Data breaches usually start with an employee mistake. Someone may click a dangerous link or send data via an unprotected connection. Soon, that error becomes a crisis. Websites fail, customer data spreads across the Dark Web, and regulators become involved.
Most of the time, all of this can be avoided. Proper cybersecurity training and cybersecurity tabletop exercise tools prepare staff to deal with threats.
The shocking thing is that almost one-third of US companies don’t provide cybersecurity training for employees. Worse still, over half of SMBs have no cybersecurity plan at all.
Don’t follow their example. Create a cybersecurity awareness training program that educates employees and puts security policies into action.
This article will explain how to raise cybersecurity awareness across your organization. So pull a chair up to the whiteboard as we deliver our 10-step cybersecurity training roadmap.
Key takeaways
-
Raising cybersecurity awareness is a vital business goal. Start by building a foundation. Create comprehensive cybersecurity policies and aim to ensure every employee is aware of their security role.
-
Cybersecurity training should focus on urgent data security threats. List relevant risks and train employees to identify and minimize them.
-
Device security awareness training is critical–especially in companies that rely on remote workers. Train employees to secure devices from digital and physical threats.
-
Educating employees on password security is a priority. Most cybersecurity breaches target weak credentials. Ensure staff know how to use strong passwords and access network assets safely.
-
Focus training on confidentiality and data protection. Define company data and instruct employees how to handle data securely. This includes regular backups, secure storage, and tools like Virtual Private Networks (VPNs).
-
Update training programs annually. Cybersecurity threats evolve, and training should keep pace. Refresh employee knowledge, taking advantage of free cybersecurity training when possible.

Step 1: Ensure employees understand their cybersecurity role
Cybersecurity training must include every employee, no matter how junior (or senior). Every network user must be aware of their security responsibilities. Communicate that one slip-up or policy breach can lead to data theft and regulatory action.
Guide employees on how to meet security requirements. For instance, you may require a VPN and Secure Remote Access for remote workers. Inform staff how to report security issues and reassure them. Reporting accidental policy breaches is a good thing–not something to fear.
Step 2: Create watertight data security policies
Cybersecurity training rests on comprehensive and easy-to-follow security policies. Create formal policies on handling confidential data, incident response, password management, remote work, and other relevant areas.
Security awareness training should cover employee knowledge of security policies. But one-time testing is not enough. Schedule regular meetings to discuss policies. Test knowledge annually to ensure staff remain aware of policy requirements.
Remember: policies are worthless if they are just documents. They need to be part of everyday professional practice. Make policies available in a central library for staff to access, and double-check the language to avoid technical jargon.
Step 3: Train employees to identify data security threats
Cybersecurity training can’t necessarily create an army of technical experts, but raising overall awareness is vital. Well-trained employees understand cyber threats and know how to prevent or mitigate them.
Train staff to identify email phishing, fake websites, insecure document transmission, and the risks of using unsecured public Wi-Fi. Make it clear that adding unauthorized software to the network is out of bounds.
Real-life examples help employees understand the nature of cyber threats. For example, sessions could include visual material on pop-ups, sudden device slow-downs, or unrequested browser extensions.
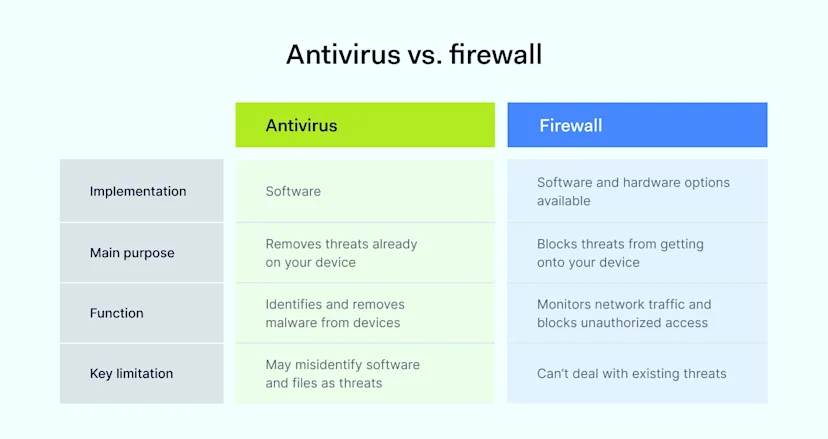
Above all, employee training must communicate the consequences of cyber-attacks and emphasize the need to follow security policies. By educating staff, you build a human firewall that adds an extra layer of defense against attackers.
This is a critical point and a key recommendation in Gartner’s 2024 Cybersecurity Trends Report. Human firewalls complement technology by changing employee behavior to mitigate potential threats. Properly-educated employees understand the threat reporting process. Training involves everyone in network protection efforts. A human firewall of engaged employees is much more likely to identify cybersecurity problems before a data breach occurs.

