Summary: Cyber threats to gaming companies are growing fast. Discover why cybersecurity is essential for protecting player trust, revenues, and gaming operations.
The gaming industry is booming—and it’s easy to see why. With exciting innovations in online gaming and global player engagement soaring, revenues keep climbing. Experts estimate the industry will hit over $300 billion in annual revenue by 2028. That’s more than double its value back in 2019.
As gaming continues to grow, cybercriminals see opportunities too. Online gaming platforms handle enormous amounts of sensitive information, from payment details to login credentials and personal player data. With so much valuable information stored digitally, gaming companies have become prime targets for cyber threats.
Now more than ever, cybersecurity in gaming isn’t just an IT issue—it’s a fundamental business concern. Game developers and gaming companies must invest in strong security measures to protect data, maintain player trust, and secure their financial futures.
The biggest cybersecurity threats to gaming companies
The variety and frequency of cyber threats are increasing rapidly, presenting serious challenges for gaming companies. Attackers constantly refine their tactics, searching for new ways to breach defenses and compromise gaming accounts. Let’s break down the biggest threats the gaming industry faces today.

DDoS attacks and service disruption
One common threat is distributed denial of service attacks—or simply, DDoS attacks. These cyber-attacks flood gaming servers with excessive traffic, forcing them offline.
For example, in 2020, Blizzard Entertainment faced severe disruptions during major tournaments due to relentless DDoS attacks. In April 2025, they experienced a DDoS attack again. These disruptions don’t just frustrate gamers—they also lead to significant financial losses for gaming companies.
Credential stuffing and account takeovers
Many players reuse passwords across different online gaming platforms, making gaming accounts easy prey for attackers. Cybercriminals launch brute force attacks using automated tools that systematically try millions of username and password combinations.
In 2019, Epic Games had to warn Fortnite players after attackers successfully compromised millions of accounts. Securing player accounts with multi-factor authentication (MFA) significantly reduces this threat.
Phishing scams and social engineering
Attackers frequently use clever social engineering tactics, especially phishing scams, to trick gamers into revealing their login credentials or other sensitive information. Fake promotions offering in-game rewards or currency entice players to click malicious links. Falling victim may expose sensitive data or financial details to cybercriminals.
Ransomware attacks on game developers
Ransomware—malicious software designed to encrypt data and hold it hostage—also threatens the gaming industry. In 2021, CD Projekt Red suffered a massive ransomware attack, halting game development and causing serious financial and reputational damage. Companies need strong backup plans and endpoint protection to proactively guard against ransomware.
Cheating software as malware carriers
Illegal cheat programs often come bundled with hidden malware, infecting thousands of gaming devices without the user’s knowledge. Games like Call of Duty have seen cheats used to install spyware and other malicious programs, exposing players to identity theft and fraud. The gaming industry must educate players about these hidden risks.
Supply chain vulnerabilities
The modern gaming ecosystem depends on third-party providers and external tools for game developers. Unfortunately, these outside tools can introduce hidden vulnerabilities. The SolarWinds breach showed how attackers can exploit vulnerabilities in supply chains and impact industries like online gaming.
Insider threats to gaming companies
Sometimes threats come from within the organization itself. Employees or contractors with privileged access may accidentally or deliberately cause security breaches. Zynga once faced a situation where former employees stole proprietary game data, threatening both the company’s intellectual property and its reputation.
Why cybersecurity is critical for gaming businesses
Cybersecurity isn’t just about avoiding threats—it directly contributes to a gaming company’s overall success and profitability. Here’s why robust cybersecurity practices are essential for the gaming industry.

