Most people understand that routers can be hacked, but not everybody realizes just how damaging this kind of cyberattack can be. In this article, I will explain exactly how a hacker can target your router, what the consequences could be, and what you can do to protect yourself.

Most users underestimate the risk
No one wants to be hacked, but it’s easy to come up with excuses for not addressing router security issues — excuses like:
-
Hackers don’t want to hack me (aka: “I have nothing to hide” or “My data isn’t valuable to anyone”).
-
It’s too complicated to secure my router and configure it properly.
-
I assume that it’s secure by design (aka: “I trust my ISP to secure it”).
Do these excuses look reasonable to you? Maybe, but the truth is that most hackers would be happy to attack your router if it’s not properly protected, especially if they can do so quickly.
Securing your router is not technically complicated – you don’t need an IT specialist to keep your router safe anymore than you need an automobile engineer to drive your car. Making sure your router is protected should be a standard part of internet use.
Finally, you should not trust your internet service provider (ISP) to keep you safe. More often than not, its security measures are inadequate.
Types of vulnerabilities
Routers are commonly attacked using five main methods. In all the cases, an attacker gets root access (also known as administrative access) and gains full control of the device. The following list begins with the most unlikely and challenging hacks and ends with most common methods, which are also the easiest for the hacker. Each method also comes with an example of the tools and exploits a hacker could use to carry them out.
Physical (Hacking level: extremely difficult)
A physical attack requires the hacker to get physical access to your router. If they manage this, they can bypass security measures and get full administrator access. This process usually involves connecting the router to special hardware (in most cases, a serial console or JTAG).
While it may be a challenge for them to get close to your home router, hackers can use other ways to gain physical access to these devices. For example, they could target an outdoor wireless extender placed in the yard or a wireless router in a hotel that is used by guests.
-
Example: Almost any device with easy access to TTL or JTAG (for example, D-Link DIR-825AC) could be used to launch this hack. JTAG can also be used legitimately to unlock and customize a router.
Local authenticated (Hacking level: moderately difficult)
To perform a local authenticated attack, a hacker must connect to your LAN (local area network) or Wi-Fi. Usually this involves connecting a tiny device to a free network socket or cracking a weak wireless password.
The hacker must also know the default administrator’s password (or be able to brute force it). Collections of default router passwords are available to hackers online as well as tools that allow them to brute force weak passwords. Infecting a local connected device, like a laptop or smartphone, could give the hacker the same level of access to your local network.
-
Example: The Telia Technicolor Samba symlink exploit. This is also used by non-malicious technicians to jailbreak locked devices.
Local unauthenticated (Hacking level: challenging)
Like the local authenticated method, a local unauthenticated attack requires the hacker to connect to the LAN or Wi-Fi or to infect a local device. This time, however, the hacker does not need to know the administrator’s password.
Usually, local unauthenticated attacks involve exploiting some software vulnerability in your router’s firmware (for example, the buffer overflow in its web management function) or accessing misconfigured components (like a default telnet left without password protection).
-
Example: The Mikrotik RouterOS vulnerability CVE-2018-14847 and the Telia ADB hardcoded “tadmin” superuser method.
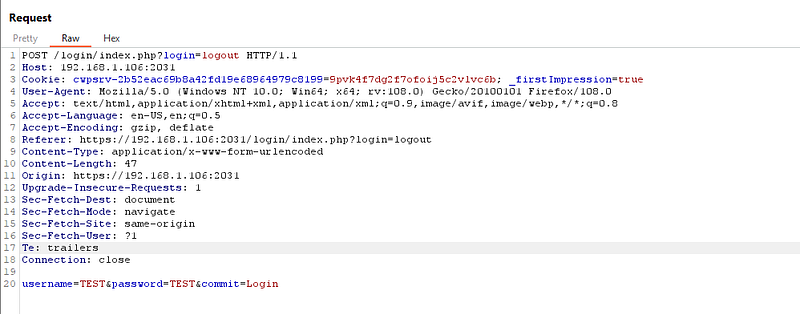
Remote authenticated (Hacking level: relatively easy)
Remote authenticated attacks are possible against certain routers via the internet, so the hacker doesn’t need to be close to you or join your LAN. They still need to know some default credentials to bypass the service password, but they can also brute force it if necessary.
-
Example: The Huawei LANSwitch model with a default Web UI open to the internet. This exploit was resolved in January 2023 but still acts as a good example of a remote authenticated threat — albeit one that is no longer active.
