As new technologies emerge and cyber criminals become more capable, businesses face increasingly sophisticated threats that can bypass traditional security measures.
However, managed detection and response (MDR) has emerged as a comprehensive solution to address these challenges, from early threat detection to the immediate remediation of breaches.
MDR combines advanced technology with human expertise to provide round-the-clock monitoring, threat hunting, and incident response capabilities that help organizations stay one step ahead of cybercriminals.
In this article, we’ll discuss MDR, how it works, and why it’s becoming an essential component of modern cybersecurity strategies for businesses of all sizes.
So, what is MDR in cybersecurity, and how can it help keep your organization safe from cyber criminals and their attacks on your finances and vital information?
Key Takeaways
- MDR combines advanced tools, human expertise, and proactive measures to defend against sophisticated threats.
- Unlike EDR and XDR, MDR offers comprehensive coverage, including endpoint monitoring, network security, and threat intelligence.
- MDR’s proactive threat hunting and real-time responses minimize the impact of incidents like ransomware and data breaches.
- Customized reporting ensures actionable insights, aiding in compliance and improving overall security posture.
- For MSPs, MDR is a cost-effective way to offer premium cybersecurity solutions without significant upfront investments.
- A successful MDR strategy requires clear objectives, strong provider partnerships, and continuous performance optimization.
What Is MDR in Cyber Security?
Managed detection and response (MDR) is a cybersecurity service that delivers continuous monitoring, threat detection, and incident response through cutting-edge technology and expert human analysis.
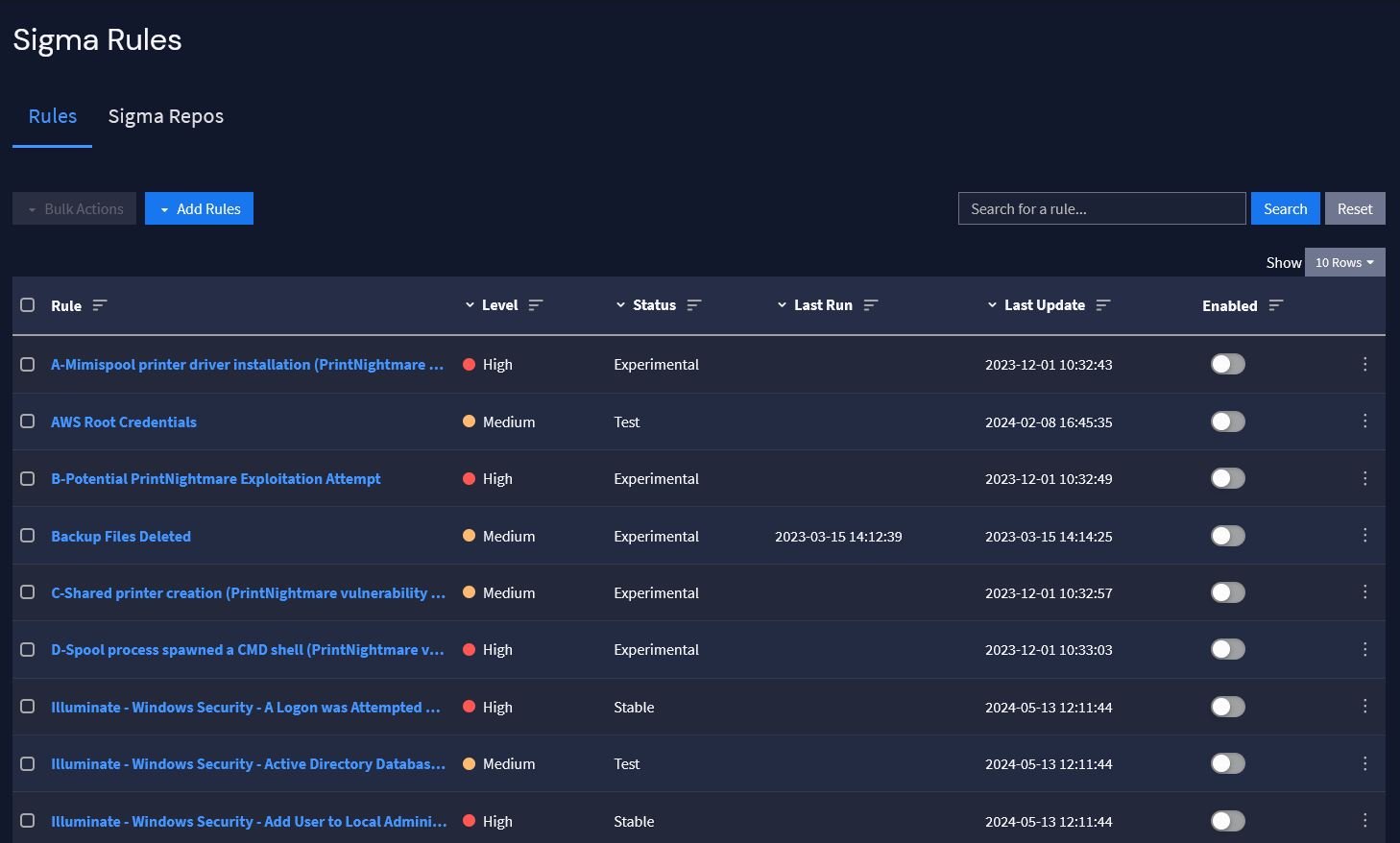
MDR providers use advanced tools, such as endpoint detection and response (EDR), security information and event management (SIEM), and threat intelligence, to identify potential security incidents in real time.
