Compliance made easy: Introducing Vanta integration
Achieving and maintaining prestigious security compliance certificates like SOC2, ISO 270001, or HIPAA is not an easy venture. The company must put forth a tremendous amount of effort and resources into preparing for compliance audits and assessments. Luckily, Vanta, the leading trust management platform, makes collecting the proof required for certifications much easier. And now, with its integration with NordPass, this strenuous process becomes even more automated, faster, and less demanding for the company.
As with all great partnerships — the integration of our business password manager with a popular trust management platform means much more than just a sum of features. Read on and discover how your business can benefit from integrating NordPass and Vanta.
Customers choose companies they trust
According to The State of Trust Report 2023, 70% of business and IT leaders say that better security and compliance strategy builds consumer trust, positively affecting the business. Cybersecurity gives the company a real competitive advantage during sales conversations, especially if it is audited and approved by external certifications.
The problem is that security and compliance specialists often hit the wall because they lack the stuff and budget required to achieve or maintain such certificates. That’s where Vanta, the leading trust management solution, comes in handy. It automates much of the work involved in preparing for audits and assessments, as well as maintaining already gained certificates. In turn, Vanta can save the company lots of time, effort, and money.
Vanta, combined with NordPass, can transform your entire experience with the certification process. Now, let’s discuss the integration, its benefits, and how easy it is to implement.
Benefits of integrating NordPass with Vanta
Many of our clients requested the Vanta integration feature. We are very happy to answer the calls as the update holds many benefits for organizations. Let’s take a look:
Automating SOC2, ISO 270001, and HIPAA certification processes
Reliable security and compliance certificates require collecting vast amounts of information and proof. If this is done manually, it puts tremendous pressure on the company’s resources. Integrating NordPass with Vanta provides organizations with real-time password management data and points directly to areas in need of improvement.
Prioritizing gap resolution over data collection
Streamlined, automated data collection allows employees to focus on what’s the most important — identified risks and issues related to password security and/or compliance. No more precious company time gets spent on gathering data manually and fixing errors, the natural consequence of handling such tasks by hand. Therefore, prioritizing gap resolution saves money but also enables organizations to optimize employees’ time.
Strengthening the company’s overall security and compliance
The unified approach to cybersecurity streamlines business password management and compliance workflows. It enforces consistent password policies, fortifies access control, and ensures you meet the audit requirements. Vanta and NordPass integration results in a more secure and compliant organizational environment, safeguarding your company from cyber threats.
Effortless API integration
We put a lot of effort into making the Vanta and NordPass integration as user-friendly as possible. In fact, you don’t even need a tech person to achieve it.
All you need to do is go to the Integrations tab in your NordPass Admin Panel and choose to connect with Vanta. You’ll be asked to reenter the Master Password to your administrative business account and confirm the integration. The entire process is as straightforward and uncomplicated as setting up an average application for private use.
How else can we make your work easier?
With Vanta’s expertise in trust management and NordPass’ robust password management capabilities, achieving and maintaining prestigious security certificates like SOC2, ISO 270001, and HIPAA has never been easier. Effortless API integration makes a unified approach to cybersecurity and compliance accessible to both tech and non-tech users. Go on, say goodbye to manual processes, and embrace your company’s new security posture.
At NordPass, we’re dedicated to providing organizations with solutions that boost productivity and simplify day-to-day security operations. In the near future, expect more innovative features to enhance current functionalities and address ever-changing security challenges. Keep an eye out for the upcoming updates!
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordPass
NordPass is developed by Nord Security, a company leading the global market of cybersecurity products.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.


Third-party reviews: Perimeter 81 competitors and alternatives
We know how important it is to make the right decision when it comes to selecting cybersecurity tools and solutions. This blog article will have hands-on information about how secure network access solutions and VPNs compare to the most commonly chosen alternatives in the market.
In this article, we will overview Perimeter 81 competitors and alternatives.
Disclaimer: This article is based entirely on third-party reviews and open-source online information accessed between April 15 and 22, 2024. NordLayer is not responsible for data accuracy, as competitor information is subject to change. The competitor information was gathered through a combination of manual research and data extraction. Data points include feature comparisons and product analysis.
Overview of Perimeter 81
Perimeter 81’s mission is to simplify secure network, cloud, and application access for the modern and mobile workforce. It achieves this by transforming traditional network security technology into one unified Zero Trust Network as a Service derived from a SASE framework.