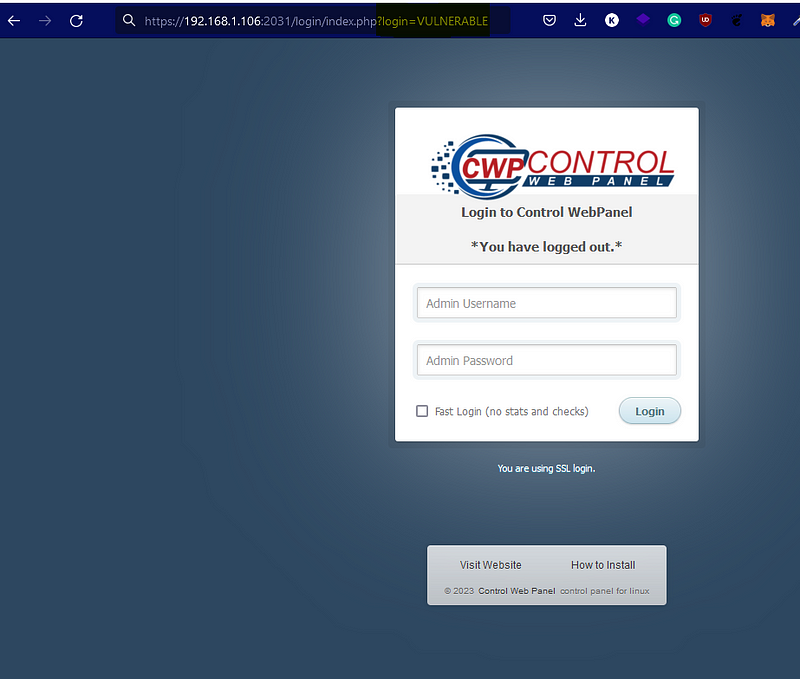
Remote unauthenticated (Hacking level: very easy)
Remote unauthenticated attacks are the worst-case scenario. Remote unauthenticated attacks can occur if anyone can access the router from the internet, without needing an administrator’s credentials.
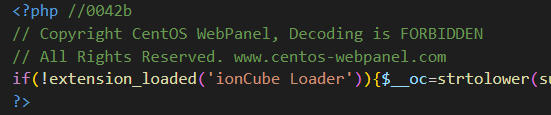
Usually, if a router can be accessed in this way, it is the result of the device coming with bad default configuration, a hidden backdoor, or a vulnerability in the software. In some nightmare scenarios, a router may end up with all three of these issues.
A router with these problems can be quickly scanned and exploited by thousands of automated bots or commercial providers (Shodan, for example). It takes between a few minutes and a few hours for the first bot to reach the device once it’s been connected to the internet. After scanning the router, a bot will be able identify the model and use the appropriate script to gain the access.
-
Example: Security flaws in multiple cheap routers sold on Amazon and Walmart. While these two examples are particularly egregious, many other routers may have the same issues.
What happens once you’ve been hacked?
Your router has been hacked. What happens now? After gaining root access, the attacker’s power over the device is unlimited. Here are some of the steps a hacker might take next:
-
Add a persistent backdoor to allow for remote device use or botnet inclusion.
-
View your unencrypted traffic in plain text (using tcpdump, for example).
-
Carry out deep packet inspection (DPI) on any encrypted traffic.
-
Redirect your traffic (for example, through DNS spoofing or by using iptables).
-
Launch social engineering attacks against you (for example, a hacker could redirect you to a fake website, pretending to be your online banking platform, where you might expose sensitive information).
-
Disconnect you from the internet and demand a ransom to restore access.
-
Make your router a proxy for other criminals to perform criminal activities from your IP address (potentially leaving you to convince the police that you weren’t the source of the criminal activity).
-
Hack your other devices (moving laterally) which were not accessible from the internet. If successful, this could allow the hacker to install ransomware or cryptominer malware on your other computers at home.
Still think it’s not worth your time to secure your router?
How to protect your router
If you think it’s time to start protecting your router and the devices connected to it, take the following steps.
-
Understand that your data is valuable. Even if you are not a celebrity or a high-profile politician, it’s still worth a hacker’s time to attack your router. Always see yourself as a potential target. You don’t have to be paranoid, but don’t ignore the risks.
-
Buy a user-friendly router that has good documentation and a clear user interface and that provides technical support and firmware updates. These routers may cost more, but security is a worthwhile investment.
-
Do not trust your ISP. ISPs tend to lower maintenance costs by saving on security. If possible, avoid using the router provided by your ISP, or at least unlock and take full control of it (change the default password, disable remote management, remove backdoors, and enable a firewall).
-
If possible, use WPA3, and protect yourself with a non-dictionary-based password containing at least ten characters. Never use WEP or unencrypted Wi-FI.
-
Use a VPN on your local devices (laptops, phones, TVs) to encrypt traffic.
You should now understand both the risks of an unsecured router and the actions you can take today to protect it. Stay safe!
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About Nord Security
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.