When a threat is detected, MDR analysts investigate the issue and take swift action to contain and remediate the problem, minimizing the impact on the organization.
This proactive approach to cybersecurity helps businesses detect and respond to threats that might otherwise go unnoticed, reducing the risk of data breaches, financial losses, and reputational damage.
Let’s move on and discuss how MDR works and its main components.
How Does MDR Work?
MDR providers employ a multifaceted approach to protecting your organization from cyberthreats. They combine advanced technologies, expert human analysis, and proven processes, such as 24/7 threat monitoring, proactive threat hunting, and incident remediation, to deliver comprehensive security coverage.
Here are the main components of a robust MDR system.
24/7 Threat Monitoring and Response
MDR services provide constant monitoring of endpoints, networks, and cloud environments to detect and address security incidents in real time, minimizing risks of disruption.
When alerts are triggered, analysts validate threats, assess their scope, and swiftly contain them using predefined protocols, ensuring minimal operational impact. This allows your business to remain focused on its goals while maintaining robust security.
Proactive Threat Hunting
MDR services go beyond reactive security by actively searching for hidden threats. Combining automation with expert analysis, they identify advanced persistent threats, insider risks, and zero-day attacks. By analyzing anomalies and patterns, MDR uncovers sophisticated attacks early, preventing breaches and costly disruptions.
Incident Response and Remediation
In the event of a security incident, MDR services execute predefined response protocols to rapidly contain threats, eliminate malicious elements, and restore systems.
They also perform root cause analysis, document findings, and implement measures to prevent future incidents, helping your organization recover quickly with a stronger security framework.