Perimeter 81 capabilities
Smooth integration and deployment
Good customer service
Satisfactory speed and performance
Offers completely audited access
Perimeter 81 benefits
According to the Perimeter 81 website, the flexible and straightforward solution is their strength.
Easy building and management without lengthy setups and manual configurations.
Fast and flexible solution deployment with a centralized dashboard for resource management.
Perimeter 81 limitations
Perimeter’s weaknesses, according to the mentioned review platforms, are:
Premium plans are required to access advanced features
Customer support has access to substantial information
A relatively small number of countries to select from
Pricing is on the higher end
Let’s overview the competition of Perimeter 81 available in the market.
Disclaimer: Product review is based on information provided on VPN review sites such as Gartner, Capterra, and Cybernews and assessed customer feedback shared on these platforms, accessed on April 22, 2024.
NordLayer
NordLayer is a multi-layered business cybersecurity tool enabling all ways of working. It is a secure remote access solution from the Nord Security powerhouse and consumer product NordVPN.
The baseline of NordLayer’s development focus is defined by Secure Access Service Edge (SASE) and Zero Trust frameworks. The solution introduces SaaS security features for the internet, resource, and network access control.
NordLayer capabilities
Seamless integration with existing infrastructure and intuitive deployment of a cloud-based platform
Scalable with an unlimited number of users and adaptable to various business needs
High-performance service and 24/7 tech-savvy support for all plans
Strong product capabilities and comprehensive cloud-native feature set
In-house developed NordLynx VPN protocol based on Wireguard® for unprecedented performance and speed.
NordLayer benefits
According to the NordLayer website, the solution’s strengths are in its simplicity, security capabilities, and performance.
Easy to start, scale, and combine, as the solution requires no hardware and is simple to deploy, set up, and maintain within minutes. It integrates seamlessly with existing infrastructures and has a user-friendly Control Panel.
Custom and unique security solutions like NordLayer, the fastest unique VPN protocol, or Browser Extension, a lightweight solution for traffic encryption on a browser level only.
Compatibility with popular security providers facilitates the smooth integration of existing Identity & Access Management (IAM) and authentication systems and tools for a quick setup.
NordLayer offers a 14-day money-back guarantee.
NordLayer use cases
NordLayer offers a hassle-free cybersecurity solution tailored for businesses. It enables organizations to create secure remote connections to the internet, their company network, and cloud-based resources, facilitating compliance for any way of working.
Secure internet access: Protect traveling employees by securing remote access through public Wi-Fi. This prevents threats while browsing the internet, allows access to geo-specific content, and ensures the masking of IP addresses for enhanced privacy and security.
Network & resource access management: Establish segmented access to company resources, control access by selecting specific content categories and applications, create connections between remote devices, and enable remote access to hybrid resources. This enhances overall operational flexibility and security.
Achieving compliance: Continuously monitor VPN activity within your organization, maintain an overview of devices present in the network, manage identity and remote access for both users and applications, and ensure the encryption of data transmissions originating from untrusted networks to bolster overall cybersecurity.
