Cybersecurity roles and responsibilities are in a constant state of flux. Just as the defenders adapt, so do the adversaries. Enter the latest evolution in the cybersecurity workforce: the Zero Trust Program Manager. If you’ve been in the cybersecurity field for more than a hot minute, you’re likely aware that “Zero Trust” has become a buzzword so pervasive that it’s now almost as ubiquitous as the phrase “we take your security seriously” in every corporate breach apology letter. But unlike the latter, Zero Trust is more than just lip service. It’s a paradigm shift in how we think about securing our digital environments. And it’s precisely this shift that has given rise to the need for a dedicated role to manage it.
What Exactly is a Zero Trust Program Manager?
At its core, the Zero Trust Program Manager (ZTPM) is the strategic leader responsible for implementing and overseeing an organization’s Zero Trust architecture. This role isn’t just about managing technology; it’s about orchestrating a cultural shift in how an organization approaches security. The ZTPM is tasked with ensuring that no entity—be it user, device, or application—is inherently trusted, whether inside or outside the organization’s perimeter. Instead, everything and everyone must be continuously authenticated and authorized.
This role is a blend of project management, cybersecurity expertise, and change management. The ZTPM must work closely with various stakeholders across the organization, from IT and security teams to business leaders, to ensure that the principles of Zero Trust are understood, embraced, and effectively implemented. They are the evangelist, the educator, and the enforcer of this new security mindset.
Why Does This Role Exist Today?
The rise of the ZTPM is not just a random blip on the cybersecurity radar; it’s a direct response to the changing threat landscape and the realization that traditional perimeter-based security models are no longer sufficient. The days when securing the castle walls could keep the bad guys out are long gone—primarily because the castle doesn’t even have walls anymore. Today, organizations operate in a borderless environment where users and data move fluidly across cloud services, mobile devices, and remote locations. The traditional model of “trust but verify” has been replaced with “never trust, always verify.”
Moreover, the acceleration of digital transformation, spurred on by global events like the COVID-19 pandemic, has further blurred the lines between internal and external networks. As organizations rapidly adopted remote work models and cloud services, the attack surface expanded exponentially. In this new reality, the concept of a trusted internal network is not just outdated; it’s downright dangerous.
Enter Zero Trust—a model that doesn’t assume that anything or anyone is trustworthy just because they’re inside the network. Every request, every access attempt, every interaction is scrutinized. This approach requires a fundamental shift in how security policies are designed, enforced, and managed. And that’s where the ZTPM comes in. Their role is to steer this transformation, ensuring that Zero Trust principles are not just a checkbox on a compliance form, but a living, breathing part of the organization’s security fabric.
Scope of Responsibilities
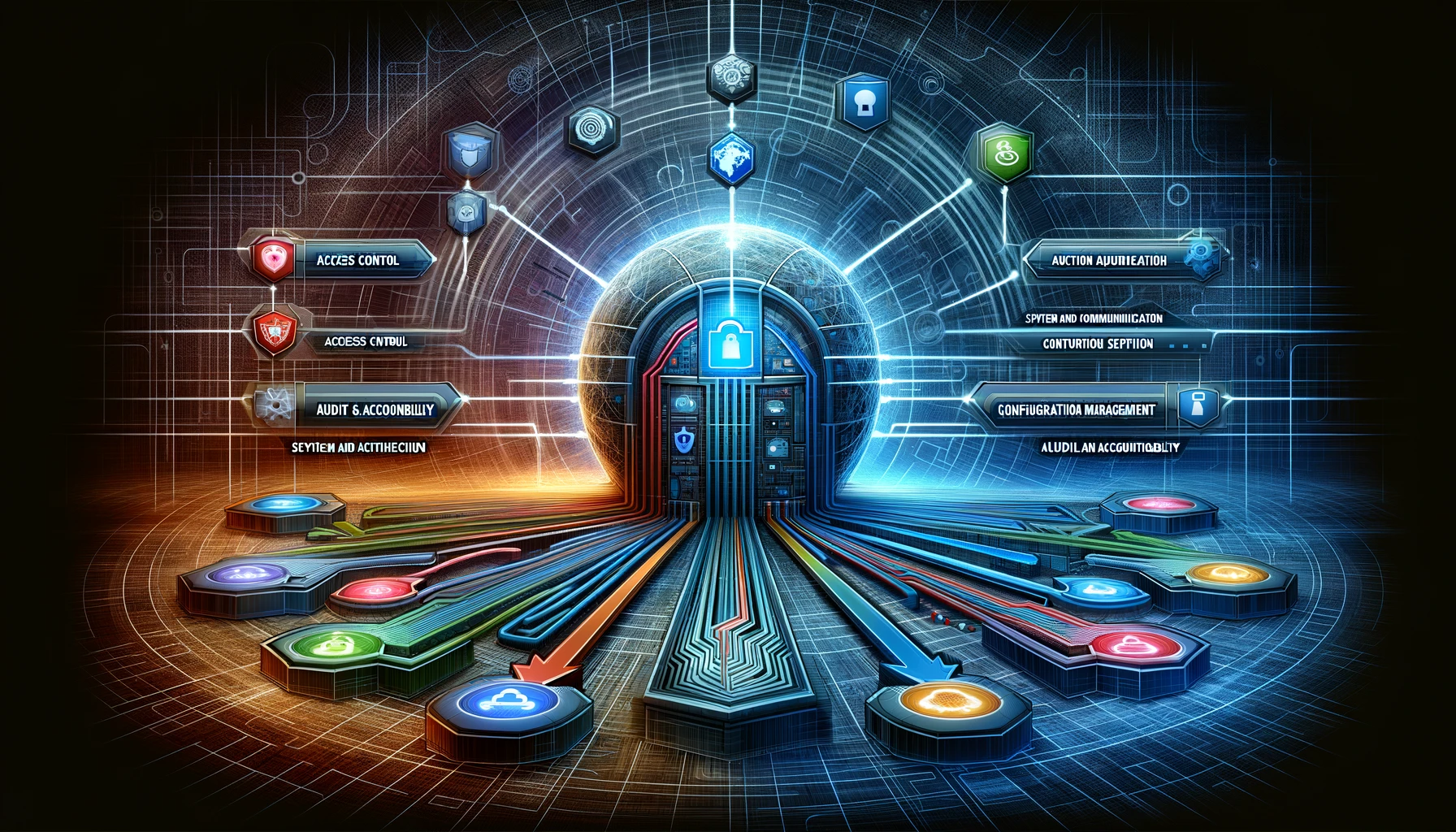
The responsibilities of a Zero Trust Program Manager are as wide-ranging as they are critical. Here’s a closer look at what this role entails:
- Strategy Development and Implementation: The ZTPM is responsible for developing a comprehensive Zero Trust strategy that aligns with the organization’s business objectives. This includes defining the scope, setting milestones, and ensuring that all security policies and technologies are aligned with Zero Trust principles.
