
Many organizations are now choosing to migrate to Microsoft 365 for a number of reasons including collaborative working options and Microsoft 365. Doing so has a number of advantages, but the movement of data can be difficult. A main consideration during the migration process can be maintaining data integrity whilst securing the data throughout the migration. Here are some migration security measures to consider to ensure a secure migration to Microsoft 365.
Encryption of Data
End-to-end encryption is the most secure way to communicate securely and with privacy online. The messages are encrypted at both ends of the conversation which prevents anybody in the middle from reading the private communications. Neither hackers nor unwanted third parties can access the encrypted data on the server.
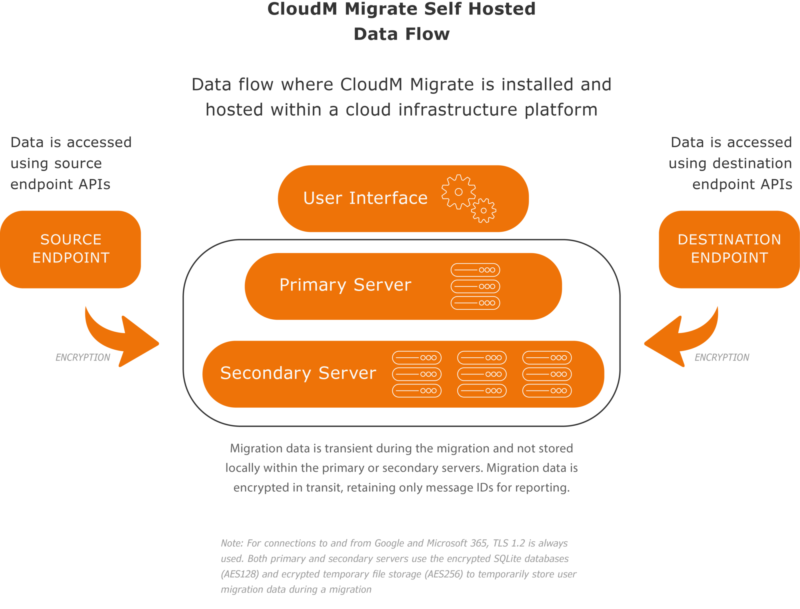
CloudM Migrate has end-to-end encryption between migration endpoints. The option to Self Host CloudM Migrate will completely isolate your migration data from your source environment to the destination cloud tenant.
Both primary and secondary servers use the following components to temporarily store migration data during a migration.
- Encrypted SQLite databases (AES256)
- Encrypted temporary file storage (AES256)
Where CloudM Migrate requires a username or password to interact with a system, and stores sensitive data like this, that data is stored encrypted within SQL Server (AES256). SQL Server 2019 Express is installed by default but you can specify your own SQL instance.
Know your source data
Before you start migrating data, you need to know exactly what it is you’re moving. Ensure you know the format of the data, where it is in the system, and if it does actually need to be migrated. Ensure the data is clean and any data that does not need to be kept, can be disposed of to reduce costs and decrease the chance of security risks.
Know your destination
Knowing everything about where the data is coming from is half the battle, the other half is knowing where it’s going.
Ensure that you know the exact destination your data will be going to. From simple things like username conflicts to license fees, the new system will have its own set of rules and regulations.
For example, if you are moving from a legacy endpoint to Microsoft 365, you need to know that all data will be working as expected and the appropriate security compliances are in place. It is also important to ensure everything will be compatible
Back up data
Before the migration begins, ensure all data has been backed up, especially the files you will be migrating. If there are any issues or problems during the migration, such as corrupt or missing files, then you can always restore from the backup.
Get us to help
Migrations are a specialized area, bringing with them their own challenges and solutions, and the right advice from experts like us can make things go a lot smoother. It’s important to understand your limitations, as mishandling a migration can have disastrous consequences.
We know how important security is during migrations. Move to the cloud with confidence with guaranteed data integrity with zero downtime for users with our secure cloud migration tool.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About CloudM
CloudM is an award-winning SaaS company whose humble beginnings in Manchester have grown into a global business in just a few short years.
Our team of tech-driven innovators have designed a SaaS data management platform for you to get the most from your digital workspace. Whether it’s Microsoft 365, Google Workspace or other SaaS applications, CloudM drives your business through a simple, easy-to-use interface, helping you to work smarter, not harder.
By automating time-consuming tasks like IT admin, onboarding & offboarding, archiving and migrations, the CloudM platform takes care of the day-to-day, allowing you to focus on the big picture.
With over 35,000 customers including the likes of Spotify, Netflix and Uber, our all-in-one platform is putting office life on auto-pilot, saving you time, stress and money.