NordLayer limitations
No API access is available
Does not integrate with SIEM solutions
Minimum member license quota
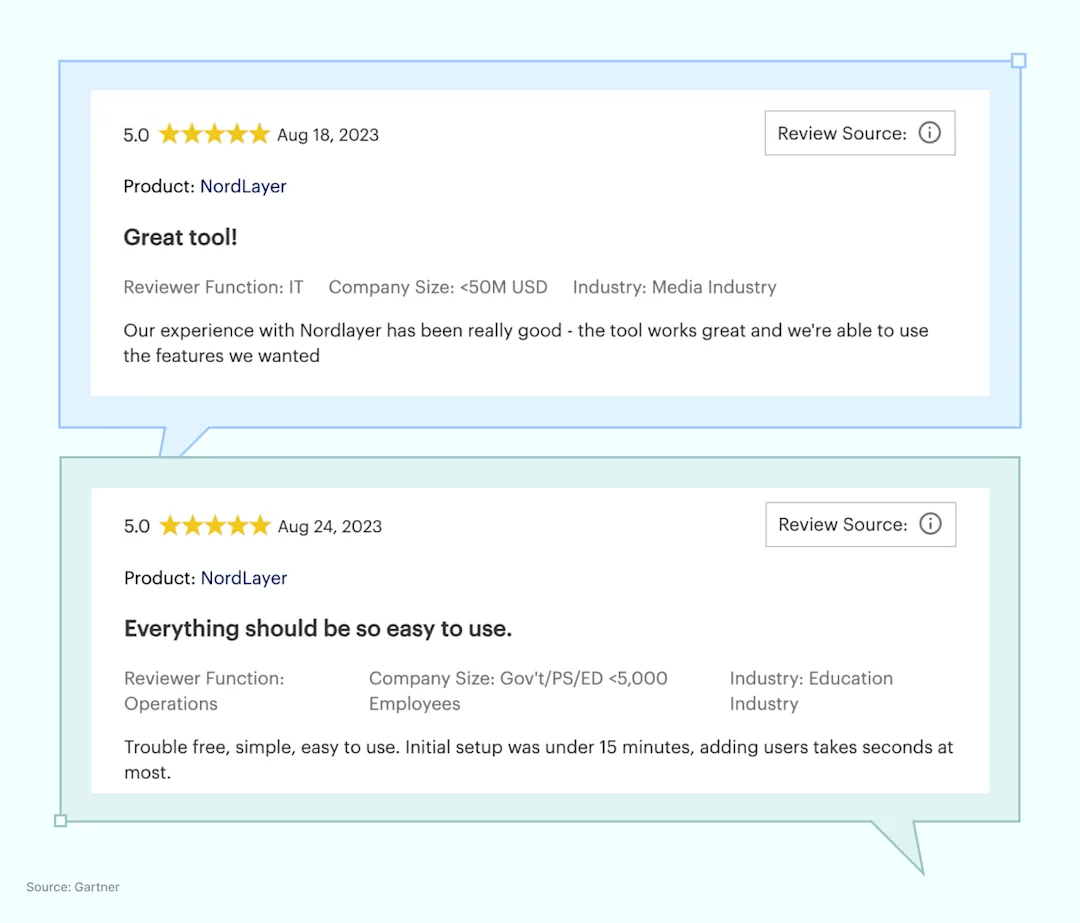
NordLayer reviews
To provide an objective evaluation of the product, we will refer to major VPN review sites (Gartner, Capterra, Cybernews) and will look into client feedback shared on these websites:
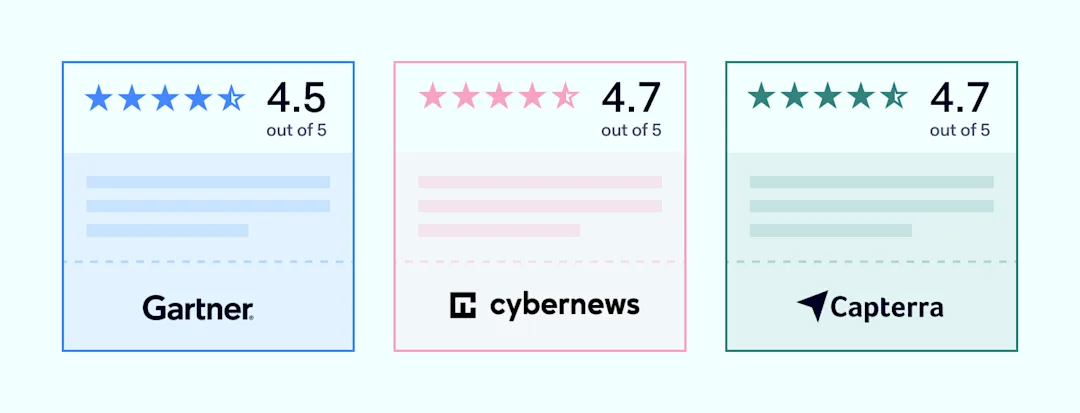
Customer feedback and insights:
NordLayer offers Security Service Edge (SSE) capabilities like Cloud Firewall (FWaaS), Zero Trust Network Access (ZTNA), and Secure Web Gateway (SWG) for creating robust security policies. To learn more about NordLayer’s secure network access solution features and plans, see our pricing information.
Twingate
Twingate is a security service that provides controlled remote access to company cloud resources through Zero Trust verification, detailed secure access policies, and multi-factor authentication. It’s deployable on multiple cloud-native services and designed for easy integration with existing tech stacks.