Utilizing Advanced Technologies
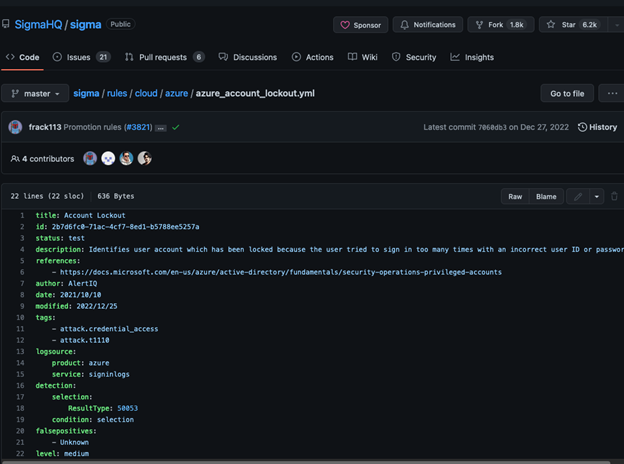
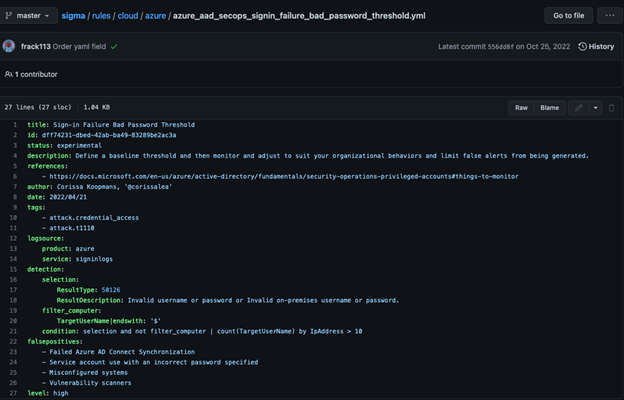
MDR providers use advanced tools like EDR, SIEM, UEBA, and threat intelligence platforms to enhance threat detection and response capabilities.
Endpoint Detection and Response (EDR)
EDR tools monitor endpoint activity in real time, detecting suspicious actions like unauthorized access or abnormal file executions. They enable quick root cause analysis and immediate actions, such as isolating compromised devices or reversing malicious changes.
Security Information and Event Management (SIEM)
SIEM systems collect and correlate log data from firewalls, servers, and applications to identify patterns and anomalies that may indicate security events. This helps analysts prioritize alerts and investigate threats efficiently.
User and Entity Behavior Analytics (UEBA)
UEBA tools use machine learning to analyze user and entity behavior. By establishing a baseline of normal activity, they flag unusual actions, such as privilege abuse or unexpected access to sensitive files, indicating potential threats.
Threat Intelligence Platforms
These platforms compile global data on emerging attack tactics and techniques. MDR teams use this intelligence to anticipate threats, refine defenses, and deliver insights tailored to your organization’s specific risks.
Customized Reports: Clear Insights and Recommendations
MDR services deliver customized reports offering detailed analyses, performance metrics, actionable recommendations, and compliance support.
Incident Analysis
Reports detail the timeline and resolution of incidents, explaining how threats were detected, tactics used, and mitigation steps taken.
Performance Metrics
Key metrics, like detection and response times, highlight trends and vulnerabilities, helping strengthen defenses.
Actionable Recommendations
Reports provide tailored advice, such as enhancing endpoint security or improving employee training, for focused improvements.
Compliance Support
Compliance-focused insights align your security measures with standards like GDPR, HIPAA, or PCI DSS, identifying gaps and remediation steps.
Example of MDR in Action
To better understand the value of MDR, let’s look at a real-world scenarios where an MDR service can make a significant difference, where an employee falls victim to a phishing scam.
Stopping a Ransomware Attack via a Phishing Email
An employee receives a phishing email disguised as an urgent message from a trusted vendor. The email includes a link that, when clicked, downloads ransomware onto the employee’s device. Within moments, the ransomware begins encrypting critical files on the system.
How can MDR help counteract this threat?
MDR in Action
- Detection: The MDR solution’s Endpoint Detection and Response (EDR) system identifies unusual file encryption activity, such as multiple file extensions being modified in rapid succession. This triggers an immediate alert.
- Isolation: The MDR team remotely isolates the infected device from the network to prevent the ransomware from spreading to other systems.
- Investigation: Analysts review the source of the attack, identifying the phishing email as the entry point. Threat intelligence data is cross-referenced to confirm the ransomware variant.
- Remediation: The MDR team works with the company to restore encrypted files using backups. They also verify that no additional payloads were deployed.