Protecting revenue streams
Downtime is costly. Every minute gaming platforms remain offline, companies lose potential revenue.
DDoS attacks interrupting major tournaments or game launches can be devastating. Strong security measures, including VPNs and real-time DDoS mitigation, keep gaming services stable and protect revenue streams.
Maintaining brand reputation
The gaming industry depends on player trust. Serious security breaches can permanently damage a company’s brand. Strong cybersecurity practices prevent these disasters, preserving consumer trust and loyalty.
Enhancing player experience
Players want secure, fair, and uninterrupted gaming experiences. Malware infections, account theft, or cheating disrupt the fun, driving players away. Implementing effective cybersecurity—such as endpoint protection and proactive anti-cheat measures—maintains a positive gaming environment, encouraging player retention.
Avoiding regulatory fines
Globally, laws like GDPR impose strict penalties for mishandling sensitive data—fines can reach up to 4% of annual revenue. Compliance with data protection regulations isn’t just smart—it’s mandatory. The gaming industry must adopt stringent cybersecurity practices to stay compliant and avoid expensive penalties.
Attracting investments and partnerships
Investors and partners favor companies with secure, well-managed cybersecurity frameworks. Demonstrating a commitment to protecting data and infrastructure enhances credibility. Adopting principles like Zero Trust further strengthens security and makes companies more attractive to potential investors and partners.
Best practices for cybersecurity in the gaming industry
With cyber threats constantly evolving, gaming companies need comprehensive cybersecurity strategies. Here are some proven best practices every gaming company should adopt:
Protecting user data and privacy
Gamers trust companies to protect their personal data. Implement robust measures such as:
- Secure payment gateways: Comply with PCI DSS standards to securely process payments.

Preventing account takeovers
Protecting gaming accounts is crucial for player retention and security. Account theft can permanently drive loyal players away—preventing it ensures your gaming community thrives.
- Multi factor authentication (MFA): MFA prevents unauthorized access even if login credentials are compromised.
- Player education: Inform players about phishing, social engineering, and the importance of strong, unique passwords.
Maintaining service availability
Reliable gaming services build player loyalty and satisfaction. Just one prolonged service interruption can damage your reputation—stable services keep your players happy and engaged.
- DDoS mitigation: Implement real-time traffic monitoring to neutralize attacks quickly.
- Cloud security: Regularly audit cloud infrastructure to prevent vulnerabilities.
- Cloud firewall and VPN gateways: Use strong perimeter defenses and encrypted VPN connections to secure remote gameplay, especially during high-traffic events.
Protecting against malware and ransomware
Even a single malware infection can halt game development, so defensive measures are your best line of protection. Proactively defend your infrastructure against malware:
- Endpoint protection: Deploy antivirus and Endpoint Detection and Response (EDR) solutions across every gaming device.
- Regular backups: Store backups separately to quickly recover after ransomware attacks.
- System updates and patches: Regularly update software and security configurations to eliminate vulnerabilities.
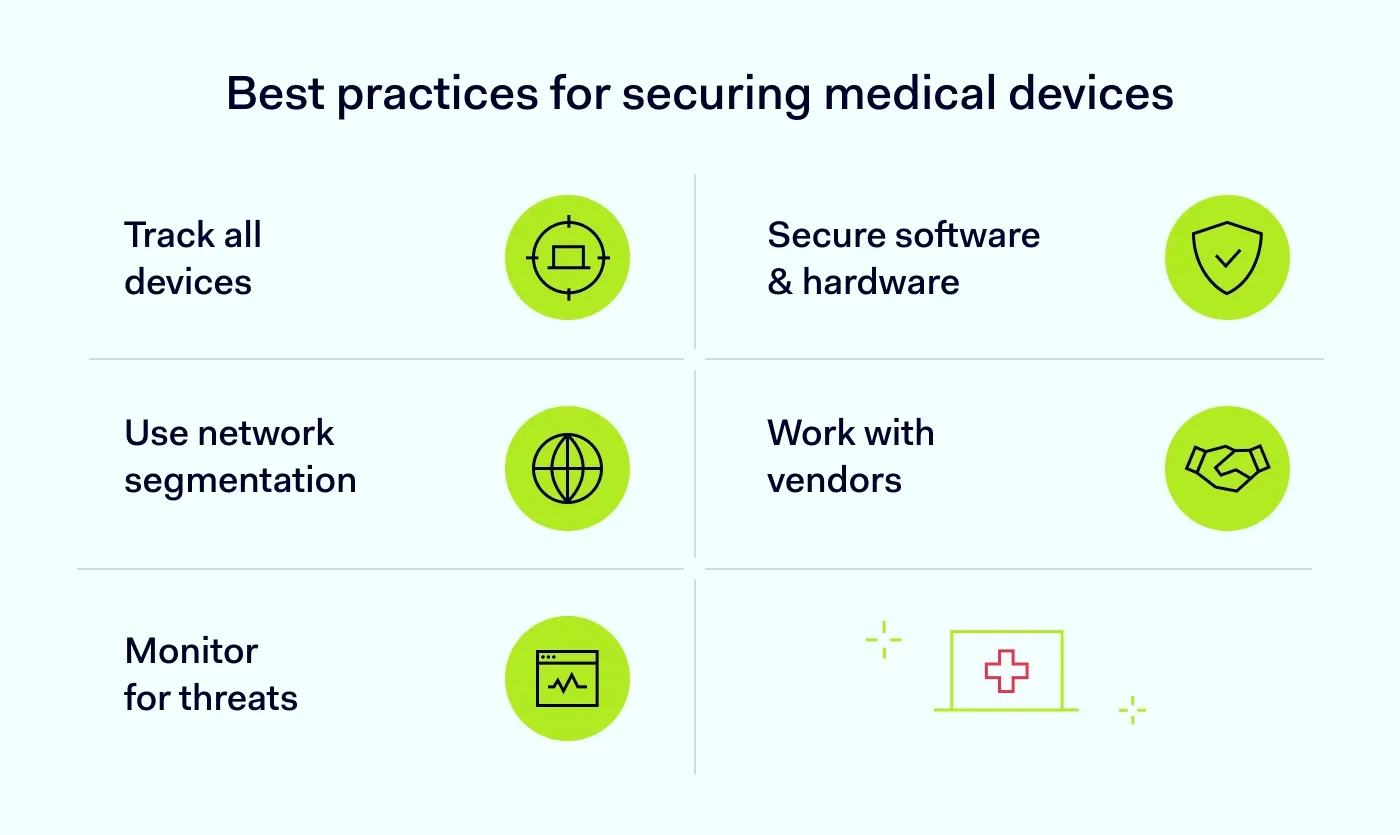
Minimizing insider and supply chain risks
Trusting third-party providers blindly is risky. Vigilant security keeps your game development pipeline secure. Protect against threats from insiders and third-party providers:
- Least privilege principle: Limit access rights to necessary functions, reducing potential internal risks.
- Network segmentation: Separate sensitive areas to contain threats.
- Vendor security assessments: Regularly audit third-party providers for secure coding and compliance practices.
- Zero Trust architecture: Continuously verify all users and devices, preventing unauthorized lateral movements within networks.
Meeting compliance and regulatory requirements
Complying with regulatory standards like GDPR, COPPA, and PCI DSS is crucial for gaming companies. Strict compliance helps avoid costly fines and maintains player trust. Companies should clearly document data handling practices to ensure transparency. Regular compliance audits and risk assessments are essential. It’s important to continuously encrypt payment details and sensitive player data. Monitoring regulatory changes closely helps avoid unexpected compliance issues. Holding third-party vendors to consistent data protection standards strengthens overall security. Ultimately, transparency and strict compliance build long-term credibility with players and regulators.
Emerging cybersecurity trends in the gaming industry
Technology advances quickly, and cybercriminals continuously evolve their methods. This makes cybersecurity an ongoing challenge for the gaming industry.