Twingate capabilities
Integrations with major IdPs, MDM/EDRs, SIEMs, and DOH providers
Security model based on Zero Trust Architecture
Centralized management
Free introductory plan and free trial
Twingate benefits
According to the Twingate website, the solution’s strengths are its access controls and connectivity.
Implementation of least privileged access to protect SaaS applications and cloud-based or on-premise resources
Automated Zero Trust integration with API-first design for easy integration with infrastructure as code (IaC)
Twingate limitations
It doesn’t provide access control at the port level
Requires third-party access to company infrastructure
Customer support is limited (i.e., forum support for mid-tier plan)
Twingate connector deployment for remote resource access is done via Linux systems or an OCI (docker), which requires technical knowledge
Disclaimer: This review draws on details from prominent VPN evaluation websites like TechRadar, TrustRadius, Comparitech, and customer opinions shared through these channels as of April 22, 2024.
GoodAccess
GoodAccess is a cloud-based VPN that offers secure, encrypted access to local networks with Zero Trust security, static IPs, and threat protection for remote workforce across various devices and locations.
GoodAccess capabilities
Static IP for business teams, enabling access to geo-blocked resources
High-level encryption for secure internet access and data protection
The global public infrastructure of 35+ locations
Security features include features like basic and premium threat blockers
GoodAccess benefits
According to the GoodAccess website, the solution’s strengths are its access controls and connectivity.
Inexpensive with a free trial and a starting capabilities plan
Fast setup and simplified management with an easy-to-use web management platform
GoodAccess limitations
Few private server locations
Better suits small- and medium-sized organizations
24/7 live support is available for the enterprise plan only
Disclaimer: This analysis is informed by details from leading VPN comparison websites (Capterra, TechRadar, G2) and reviews shared by users on those platforms as of April 22, 2024.
Zscaler
Zscaler is a cloud-based security company providing solutions that improve the safety of users and data across various internet and private networks. It is designed to securely connect users to their applications and manage device policies without traditional hardware-based boundaries.
Zscaler capabilities
Offers SASE framework components: SWG, CASB, ZTNA, FWaaS
Access control that is detailed and customizable
Enhanced visibility into user activities and assets
Zscaler benefits
Enhanced security through a multi-layered approach
Suits businesses of all sizes
User-friendly interface
Zscaler limitations
Configuration complexity, which can be challenging for businesses without dedicated IT teams
Demands high-speed internet for optimal performance
Pricing details are only available through consultation
Disclaimer: Product review is based on information provided on Zscaler’s website, Gartner and TechRadar’s reviews of Zscaler, and customer feedback shared on review platforms (G2), accessed on April 22, 2024.
Cisco
Cisco is a global technology leader known for its networking and security solutions. These solutions are integrated across Cisco’s entire product portfolio and aim to protect enterprise networks, data, and applications.
Cisco capabilities
Provides services like malware protection, intrusion prevention, and secure internet gateways.
Offers an SSE-based unified defense strategy across networks, clouds, endpoints, and applications.
Delivers comprehensive network and cloud security analytics, ideal for large enterprises due to its scalable and detailed features.
Cisco benefits
Scalable, advanced threat protection, and comprehensive integration capabilities.
Centralized management features across its products enable simplified administration of security policies and procedures.
Extensive global reach.
Cisco limitations
Some users find the setup and management of certain Cisco security products to be complex and resource-intensive.
The cost can be a barrier for smaller businesses or those with limited IT budgets.
Disclaimer: This review draws from details on Cisco’s corporate site, analyses from industry analysts like Gartner and Forrester, as well as end-user reviews found on TrustRadius and G2 as of April 22, 2024.
Make an informed decision
The review of Perimeter 81 and its competitors aims to support decision-makers in securing access to the organization’s local networks and protecting their teams. However, they are struggling to find a starting point.
Explore Decision Maker’s Kit, a free tool prepared by the NordLayer team, which helps build a strategy for selecting the most suitable solution for your organization and guides you throughout the process from A to Z.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.


What does ransomware recovery look like?
Ransomware recovery isn’t a one-size-fits all type of thing, and as such, it’s important to be thinking about data protection best practices and how to minimize the impact of an eventual ransomware attack — because it’s a matter of when it happens to you, not if.
Because of the complexity of SaaS deployments and all the differing policies, it’s easy to overlook some details and have data protection gaps — gaps that will become painfully obvious when you’re trying to recover from ransomware or another data loss scenario.