- Prevention: The MDR provider helps implement safeguards to prevent future attacks, including improved email filtering, user training, and multi-factor authentication (MFA).
Now that we know exactly how MDR works, let’s discuss its numerous benefits in greater detail.
Benefits of MDR for Businesses
MDR services offer a range of benefits for businesses looking to strengthen their cybersecurity posture and protect their valuable assets from increasingly sophisticated threats. These included greater protection against sophisticated threats, reduced burdens on IT teams, improved compliance, and greater cost-effectiveness.
Here are the many reasons why small and large businesses alike should consider a comprehensive MDR provider:
Enhanced Protection Against Sophisticated Threats
Modern threats often bypass traditional security measures, but MDR providers use advanced technologies, real-time intelligence, and skilled analysis to combat these evolving risks. They adapt to tactics like zero-day exploits and fileless malware, spotting anomalies and addressing threats proactively.
Combating Evolving Threats
MDR identifies complex attacks, such as phishing and advanced malware, using tools like user behavior analytics and machine learning to detect unusual activity. This dynamic approach ensures even hidden threats are neutralized before causing damage.
Minimizing Risks
This proactive approach significantly reduces the risk of data breaches, financial losses, and reputational damage.
With MDR, your organization is equipped to address threats before they escalate, providing peace of mind that your security measures are both effective and future-proof.
Reduced Burden on Internal IT Teams
Managing cybersecurity internally can overwhelm IT teams. MDR offloads this responsibility, letting teams focus on strategic projects and core functions.
However, a robust MDR provider can help reduce burdens on IT teams in the following ways:
Focus on Strategic Initiatives
By handling day-to-day security operations, MDR allows internal teams to prioritize productivity and innovation without being bogged down by routine cybersecurity demands.
Around-the-Clock Coverage
With 24/7 monitoring, MDR ensures threats are identified and addressed immediately, even during off-hours, reducing the chance of unnoticed incidents.
Cost-Effective Cybersecurity Solution
Building an in-house security operations center (SOC) is a significant investment, requiring advanced technology, skilled personnel, and ongoing maintenance. For many organizations, this approach is neither feasible nor cost-effective.
Accessible Advanced Security
MDR provides a more affordable alternative by giving you access to enterprise-grade security tools and expertise without the need for substantial upfront costs.
Instead of hiring and training a full-time security team, you gain access to seasoned analysts and advanced threat detection capabilities.
Flexible Pricing Models
MDR providers offer scalable pricing options tailored to your organization’s size, industry, and risk profile. This flexibility allows you to allocate resources more efficiently while maintaining robust security, making MDR a cost-effective choice for businesses of all sizes.
Improved Compliance and Reporting
Meeting regulatory requirements such as GDPR, HIPAA, and PCI DSS is a critical aspect of modern cybersecurity. Non-compliance can lead to severe financial penalties and legal repercussions.
Here’s how MDR can help avoid those repercussions:
Ensuring Regulatory Compliance
MDR services help you stay compliant by providing comprehensive monitoring, incident response, and reporting solutions that align with industry standards.
They ensure your organization is prepared for audits, supplying the necessary documentation and evidence to demonstrate adherence to regulations.
Visibility Through Reporting
Regular reports and analytics provided by MDR providers offer clear insights into your organization’s security posture.
These reports highlight key metrics, incident trends, and areas for improvement, empowering you to make informed decisions about future cybersecurity investments.
Real-World Example
Consider a healthcare organization subject to HIPAA regulations. An MDR provider would monitor protected health information (PHI) for unauthorized access, respond to potential breaches, and generate detailed audit logs required for compliance, all while ensuring minimal disruption to daily operations.
Start learning how Guardz can help MSPs take advantage of these benefits and achieve success.
Now that we’ve covered the basics, avoiding confusion and distinguishing between MDR, EDR, and XDR is important.
MDR vs EDR vs XDR: What’s the Difference?