Artificial intelligence is becoming both a weapon and a defense. Attackers use AI-driven tools to evade traditional security measures. Gaming companies respond with real-time analytics to rapidly spot these threats. Blockchain technology provides secure and transparent transactions, safeguarding digital assets from theft. Automated threat intelligence platforms help gaming companies swiftly identify cyber threats. Bug bounty programs and regular penetration testing proactively uncover vulnerabilities. These measures keep gaming platforms secure and resilient.
Enhancing gaming cybersecurity with NordLayer
NordLayer provides specialized cybersecurity solutions designed for the gaming industry. Its comprehensive offerings include:
- Zero Trust Network Access (ZTNA) features
- Secure VPN with NordLynx (based on WireGuard) and Site-to-Site connections
- Advanced network segmentation
- User identity management with popular identity providers like Okta and Google
- Secure Web Gateway (SWG) features
- Real-time network visibility and monitoring
For instance, Eldorado Games successfully leveraged NordLayer’s solutions to protect its remote workforce, secure critical data, and maintain smooth processes for game developers.
To learn more, explore the detailed Eldorado Games case study or check our resource on cybersecurity in software development. NordLayer helps the gaming industry effectively safeguard its operations, secure gaming platforms, and deliver reliable gaming experiences that players trust and enjoy.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.









:format(avif))