Carry out processes that enable sustainable efforts;
- Maintain a constant pace for the completion of a job;
- Contemplate the change of requirements, even at the end of a job;
- Daily meetings of the teams throughout the project;
- Reflect on how to make the operation more effective by the team, followed by adjustments to achieve this goal;
- Measure the evolution by the amount of work completed;
- Constantly seek excellence; and
- Leverage changes to gain competitive advantages.
The goal of the Agile Manifesto is to ensure quality by creating products that meet the demands of the public and meet their expectations. Its 12 principles have the function of ensuring a work focused on the user and able to adapt to the changes in their needs and demands of the market.
Now that you know what Agile is, you may be wondering how it is translated into IT service management. In practice, for the IT department to act in an agile manner, it must follow the following guidelines:
- Involve consumers in the design of services and processes;
- When launching a new solution, launch a version for a small audience and the final version according to its feedback;
- Search the processes for the user, removing unnecessary steps;
- Authorize its IT team to go beyond standardized processes to achieve more efficient solutions.
Also, you need to keep in mind the Agile approach to software development is committed to designing a program with regular increments, offering new versions to users after brief periods of work, which are called sprints.
- Workforce Training: Understand this Approach
One can have more satisfied users by using innovative technology through workforce training. This concept assumes customers want to actively resolve their demands through their own devices and applications.
In this context, the role of the IT department is to provide everything the user needs to solve their problems and be satisfied.
In addition, the training of the workforce aims to engage employees, after all, this is what guarantees productivity, customer satisfaction, and good performance for the company.
However, in order to ensure the motivation of employees through workforce training, one needs to invest in technology, processes, and IT staff.
- ITSM Resources
Some features cannot be overlooked when it comes to ITSM software and tools. Here is what you should consider:
For all departments of a company to take advantage of ITSM features, the tools must be intuitive and easy to use. For this, it is recommended to adopt a self-service portal that provides the necessary information to users.
To achieve the desired effect, IT Service Management (ITSM) must stimulate collaboration between different sectors. Thus, services will gain efficiency and agility.
Over time, a company grows, develops, and changes. Therefore, changes should also occur with your IT Service Management (ITSM). For that reason, its tools and software must be planned to adapt to future realities.
- Easy Setup and Activation
The first obstacle faced by those who need to adhere to software or tool is often a complex setup and activation mode. So, we also recommend the use of self-service portals, as well as efficient support.
This content has explained everything about IT Service Management (ITSM), its importance, functionality, and benefits. If you know someone also interested in the topic, please share our article.