While MDR, EDR, and XDR all aim to protect organizations from cyber threats, each takes a different approach. Here’s a breakdown of their features and distinctions:
Endpoint Detection and Response (EDR)
EDR focuses on securing endpoints like laptops, desktops, and servers, which are common entry points for cyberattacks.
It continuously collects and analyzes endpoint data, such as file changes and user activity, to detect malware, unauthorized access, and unusual behavior.
When threats are detected, EDR can automatically isolate affected devices to prevent spread and minimize damage. It also includes investigation tools for tracing attack origins and identifying vulnerabilities.
However, EDR’s scope is limited to endpoints, leaving other IT areas like networks and cloud services unmonitored.
Managing EDR requires in-house teams to interpret and act on alerts, which can be resource-intensive for smaller organizations.
Extended Detection and Response (XDR)
XDR builds on EDR by integrating security data from endpoints, networks, cloud applications, and email systems. This holistic approach provides a unified view of security events, enabling organizations to detect and respond to threats spanning multiple IT layers.
Advanced analytics and machine learning identify patterns of multi-stage attacks, such as phishing campaigns that compromise credentials and exploit cloud services.
XDR’s ability to correlate data and automate responses ensures coordinated actions, such as isolating endpoints, blocking malicious traffic, and flagging suspicious cloud activity.
While XDR offers a more comprehensive solution than EDR, it requires a strong security infrastructure and skilled personnel to manage, which can be a challenge for smaller organizations.
Managed Detection and Response (MDR)
MDR combines the capabilities of EDR and XDR with human expertise to provide a fully managed solution. It offers 24/7 monitoring, threat hunting, and incident response across all IT systems.
By using advanced tools and skilled analysts, MDR addresses sophisticated threats while reducing the burden on internal teams. MDR providers handle the complexities of security management, making it accessible to organizations of all sizes.
Unlike EDR and XDR, which rely on in-house resources, MDR delivers a complete solution, ensuring both robust protection and ease of use.
Main Differences Between EDR, XDR, and MDR
Based on the above, we can assume that while both EDR and XDR have their advantages, MDR is the most comprehensive solution. Let’s compare the three based on several key factors, such as scope of coverage, automation, detection capabilities, and response mechanisms.
Here’s why MDR stands out.
Scope of Coverage
EDR focuses on securing individual endpoints like laptops and servers by monitoring activity and detecting endpoint-specific threats. However, it does not address the broader IT infrastructure.
XDR expands coverage by integrating data from various layers of the IT environment, such as networks, cloud systems, and email platforms, providing a unified view for detection and response.
MDR combines EDR and XDR capabilities with human expertise, offering 24/7 monitoring, threat hunting, and incident response across the entire IT ecosystem.
Role of Automation vs. Human Expertise
EDR relies on automated tools for threat detection and response, requiring in-house teams to interpret alerts and take action.
XDR enhances this with advanced analytics and machine learning, reducing false positives but still depending on internal staff for management.
MDR adds skilled analysts who monitor, investigate, and respond to threats, reducing the burden on internal teams while delivering a proactive, hands-on approach to security.
Detection Capabilities
EDR is effective at identifying threats targeting individual endpoints but lacks broader IT visibility.
XDR correlates data across endpoints, networks, and cloud systems, enabling detection of multi-stage attacks.
MDR combines the strengths of EDR and XDR with real-time intelligence and threat hunting, identifying advanced threats that may evade automated systems.
Response Mechanisms
EDR focuses on endpoint-specific responses, such as isolating infected devices. XDR coordinates responses across IT layers, blocking malicious activity at multiple points.
MDR goes further, managing incidents from detection to remediation and providing post-incident guidance for improved security.
Management Requirements
EDR demands dedicated internal teams, which can strain resources, while XDR centralizes
data for easier management but still requires in-house expertise.
MDR outsources monitoring and response to an expert team, making it ideal for organizations seeking robust security without extensive internal resources.