- Cross-Functional Collaboration: Implementing Zero Trust is not a one-department job. The ZTPM must work closely with IT, security, compliance, and business units to ensure that the Zero Trust framework is understood and adopted across the organization. This includes leading workshops, training sessions, and regular check-ins to ensure alignment.
- Technology Oversight: While the ZTPM isn’t necessarily the person configuring firewalls or deploying MFA solutions, they are responsible for overseeing the technology stack that supports the Zero Trust model. This includes evaluating and selecting the right tools, ensuring they are properly integrated, and monitoring their effectiveness.
- Change Management: Moving to a Zero Trust model is as much about changing mindsets as it is about changing technology. The ZTPM must manage the human side of this transformation, addressing resistance, ensuring proper training, and fostering a culture that supports continuous verification.
- Risk Management and Compliance: The ZTPM plays a crucial role in identifying and mitigating risks associated with the transition to Zero Trust. They must ensure that the organization remains compliant with relevant regulations and industry standards while adopting this new security model.
- Continuous Improvement: Zero Trust is not a set-it-and-forget-it approach. The ZTPM is responsible for continuously assessing the effectiveness of the Zero Trust framework, making adjustments as needed, and staying ahead of emerging threats.
Qualifications and Skills
Given the breadth of responsibilities, the ideal ZTPM is a cybersecurity Renaissance person—a Jack or Jill of many trades, with a deep understanding of security principles and a knack for project management. Key qualifications might include:
- Experience: A strong background in cybersecurity, with experience in implementing security frameworks and leading cross-functional teams.
- Certifications: Relevant certifications such as CISSP, CISM, or specific Zero Trust certifications can be a strong indicator of expertise.
- Communication Skills: The ability to articulate complex security concepts to non-technical stakeholders is crucial.
- Leadership: Proven leadership skills, particularly in driving organizational change, are essential.
- Strategic Thinking: The ZTPM must be able to see the big picture, aligning security initiatives with broader business goals.
Zero Trust, the ZTPM & Network Access Control (NAC)
One of the critical areas where the Zero Trust Program Manager (ZTPM) must exert influence is in the realm of Network Access Control (NAC). NAC plays a pivotal role in the enforcement of Zero Trust principles, acting as one of the frontline defenses against unauthorized access. In the context of Zero Trust, NAC is not merely a gatekeeper that decides who gets in; it is a dynamic system that continuously assesses and verifies the trustworthiness of every device and user attempting to access the network.
The ZTPM must work closely with network administrators and security teams to ensure that NAC solutions are tightly integrated into the broader Zero Trust architecture. This involves configuring NAC policies to align with the Zero Trust mantra of “never trust, always verify.” For example, NAC policies may need to be updated to enforce strict access controls based on user roles, device health, and contextual factors such as the location and behavior of the device. The ZTPM oversees this integration, ensuring that the NAC system not only blocks unauthorized devices but also actively participates in the continuous monitoring and assessment of devices already within the network.
Furthermore, the ZTPM must consider how NAC fits into the overall user experience. While security is paramount, the role requires balancing stringent access controls with the need for operational efficiency. Implementing NAC in a Zero Trust environment is not just about adding layers of security; it’s about creating an adaptive, intelligent system that can respond to threats in real-time without unnecessarily hindering legitimate business activities. This means the ZTPM must ensure that NAC is fine-tuned to minimize disruptions while still providing robust protection, making it an essential tool in the Zero Trust toolkit.
By effectively managing NAC within a Zero Trust framework, the ZTPM helps to create a more resilient and responsive security posture, one where access is always under scrutiny and never taken for granted.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About Portnox
Portnox provides simple-to-deploy, operate and maintain network access control, security and visibility solutions. Portnox software can be deployed on-premises, as a cloud-delivered service, or in hybrid mode. It is agentless and vendor-agnostic, allowing organizations to maximize their existing network and cybersecurity investments. Hundreds of enterprises around the world rely on Portnox for network visibility, cybersecurity policy enforcement and regulatory compliance. The company has been recognized for its innovations by Info Security Products Guide, Cyber Security Excellence Awards, IoT Innovator Awards, Computing Security Awards, Best of Interop ITX and Cyber Defense Magazine. Portnox has offices in the U.S., Europe and Asia. For information visit http://www.portnox.com, and follow us on Twitter and LinkedIn.。