 Cloud migrations are complex, always changing, and unique to every organization. You need the flexibility and control to tackle your project in the way that suits you best. This is why we have multiple migration deployment options to suit all businesses.
In this blog, we break down exactly what CloudM Migrate Self-Hosted is as well as explain security, endpoint, and installation information so you have more guidance when selecting a deployment option.
Definition
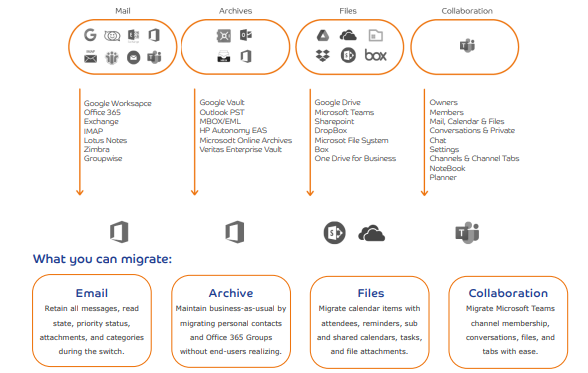
CloudM Migrate Self-Hosted is the downloadable version of CloudM Migrate, ideal for large and complex migrations. Migrate (Self-hosted) is highly configurable, allowing you to complete the most complex and demanding migrations seamlessly. Using our web interface, you can run a multitude of virtual machines to complete your self-hosted migration to Microsoft 365. Once set up in your environment, Migrate (Self-hosted) can securely migrate your mailboxes, files, SharePoint sites, mailbox archives, and more to Microsoft 365.
Security
If the organization has compliance obligations that do not permit you to use a third-party service, Migrate Self-Hosted is most appropriate. The software can be run behind your own organization’s firewall, critical data is kept internally and no other party has access to it.
CloudM Migrate already has end-to-end encryption between migration endpoints. The option to Self Host CloudM Migrate will completely isolate your migration data from your source environment to the destination cloud tenant.
Cloud migrations are complex, always changing, and unique to every organization. You need the flexibility and control to tackle your project in the way that suits you best. This is why we have multiple migration deployment options to suit all businesses.
In this blog, we break down exactly what CloudM Migrate Self-Hosted is as well as explain security, endpoint, and installation information so you have more guidance when selecting a deployment option.
Definition
CloudM Migrate Self-Hosted is the downloadable version of CloudM Migrate, ideal for large and complex migrations. Migrate (Self-hosted) is highly configurable, allowing you to complete the most complex and demanding migrations seamlessly. Using our web interface, you can run a multitude of virtual machines to complete your self-hosted migration to Microsoft 365. Once set up in your environment, Migrate (Self-hosted) can securely migrate your mailboxes, files, SharePoint sites, mailbox archives, and more to Microsoft 365.
Security
If the organization has compliance obligations that do not permit you to use a third-party service, Migrate Self-Hosted is most appropriate. The software can be run behind your own organization’s firewall, critical data is kept internally and no other party has access to it.
CloudM Migrate already has end-to-end encryption between migration endpoints. The option to Self Host CloudM Migrate will completely isolate your migration data from your source environment to the destination cloud tenant.
 CloudM has adopted the ISO 27001 standard as its framework and is externally certified. ISO27001 is one of the most popular information security standards in the world, focusing on protecting three key aspects of information; confidentiality, integrity, and availability.
Installation
Basic installation will install all components to a single machine and is suitable for performing migrations from a single server or as the main server in a multi-server migration.
If you have specialized requirements, have a pre-existing SQL Server instance you would like to use, or will be performing multi-server migrations using a server farm, you should also review the advanced installation documentation.
The following components makeup and are used by CloudM Migrate:
CloudM has adopted the ISO 27001 standard as its framework and is externally certified. ISO27001 is one of the most popular information security standards in the world, focusing on protecting three key aspects of information; confidentiality, integrity, and availability.
Installation
Basic installation will install all components to a single machine and is suitable for performing migrations from a single server or as the main server in a multi-server migration.
If you have specialized requirements, have a pre-existing SQL Server instance you would like to use, or will be performing multi-server migrations using a server farm, you should also review the advanced installation documentation.
The following components makeup and are used by CloudM Migrate:
 We’re here to help inform you about the most compatible deployment options for your business. Get in touch today to discuss your available options with one of our experienced solutions architects.
We’re here to help inform you about the most compatible deployment options for your business. Get in touch today to discuss your available options with one of our experienced solutions architects. 

 The New integration screen just got published. The screen’s rework includes much simpler and intuitive navigation between all integrations options. Check it out now!
The New integration screen just got published. The screen’s rework includes much simpler and intuitive navigation between all integrations options. Check it out now! 