So, that’s why I want to equip you with some of my recommended steps that you can use to hopefully make good business decisions about how you can prepare for the time when ransomware comes to you.
Here’s a checklist of six points for disaster recovery and business continuity that I would encourage you to keep in mind and think about to boost your cyber resiliency:
1. You’ve done a risk assessment to find the most critical infrastructure and data assets to protect.
2. You’ve created a prioritized, granular DR (disaster recovery) plan supported by your software.
3. You’ve backed up all your mission-critical data.
4. You regularly test and verify your recovery processes.
5. You’re recovering from backups that are immutable and tamper proof.
6. Your backups remain available on a separate, air-gapped infrastructure.
Let’s dive deeper into the details of the six steps I’ve recommended
Point 1: Do a formal risk assessment
The first thing I’d recommend you check is that you’ve done a formal risk assessment to identify what the most critical infrastructure and data assets are for you to protect. This is obviously going to vary according to your business. Where are you located? What line of business are you in? What are the biggest risks that your business faces? And so on.
It’s very likely you’ve already done some of that work for sort of generic cybersecurity reasons, but you need to carry it to the next step and say, “All right, if I have assessed the risk of different security threats and the impact that they may have, what’s the second order risk assessment if one of those risks turns into a vulnerability that is successfully exploited? What does it mean for my business continuity capabilities?”
Point 2: Create a prioritized, granular DR plan
Second, you should be able to check off the box that says you’ve created a prioritized, granular disaster recovery plan that’s supported by your software. I see far too many customers who come to us and say, “Hey, good news, we’re buying your solutions so our SaaS data will be protected.” I say, “OK, that’s great. Tell me about your disaster recovery plan.” And their answer is, “Well, we’re just getting started. We don’t really have a plan yet.”
If I’m honest, I’d rather you build a plan and then call Keepit rather than call Keepit and then build your plan because your plan has to incorporate things that don’t involve SaaS data recovery. Just to cite one example from a real customer that we’re working with: Suppose that your operations are in a part of the world that is subject to hurricanes.
That means for every hurricane that you see, you’re going to see several other events — high winds, flooding, storm surge, and so on. How do you tell people not to come to work because the building is flooded? You may not be able to rely on Teams or on Zoom or on another cloud-based communication system to do that. That’s a part of your disaster recovery plan.
Point 3: Create a backup of all your mission-critical data
I like to emphasize to people that recovering your data is the first necessary part of restoring your business operations. It’s not completely sufficient all by itself just to say, “Oh, I have a backup” because if I walked up to you and said, “Oh, you had a disaster, great, here’s a USB stick that has all of your data on it” that probably wouldn’t be enough to get your business up and running again. It would help, but it wouldn’t be enough all by itself.
Point 4: Test regularly and verify your backups
Having a backup of your mission critical data and knowing that that backup is valid because you have regularly tested and verified the recovery is critical. This helps you know, in the gravest extreme, where your data is, that it’s intact, that it hasn’t been tampered with, and that you have people available to you who can coordinate and execute or restore leading to a recovery. Super important.
Those are the things most people think of when they think of what does good recovery look like. Do I have a backup and does my backup work? That’s not to minimize the importance of these questions, but they’re only part of the overall evaluation that you should be doing.
Point 5: Ensure your backups are immutable and tamper proof
Next, when you do a recovery, ensure the source backups that you’re using to do that recovery are immutable and tamper proof — and you can prove it. Why do I say that? Well, if you have a backup and you don’t know for certain that it is immutable, then you’ve got a potential exploitable data protection gap. (Read more about immutable data protection.)
As we see persistent nation-state scale attacks becoming more common, one increasingly common tactic is for the attacker to attack your repository of backups, too. (Attacks such as Midnight Blizzard.) When you think about how traditional backup systems are constructed, if an attacker can get into your on-premises environment, they can probably escalate privileges and pivot to kill your on-prem backups. Now you may say, “Oh hey, no problem, I’ve got backups in the cloud.”
Well, guess what?
If your cloud environment is linked to your on-prem environment, as it almost always will be with Azure and very probably is with AWS (Amazon Web Services), then an attacker who can compromise an account and then escalate privileges in the cloud can take that privilege to account, pivot to the cloud, and start blowing things up. This is the whole focus of the Mango Sandstorm attacks that Microsoft wrote about last year. So, the only way to protect yourself against that is to have your backups isolated. Which leads me to my final point.