Key Considerations When Choosing an MDR Provider
Selecting the right Managed Detection and Response (MDR) provider is critical in enhancing your organization’s cybersecurity. Your chosen provider should align with your needs, goals, and operational requirements.
Below are the key factors to evaluate when assessing potential MDR partners.
Expertise and Industry Experience
An MDR provider should have a proven record of mitigating advanced threats and understanding the latest tactics used by attackers.
Industry-specific experience is vital, as providers familiar with your sector can address unique challenges and compliance needs. For example, a healthcare organization should seek providers with expertise in HIPAA compliance and securing patient data.
Comprehensive and Proactive Service Offerings
Choose a provider offering more than basic threat detection. Look for services like monitoring, investigation, response, and remediation.
Proactive measures, such as threat hunting and vulnerability assessments, are essential for identifying risks early. Value-added services like employee training and incident response exercises enhance your overall security posture, ensuring your organization is prepared for future threats.
Customization and Scalability
An effective MDR provider tailors solutions to fit your risk profile and business goals. As your organization grows or threats evolve, their services should scale accordingly.
Flexibility in customizing communication protocols, escalation processes, and workflows ensures seamless integration with your internal teams.
Integration with Your Existing Security Stack
Your MDR provider should integrate smoothly with tools like EDR, SIEM, firewalls, and cloud platforms. Effective integration aggregates data for a unified view, improving detection and response times while preserving your existing security investments.
Providers experienced with your tools can ensure a seamless transition without disrupting your current systems.
Implementing an Effective MDR Strategy
A managed detection and response (MDR) strategy requires careful planning, ongoing collaboration, and adaptability. When executed effectively, it can enhance your organization’s cybersecurity posture, improve threat detection, and reduce risks. Here are the essential steps to building a successful MDR strategy:
Defining Clear Objectives
Set measurable goals aligned with your cybersecurity priorities, such as improving threat detection, reducing response times, or meeting compliance standards like GDPR or HIPAA. Involve key stakeholders across IT, security, legal, and executive teams to ensure alignment, and use these objectives as benchmarks for tracking success.
Establishing a Strong Partnership With Your MDR Provider
Treat your MDR provider as an extension of your security team by fostering open communication and collaboration. Define roles, establish escalation protocols, and develop tailored playbooks. Regularly review service level agreements (SLAs) and refine processes based on feedback and emerging risks, such as phishing or other recurring threats.
Continuously Measuring and Optimizing Performance
Track key performance indicators (KPIs) like mean time to detect (MTTD) and mean time to respond (MTTR) to evaluate the strategy’s effectiveness. Use data to identify trends, address gaps, and refine protocols. For example, high false-positive rates may require better tuning of detection tools.
Adapting to Evolving Threats
Stay ahead of emerging threats by collaborating with your MDR provider to update detection and response mechanisms. For example, new ransomware tactics may require revised playbooks, while integrating new technologies like IoT or cloud platforms demands expanded security measures.
Is Managed Detection and Response Ideal for MSPs?
As a Managed Service Provider (MSP), improving your cybersecurity offerings is essential to staying competitive and delivering value to your clients.
Managed detection and response (MDR) services can be a game-changer, enabling you to differentiate your business, attract new customers, and better protect your clients.
However, determining whether MDR is worthwhile requires thoroughly assessing its alignment with your business goals, target market, and return on investment (ROI).
Here’s how to decide if MDR is right for you as an MSP:
Evaluating Client Needs
Understanding your clients’ cybersecurity needs is crucial. Small to medium-sized businesses (SMBs) often lack the in-house resources or expertise to handle advanced cybersecurity threats.
MDR offers an outsourced, comprehensive solution for these clients that can bridge critical security gaps.
In contrast, larger enterprises with established security teams may not find the same value in MDR, as they often prefer to maintain control over their operations and have the resources to build and manage their own detection and response capabilities.
Before investing, analyze whether your typical client base would benefit significantly from MDR services.