Step 4: Tighten up your password hygiene
Weak, rarely-changed passwords often expose businesses to information security threats. Robust password policies are the only reliable protection.
Don’t assume employees understand password risks. Two-thirds of Americans re-use passwords across accounts. Up to 80% of data breaches result from easily guessed or stolen passwords. People tend to be lazy about password hygiene. Don’t give them that option.
Instead, consider assigning passwords to employees and rotating these passwords regularly. Train staff and password managers to use strong passwords. Add multi-factor authentication to network logins and ensure employees know how to use it.
Step 5: Fine-tune device security
Training employees on cybersecurity must cover device security. Remote and off-site staff often rely on mobile devices. If a device contains sensitive data or allows network access, security policies apply.
Take action to minimize the risk of device loss. Mandate separate work and personal devices when cybersecurity risks are high. Include training modules explaining the difference between personal and business use.
Cybersecurity training should cover physically securing devices and protecting remote connections. It’s also wise to use remote monitoring tools and inform employees that their business accounts are transparent.
Step 6: Make sure employees backup critical data
Employees must back up company data, preferably every day. During employee training, make it clear that local backups are insufficient. Employee devices are vulnerable to theft or external attacks. Instead, use secure cloud storage systems to hold critical documents or customer data.
Step 7: Put in place authorization and access management systems
Authorization and authentication technology should always shield central data centers and cloud-hosted apps. However, it’s important to instruct employees in proper access security practices.
For instance, employees should never share work devices with colleagues or external individuals without authorization. Writing down passwords or authentication codes is out of the question. Adding new devices without agreement from network admins should also be prohibited.
Sometimes, employees complain about time-consuming authorization systems. Outflank those issues by explaining why MFA and VPNs are so important. When they know what is at stake, employees will quickly adopt secure access routines.
Step 8: Ensure secure web development and website updating
SQL and web application exploits are common security breach vectors, making secure coding a vital element of cybersecurity awareness training.
Deliver a secure training program to every staffer with access to web backends and coding tools. Even those without direct coding responsibilities can allow access to attackers. If employees update web assets in any way, they must do so safely.
Authorization is also important. Employees should know who is authorized to change web code or update websites and how to request permission to make changes.
Step 9: Make sure employees use email securely
Email is another critical weak point in business cybersecurity. Cybersecurity awareness training should help employees spot potential threats like phishing attempts and links to suspicious websites.
If necessary, test employee competence with phishing simulations that generate false social engineering emails. Simulations are great because they prove users can spot dangerous messages from authentic business communications.
Separate training applies if employees use email to transmit sensitive information. In these cases, ensure workers use VPNs and email encryption to safeguard data.
It should go without saying, but you should also test employees on what constitutes “sensitive data.” Many email users send confidential information via unsafe personal accounts, and that should end when they understand how you classify information.
Step 10: Update your training program regularly
Cybersecurity awareness tends to wane after a few months. Around 10% of employees say they remember all of their cybersecurity training. The other 90% have likely drifted back to unsafe passwords or unsecured remote connections.
Refreshing cyber security training is the only viable solution, but it can be challenging for businesses with a limited security awareness budget.
However, refreshing knowledge does not need to be expensive. Cybersecurity awareness training often costs virtually nothing if you know where to look.
Keep costs low by checking out free cybersecurity training listed at the National Institute for Science and Technology (NIST). For example:
-
The Cisco Networking Academy offers 6 hours of free cybersecurity training covering all core themes.
-
Evolve Academy provides free cybersecurity awareness training focused on practical technical skills.
-
Microsoft Technologies Training offers refresher courses to boost information security awareness when using Microsoft products.
These are just a few of many free or low-cost cybersecurity education options. You can also listen to podcasts about security awareness. Combine external courses with internal training to manage cybersecurity costs.
How can NordLayer help?
Companies are never alone when delivering cyber security awareness training, so don’t feel isolated. Instead, work with trusted partners like NordLayer to build internal knowledge and upskill your workforce.
NordLayer’s Learning Center is the perfect bookmark for trainers and employees. Use our accessible security checklists and in-depth explainers to understand concepts and tick off cybersecurity tasks. And stay on top of emerging threats thanks to cutting-edge intelligence.
It also helps to add video elements to training sessions. In that case, explore NordLayer’s YouTube channel. Our channel covers cybersecurity essentials like device posture security and secure remote access—supplementing tests and in-person training.
Whatever you do, don’t struggle alone. Share the cybersecurity challenge by enlisting expert assistance. If you’d like to find out more, get in touch with NordLayer today. We’ll help you find the right training and security solutions.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.






)
) As the digital world continues to expand and evolve, the need for secure authentication is more critical than ever. Enter passkeys – a modern solution for secure authentication that provides a safer and more convenient way to access apps and websites without ever having to remember or type out a password. Today, we’re looking into the world of passkeys, explaining what they are, how they work, and why they’re considered the future of authentication.
As the digital world continues to expand and evolve, the need for secure authentication is more critical than ever. Enter passkeys – a modern solution for secure authentication that provides a safer and more convenient way to access apps and websites without ever having to remember or type out a password. Today, we’re looking into the world of passkeys, explaining what they are, how they work, and why they’re considered the future of authentication.