Point 6: Keep backups on a logically separate, air-gapped infrastructure
You can call them air gapped, and you can call them isolated. The term isn’t as important as the notion that you want your backups to be stored somewhere that doesn’t have direct directory or security connectivity to your production systems. This way, if your production system is compromised, you’re able to get into your backup environment, verify the presence of your backups, verify the integrity of your backups before you start doing a restore. Read about why air-gapped backup is your best defense against ransomware.
Final words
From conducting a comprehensive risk assessment to fortifying your backups within an air-gapped, immutable backup, each step is a crucial layer in the armor of cyber defense. The importance of proactive measures can’t be overstated, so I hope the pointers outlined above are helpful for you and your DR plan.
If you’d like to learn more about ransomware recovery, be sure to catch our on-demand webinar, The ROI of ransomware recovery.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About Keepit
At Keepit, we believe in a digital future where all software is delivered as a service. Keepit’s mission is to protect data in the cloud Keepit is a software company specializing in Cloud-to-Cloud data backup and recovery. Deriving from +20 year experience in building best-in-class data protection and hosting services, Keepit is pioneering the way to secure and protect cloud data at scale.


ESET Launches AI Advisor to Enhance Threat Detection and Response
BRATISLAVA, Slovakia – May 29, 2024 — ESET, a global leader in cybersecurity solutions, is proud to introduce ESET AI Advisor, an innovative generative AI-based cybersecurity assistant that transforms incident response and interactive risk analysis. First showcased at RSA Conference 2024, the new solution is now available as part of the ESET PROTECT MDR Ultimate subscription tier and ESET Threat Intelligence.
Unlike other vendor offerings and typical generative AI assistants that focus on soft features like administration or device management, ESET AI Advisor seamlessly integrates into the day-to-day operations of security analysts, conducting in-depth analysis. Building on over two decades of ESET’s expertise in AI-driven endpoint protection, the offering provides detailed incident data and offers SOC team-level advisory. This is a gamechanger for companies with limited IT resources who want to utilize the advantages of advanced Extended Detection and Response (XDR) solutions and threat intelligence feeds.
“As cybersecurity threats become increasingly sophisticated, ESET remains committed to providing cutting-edge solutions that address these challenges. The ESET AI Advisor module represents a significant leap forward in our mission to close the cybersecurity skills gap and empower organizations to safeguard their digital assets effectively,” said Juraj Malcho, Chief Technology Officer at ESET.
One of its primary benefits for this new solution is closing the cybersecurity skills gap. Security analysts of all skill levels can use ESET AI Advisor to conduct interactive risk identification, analysis, and response capabilities, which are provided in an easily understandable format. The user-friendly interface makes sophisticated threat data actionable even for less experienced IT and security professionals.
The ESET AI Advisor also excels in facilitating faster decision-making for critical incidents. Security analysts can simply consult the ESET AI Advisor to understand the specific threats their environment faces. Leveraging extensive XDR collected data, the ESET AI Advisor identifies and analyzes potential malware threats, providing intuitive insights into their behavior and impact. It assists in recognizing phishing attempts and advising users on how to avoid falling victim to fraudulent emails or websites. By monitoring network traffic, the ESET AI Advisor can flag unusual or suspicious behavior, helping security teams take appropriate action. Its ability to automate repetitive tasks is an additional advantage. By managing routine processes such as data collection, extraction, and basic threat detection, it allows security teams to focus on more strategic initiatives.
In ESET Threat Intelligence, the new module will help researchers analyze vast quantities of unique APT reports and understand latest development in world of cyber threats. With its conversational prompts and interactive dialogue, ESET AI Advisor empowers organizations to analyze and mitigate threats effortlessly and fortify their cybersecurity posture.
For more information on the use of AI in cybersecurity, download ESET’s whitepaper here: Cybersecurity in an AI Turbocharged Era.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About ESET
For 30 years, ESET® has been developing industry-leading IT security software and services for businesses and consumers worldwide. With solutions ranging from endpoint security to encryption and two-factor authentication, ESET’s high-performing, easy-to-use products give individuals and businesses the peace of mind to enjoy the full potential of their technology. ESET unobtrusively protects and monitors 24/7, updating defenses in real time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company. Backed by R&D facilities worldwide, ESET became the first IT security company to earn 100 Virus Bulletin VB100 awards, identifying every single “in-the-wild” malware without interruption since 2003.