Weighing Costs and Investments
Delivering MDR services requires significant investments in advanced security technologies, skilled analysts, and robust processes for threat monitoring, investigation, and response.
These costs can be substantial, so evaluating whether the potential revenue and margins justify the expense is essential.
To reduce upfront costs and accelerate your time to market, consider partnering with an established MDR provider rather than building the service in-house.
With 77% of MSPs reporting challenges in managing multiple cybersecurity solutions, leveraging an external provider’s infrastructure and expertise can help streamline operations and ensure effective service delivery.
Aligning MDR With Your Business Goals
For MDR to be a successful addition to your portfolio, it must align with your overall service offerings and value proposition.
Consider how MDR complements your existing cybersecurity services and whether it addresses specific pain points for your target customers.
Assess your area’s market demand for MDR services and your clients’ willingness to pay a premium for advanced cybersecurity capabilities.
Moreover, consider how to differentiate your MDR offering from competitors to provide unique value.
Key Questions to Consider
Before committing to MDR, ask yourself the following questions:
- What are the primary cybersecurity challenges faced by your clients?
- How does MDR fit within your current service portfolio?
- Is there sufficient demand for MDR services, and will clients pay for it?
- What are the costs of implementing and maintaining MDR, and how can you manage them effectively?
- How will you position and differentiate your MDR offering in a competitive market?
Final Thoughts on the Role of MDR in Cybersecurity
Managed detection and response (MDR) represents an essential evolution in cybersecurity. By combining advanced technologies, expert human analysis, and proactive strategies, MDR allows businesses to detect and respond to sophisticated threats with precision and speed.
Its value extends beyond traditional tools like EDR and XDR, delivering robust security coverage and tailored solutions that align with organizational goals and unique security needs.
For MSPs, MDR presents an opportunity to enhance service portfolios, address client pain points, and differentiate in a competitive market. However, its implementation must be guided by a clear understanding of client needs, cost considerations, and alignment with business objectives.
Whether it’s stopping ransomware in its tracks, mitigating zero-day vulnerabilities, or helping small businesses navigate compliance complexities, MDR is more than a service—it’s a partnership that strengthens security posture and builds resilience against an ever-evolving threat landscape.
By carefully evaluating providers, aligning MDR with operational goals, and continually adapting strategies, businesses and MSPs can leverage MDR to face modern cybersecurity challenges confidently.
Book a demo with Guardz to see how MDR can benefit you as an MSP.
Frequently Asked Questions
How Does MDR Differ From EDR and XDR?
MDR integrates the capabilities of EDR and XDR while adding human expertise and proactive threat hunting. Unlike EDR or XDR, which rely on internal teams for management, MDR includes 24/7 monitoring and expert-led incident response, making it a more comprehensive solution.
Is MDR Suitable for Small Businesses With Limited IT Resources?
Yes, MDR is particularly beneficial for small businesses that lack in-house cybersecurity expertise. It provides cost-effective, enterprise-grade security services, including continuous monitoring, rapid incident response, and compliance support, without the need for a dedicated security team.
Can MDR Help With Regulatory Compliance?
Absolutely. MDR services often include compliance-focused reporting and monitoring, ensuring alignment with regulations such as GDPR, HIPAA, or PCI DSS. Providers can help prepare audit-ready documentation and address vulnerabilities that could lead to non-compliance.
What Is the ROI of Investing in MDR for MSPs?
For MSPs, MDR offers significant ROI by enhancing service offerings and addressing a growing demand for advanced cybersecurity solutions. It reduces the need for costly in-house investments while enabling MSPs to attract new clients and retain existing ones with comprehensive security services.
About Guardz
Guardz is on a mission to create a safer digital world by empowering Managed Service Providers (MSPs). Their goal is to proactively secure and insure Small and Medium Enterprises (SMEs) against ever-evolving threats while simultaneously creating new revenue streams, all on one unified platform.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.